Resolving Roaming Issues in Corporate WLANs
This guide provides network architects and IT managers with a definitive technical reference for diagnosing and resolving WiFi roaming issues in corporate WLANs. It covers the mechanics of IEEE 802.11r Fast BSS Transition, 802.11k Radio Resource Measurement, and 802.11v BSS Transition Management, with vendor-neutral configuration guidance for VoIP and mobile workforce deployments. Real-world implementation scenarios from hospitality, retail, and public-sector environments demonstrate measurable outcomes and the business case for investing in fast roaming infrastructure.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Root Cause of WiFi Roaming Issues
- 802.11r — Fast BSS Transition (FT)
- 802.11k — Radio Resource Measurement
- 802.11v — BSS Transition Management
- The Triple Stack in Practice
- Implementation Guide
- Phase 1: RF Design and Coverage Validation
- Phase 2: SSID and Mobility Domain Configuration
- Phase 3: Client Steering and Roaming Thresholds
- Phase 4: 802.1X and RADIUS Infrastructure
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Mode 1: Legacy Devices Failing to Associate After 802.11r Enablement
- Common Failure Mode 2: Sticky Clients Persisting Despite 802.11v BTM Requests
- Common Failure Mode 3: Roaming Loops
- Risk Mitigation: Change Management
- ROI & Business Impact
- Quantifying the Cost of Poor Roaming
- Measuring Success
- Total Cost of Ownership

Executive Summary
WiFi roaming issues are one of the most operationally damaging and frequently misdiagnosed problems in enterprise wireless networks. When a mobile device transitions between access points — whether a hotel guest on a Wi-Fi call, a nurse carrying a tablet between wards, or a warehouse operative on a powered vehicle — the quality of that handoff determines whether the application stays alive or fails. Standard 802.11 roaming, even with WPA2-Enterprise and 802.1X authentication, introduces handoff latency of 500ms to over 1,000ms. That is catastrophic for real-time voice and unacceptable for latency-sensitive operational applications.
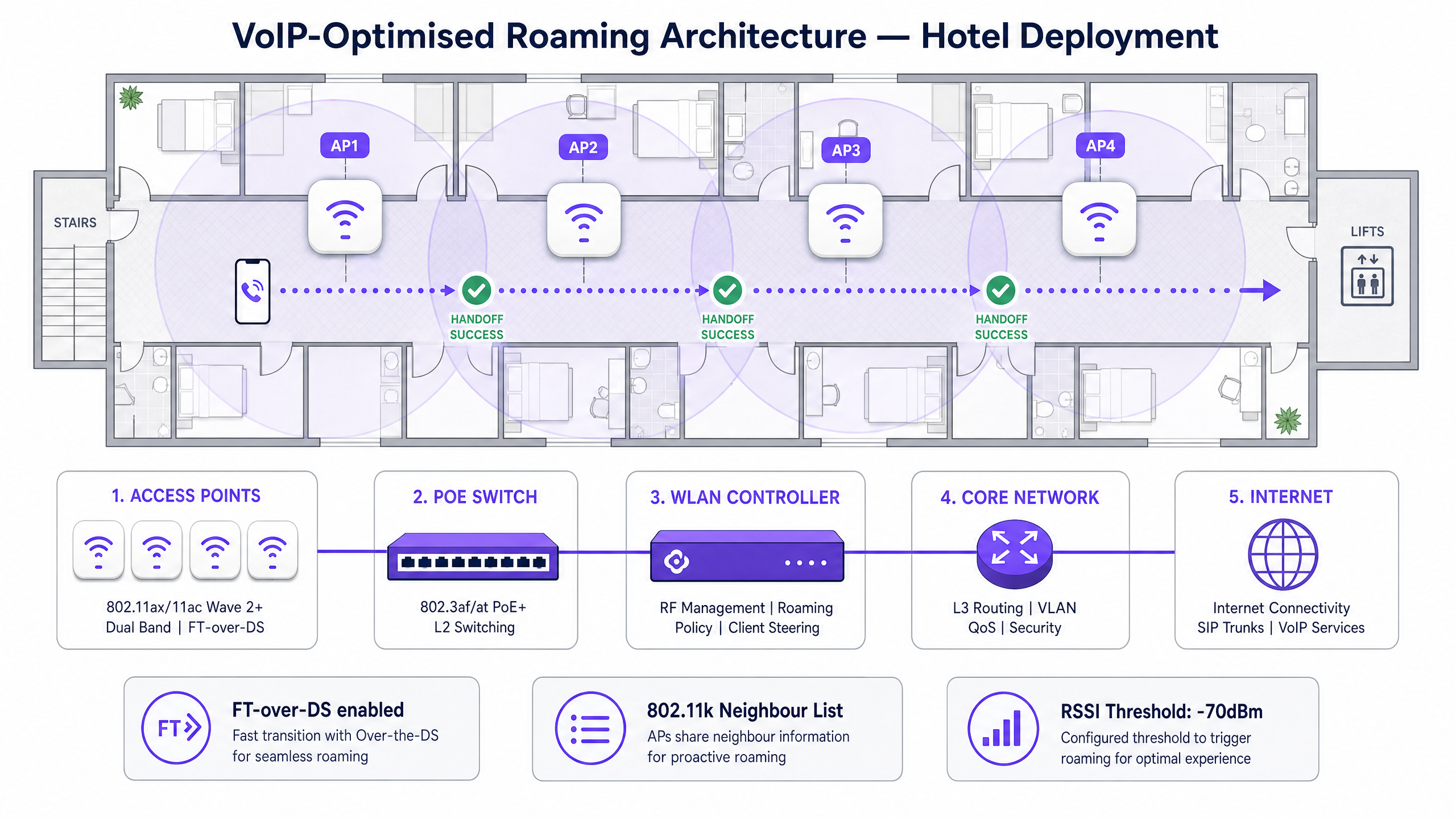
The IEEE 802.11 amendment suite — specifically 802.11r (Fast BSS Transition), 802.11k (Radio Resource Measurement), and 802.11v (BSS Transition Management) — was designed to address this directly. Deployed as a coordinated "Triple Stack", these three protocols reduce handoff latency to under 50ms, accelerate AP discovery, and enable network-directed client steering. This guide walks through the architecture, configuration, and operational implications of each protocol, with implementation guidance for hospitality, retail, and public-sector environments where Guest WiFi and mobile workforce connectivity are business-critical.
Technical Deep-Dive
The Root Cause of WiFi Roaming Issues
