How to Stop Bandwidth Hogging on Public WiFi
This guide provides a technical blueprint for IT leaders to implement intelligent DNS filtering on public WiFi networks. By blocking ad networks and telemetry at the edge, venues can reclaim up to 40% of wasted bandwidth and improve the guest experience without relying on blunt rate-limiting.
- Executive Summary
- Technical Deep-Dive
- The Limitations of Rate-Limiting
- Intelligent DNS Filtering Architecture
- Standards Alignment and Compliance
- Mitigating DNS over HTTPS (DoH) Bypass
- Implementation Guide
- Phase 1: Audit and Baseline
- Phase 2: Policy Design
- Phase 3: Pilot Deployment
- Phase 4: Full Rollout and Lifecycle Management
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
Public WiFi networks are under unprecedented strain. As device density increases and applications become more bandwidth-intensive, IT teams frequently default to rate-limiting to maintain stability. However, traffic analysis across enterprise deployments reveals that up to 40% of outbound guest bandwidth is consumed by background telemetry, ad network CDNs, and tracking pixels rather than legitimate user activity.
This guide explores a more intelligent approach: deploying DNS filtering at the network edge to block high-bandwidth, non-user-facing traffic before a connection is even established. Unlike blunt rate-limiting, this strategy improves the user experience while significantly reducing WAN uplink saturation. We detail the technical architecture, implementation phasing, and business case for transitioning from legacy traffic shaping to intelligent, policy-driven DNS control. For operators in Hospitality , Retail , and Transport , this represents a critical optimisation strategy for 2026.
Technical Deep-Dive
The Limitations of Rate-Limiting
Traditional network optimisation relies heavily on traffic shaping and per-client rate limits. While effective at preventing a single user from saturating an uplink, rate-limiting fails to address the composition of the traffic itself. When a client is throttled to 5 Mbps, the network treats a background telemetry upload with the same priority as a VoIP call. The result is degraded performance for legitimate applications, leading to poor user experience scores.
Intelligent DNS Filtering Architecture
