WPA3: The Next Generation of WiFi Security Explained
This comprehensive technical reference guide explains the architectural shifts introduced by WPA3, including SAE, OWE, and Forward Secrecy. It provides actionable deployment strategies for IT managers and network architects to upgrade enterprise and public venue networks securely.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- Simultaneous Authentication of Equals (SAE)
- Forward Secrecy
- Opportunistic Wireless Encryption (OWE)
- WPA3-Enterprise and 192-bit Security
- Implementation Guide
- Phase 1: Assessment and Auditing
- Phase 2: WPA3 Transition Mode Deployment
- Phase 3: Segmentation and Enforcement
- Integrating with Captive Portals
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact
- Listen to the Technical Briefing

Executive Summary
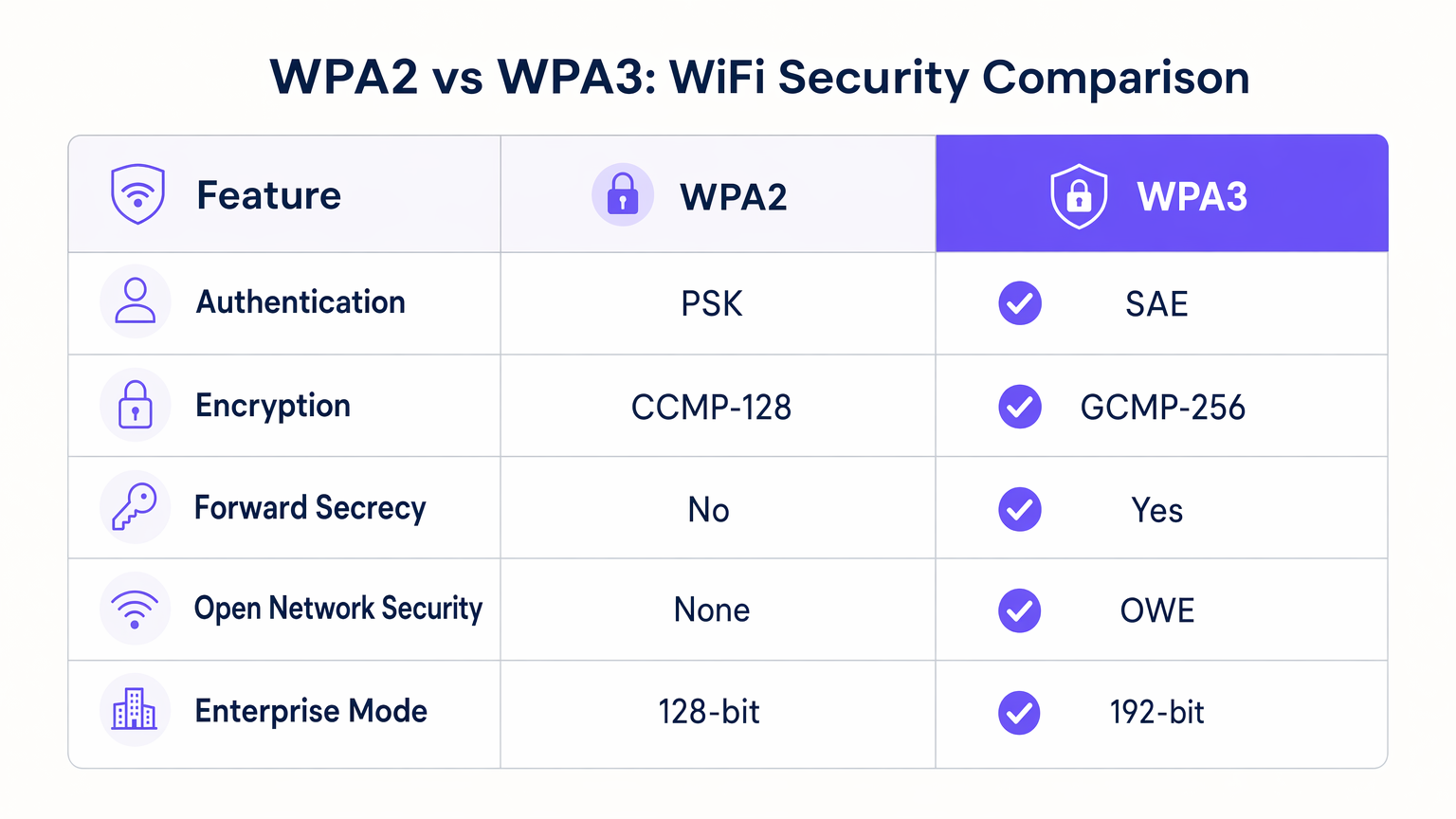
For IT managers, network architects, and venue operations directors, the transition to WPA3 represents the most significant wireless security architecture shift in two decades. While WPA2 has served as the industry standard since 2004, its reliance on Pre-Shared Keys (PSK) and vulnerability to offline dictionary attacks make it increasingly unsuitable for modern enterprise environments. WPA3 addresses these fundamental architectural flaws while introducing critical new capabilities for public venues.