Before addressing the solution, it is worth being precise about the problem. In a standard 802.11 WLAN, the roaming decision is entirely client-driven. The infrastructure has no mechanism to instruct a device to move to a better AP. The client holds onto its current association until the received signal strength indicator (RSSI) degrades to a point where the device's internal roaming algorithm decides to seek an alternative. This results in two well-documented failure modes.
The first is the sticky client problem: a device remains associated with a distant, degraded AP rather than transitioning to a closer, stronger one. This is particularly common with older operating systems and enterprise handsets that have conservative roaming thresholds. The second is handoff latency: even when the client does decide to roam, the re-authentication process in an 802.1X environment requires a full EAP exchange with the RADIUS server, which introduces the latency that breaks real-time applications.
Understanding Wi-Fi frequencies is a prerequisite for roaming design — the 5 GHz and 6 GHz bands offer more non-overlapping channels and less co-channel interference, making them the preferred bands for voice and latency-sensitive traffic, but their shorter propagation range means more APs are required, which in turn increases the frequency of roaming events.
802.11r — Fast BSS Transition (FT)
802.11r, ratified in 2008 and incorporated into the 802.11-2012 consolidated standard, solves the re-authentication latency problem by introducing a key caching hierarchy. During the initial 802.1X authentication, the RADIUS server derives a master session key (MSK). In a standard deployment, this key is used to derive the Pairwise Master Key (PMK), which is then used in a four-way handshake to derive the Pairwise Transient Key (PTK) for the session.
With 802.11r, the PMK is used to derive a PMK-R0 (root key), which is held by the WLAN controller or mobility domain anchor. From this, PMK-R1 keys are pre-distributed to neighbouring APs within the same Mobility Domain. When the client roams, it presents its PMK-R1 holder identity to the target AP, which already holds the relevant key material. The four-way handshake is replaced by a two-message fast transition exchange, reducing the cryptographic overhead to near-zero.
The result is a handoff time of under 50ms — within the ITU-T G.114 recommendation of 150ms one-way delay for voice quality, and well within the threshold for maintaining an active SIP session without packet loss.
802.11r supports two transition modes:
| Mode | Mechanism | Use Case |
|---|---|---|
| FT over-the-Air | Client communicates directly with target AP during transition | Standard deployments with direct AP-to-AP communication |
| FT over-the-DS | Client communicates with target AP via current AP and distribution system | Deployments where APs cannot communicate directly; more controller-dependent |
FT over-the-DS is generally preferred in controller-based architectures as it allows the WLAN controller to manage the key distribution centrally.