A more effective approach intercepts traffic at the DNS layer. Before a device can initiate a TCP connection to an ad network or tracking pixel, it must resolve the domain name. By routing all guest DNS queries through an intelligent filtering resolver, IT teams can enforce policies that return a null response (NXDOMAIN or a block page IP) for categorised domains.
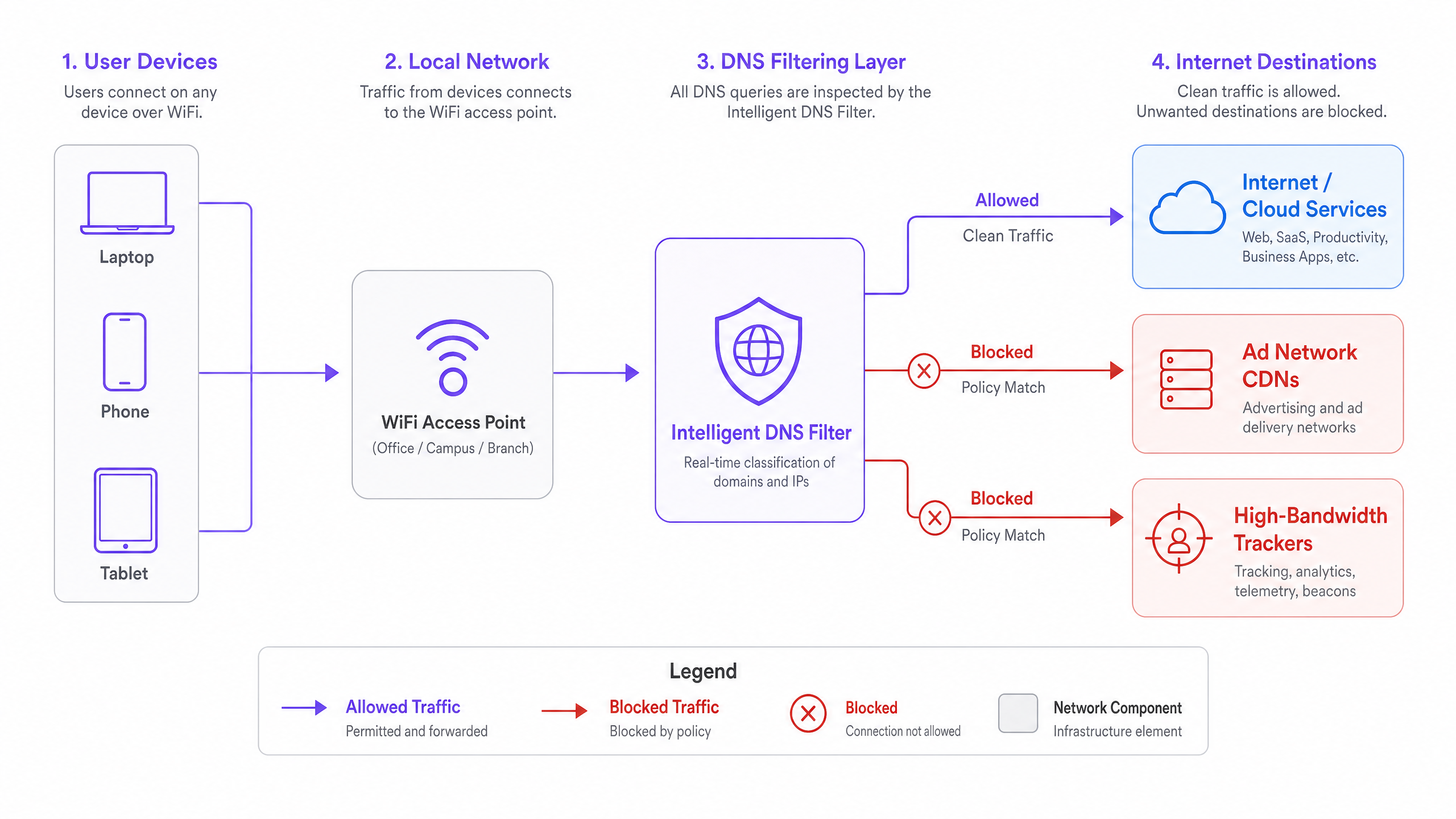
This architecture provides several distinct advantages:
- Zero Payload Transfer: Because the connection is never established, zero bandwidth is consumed by the blocked service.
- Reduced AP Contention: Fewer connections mean less airtime utilisation and lower collision rates in high-density environments.
- Improved Page Load Times: Without the overhead of loading dozens of third-party tracking scripts, legitimate web content renders faster on the client device.
Standards Alignment and Compliance
Implementing DNS filtering aligns strongly with enterprise security and compliance frameworks. From a GDPR perspective, blocking third-party tracking domains on Guest WiFi serves as a proactive data minimisation control. For PCI DSS environments, it strengthens network segmentation by preventing guest devices from reaching known malicious or compromised infrastructure.
Furthermore, as networks migrate to WPA3 for enhanced encryption, DNS filtering ensures that the control plane remains visible and manageable, even when the underlying payload is encrypted via TLS 1.3. For more insights on security compliance, see our guide on Explain what is audit trail for IT Security in 2026 .
Mitigating DNS over HTTPS (DoH) Bypass
A critical technical challenge in modern deployments is the proliferation of DNS over HTTPS (DoH). Modern operating systems and browsers increasingly attempt to bypass local DHCP-assigned resolvers by tunnelling DNS queries over port 443 to public resolvers (e.g., 8.8.8.8, 1.1.1.1). To maintain policy enforcement, network architects must implement Layer 4 firewall rules that block outbound traffic to known DoH provider IPs on the guest VLAN, forcing clients to fall back to the local filtering resolver.
Implementation Guide
Deploying DNS filtering across a distributed enterprise requires a phased, methodical approach to minimise false positives and ensure seamless integration with existing infrastructure.