This technical reference guide provides actionable guidance on deploying WPA3 across hospitality, retail, and public-sector networks. It covers the four core pillars of the new standard: Simultaneous Authentication of Equals (SAE) for robust password-based authentication, Opportunistic Wireless Encryption (OWE) for securing open networks, Forward Secrecy to protect historical traffic, and a 192-bit security suite for highly regulated enterprise deployments.
By understanding these mechanisms, network operators can plan a phased migration strategy that enhances security posture without disrupting legacy client devices or the user experience. Crucially, this guide maps these technical capabilities to tangible business outcomes, demonstrating how robust wireless security integrates with Guest WiFi and WiFi Analytics platforms to deliver secure, compliant, and data-rich guest experiences.
Technical Deep-Dive
The transition from WPA2 to WPA3 is not merely an incremental cryptographic update; it is a fundamental redesign of the authentication handshake and encryption negotiation processes. Understanding the mechanics of these changes is essential for architects designing next-generation wireless networks.
Simultaneous Authentication of Equals (SAE)
The most significant vulnerability in WPA2-Personal is the four-way handshake used to establish a secure connection using a Pre-Shared Key (PSK). If an attacker captures this handshake, they can take the data offline and run brute-force dictionary attacks against it indefinitely until the password is recovered.
WPA3 replaces the PSK mechanism with Simultaneous Authentication of Equals (SAE), a variant of the Dragonfly key exchange protocol. SAE utilises a Diffie-Hellman-style exchange where both the client and the access point prove knowledge of the password without ever transmitting it over the air, even in a hashed format. This zero-knowledge proof completely eliminates the vector for offline dictionary attacks. Even if an attacker captures every packet of the SAE exchange, they cannot derive the session key or the original password from the captured data.
Forward Secrecy
A critical operational benefit of SAE is the introduction of Forward Secrecy. Under WPA2, if an attacker records encrypted traffic today and manages to obtain the network password tomorrow (e.g., through a social engineering attack or a compromised employee device), they can retroactively decrypt all previously recorded traffic.
WPA3's SAE generates a unique ephemeral encryption key for every session. Because the session keys are not mathematically derived from the master password in a reversible way, compromising the network password does not compromise past traffic. For Hospitality venues handling sensitive guest information, this provides a significant layer of risk mitigation against long-term passive eavesdropping.
Opportunistic Wireless Encryption (OWE)
For public venues, Opportunistic Wireless Encryption (OWE) — marketed by the Wi-Fi Alliance as Wi-Fi Certified Enhanced Open — is the most transformative feature of WPA3. Historically, open networks (those without a password) transmit data in plaintext, leaving users vulnerable to packet sniffing and session hijacking.
OWE automatically negotiates an encrypted connection between the client device and the access point without requiring user authentication or a password. The user experience remains identical to a traditional open network — the user simply selects the SSID and connects — but the underlying 802.11 frames are encrypted. This is particularly relevant for Retail environments where frictionless onboarding is required, but data privacy (and GDPR compliance) must be maintained.
WPA3-Enterprise and 192-bit Security
For highly regulated environments, WPA3-Enterprise introduces an optional 192-bit minimum security mode aligned with the Commercial National Security Algorithm (CNSA) suite. This mode mandates the use of GCMP-256 (Galois/Counter Mode Protocol) for encryption and HMAC-SHA-384 for integrity checking, providing robust protection for financial, government, and Healthcare networks.
