How to Use WiFi Analytics to Improve Customer Experience
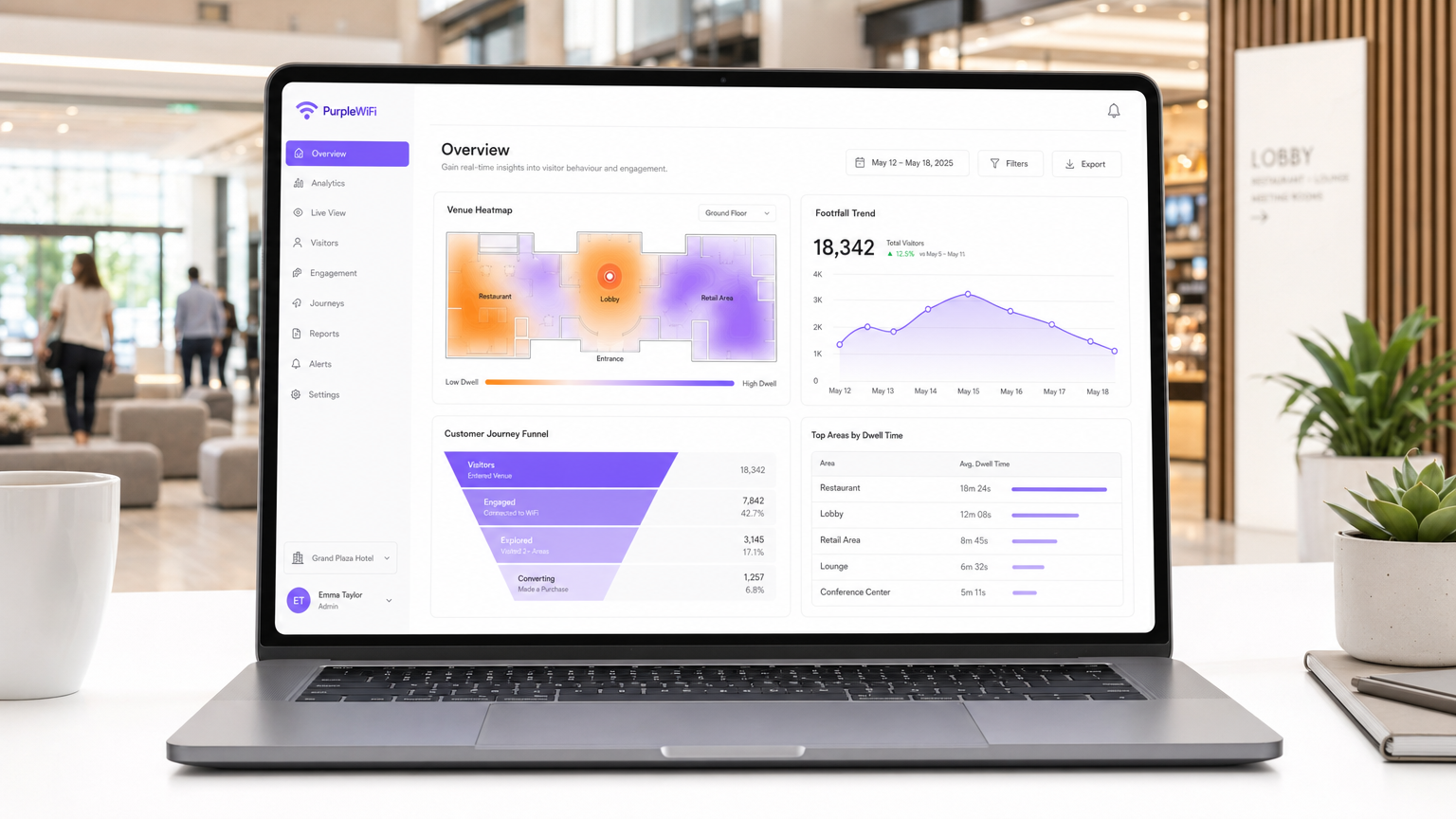
This authoritative guide shows IT managers, network architects, and venue operations directors how to transform guest WiFi into a customer experience engine by capturing footfall, dwell time, and behavioural data. It covers the full technical architecture — from probe-request capture and trilateration to captive portal authentication and CRM integration — alongside practical deployment guidance, GDPR compliance requirements, and measurable ROI frameworks. Real-world scenarios from retail and hospitality demonstrate how WiFi analytics data translates directly into layout optimisation, dynamic staffing, and personalised loyalty engagement.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: How WiFi Analytics Works
- Data Capture Mechanisms
- The Authentication Layer: From Anonymous to Known
- Data Processing and Integration
- Implementation Guide: Deploying for CX Impact
- Phase 1: Infrastructure Assessment
- Phase 2: Captive Portal Design and Consent
- Phase 3: Zone Definition and Mapping
- Phase 4: Integration and Activation
- Best Practices by Vertical
- Retail: Layout Optimisation and Conversion
- Hospitality: VIP Recognition and Personalisation
- Healthcare: Patient Flow and Wayfinding
- Transport: Real-Time Congestion Management
- Troubleshooting and Risk Mitigation
- MAC Randomisation
- Poor Location Accuracy
- Data Privacy and Compliance
- ROI and Business Impact
Executive Summary
For IT leaders, network architects, and venue operations directors, the guest WiFi network is no longer simply a cost centre or a basic amenity — it is a critical sensor network for physical spaces. By capturing and analysing data from device connections, organisations can answer the fundamental question of how to improve customer experience with WiFi. This guide provides an authoritative, vendor-neutral framework for deploying Guest WiFi and leveraging a WiFi Analytics platform to transform footfall, dwell time, and movement data into actionable business intelligence.