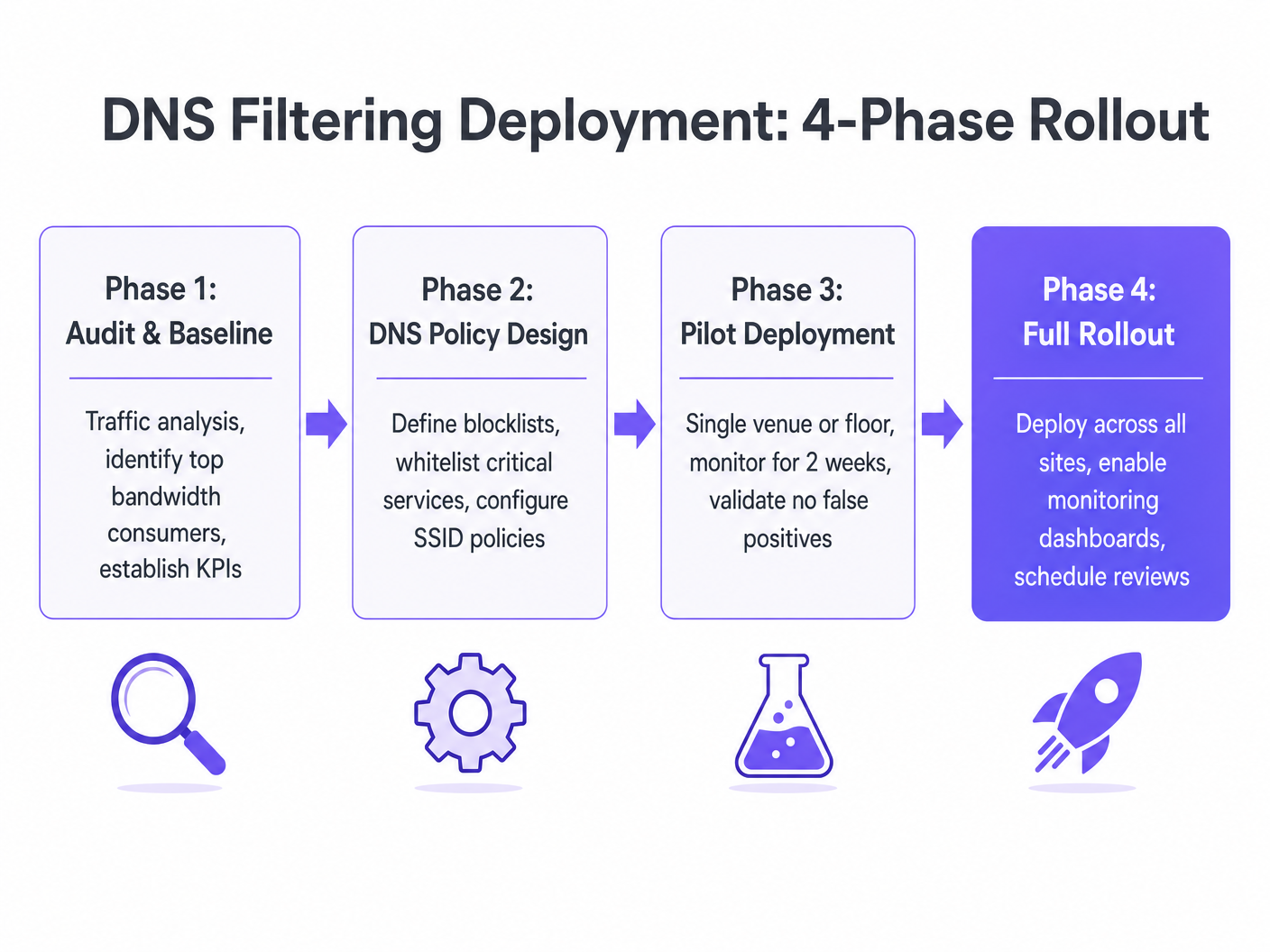
Phase 1: Audit and Baseline
Before implementing any blocking policies, deploy a traffic analysis tool to monitor the existing environment for 14 days. Identify the top bandwidth-consuming domains and categorise them. This baseline is essential for measuring the ROI of the deployment and understanding the specific traffic profile of your venues.