Implementation Guide
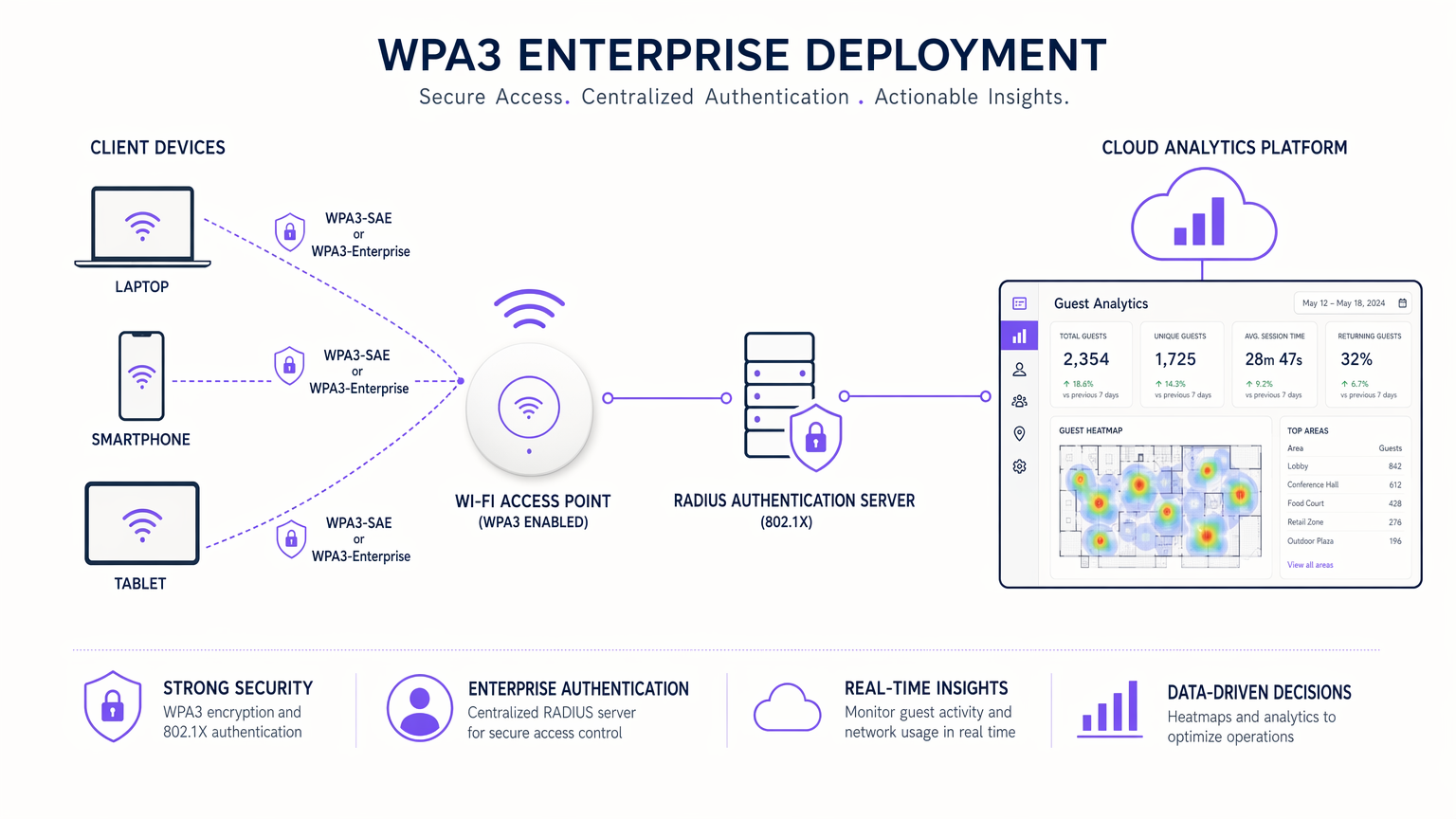
Deploying WPA3 across an enterprise estate requires a phased approach to accommodate legacy devices while maximising security for capable clients.
Phase 1: Assessment and Auditing
Begin by auditing the firmware versions of your existing access points and wireless LAN controllers. Most enterprise-grade hardware manufactured after 2018 supports WPA3 via firmware updates. Simultaneously, profile your client device estate using your network management platform or WiFi Analytics dashboard to determine the percentage of WPA3-capable devices.
Phase 2: WPA3 Transition Mode Deployment
To support a mixed environment, deploy WPA3 Transition Mode. This allows a single SSID to accept both WPA2 (PSK) and WPA3 (SAE) connections.
- Configure the SSID: Enable WPA3 Transition Mode on the target SSID.
- Monitor Connections: Use analytics to track the ratio of WPA2 to WPA3 connections over time.