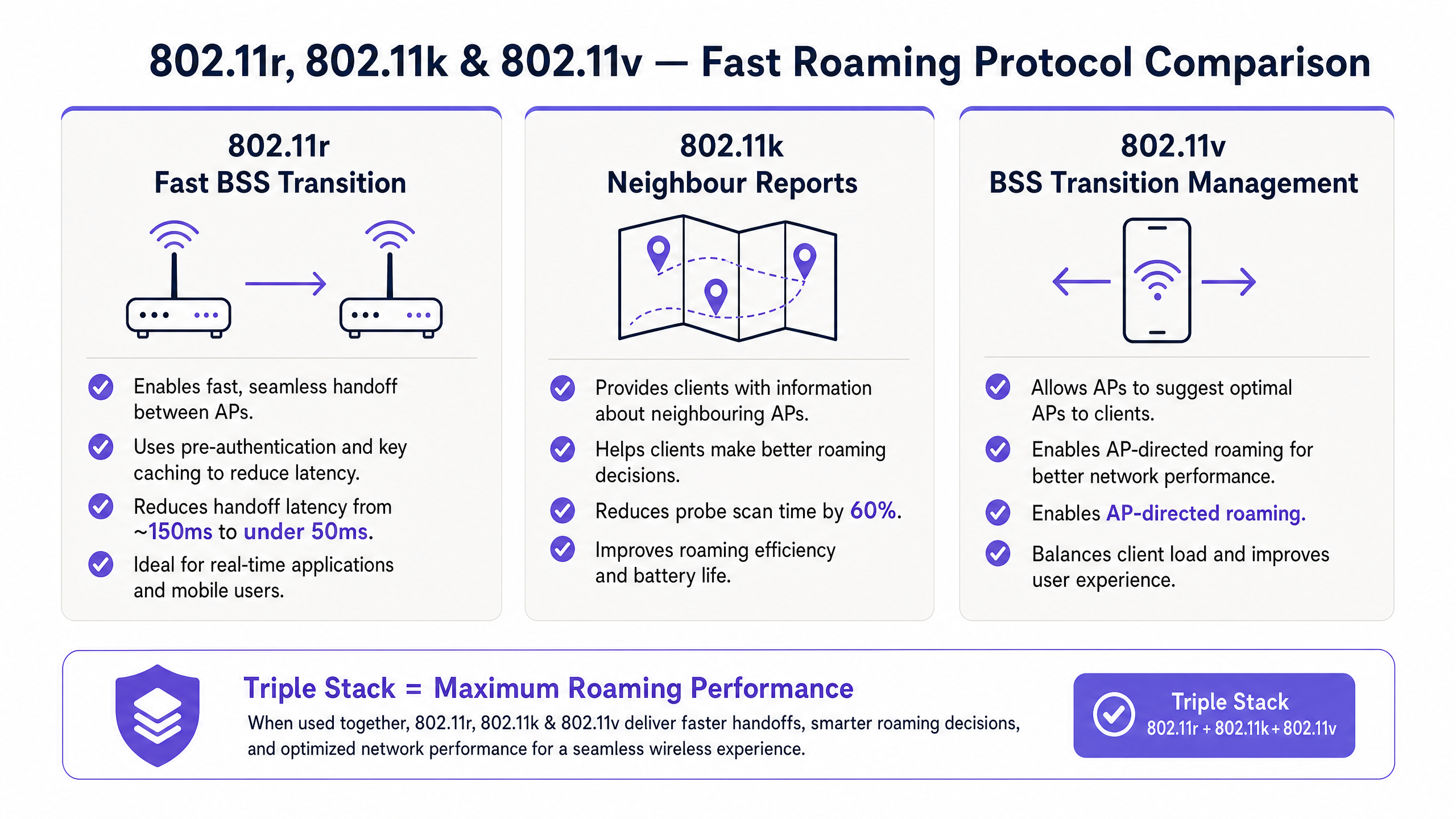
802.11k — Radio Resource Measurement
While 802.11r accelerates the transition itself, 802.11k addresses the AP discovery problem. Without 802.11k, a client seeking a new AP must perform an active or passive scan across all supported channels. In a dense enterprise environment operating across 2.4 GHz, 5 GHz, and potentially 6 GHz bands, this can take 200–400ms — adding significant latency before the 802.11r transition even begins.
