How MAC Address Randomization Affects Guest WiFi Analytics
This guide provides a technical deep-dive into how MAC address randomization impacts guest WiFi analytics. It offers practical strategies for IT leaders and network architects to restore visibility, ensure accurate metrics, and maintain compliance across large-scale deployments. Covering the mechanics of per-network and ephemeral randomization, identity resolution architecture, and real-world deployment scenarios, this is the definitive reference for any organisation relying on WiFi-derived spatial data.
Listen to this guide
View podcast transcript
Executive Summary
For IT managers, network architects, and venue operations directors, the widespread adoption of MAC address randomization across iOS, Android, and Windows has fundamentally disrupted traditional guest WiFi analytics. What was once a reliable, persistent hardware identifier has become an ephemeral data point, rendering legacy analytics models obsolete. This technical reference guide explores the mechanics of MAC randomization, its direct impact on metrics such as unique visitor counts, dwell time, and return visit rates, and the architectural shifts required to restore data integrity. By transitioning from hardware-centric tracking to identity-based resolution models, organisations in Retail , Hospitality , Healthcare , and Transport can maintain accurate analytics while respecting user privacy and regulatory frameworks like GDPR and PCI DSS.
Technical Deep-Dive
The Mechanics of MAC Randomization
Historically, the Media Access Control (MAC) address served as a globally unique, persistent identifier assigned to a network interface controller (NIC). In a pre-randomization environment, a device broadcasting probe requests to discover available networks would transmit its permanent, hardware-burned MAC address. This allowed network infrastructure to track a device's presence, movement, and return visits even if the user never authenticated to the network.