From dynamic staffing models in transport hubs to optimised floor layouts in retail chains and personalised loyalty recognition in hotels, the use cases are concrete and the ROI is measurable. The guide addresses the full deployment lifecycle: infrastructure assessment, captive portal design, zone mapping, CRM integration, and ongoing compliance with GDPR and IEEE 802.1X standards. Whether you are evaluating a first deployment or looking to extract more value from an existing network, this guide provides the technical depth and practical frameworks to make that decision this quarter.
Technical Deep-Dive: How WiFi Analytics Works
To understand how to measure customer experience through wireless networks, it is necessary to examine the underlying architecture of location-based services (LBS) and WiFi analytics from the ground up.
Data Capture Mechanisms
Every mobile device continuously broadcasts probe requests — signals sent out to discover available networks. Even before a user actively connects, your access points (APs) can detect the device's MAC address and its Received Signal Strength Indicator (RSSI). This passive detection is the foundation of presence analytics: knowing how many devices, and therefore how many people, are in your venue at any given moment.
When RSSI readings are combined across three or more APs, the analytics engine can calculate a device's approximate physical location through trilateration — the same geometric principle used by GPS, applied to your wireless infrastructure. In a properly deployed network, this achieves location accuracy of three to five metres, which is sufficient to determine whether a customer is in your restaurant, your electronics department, or your hotel lobby.
Location analytics extends this capability to track movement over time: which zones a device visits, in what sequence, and for how long. This produces the dwell time and customer journey data that directly informs CX decisions.

The Authentication Layer: From Anonymous to Known
Aggregate footfall data is operationally useful, but genuine CX personalisation requires resolving anonymous MAC addresses to verified user profiles. This is achieved through the authentication layer.
The captive portal is the traditional mechanism: a web page presented to users before network access is granted, where they exchange basic demographic data (email address, age, gender, marketing consent) for internet access. When a user completes this login, the anonymous MAC address is permanently tied to a known profile. Every subsequent visit, every zone traversal, and every dwell time measurement is now attributable to a real person.
For higher-friction environments where captive portals reduce adoption, Passpoint (Hotspot 2.0) — standardised under IEEE 802.11u — provides a cellular-like automatic authentication experience. The user's device connects seamlessly using credentials stored on the device, encrypted via WPA3 Enterprise. Platforms like Purple act as identity providers within this framework, enabling persistent, consent-driven identity resolution without requiring manual login at every visit. For a broader view of how connected device architectures underpin this, see our Internet of Things Architecture: A Complete Guide .
Data Processing and Integration
Raw probe data is inherently noisy. An enterprise-grade analytics engine must handle MAC randomisation filtering, session deduplication, and zone boundary calculations before generating reliable metrics. The processed data is then surfaced via APIs to downstream systems:
| Integration Target | Data Consumed | CX Action Enabled |
|---|---|---|
| CRM Platform | Visit frequency, dwell time, zone history | Profile enrichment, loyalty tier updates |
| Marketing Automation | Real-time location, consent flags | Triggered location-based campaigns |
| Operational Dashboard | Live footfall, zone density | Dynamic staffing, queue management |
| BI / Data Warehouse | Historical trends, cohort analysis | Layout optimisation, capacity planning |
Implementation Guide: Deploying for CX Impact
A successful WiFi analytics deployment requires structured planning across four phases.
Phase 1: Infrastructure Assessment
Before any software configuration, validate that your wireless infrastructure supports location analytics. This is not purely a coverage exercise — AP placement must be optimised for trilateration accuracy.