802.11k enables APs to provide clients with a Neighbour Report: a structured list of nearby BSSIDs, their operating channels, and capability information. When a client requests a Neighbour Report (or receives an unsolicited one), it can target its scan to only the channels and BSSIDs listed, reducing discovery time by up to 60% in typical enterprise deployments.
Additionally, 802.11k supports Beacon Reports, where the AP requests that the client measure and report signal levels from surrounding APs. This gives the WLAN controller real-time visibility into the RF environment from the client's perspective — invaluable for RF optimisation and troubleshooting persistent roaming issues.
For healthcare environments where nurses and clinicians carry Wi-Fi-enabled devices between wards, 802.11k's ability to reduce scan time is operationally significant. A 400ms scan delay on a clinical alarm notification system is not acceptable; a 40ms targeted scan is.
802.11v — BSS Transition Management
802.11v inverts the traditional roaming model by giving the infrastructure a voice in the roaming decision. The protocol defines a BSS Transition Management (BTM) Request frame, which the AP or WLAN controller can send to a client to suggest — or strongly recommend — that it transition to a specific target AP.
This is the mechanism that enables AP-directed load balancing. If a particular AP is approaching its client capacity threshold (typically 25–30 clients per radio for voice-grade deployments), the controller can send BTM Requests to clients with the lowest RSSI on that AP, steering them towards less-loaded neighbours. This prevents the degraded experience that occurs when a single AP becomes a hotspot — common in conference rooms, hotel lobbies, and retail checkout areas.
802.11v also supports Disassociation Imminent notifications, where the AP informs a client that it will be disassociated within a specified timeframe, giving the client time to transition gracefully rather than experiencing an abrupt disconnection. This is particularly useful during planned maintenance windows or when an AP detects a hardware fault.
It is important to note that 802.11v is advisory, not mandatory. The client device makes the final roaming decision. Apple iOS devices (iOS 11 and later) respond reliably to BTM Requests. Android behaviour varies significantly by manufacturer and OS version, and some enterprise handsets require specific firmware configurations to honour BTM Requests consistently.
The Triple Stack in Practice
The three protocols are complementary and should be deployed together for maximum effect. The operational flow is as follows: 802.11k provides the client with a curated list of candidate APs, eliminating the need for a full channel scan. 802.11v allows the infrastructure to proactively steer the client towards the optimal candidate based on load and signal quality. 802.11r ensures that when the client executes the transition, the cryptographic handshake completes in under 50ms.
Deployed in isolation, each protocol provides partial benefit. Deployed together, they deliver a roaming experience that is effectively transparent to the application layer — which is the operational goal for voice, real-time collaboration tools, and mobile enterprise applications.
Implementation Guide
Phase 1: RF Design and Coverage Validation
No amount of protocol configuration compensates for inadequate RF design. Before enabling fast roaming protocols, validate that your physical layer meets the following criteria.
For voice-grade deployments, design for a minimum received signal strength of -65 dBm at the cell edge, with a minimum 15–20% cell overlap between adjacent APs. This overlap is the physical window during which the roaming event occurs; insufficient overlap means the client is already in a degraded signal state before it initiates the transition. Use a professional RF survey tool — not a vendor's planning calculator — to validate actual coverage, particularly in environments with dense construction materials such as reinforced concrete, metal shelving, or glass partitions common in retail and hospitality venues.
Transmit power management is equally critical. APs broadcasting at maximum power create large, overlapping cells that encourage sticky client behaviour. Enable automatic transmit power control (TPC) on your WLAN controller, targeting a cell edge RSSI of -65 to -67 dBm. This creates appropriately sized cells that encourage timely roaming without creating coverage gaps.
Phase 2: SSID and Mobility Domain Configuration
All APs participating in fast roaming must share the same Mobility Domain Identifier (MDID) — a two-byte value configured on the WLAN controller that groups APs into a single fast transition domain. Clients that have authenticated within a Mobility Domain can perform fast transitions between any APs in that domain without re-authenticating with the RADIUS server.
For environments with multiple SSIDs (e.g., a corporate SSID, a guest WiFi SSID, and an IoT SSID), configure separate Mobility Domains per SSID where appropriate. The guest network should not share a Mobility Domain with the corporate network, both for security isolation and to prevent key material from being distributed to APs that serve untrusted clients.
Enable Adaptive 802.11r (also referred to as Mixed-Mode FT) on all SSIDs where legacy device compatibility is a concern. This configuration causes the AP to include both standard RSN and FT information elements in its beacon frames, allowing 802.11r-capable clients to use fast transition while legacy clients fall back to standard association. This is the recommended default for most enterprise deployments.