Beginning with iOS 14 and Android 10, mobile operating systems introduced MAC address randomization by default. Instead of transmitting the hardware MAC, the device generates a randomized, locally administered MAC address. The implementation varies slightly between vendors but generally follows two primary models:
- Per-Network Randomization: The device generates a unique MAC address for each distinct Service Set Identifier (SSID) it connects to. This MAC remains consistent for that specific SSID, allowing the device to reconnect seamlessly.
- Daily or Ephemeral Randomization: Some implementations rotate the randomized MAC address periodically (e.g., every 24 hours) or upon every connection attempt, further obscuring the device's identity over time.
The Impact on WiFi Analytics
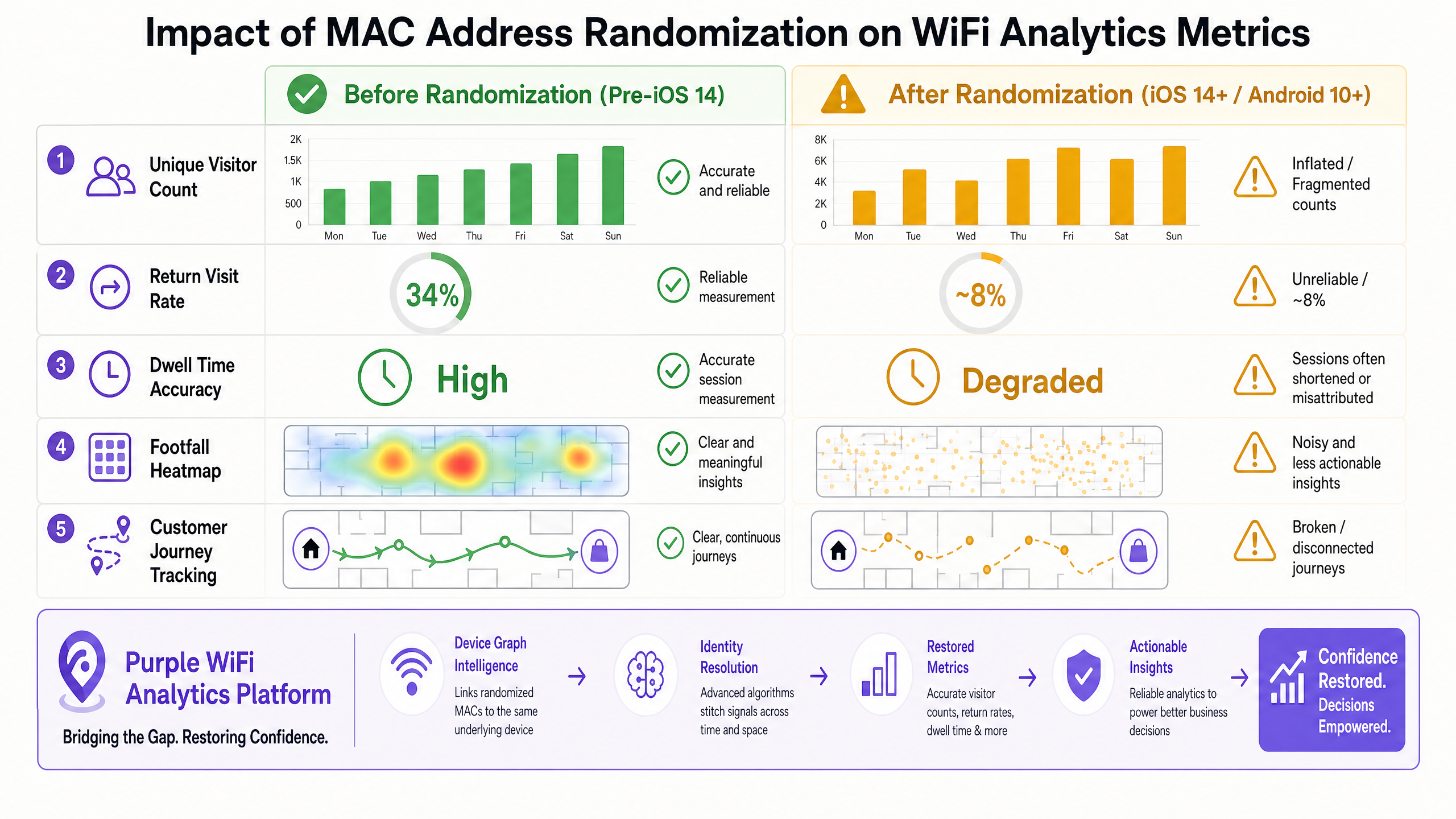
When legacy analytics platforms encounter randomized MAC addresses, the data integrity degrades rapidly. The reliance on a persistent identifier leads to significant distortions in key metrics:
- Unique Visitor Counts: Because a single physical device may present multiple MAC addresses over time (or across different SSIDs within a venue), legacy systems will count it as multiple unique visitors. This leads to artificially inflated footfall metrics.
- Return Visit Rates: If a device rotates its MAC address between visits, the analytics platform cannot link the current session to a historical session. The user is treated as a new visitor, causing return visit rates to plummet.
- Dwell Time Accuracy: In environments where a device might rotate its MAC during a prolonged session, a single visit is fragmented into multiple short sessions, skewing dwell time averages downward.
- Customer Journey Tracking: Tracking a user's movement across a large venue (e.g., a stadium or a retail complex with multiple SSIDs) becomes disjointed. The path is broken every time the MAC address changes.
