How to Build a Customer Experience Strategy
This technical reference guide provides a practical framework for IT leaders, network architects, and venue operations directors on how to build a data-driven customer experience strategy. It covers the full architecture from guest WiFi authentication and captive portal design through to spatial analytics, CRM integration, and measurable ROI — with concrete implementation scenarios drawn from hospitality, retail, and public-sector environments. Purple's guest WiFi and analytics platform is positioned throughout as the enabling infrastructure layer.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Architecting the CX Data Foundation
- Authentication and Data Capture Mechanisms
- Location Analytics and Behavioural Tracking
- Implementation Guide: Deploying the Strategy
- Phase 1: Infrastructure Assessment and RF Design
- Phase 2: Captive Portal Configuration and CRM Integration
- Phase 3: Analytics Baseline and Audience Segmentation
- Phase 4: Activation and Personalisation
- Best Practices for Enterprise Deployments
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For enterprise IT leaders and venue operations directors, building a customer experience (CX) strategy is no longer solely the domain of marketing. As physical venues — from retail chains to large-scale stadiums — become increasingly digitised, the underlying network infrastructure is the primary engine for customer data acquisition. This guide details how to architect a CX strategy that leverages existing wireless infrastructure to capture actionable intelligence, automate engagement, and deliver measurable return on investment.
By deploying a robust Guest WiFi solution, organisations can transform an operational cost centre into a strategic asset. A successful CX strategy relies on seamless data collection, rigorous compliance (including GDPR and PCI DSS), and integration with existing CRM and marketing automation platforms. This document provides a vendor-neutral, technical framework for designing, implementing, and scaling a data-driven customer experience architecture across Hospitality , Retail , Healthcare , and Transport environments.
Technical Deep-Dive: Architecting the CX Data Foundation
The foundation of any modern CX strategy in a physical venue is the ability to reliably identify and track users across their visit lifecycle. This requires a robust network architecture capable of handling high concurrent device counts while seamlessly routing authentication traffic to a captive portal or identity provider.
Authentication and Data Capture Mechanisms
When a user associates with the guest SSID, the access point (AP) or wireless LAN controller (WLC) intercepts the HTTP/HTTPS request and redirects it to a captive portal. This portal serves as the primary data ingestion point — the digital threshold between anonymous visitor and identified customer.
Standard deployment models utilise RADIUS (Remote Authentication Dial-In User Service) for authentication, authorisation, and accounting (AAA). When integrating with platforms like Purple's WiFi Analytics , the captive portal requests specific user attributes — email address, demographic data, or social login tokens — before granting network access via a RADIUS Access-Accept message. The data is simultaneously written to the analytics platform's customer database and, via API webhook, to the connected CRM.
For advanced deployments, technologies like Passpoint (Hotspot 2.0) and OpenRoaming allow for seamless, secure onboarding using IEEE 802.1X and WPA3 Enterprise encryption. Purple acts as a free identity provider for OpenRoaming under the Connect licence, enabling automatic authentication without repetitive captive portal interactions — significantly reducing friction while maintaining secure data attribution for returning visitors.
Location Analytics and Behavioural Tracking
Beyond initial authentication, continuous spatial analytics are critical for understanding the full customer journey within the venue. This is achieved by tracking the Received Signal Strength Indicator (RSSI) of both unassociated probe requests and associated client traffic across multiple APs.
By triangulating these signals, the network calculates dwell times, identifies high-traffic zones, and maps typical visitor flow patterns. For more granular accuracy, deployments may integrate Bluetooth Low Energy (BLE) beacons or Ultra-Wideband (UWB) sensors alongside the WiFi layer, as detailed in the Indoor Positioning System: UWB, BLE, & WiFi Guide . This spatial data is then aggregated and visualised through heatmaps and journey flows, providing the empirical evidence required to optimise physical layouts, staffing models, and in-venue marketing placement.