Phase 2: Policy Design
Based on the audit data, define the blocking categories. Core recommendations include:
- Advertising Networks and CDNs
- Tracking and Telemetry Infrastructure
- Known Malware and Phishing Domains
Ensure that critical services, such as captive portal authentication domains and payment gateways, are explicitly whitelisted. For venues utilising advanced analytics, ensure that platforms like WiFi Analytics are permitted.
Phase 3: Pilot Deployment
Select a representative pilot site—such as a single hotel property or a high-traffic retail location. Apply the policy to the guest SSID and monitor for 14 days. Key metrics to track include:
- Reduction in total outbound bandwidth
- False positive reports (legitimate services breaking)
- Helpdesk ticket volume related to WiFi performance
Phase 4: Full Rollout and Lifecycle Management
Upon successful pilot validation, deploy the policy globally. Crucially, establish a quarterly review cycle to update custom whitelists and revview category definitions, as the ad-tech landscape evolves rapidly.
Best Practices
- Communicate the Change: While guest communication is rarely necessary, ensure that venue operations and IT helpdesk teams are aware of the new filtering policies to aid in troubleshooting.
- Start Conservative: Begin by blocking only the most egregious bandwidth hogs (e.g., video ad networks). Gradually expand the policy as confidence in the whitelist grows.
- Leverage Vendor Intelligence: Do not attempt to maintain blocklists manually. Utilise a DNS filtering provider that offers dynamic, real-time domain categorisation.
- Monitor the Edge: For further reading on edge optimisation, see Improving WiFi Speeds by Blocking Ad Networks at the Edge .
Troubleshooting & Risk Mitigation
The primary risk associated with DNS filtering is the false positive—blocking a domain that is required for a legitimate application to function. This often occurs with shared CDNs that host both advertising assets and core application scripts.
Failure Mode: A guest complains that a specific airline booking app is failing to load on the hotel WiFi. Mitigation: The IT team must have access to a real-time DNS query log to identify the blocked domain associated with the app. Once identified, the domain is added to the global whitelist, and the policy is pushed to all edge resolvers within minutes.
Failure Mode: Tech-savvy users bypass the filter using DoH or custom DNS settings. Mitigation: Enforce strict egress firewall rules on the guest VLAN, permitting outbound DNS (port 53) only to the approved filtering resolver and blocking known DoH endpoints.
ROI & Business Impact
The business case for intelligent DNS filtering is compelling and highly measurable. Venue operators typically observe a 25% to 40% reduction in total outbound bandwidth consumption on guest networks.
This reduction translates into several tangible benefits:
- Deferred CapEx: By reclaiming wasted bandwidth, organisations can defer costly WAN circuit upgrades.
- Improved User Experience: Reduced AP contention and faster page load times directly correlate with higher guest satisfaction scores.
- Enhanced Security Posture: Proactive blocking of malicious domains reduces the risk of malware propagation on the guest network.
For public-sector organisations looking to optimise their infrastructure, this approach aligns with broader digital inclusion goals, as discussed in our recent announcement: Purple Appoints Iain Fox as VP Growth – Public Sector to Drive Digital Inclusion and Smart City Innovation .
Listen to our full briefing on this topic below: {{asset:how_to_stop_bandwidth_hogging_on_public_wifi_podcast.wav}}
Key Definitions
DNS Filtering
The practice of using the Domain Name System to block malicious or inappropriate websites by returning a null IP address for categorized domains.
Used by IT teams to proactively manage traffic composition and security at the network edge.
Rate-Limiting
A network control mechanism that restricts the maximum bandwidth available to a specific client or application.
A legacy approach to bandwidth management that often degrades user experience by throttling legitimate and wasteful traffic equally.