AP Density and Placement: For zone-level accuracy (3–5 metres), APs should be deployed with overlapping coverage in a staggered, triangular pattern. Avoid collinear placement along corridors — the "hallway effect" makes trilateration geometrically impossible and produces unreliable zone data. Perimeter APs are critical for defining the venue boundary and distinguishing internal visitors from passersby.
Controller Configuration: Ensure your WLAN controller supports continuous scanning and reporting of unassociated client data. Many enterprise controllers require specific licensing for location services — validate this before committing to a deployment timeline.
Phase 2: Captive Portal Design and Consent
The captive portal is your primary data collection touchpoint and your legal basis for processing personal data under GDPR.
Keep the login flow to three steps or fewer. Offer social login options (Google, Apple, Facebook) to reduce drop-off rates — venues typically see 40–60% higher completion rates with social login versus email-only forms. The privacy notice must clearly state what data is collected, the purpose of processing, retention periods, and how users can exercise their rights. Obtain explicit opt-in consent for marketing communications as a separate, unchecked checkbox.
Phase 3: Zone Definition and Mapping
Map your venue into logical analytics zones that correspond to real business decisions. A retail environment might define zones by product category; a hospital by department; a stadium by concourse section. Zone boundaries should reflect the physical layout and the AP coverage map — not arbitrary administrative divisions.
For more granular indoor positioning requirements, particularly in complex multi-floor environments, consider supplementing WiFi analytics with BLE beacons or UWB anchors. See our Indoor Positioning System: UWB, BLE, & WiFi Guide for a detailed comparison of technologies.
Phase 4: Integration and Activation
Connect the analytics platform to your broader technology stack via REST APIs or native connectors. The key integrations are CRM (for profile enrichment), marketing automation (for triggered campaigns), and operational dashboards (for real-time staffing decisions). Define the specific CX use cases each integration will serve before go-live — this prevents the common failure mode of deploying a platform that generates data nobody acts on.

Best Practices by Vertical
The principles of WiFi analytics are consistent, but the CX applications vary significantly by industry.
Retail: Layout Optimisation and Conversion
For Retail environments, the primary use cases are zone traffic analysis, dwell time benchmarking, and repeat visit tracking. Identify "cold zones" — areas with low footfall relative to their floor space — and correlate them with product category performance. Use dwell time data to evaluate whether promotional displays are generating engagement or simply occupying space. Track the repeat visit rate of authenticated users as a proxy for loyalty programme effectiveness.
Hospitality: VIP Recognition and Personalisation
In Hospitality , recognising returning guests before they reach the front desk is a high-impact CX differentiator. When a loyalty member's device connects to the hotel's perimeter WiFi, an API webhook can trigger an alert on the concierge's operational dashboard — surfacing the guest's profile, preferences, and stay history before any verbal interaction occurs. This transforms a transactional check-in into a personalised arrival experience.
Healthcare: Patient Flow and Wayfinding
In Healthcare environments, reducing patient anxiety and wait times directly improves the care experience. WiFi analytics can identify bottlenecks in patient routing — areas where dwell time significantly exceeds the expected service time — enabling operational interventions. Digital wayfinding services, powered by the same location infrastructure, reduce the cognitive load on patients navigating complex facilities.
Transport: Real-Time Congestion Management
For Transport hubs — airports, rail terminals, ferry ports — real-time density monitoring is critical for both safety and service quality. WiFi analytics provides a live view of crowd distribution across security lanes, boarding gates, and retail concourses, enabling dynamic staff deployment to alleviate bottlenecks before they become service failures. For automotive and in-vehicle connectivity contexts, see our Wi Fi in Auto: The Complete 2026 Enterprise Guide .
Troubleshooting and Risk Mitigation
MAC Randomisation
Apple introduced per-network MAC randomisation in iOS 14 (2020); Android followed with Android 10. The practical effect is that passive, unauthenticated tracking of repeat visitors is no longer reliable — the same physical device may present dozens of different MAC addresses across multiple visits.
Mitigation: Shift your measurement strategy to rely on authenticated sessions exclusively for longitudinal tracking. Captive portal logins and Passpoint connections both provide persistent identity resolution that is immune to MAC randomisation. Use unauthenticated probe data only for aggregate, real-time footfall counts where individual identity is not required.
Poor Location Accuracy
Inaccurate zone data produces flawed business decisions. The most common causes are insufficient AP density, collinear AP placement, and RF interference from structural elements.
Mitigation: Conduct a dedicated RF site survey before finalising AP placement. Use the analytics platform's calibration tools to validate zone boundary accuracy against physical walkthroughs. Revisit the survey annually or after significant structural changes to the venue.