Implementation Guide: Deploying the Strategy
Implementing a WiFi-driven CX strategy requires cross-functional alignment between IT, marketing, and operations. The deployment should follow a phased approach to ensure infrastructure stability, data integrity, and measurable outcomes at each stage.
Phase 1: Infrastructure Assessment and RF Design
Before deploying analytics overlays, the underlying RF (Radio Frequency) environment must support high-density client loads. Conduct both predictive and active site surveys to guarantee adequate signal coverage — typically -65 dBm or better at the client device — and sufficient AP capacity. For complex or specialised environments such as automotive showrooms, refer to the Wi Fi in Auto: The Complete 2026 Enterprise Guide for deployment-specific guidance.
Key infrastructure parameters to validate before proceeding:
| Parameter | Minimum Threshold | Notes |
|---|---|---|
| Signal Coverage | -65 dBm | At client device height |
| AP-to-Client Ratio | 1:25 (dense) | Adjust for event venues |
| Channel Utilisation | <60% | Per AP, 2.4 GHz and 5 GHz |
| Captive Portal Latency | <500ms | Redirect response time |
| RADIUS Round-Trip | <100ms | Authentication response |
Phase 2: Captive Portal Configuration and CRM Integration
The captive portal must balance data acquisition with user experience. Implement progressive profiling — requesting minimal data during the first visit and incrementally gathering additional attributes on subsequent logins. A well-optimised portal should achieve a login conversion rate of 40-60% of total venue visitors.
Ensure seamless API integration between the WiFi analytics platform and the corporate CRM (Salesforce, HubSpot, Microsoft Dynamics, or equivalent). This enables real-time data synchronisation and automated marketing triggers based on physical presence — for example, dispatching a personalised welcome message when a loyalty programme member enters a retail environment, or triggering a post-visit satisfaction survey 30 minutes after departure.
For retail-specific data collection strategies, the How to Collect Customer Data In-Store: A Retailer's Guide provides a detailed operational framework.
Phase 3: Analytics Baseline and Audience Segmentation