Implementation Guide
Restoring Visibility: The Identity-Centric Architecture
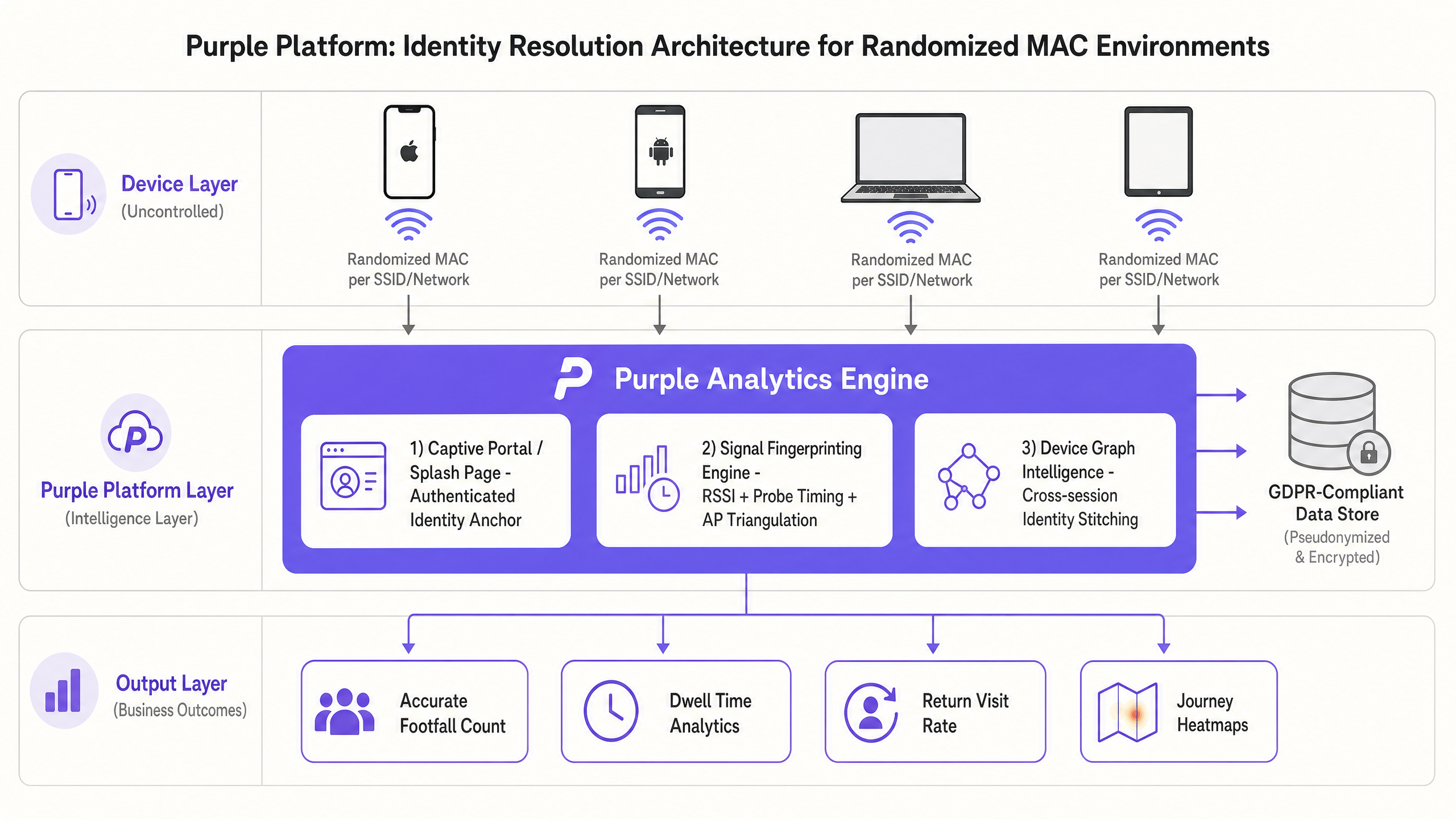
To overcome the limitations imposed by MAC randomization, IT teams must shift from hardware-based tracking to an identity-centric architecture. This involves deploying an intelligent layer that resolves multiple ephemeral identifiers back to a single, persistent user profile. The Guest WiFi platform must evolve into a comprehensive identity resolution engine.
Step 1: Establish the Authenticated Identity Anchor
The most reliable method for establishing identity is through a captive portal or splash page. When a user authenticates to the network (via email, social login, or SMS), the system creates an anchor record. This record links the current (randomized) MAC address to a known, persistent identity (e.g., an email address or a unique user ID).
This approach requires a robust WiFi Analytics platform capable of maintaining a dynamic device graph. When the user returns and authenticates again (even with a new randomized MAC), the system updates the device graph, linking the new MAC to the existing user profile.
Step 2: Implement Signal Fingerprinting (Where Permissible)
In scenarios where authentication is not required or has not yet occurred, advanced platforms utilise signal fingerprinting. This involves analysing secondary characteristics of the device's radio transmissions, such as:
- Received Signal Strength Indicator (RSSI) Patterns: Analysing how the signal strength changes as the device moves through the venue.
- Probe Request Timing and Frequency: Devices exhibit distinct patterns in how often and when they send probe requests.
- Access Point Triangulation: Using multiple APs to pinpoint the device's location and track its movement.