- Identify Legacy Devices: Isolate devices that fail to connect or consistently fall back to WPA2 (e.g., older IoT devices or legacy POS terminals).
Note: WPA3 Transition Mode is susceptible to downgrade attacks where an active adversary forces a WPA3-capable client to connect using WPA2. Therefore, it should be viewed as a temporary migration step, not a permanent architecture.
Phase 3: Segmentation and Enforcement
Once the volume of legacy devices drops below an acceptable threshold, move to full WPA3 enforcement.
- Isolate Legacy IoT: Move non-compliant devices (smart TVs, older building management systems) to a dedicated, hidden WPA2 SSID on an isolated VLAN.
- Enforce WPA3-Only: Disable WPA2 on the primary guest and corporate SSIDs, ensuring all capable devices benefit from SAE and Forward Secrecy.
Integrating with Captive Portals
When deploying OWE for public networks, ensure your captive portal solution is compatible. Platforms like Purple act as the identity provider and consent mechanism above the encrypted OWE transport layer. The access point handles the OWE encryption, while the captive portal manages the user journey, terms of service acceptance, and data capture.
Best Practices
- Firmware Maintenance: Ensure all access points are running the latest firmware to mitigate early WPA3 vulnerabilities, such as SAE confirmation frame flooding.
- VLAN Segmentation: Regardless of the WPA version, maintain strict VLAN segmentation between guest traffic, corporate data, and IoT devices. This is foundational for PCI DSS compliance.
- Avoid Mixed-Mode on High-Security SSIDs: For critical corporate networks, bypass Transition Mode entirely and deploy a dedicated WPA3-Enterprise SSID to prevent downgrade attacks.
- Educate the Helpdesk: Ensure frontline IT support understands the difference between WPA2 and WPA3, particularly regarding legacy device compatibility and OWE behaviour.
For a broader perspective on network architecture optimisation, consider reading about The Core SD WAN Benefits for Modern Businesses .
Troubleshooting & Risk Mitigation
Common Failure Modes
- Legacy Client Connectivity Issues: Some older client devices (particularly legacy Android devices and cheap IoT sensors) may fail to connect to an SSID broadcasting WPA3 Transition Mode, even if they only support WPA2.
- Mitigation: Maintain a dedicated WPA2-only SSID for these specific devices until they can be decommissioned.
- Captive Portal Redirection Failures: In some early OWE implementations, clients may struggle with captive portal redirection.
- Mitigation: Test thoroughly with a mix of iOS, Android, and Windows devices. Ensure your guest WiFi platform is explicitly validated for OWE environments.
- SAE Handshake Overhead: In extremely high-density environments (e.g., stadiums), the computational overhead of the SAE handshake can marginally impact AP CPU utilisation.
- Mitigation: Monitor AP performance during peak load and adjust client load-balancing thresholds if necessary.
ROI & Business Impact
Upgrading to WPA3 is not typically a revenue-generating project, but it is a critical risk mitigation and compliance enablement initiative.
- Risk Reduction: Eliminating offline dictionary attacks and implementing Forward Secrecy drastically reduces the potential blast radius of a wireless network compromise, protecting brand reputation and avoiding regulatory fines.
- Compliance Enablement: WPA3-Enterprise 192-bit mode and OWE directly support compliance with stringent frameworks like PCI DSS and GDPR by ensuring data confidentiality in transit.
- Future-Proofing: The Wi-Fi Alliance requires WPA3 for all Wi-Fi 6 (802.11ax) and Wi-Fi 6E certifications. Migrating now ensures your infrastructure is ready to support the next generation of high-performance wireless standards.
By pairing robust WPA3 security with a comprehensive Guest WiFi platform, venues can deliver a secure, frictionless connectivity experience that builds customer trust while capturing the first-party data necessary to drive loyalty and engagement. For a detailed comparison of legacy standards, review our guide: WPA, WPA2 and WPA3: What's the Difference and Which Should You Use? .
Listen to the Technical Briefing
For a deeper dive into the operational implications of WPA3, listen to our 10-minute technical podcast:
Key Definitions
WPA3 (Wi-Fi Protected Access 3)
The latest generation of Wi-Fi security certified by the Wi-Fi Alliance, introducing significant cryptographic upgrades over WPA2.
When IT teams are refreshing network hardware or updating security policies to meet modern compliance standards.