Once data is flowing, establish baseline metrics for visitor capture rates, average dwell times, and repeat visit frequencies over a minimum 30-day period. Use this data to construct segmented audience profiles. In a hospitality context, for example, you might segment users into Business Travellers (short dwell times, high visit frequency, weekday-dominant) and Leisure Guests (extended dwell times, low visit frequency, weekend-dominant), tailoring digital communications and in-venue experiences accordingly.
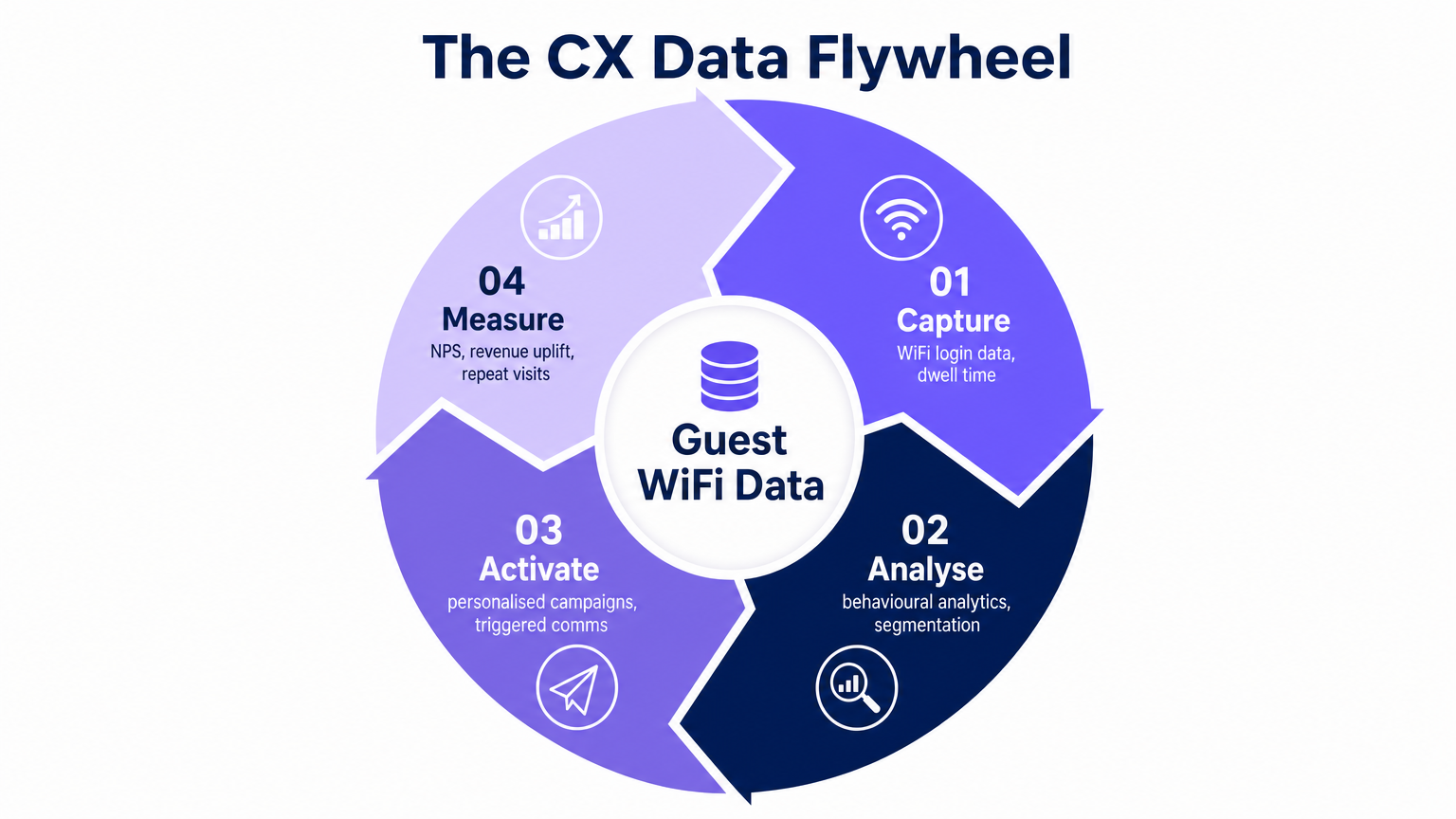
Phase 4: Activation and Personalisation
With segmented profiles established, activate the data through targeted communications and in-venue personalisation. Triggered email sequences, SMS campaigns, and app push notifications can all be driven by physical presence events detected by the WiFi infrastructure. The IoT integration layer that underpins this activation is covered in depth in the Internet of Things Architecture: A Complete Guide .
Best Practices for Enterprise Deployments
Prioritise Privacy and Compliance by Design. All data collection mechanisms must explicitly request user consent in accordance with GDPR, CCPA, and applicable local privacy regulations. Implement MAC address anonymisation for unauthenticated probe requests at the network edge — on the AP or WLC — before any data reaches the analytics platform. Consent records must be stored with timestamps and version references to the specific privacy notice presented.
Optimise for Mobile-First Authentication. The captive portal and all subsequent digital interactions must be flawlessly responsive across iOS and Android. Latency during the authentication process directly correlates with abandonment rates. Target a portal load time of under two seconds on a 4G connection.
Align IT and Marketing KPIs. IT is accountable for network uptime, throughput, and authentication latency. Marketing is accountable for data capture rates and campaign performance. A successful CX strategy requires shared objectives — metrics such as WiFi Capture Rate (percentage of venue visitors who authenticate), Cost per Identified Visitor, and Repeat Visit Rate bridge the two functions.
Segment Your Network Architecture Correctly. The guest WiFi network must be logically isolated from the corporate LAN using VLANs and strict stateful firewall rules. This is a PCI DSS requirement in retail and hospitality environments where payment card data is processed on the same site. Regular penetration testing of the network boundary is essential.