Data Privacy and Compliance
Mishandling personal data collected via guest WiFi carries significant regulatory exposure under GDPR (fines of up to 4% of global annual turnover) and reputational risk.
Mitigation: Implement a documented data retention policy — most organisations apply a 12-month rolling window for behavioural data. Ensure the captive portal consent flow is reviewed by legal counsel. Maintain a Record of Processing Activities (ROPA) entry for the WiFi analytics programme. For venues processing payment card data, verify that the guest WiFi network is appropriately segmented from PCI DSS-scoped infrastructure.
ROI and Business Impact
To justify the investment in a WiFi analytics platform, focus on three measurable outcome categories.
Operational Efficiency: Dynamic staffing based on real-time footfall data typically reduces labour costs by 8–15% in high-variability environments (retail, hospitality, transport) by aligning headcount to actual demand rather than historical schedules.
Revenue Uplift: Targeted, location-triggered promotions delivered via the captive portal or post-visit email campaigns consistently outperform untargeted communications. Venues report 15–25% higher redemption rates on location-contextualised offers versus generic campaigns.
Loyalty and Retention: Tracking the return visit rate of authenticated users provides a direct measure of loyalty programme effectiveness. Personalised recognition at the point of arrival — enabled by WiFi-triggered CRM alerts — demonstrably increases guest satisfaction scores in hospitality deployments.
For a comprehensive framework for measuring and acting on these metrics, refer to our guide on WiFi Footfall Analytics: How to Measure and Act on Visitor Data . Spanish-language version also available: Análisis de afluencia WiFi: Cómo medir y actuar sobre los datos de los visitantes .
| Outcome Category | Typical Metric | Expected Range |
|---|---|---|
| Operational Efficiency | Labour cost reduction | 8–15% |
| Revenue Uplift | Location-triggered offer redemption rate | 15–25% above baseline |
| Loyalty | Repeat visit rate (authenticated users) | +10–20% YoY with active personalisation |
| CX Score | NPS / CSAT improvement | +5–12 points over 12 months |
Key Terms & Definitions
Footfall Analytics
The measurement of the total number of unique devices (people) entering a defined physical space over a specific period, derived from WiFi probe detection or authenticated connection data.
Used by operations directors to gauge venue popularity, optimise staffing levels, and measure the physical impact of marketing campaigns. Baseline metric for all WiFi analytics deployments.
Dwell Time
The duration a connected or probing device remains within a specific analytics zone or the overall venue perimeter.
Critical for retailers measuring engagement with specific product categories, for transport hubs identifying queue bottlenecks, and for hospitality operators benchmarking lounge and F&B utilisation.
MAC Randomisation
A privacy feature in modern mobile operating systems (iOS 14+, Android 10+) where the device broadcasts a temporary, randomised MAC address when probing for networks, rather than its true hardware address.
Forces IT teams to rely on authenticated sessions rather than passive probe data for any longitudinal customer tracking. Makes unauthenticated repeat-visit measurement unreliable.
Captive Portal
A web page presented to users before network access is granted, used for authentication, data collection, and obtaining marketing consent.
The primary mechanism for resolving anonymous device MAC addresses to verified user profiles. Also the legal touchpoint for GDPR consent collection in WiFi analytics deployments.
Passpoint (Hotspot 2.0)
An industry standard (IEEE 802.11u) enabling seamless, automatic, WPA3 Enterprise-encrypted WiFi authentication without manual captive portal interaction, analogous to cellular network roaming.
Essential for delivering a frictionless connection experience in hospitality and large public venues. Enables persistent identity resolution for authenticated analytics without user friction.
Trilateration
The mathematical process of determining a device's physical location by measuring its distance from three or more access points based on RSSI (Received Signal Strength Indicator) readings.
The underlying principle of WiFi location analytics. Dictates AP placement requirements — a minimum of three APs with overlapping coverage are required for any given zone to achieve reliable location data.
Presence Analytics
The detection and counting of devices within the general vicinity of a venue, regardless of whether they have authenticated or connected to the network.
Provides aggregate footfall and passerby metrics. Useful for calculating venue capture rates (ratio of passersby who enter) but insufficient for individual CX personalisation.
Location Analytics
The tracking of a device's specific movement, position, and dwell time within defined zones of a venue, derived from trilateration across multiple access points.
Enables granular CX insights including heatmapping, journey path analysis, and zone conversion rates. Requires higher AP density and more precise infrastructure planning than presence analytics alone.
RSSI (Received Signal Strength Indicator)
A measurement of the power level of a received radio signal, expressed in decibels relative to one milliwatt (dBm). Used by WiFi analytics engines to estimate device distance from each access point.