SAE (Simultaneous Authentication of Equals)
A secure key establishment protocol used in WPA3-Personal that replaces the Pre-Shared Key (PSK) method, providing resistance against offline dictionary attacks.
When configuring the authentication method for new SSIDs, ensuring robust protection against brute-force password guessing.
OWE (Opportunistic Wireless Encryption)
A standard that provides individualized data encryption for open Wi-Fi networks without requiring user authentication.
When deploying public guest WiFi in retail or hospitality environments where frictionless access must be balanced with user privacy.
Forward Secrecy
A cryptographic feature ensuring that session keys are not compromised even if the long-term master password is later discovered.
When evaluating the risk of long-term passive eavesdropping and data interception in enterprise environments.
WPA3 Transition Mode
A configuration allowing a single SSID to support both WPA2 and WPA3 clients simultaneously.
When planning a phased migration to WPA3 in an environment with a mix of modern and legacy client devices.
Downgrade Attack
A security exploit where an attacker forces a system to abandon a high-security mode of operation (like WPA3) in favor of an older, more vulnerable standard (like WPA2).
When assessing the risks of running WPA3 Transition Mode for extended periods.
CNSA (Commercial National Security Algorithm)
A suite of cryptographic algorithms promulgated by the NSA for protecting classified information, supported by WPA3-Enterprise 192-bit mode.
When designing networks for highly regulated sectors such as government, defense, or healthcare.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic and improve security.
When isolating vulnerable legacy IoT devices from the primary corporate or guest networks during a WPA3 migration.
Worked Examples
A 200-room hotel needs to upgrade its guest WiFi to WPA3 but has a significant number of legacy smart TVs in the guest rooms that only support WPA2. How should the network architect proceed?
The architect should implement a split-SSID strategy. First, create a dedicated, hidden SSID configured strictly for WPA2-Personal and assign it to an isolated VLAN with no access to the corporate network or other guest devices. Connect all legacy smart TVs to this SSID. Second, configure the primary, public-facing guest SSID to use WPA3 Transition Mode (or pure WPA3 if all guest devices are modern) and route this traffic through the Purple captive portal for authentication and analytics.
A large retail chain wants to implement frictionless WiFi for shoppers without requiring a password, but the CISO is concerned about GDPR compliance and plaintext data transmission over open networks. What is the recommended architecture?
The deployment should utilize WPA3 Opportunistic Wireless Encryption (OWE), also known as Wi-Fi Certified Enhanced Open. The access points will broadcast an open SSID, allowing shoppers to connect without a password. However, OWE will automatically negotiate unique, encrypted sessions for every client. Once connected, the traffic is routed through the Purple Guest WiFi platform to present a captive portal where users accept the terms of service and provide consent for data processing.
Practice Questions
Q1. Your university campus is deploying a new wireless network for students. You want to ensure maximum security for student laptops while still allowing older gaming consoles to connect. Which deployment strategy should you choose?
Hint: Consider the limitations of WPA3 Transition Mode and the benefits of network segmentation.
View model answer
Deploy two separate SSIDs. The primary student network should use WPA3-Enterprise (or WPA3-Personal) to ensure maximum security and Forward Secrecy for modern laptops and smartphones. A secondary, hidden SSID should be configured with WPA2-Personal on an isolated VLAN specifically for legacy gaming consoles. This prevents downgrade attacks on the primary network while maintaining compatibility.
Q2. A stadium IT director notices that during large events, the access points serving the main concourse are showing unusually high CPU utilization since enabling WPA3 Transition Mode. What is the likely cause?
Hint: Think about the cryptographic processes involved in client authentication.
View model answer
The high CPU utilization is likely caused by the computational overhead of processing Simultaneous Authentication of Equals (SAE) handshakes in a high-density environment, combined with the mixed-mode processing of WPA2 connections. The IT director should monitor the AP performance and consider adjusting client load-balancing or upgrading AP hardware if the utilization impacts throughput.
Q3. You are configuring a public WiFi network at a busy airport. The legal department requires that user traffic be protected from passive sniffing, but the marketing department insists that users should not have to enter a password to connect. How do you satisfy both requirements?
Hint: Look for a WPA3 feature specifically designed for open networks.
View model answer
Implement Opportunistic Wireless Encryption (OWE). This allows users to connect to the network without entering a password, satisfying the marketing department's requirement for frictionless access. Simultaneously, OWE automatically encrypts the data transmitted between the client and the access point, satisfying the legal department's requirement for protection against passive packet sniffing.