Troubleshooting & Risk Mitigation
Deploying a comprehensive CX analytics platform introduces specific failure modes that IT teams must anticipate and mitigate proactively.
Low Capture Rates (below 20%). If the percentage of visitors authenticating to the WiFi is low, the primary cause is almost always captive portal friction. Audit the portal UX: reduce the number of required fields to one on the first visit, add social login options (Google, Apple, Facebook), and ensure the value exchange — fast, reliable internet access in exchange for an email address — is clearly communicated on the splash page.
Inaccurate Location Data. RSSI-based location tracking is susceptible to RF attenuation from physical obstacles (concrete walls, metal shelving, glass partitions) and multipath interference in complex indoor environments. Calibrate the RF model regularly and consider supplementing WiFi positioning with BLE beacons in high-value analytics zones such as product displays or service counters.
Integration Pipeline Failures. API rate limits or schema mismatches between the WiFi analytics platform and the CRM are a common source of data loss. Implement idempotent webhook handling, dead-letter queues for failed events, and automated alerting when the event pipeline falls below expected throughput thresholds.
Security Boundary Breaches. Misconfigured VLANs or firewall rules can inadvertently expose the corporate network to guest traffic. Conduct quarterly network segmentation audits and ensure all inter-VLAN routing is explicitly denied at the firewall by default, with only required outbound internet access permitted for the guest SSID.
ROI & Business Impact
The ultimate measure of a CX strategy is its impact on commercial outcomes. By digitising the physical space, organisations can apply the analytical rigour of e-commerce to brick-and-mortar operations.
| Metric | Typical Baseline | Post-Deployment Target | Measurement Method |
|---|---|---|---|
| WiFi Capture Rate | 10-15% | 40-60% | Analytics platform |
| Repeat Visit Rate | Unmeasured | +15-25% uplift | CRM attribution |
| Email Open Rate | Industry avg 20% | 35-45% (location-triggered) | Marketing platform |
| Ancillary Revenue per Visit | Baseline | +8-12% uplift | POS integration |
| Staff Deployment Efficiency | Manual scheduling | Demand-driven (dwell data) | Operations dashboard |
Customer Lifetime Value (CLV) Uplift. Personalised engagements driven by location and behavioural data increase repeat visit rates and average transaction values. Organisations that deploy triggered, presence-based communications consistently report CLV uplifts of 10-20% within the first year of deployment.
Operational Efficiency Gains. Heatmaps and dwell time data enable demand-driven staff allocation, reducing labour costs during off-peak periods and improving service quality during peak demand. In a stadium context, this translates directly to reduced queue times and higher per-head concession spend.
Marketing Attribution Accuracy. By correlating physical visit events with digital campaign exposure, marketing teams can measure the offline impact of online spend with a precision previously only available to pure-play e-commerce operators. This moves the conversation from proxy metrics (impressions, clicks) to concrete commercial outcomes (store visits, transaction uplift).
Key Terms & Definitions
Captive Portal
A web page that a user of a public-access network is required to interact with before internet access is granted. It serves as the primary data ingestion point in a guest WiFi deployment.
IT teams encounter this as the first digital touchpoint in the physical venue. Portal design directly determines WiFi capture rates and data quality.
RSSI (Received Signal Strength Indicator)
A measurement of the power level of a received radio signal, expressed in dBm. Used by analytics platforms to estimate the distance between a client device and an access point.
The foundational input for location analytics and zone-based dwell time measurement. Accuracy is typically 3-10 metres in a well-designed RF environment.
OpenRoaming
A global roaming federation service, built on Passpoint (IEEE 802.11u/Hotspot 2.0), that enables automatic and secure WiFi onboarding without captive portal interactions.
Critical for reducing login friction for returning visitors while maintaining secure identity attribution. Purple provides a free identity provider service for OpenRoaming under the Connect licence.