DNS over HTTPS (DoH)
A protocol for performing remote DNS resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
A significant challenge for network administrators as it bypasses local, unencrypted DNS filtering controls.
False Positive (DNS)
When a legitimate, required domain is incorrectly categorized and blocked by the DNS filtering policy.
The primary operational risk when deploying DNS filtering; mitigated through careful auditing and whitelisting.
Telemetry Data
Automated communications process by which measurements and other data are collected at remote or inaccessible points and transmitted to receiving equipment for monitoring.
In the context of public WiFi, background app telemetry consumes significant bandwidth without providing immediate value to the user.
NXDOMAIN
A DNS message indicating that the requested domain name does not exist.
The standard response returned by a DNS filter when a client attempts to resolve a blocked domain.
Network Segmentation
The practice of splitting a computer network into subnetworks, each being a network segment.
A core PCI DSS requirement; DNS filtering aids segmentation by preventing guest devices from reaching untrusted external infrastructure.
Content Delivery Network (CDN)
A geographically distributed network of proxy servers and their data centers.
Ad networks use CDNs to serve high-bandwidth media. Blocking these specific CDNs reclaims significant WAN capacity.
Worked Examples
A 300-room hotel is experiencing severe WAN link saturation during peak evening hours (7 PM - 10 PM). The IT team currently enforces a 5 Mbps rate limit per device, but guest complaints regarding video streaming buffering persist. How should the network architect address this?
- Deploy a traffic analysis tool to baseline the current traffic profile. 2. Implement a cloud-based DNS filtering resolver and configure the guest DHCP scope to distribute its IP. 3. Apply a policy blocking 'Advertising' and 'Tracking' categories. 4. Implement Layer 4 firewall rules on the guest VLAN to block outbound port 53 to any IP other than the approved resolver, and block known DoH provider IPs.
A retail chain wants to deploy DNS filtering across 50 locations but is concerned about breaking their own branded mobile app, which relies on several third-party analytics SDKs for crash reporting.
- Conduct a controlled audit of the mobile app's DNS queries in a lab environment. 2. Identify all domains required for the app's core functionality and crash reporting. 3. Create a custom whitelist policy that explicitly permits these specific domains. 4. Deploy the filtering policy to a single pilot store for 14 days, monitoring the app's performance and crash reporting dashboard before rolling out to the remaining 49 locations.
Practice Questions
Q1. A stadium IT director notices that during halftime, the guest WiFi uplink is completely saturated. Rate-limiting is already set to 2 Mbps per client. What is the most effective next step to improve performance for users trying to access the stadium's ordering app?
Hint: Consider what type of traffic is likely consuming the bandwidth despite the rate limit.
View model answer
Implement DNS filtering to block high-bandwidth ad networks and background telemetry. Because rate-limiting only throttles traffic, a large volume of background requests can still saturate the uplink. DNS filtering prevents these connections from initiating, freeing up capacity for the legitimate stadium ordering app.
Q2. After deploying a DNS filtering solution, the helpdesk receives reports that a popular social media application is failing to load images on the guest network. How should the network engineer troubleshoot this?
Hint: Think about how CDNs are utilized by large applications.
View model answer
The engineer should review the DNS query logs for the affected client devices. It is likely that the social media app uses a CDN domain that has been incorrectly categorized as an 'Advertising Network' by the filter. Once the specific CDN domain is identified, it should be added to the global whitelist.
Q3. A new corporate policy mandates the use of DNS filtering on all guest networks. However, traffic analysis shows that 15% of guest devices are still successfully reaching known ad networks. What is the most likely cause of this bypass, and how can it be prevented?
Hint: Consider modern browser features that encrypt DNS queries.
View model answer
The devices are likely using DNS over HTTPS (DoH) to bypass the local DHCP-assigned resolver and query public resolvers directly. To prevent this, the IT team must implement Layer 4 egress firewall rules on the guest VLAN to block outbound traffic to known DoH provider IP addresses, forcing clients to fall back to the local filtering resolver.