The raw input for trilateration calculations. RSSI-based location is subject to interference from structural elements, RF reflections, and device orientation — factors that must be accounted for during site surveys.
Case Studies
A 200-room luxury hotel wants to improve VIP guest recognition upon arrival. Front desk staff frequently fail to identify high-tier loyalty members before they present their credentials, resulting in missed personalisation opportunities and guest dissatisfaction.
Deploy a profile-based authentication system using Passpoint (IEEE 802.11u) integrated with the hotel's CRM. Configure perimeter APs in the hotel entrance and car park to detect and authenticate returning guests' devices automatically as they approach the building. When a loyalty tier 1 or tier 2 member's device connects, the analytics engine fires a webhook to the front desk operational dashboard, surfacing the guest's profile — name, stay history, preferences, outstanding requests — before any verbal interaction occurs. The concierge is alerted with a 90-second lead time, enabling a personalised greeting by name and a proactive offer of the guest's preferred room type or upgrade.
A regional shopping centre with 80 retail units wants to measure the effectiveness of a new store layout designed to draw customers into a previously underperforming electronics department located at the rear of the building.
Before implementing the layout change, establish baseline metrics using the WiFi analytics platform: define specific zones for 'Entrance', 'Main Concourse', 'Electronics', and 'Food Court'. Record the zone conversion rate (percentage of total venue visitors who enter the electronics zone), average dwell time in the electronics zone, and the sequential journey path most commonly taken from entrance to electronics. Implement the new layout — revised signage, anchor tenant repositioning, promotional display placement — and monitor the same metrics over a 30-day post-change period. Use cohort analysis to compare the behaviour of first-time visitors versus repeat visitors, as repeat visitors may retain prior navigation habits for several weeks.
Scenario Analysis
Q1. A stadium IT director wants to use WiFi analytics to monitor crowd density at concession stands during halftime. The venue has high-density APs deployed in the seating bowl but sparse, corridor-only coverage in the concourses. Before relying on zone-level density data from the concourses, what is the primary architectural constraint that must be addressed?
💡 Hint:Consider the minimum requirements for accurate trilateration and the impact of AP placement patterns.
Show Recommended Approach
The primary constraint is insufficient AP density and likely collinear placement in the concourses. To achieve reliable zone-level location analytics at the concession stands, the IT director must deploy additional APs in the concourse areas with staggered, overlapping coverage — ensuring at least three APs have line-of-sight to any given zone. Corridor-only APs deployed in a straight line create the 'hallway effect', making trilateration geometrically impossible and producing unreliable density data. A dedicated RF site survey should be conducted before the deployment to validate placement and confirm zone boundary accuracy.
Q2. A retail chain's marketing team wants to track the repeat visit rate of customers over a 6-month period using passive WiFi probe data from unauthenticated devices. Why is this approach fundamentally unreliable, and what is the recommended alternative?
💡 Hint:Consider the privacy features introduced in modern mobile operating systems from 2020 onwards.
Show Recommended Approach
This approach is unreliable due to MAC randomisation, introduced in iOS 14 and Android 10. Modern devices broadcast a temporary, randomised MAC address when probing for networks, meaning the same physical device may appear as dozens of different identifiers across multiple visits. This makes it impossible to reliably link probe events to a single returning customer over a 6-month period using passive data alone. The recommended alternative is to implement a captive portal or Passpoint-based authentication system, which ties the device to a verified user profile at the point of login. All subsequent visits by that authenticated user can then be accurately attributed to a single identity, enabling reliable repeat visit rate measurement.
Q3. A hospital wants to implement a digital wayfinding service for patients using the existing guest WiFi network. The IT team plans to collect and process real-time location data to guide patients to their appointments. What is the most critical compliance consideration before going live, and what specific technical control mitigates the primary risk?
💡 Hint:Consider the nature of the data being processed, the environment, and the applicable regulatory framework.
Show Recommended Approach
The most critical compliance consideration is obtaining explicit, informed consent under GDPR (and applicable healthcare data regulations such as HIPAA in the US) before processing any patient location data. Location data in a healthcare setting is potentially sensitive — it can reveal information about a patient's health condition based on which department they visit. The specific technical control required is a clearly worded captive portal consent flow that: (1) explicitly describes the location data being collected, (2) states its purpose (wayfinding only), (3) specifies the retention period, and (4) provides an opt-out mechanism. Additionally, the wayfinding location data must be strictly segregated from any clinical or administrative systems to prevent inadvertent linkage with protected health information. Data minimisation — collecting only the location data necessary for wayfinding and deleting it at session end — is the recommended approach.