MAC Address Anonymisation
The process of cryptographically hashing a device's Media Access Control address before storage, preventing the identification of individual devices from the stored data.
A mandatory GDPR compliance step when tracking unauthenticated devices via probe requests. Must be implemented at the network edge, not in the analytics database.
Dwell Time
The duration of time a device remains within a specific defined zone or venue, measured from first detection to last detection within that zone.
A primary operational metric for measuring engagement, identifying queue bottlenecks, and optimising staff deployment. Typically measured in minutes.
Progressive Profiling
A data collection methodology that gathers customer attributes incrementally across multiple interactions, rather than requesting all information at a single point.
The standard best practice for captive portal design. Reduces initial login friction while building comprehensive customer profiles over time.
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance certification programme based on IEEE 802.11u that enables seamless, secure roaming between Wi-Fi networks using WPA2/WPA3 Enterprise authentication.
Provides enterprise-grade security for guest networks and automates the authentication process for returning users, eliminating repetitive captive portal interactions.
WiFi Capture Rate
The percentage of total venue visitors who successfully authenticate to the guest WiFi network, providing a consented identity record.
The primary KPI for measuring the effectiveness of the captive portal and the health of the first-party data pipeline. Industry benchmarks range from 15% (poor) to 60%+ (optimised).
Spatial Analytics
The analysis of location-based data to understand movement patterns, zone utilisation, and spatial relationships within a physical environment.
Enables venue operators to visualise customer journeys, measure zone conversion rates, and make evidence-based decisions about physical layout and resource allocation.
Case Studies
A 200-room hotel is experiencing low guest WiFi adoption rates — under 15% of guests are logging in — and is failing to capture sufficient first-party data to support a new loyalty programme initiative. The hotel uses a legacy captive portal with a six-field registration form.
Step 1 — Diagnose the Friction Point: Pull the captive portal analytics to identify the drop-off rate at each form field. In most cases, the majority of abandonment occurs after the second or third required field. Step 2 — Streamline Authentication: Replace the six-field form with a single-click social login (Google, Apple, or Facebook OAuth) as the primary option, with email-only as a secondary option. This reduces the time-to-internet from 45-60 seconds to under 10 seconds. Step 3 — Implement Progressive Profiling: Configure the analytics platform to request only the email address on the first visit. On the second visit, display a prompt offering 500 loyalty points in exchange for a phone number. On the third visit, request a date of birth for a birthday reward. Step 4 — Deploy OpenRoaming for Returning Guests: For guests who have previously authenticated, configure Passpoint/OpenRoaming so their device reconnects automatically on future visits without seeing the captive portal, while still attributing the visit to their profile. Step 5 — Measure and Iterate: Track the WiFi Capture Rate weekly. Target 40% within 60 days of deployment.
A large retail chain wants to measure the commercial effectiveness of a new store layout in driving traffic to a high-margin accessories display area, and needs to justify the capital expenditure on the refit to the board.
Step 1 — Define the Analytics Zone: Within the WiFi analytics platform, draw a geofence around the accessories display area. Ensure AP coverage within the zone is sufficient for accurate RSSI triangulation (minimum two APs with clear line of sight). Step 2 — Establish a Pre-Refit Baseline: Over a 30-day period before the layout change, measure: Zone Conversion Rate (percentage of total store visitors who enter the accessories zone), Average Dwell Time within the zone, and Bounce Rate (visitors who enter and leave within under 30 seconds). Step 3 — Implement the Layout Change. Step 4 — Measure Post-Refit Performance: Over the equivalent 30-day period post-refit, collect the same metrics. Step 5 — Correlate with POS Data: Integrate the WiFi analytics platform with the POS system to correlate zone dwell time with accessories transaction volume. Calculate the incremental revenue attributable to the layout change. Step 6 — Calculate ROI: Divide the incremental annual revenue by the refit capital cost to produce a payback period for the board presentation.