By combining these signals, the analytics engine can create a probabilistic model to stitch together fragmented sessions, although this method is less deterministic than explicit authentication.
Step 3: Integrate with Ecosystem Data
To further enrich the identity graph, the WiFi platform should integrate with other enterprise-systems. For example, linking WiFi authentication data with loyalty program databases or point-of-sale (POS) systems provides a holistic view of the customer journey. Purple's role as an identity provider for services like OpenRoaming under the Connect license facilitates this seamless integration across diverse environments.
Best Practices
- Prioritise Explicit Authentication: Design captive portals that offer clear value exchanges (e.g., free high-speed access, exclusive discounts) to encourage users to authenticate. This establishes the strongest possible identity anchor.
- Optimise the Captive Portal Experience: Ensure the authentication process is seamless. Implementing technologies that enable frictionless access, similar to the concepts discussed in How a wi fi assistant Enables Passwordless Access in 2026 , reduces drop-off rates and increases the percentage of known users on the network.
- Leverage Progressive Profiling: Instead of asking for all user information upfront, gather data incrementally over multiple visits. This reduces friction during the initial connection while building a comprehensive profile over time.
- Ensure Regulatory Compliance: The shift to identity-centric tracking necessitates strict adherence to privacy regulations like GDPR and CCPA. Ensure your platform anonymises or pseudonymises data appropriately and provides clear opt-in/opt-out mechanisms for users.
- Review Network Configuration: Ensure your wireless infrastructure is configured to handle the increased load of authentication requests and dynamic MAC address management. When planning channel assignments, be aware of DFS Channels: What They Are and When to Avoid Them (or for Italian deployments, Canali DFS: Cosa sono e quando evitarli ) to maintain network stability and optimise performance for analytics data collection.
Troubleshooting & Risk Mitigation
Common Failure Modes
- Over-Reliance on Unauthenticated Data: Continuing to base business decisions on raw, unauthenticated probe data in a randomised MAC environment will lead to flawed conclusions and misallocated resources.
- Fragmented Identity Silos: If the WiFi analytics platform does not integrate with other enterprise systems (e.g., CRM, loyalty apps), the organisation will maintain fragmented views of the customer, reducing the effectiveness of personalised engagement strategies.
- Poor Captive Portal Design: A cumbersome authentication process will deter users from connecting, resulting in a low attach rate and a small sample size of authenticated users, which diminishes the value of the analytics data.
Mitigation Strategies
- Implement a Device Graph: Deploy a platform that utilises advanced algorithms to stitch together fragmented sessions and resolve identities across multiple MAC addresses.
- Monitor Attach Rates: Closely track the percentage of visitors who authenticate to the network versus the total number of detected devices. A low attach rate indicates a need to optimise the captive portal experience or the value proposition offered to the user.
- Regularly Audit Data Integrity: Periodically compare WiFi analytics data with other data sources (e.g., footfall counters, POS data) to identify discrepancies and ensure the accuracy of the identity resolution engine.
ROI & Business Impact
Transitioning to an identity-centric WiFi analytics model requires investment, but the return on investment (ROI) is significant for organisations that rely on accurate spatial data.
- Accurate Resource Allocation: Reliable footfall and dwell time metrics enable precise staffing and resource allocation, optimising operational efficiency in environments like retail stores and transport hubs.
- Enhanced Customer Engagement: By understanding the true customer journey and return visit rates, marketing teams can deliver targeted, personalised campaigns that drive loyalty and increase revenue.
- Strategic Decision Making: High-fidelity data supports strategic initiatives, such as optimising store layouts, evaluating the effectiveness of marketing campaigns, and informing real estate decisions. Initiatives aimed at driving digital inclusion, as highlighted in Purple Appoints Iain Fox as VP Growth - Public Sector to Drive Digital Inclusion and Smart City Innovation , rely heavily on accurate usage data to measure impact.
- New Revenue Streams: In environments like stadiums and conference centres, accurate location data enables location-based services, such as targeted advertising and proximity marketing, creating new monetisation opportunities. Features like Purple Launches Offline Maps Mode for Seamless, Secure Navigation to WiFi Hotspots further enhance the value proposition for the user, driving higher engagement and data collection.
Key Definitions
Locally Administered MAC Address
A MAC address generated by the device's software rather than assigned by the hardware manufacturer. It is indicated by setting the second least significant bit of the first octet to 1 (e.g., x2:xx:xx:xx:xx:xx).
IT teams use this bit flag in raw packet captures or RADIUS logs to identify which devices on the network are using randomized addresses versus persistent hardware addresses. A high proportion of locally administered MACs in your logs is a diagnostic signal that randomization is active.
Device Graph
A dynamic database that maps multiple identifiers (e.g., various randomized MAC addresses, email addresses, loyalty IDs) to a single, persistent user profile.
This is the core technology required to restore analytics accuracy in a post-randomization environment, allowing platforms to stitch together fragmented sessions across multiple visits and MAC address rotations.
Probe Request
A management frame sent by a client device to actively discover available wireless networks in its vicinity. It contains the device's MAC address (which may be randomized).
Historically used for passive tracking of unauthenticated users. Now highly unreliable for long-term analytics due to randomization. Probe request data should be treated as a rough footfall indicator only, not a source of identity.
Identity Resolution
The process of analyzing various data points and signals to determine that multiple distinct identifiers actually belong to the same physical user or device.
The critical function performed by advanced analytics platforms to counteract the obfuscation caused by MAC randomization. It transforms fragmented, ephemeral data points into coherent, actionable user profiles.
Attach Rate
The percentage of total detected devices in a venue that successfully complete the authentication process and connect to the network.
A key operational metric for evaluating the effectiveness of a captive portal. A low attach rate means the analytics platform has a smaller sample size of reliable, authenticated data, directly impacting the statistical confidence of all downstream analytics.
Captive Portal
A web page that users are forced to view and interact with before access is granted to a public WiFi network, typically requiring a form of authentication or consent.
The primary mechanism for establishing an Identity Anchor by requiring users to provide credentials in exchange for network access. The design and value proposition of the captive portal directly determines the attach rate.
Signal Fingerprinting
A technique that uses secondary characteristics of a device's radio transmissions (like RSSI patterns, probe timing, and channel behavior) to probabilistically identify it, rather than relying solely on the MAC address.
Used as a supplementary tracking method when explicit authentication is not available. It is less reliable in high-density RF environments and should be treated as a probabilistic supplement to, not a replacement for, authenticated identity resolution.
Ephemeral Randomization
A more aggressive form of MAC randomization where the device rotates its MAC address periodically (e.g., daily) even when connected to the same SSID, rather than maintaining a consistent per-network MAC.
This completely breaks analytics platforms that rely on per-network MAC consistency. It forces the adoption of identity-centric architectures and is becoming more common as OS vendors increase privacy protections.
Worked Examples
A large retail chain with 500 locations is experiencing a sudden, inexplicable 40% spike in reported unique visitors across all stores, while POS transaction volume remains flat. The IT Director suspects an issue with the WiFi analytics platform.
- Diagnosis: The IT team analyzes the raw MAC address logs and identifies a high volume of locally administered MAC addresses (indicated by the second least significant bit of the first octet being set to 1). This confirms the spike is due to mobile OS updates enabling MAC randomization, not an actual increase in foot traffic.
- Architecture Shift: The chain migrates from their legacy, hardware-centric analytics tool to Purple's identity-centric platform.
- Captive Portal Optimization: They redesign the splash page to offer a 10% discount code in exchange for email authentication.
- Identity Resolution: Purple's device graph engine begins linking the randomized MAC addresses to the authenticated email profiles.
- Result: Within 30 days, the unique visitor count normalizes, accurately reflecting true footfall. Return visit rates, which had dropped to near zero, are restored as the platform successfully identifies returning customers despite their changing MAC addresses.
A multi-building corporate campus needs to track employee and guest movement for space utilization analysis. However, devices are rotating MAC addresses as they roam between different SSIDs (e.g., Corp-WiFi and Guest-WiFi).
- Network Consolidation (Where Possible): The network architect reviews the SSID strategy and consolidates redundant networks to minimize the need for devices to switch SSIDs, reducing the frequency of MAC rotation.