Scenario Analysis
Q1. A stadium IT director wants to track queue times at concession stands in real time to dynamically deploy additional staff during peak periods. The venue has standard WiFi coverage across the concourse. What is the most appropriate technological approach, and what are the limitations of relying solely on WiFi RSSI data for this use case?
💡 Hint:Consider the accuracy requirements for measuring a dense, slow-moving queue versus general concourse crowd flow. What is the typical RSSI accuracy range, and is it sufficient for distinguishing a 2-metre queue from a 5-metre queue?
Show Recommended Approach
Standard WiFi RSSI tracking provides positional accuracy of approximately 3-10 metres in a well-calibrated indoor environment, which is insufficient for precise queue length measurement at a concession stand. The recommended approach is to supplement the WiFi infrastructure with either: (a) BLE beacons mounted directly above each concession counter, providing sub-2-metre accuracy for devices within the queue zone; or (b) overhead stereoscopic cameras with computer vision analytics for people-counting independent of device presence. The WiFi layer remains valuable for macro-level concourse crowd density and flow direction, while the supplementary technology handles the precision queue measurement use case. The integration point is the analytics platform, which should aggregate both data streams into a unified operational dashboard.
Q2. The marketing team at a retail chain wants to send a personalised push notification to a high-value loyalty member the moment they enter the store, before they have interacted with any staff. The current deployment uses a standard captive portal that takes approximately 45 seconds to complete. How should the IT team architect a solution that delivers a sub-10-second entry notification?
💡 Hint:The captive portal authentication flow is too slow for an immediate entry notification. What authentication mechanism eliminates the portal interaction for returning users while still attributing the visit to their identity?
Show Recommended Approach
The solution requires implementing Passpoint/OpenRoaming for returning loyalty members. The workflow is: (1) On the member's first visit, they complete the standard captive portal and their device credentials are provisioned for Passpoint. (2) On all subsequent visits, the device automatically authenticates via 802.1X/WPA3 Enterprise without displaying the captive portal, completing the authentication handshake in under 2 seconds. (3) The WiFi analytics platform detects the association event and identifies the user via their provisioned identity token. (4) A real-time webhook fires to the marketing automation platform, which dispatches the push notification within 5-8 seconds of the device entering the RF coverage zone. The key architectural requirement is that the loyalty app must have push notification permissions enabled, and the member's device must have the Passpoint profile installed — typically achieved via the loyalty app onboarding flow.
Q3. During a routine network audit at a multi-site retail operator, it is discovered that the guest WiFi analytics platform has been storing raw, unhashed MAC addresses from unauthenticated probe requests for the past 18 months across all 47 stores. What is the primary regulatory risk, what is the immediate remediation action, and what architectural change is required to prevent recurrence?
💡 Hint:Consider the GDPR classification of MAC addresses and the territorial scope of the regulation. What constitutes a 'personal data breach' under Article 33?
Show Recommended Approach
The primary risk is a material GDPR violation under Article 5(1)(b) (purpose limitation) and Article 5(1)(e) (storage limitation), as raw MAC addresses are classified as personal data under Recital 30 of the GDPR. The 18-month retention of unauthenticated probe data without a lawful basis or consent constitutes unlawful processing. Immediate remediation: (1) Notify the Data Protection Officer and conduct a Data Protection Impact Assessment (DPIA). (2) Assess whether the breach meets the Article 33 threshold for supervisory authority notification (within 72 hours if there is a risk to individuals' rights). (3) Purge all stored raw MAC addresses from the analytics database immediately. Architectural remediation: Configure the analytics platform or WLC to apply a SHA-256 hash with a rotating salt to all MAC addresses at the point of capture — on the AP or controller — before any data is transmitted to the analytics platform. This ensures that no raw MAC address ever enters the data pipeline, making the stored data non-personal by design. Implement a 90-day maximum retention policy for anonymised probe data, enforced by automated database purge jobs.