- Unified Authentication: The campus implements a unified authentication framework (e.g., 802.1X for employees, a streamlined captive portal for guests) integrated with a central RADIUS server and the Purple analytics platform.
- Cross-SSID Stitching: The Purple platform is configured to ingest authentication logs from the RADIUS server. When a device authenticates to Corp-WiFi using an employee's credentials, and later authenticates to Guest-WiFi, the platform uses the shared identity credential to stitch the sessions together.
- Result: The facilities management team regains accurate visibility into space utilization across the entire campus, enabling data-driven decisions regarding real estate optimization.
Practice Questions
Q1. Your marketing team reports that a new promotional campaign launched last week drove a 300% increase in unique footfall to your flagship store. However, the store manager reports that the venue felt unusually quiet, and sales data shows a 5% decline. What is the most likely technical explanation for this discrepancy, and what is your immediate diagnostic step?
Hint: Consider what metric legacy analytics platforms use to count unique visitors and how modern mobile operating systems handle that identifier.
View model answer
The most likely explanation is that the legacy WiFi analytics platform is counting randomized MAC addresses as unique physical visitors. A recent OS update or a change in how devices behave in that specific RF environment has caused devices to rotate their MAC addresses more frequently. The platform sees multiple MACs from the same physical device and counts each as a separate unique person, leading to an artificially inflated footfall metric that does not correlate with actual physical presence or sales data. The immediate diagnostic step is to examine the raw MAC address logs and calculate the proportion of locally administered addresses (second least significant bit of the first octet set to 1). A high proportion confirms randomization is the cause. The solution is to transition to an identity-centric analytics model with a captive portal.
Q2. You are deploying a new guest WiFi network across a large hospital campus. The primary goal is to provide seamless connectivity for patients and visitors while gathering accurate data on dwell times in various waiting areas. You have a choice between an open network with no captive portal or a network requiring email authentication. Which approach do you recommend and why?
Hint: Think about the Identity Anchor principle and how MAC randomization affects long-term tracking without explicit authentication. Also consider GDPR implications of each approach.
View model answer
The network requiring email authentication via a captive portal is strongly recommended. An open network relies entirely on passive probe requests and MAC addresses for tracking. Due to MAC randomization, devices will appear as new visitors every time their MAC changes, completely breaking dwell time analytics and making it impossible to track a patient's journey across different waiting areas over time. By requiring email authentication, you establish a persistent Identity Anchor. The analytics platform can then use a device graph to link the user's email to whatever randomized MAC they are currently using, ensuring accurate dwell time and journey tracking across the campus. From a GDPR perspective, the captive portal also provides a clear consent mechanism, which is legally required when collecting personal data. The open network approach, while seemingly less intrusive, actually creates a more complex compliance situation as it relies on probabilistic tracking without explicit consent.
Q3. A stadium IT director wants to track the movement of VIP guests to optimize staffing in premium lounges. They are currently using a system that relies on signal fingerprinting (RSSI patterns) because they want to avoid forcing VIPs to use a captive portal. The data is proving to be highly inaccurate. What is the architectural flaw in this approach, and what is the recommended solution that maintains a premium user experience?
Hint: Consider the deterministic versus probabilistic nature of different tracking methods in a high-density, complex RF environment like a stadium.
View model answer
The architectural flaw is relying on probabilistic signal fingerprinting as the primary identification method in a complex, high-density RF environment like a stadium. Signal fingerprinting is imprecise; RSSI values fluctuate wildly due to physical obstructions (crowds, concrete, steel), device orientation, and competing RF sources. When combined with MAC randomization, the system cannot reliably stitch together fragmented sessions, producing inaccurate journey data. The director must implement a deterministic Identity Anchor. To maintain a premium, frictionless experience for VIPs, the recommended solution is to integrate the WiFi authentication with the VIP ticketing or access management app using a technology like Passpoint (Hotspot 2.0 / IEEE 802.11u). This allows the device to authenticate automatically and silently based on the VIP's profile credentials, providing accurate, deterministic tracking without requiring a manual captive portal login. This delivers the premium experience the director requires while restoring data integrity.