Phase 3: Client Steering and Roaming Thresholds
Configure minimum RSSI thresholds on your WLAN controller to address the sticky client problem. Most enterprise platforms support a minimum association RSSI (preventing clients from associating below a threshold, typically -80 dBm) and a minimum operational RSSI (triggering a BTM Request or disassociation when a client's signal falls below a threshold, typically -75 to -80 dBm for data, -70 dBm for voice).
For VoIP-specific SSIDs, configure QoS policies to mark voice traffic with DSCP EF (Expedited Forwarding, DSCP 46) and ensure your WLAN controller maps this to WMM AC_VO (Access Category Voice). This ensures voice packets receive priority queuing at the AP radio level, reducing jitter during the brief period of increased load that can occur during a roaming event.
Enable Band Steering to encourage dual-band clients to associate on 5 GHz rather than 2.4 GHz. The 5 GHz band's shorter range naturally creates smaller cells, which means more frequent but faster roaming events — a better outcome for voice quality than the large, interference-prone cells of the 2.4 GHz band. For environments deploying Wi-Fi 6E or Wi-Fi 7 hardware, the 6 GHz band should be the primary band for voice and latency-sensitive applications.
Phase 4: 802.1X and RADIUS Infrastructure
In 802.1X deployments, ensure your RADIUS infrastructure is sized for the authentication load. Even with 802.11r reducing re-authentication events during roaming, the initial authentication and any full re-authentications (e.g., after a device reconnects from sleep) must complete quickly. RADIUS response times above 100ms will noticeably impact the user experience at association time.
For large-scale deployments, consider deploying RADIUS servers in an active-active cluster with local caching of session data. PMK caching (OKC — Opportunistic Key Caching) is a complementary mechanism to 802.11r that caches the PMK at the AP level, allowing fast re-association when a client returns to a previously visited AP without requiring a full 802.1X exchange. OKC and 802.11r are not mutually exclusive and should both be enabled.
For environments where network segmentation is a compliance requirement — particularly those subject to PCI DSS for cardholder data environments or NHS DSPT requirements in healthcare — ensure that your Mobility Domain boundaries align with your VLAN and security zone boundaries. Refer to the Micro-Segmentation Best Practices for Shared WiFi Networks guide for detailed VLAN and segmentation architecture recommendations.
Best Practices
The following vendor-neutral recommendations represent the current industry consensus for enterprise fast roaming deployments, aligned with IEEE 802.11 standards and Wi-Fi Alliance certification requirements.
Deploy the Triple Stack by default for any voice or mobility-critical SSID. 802.11r, 802.11k, and 802.11v have been supported by all major enterprise WLAN vendors since 2015 and by mainstream client operating systems (iOS, Android, Windows 10+, macOS) since 2017. There is no longer a valid reason to leave these protocols disabled on modern infrastructure.
Use Adaptive 802.11r universally. The risk of legacy device incompatibility with strict 802.11r is real, particularly in mixed-device environments. Adaptive mode eliminates this risk with no performance penalty for capable clients.
Validate roaming performance with a protocol analyser, not just a speed test. Tools such as Wireshark with a wireless capture adapter, or vendor-specific tools like Ekahau Sidekick, allow you to measure actual handoff latency and identify authentication failures that would be invisible to a standard connectivity test. Target a measured handoff time of under 50ms for voice deployments.
Align your roaming thresholds with your application SLAs. A -70 dBm roaming threshold is appropriate for voice. A data-only SSID can tolerate a -75 dBm threshold. IoT devices with low mobility requirements may not need client steering at all. Applying a single threshold across all SSIDs is a common misconfiguration.
Document your Mobility Domain boundaries and review them after any infrastructure change. Adding a new AP to the wrong Mobility Domain, or failing to add it at all, is a frequent cause of unexpected roaming failures in expanding deployments. For transport environments such as airports and rail stations where infrastructure changes are frequent, this is particularly important.
Troubleshooting & Risk Mitigation
Common Failure Mode 1: Legacy Devices Failing to Associate After 802.11r Enablement
Symptom: After enabling 802.11r on an SSID, a subset of devices — typically older Android handsets, legacy VoIP handsets, or industrial scanners — can no longer connect.
Root Cause: These devices do not include the FT RSN Information Element in their association requests, indicating they do not support 802.11r. In strict 802.11r mode, some AP implementations reject associations from non-FT clients.
Resolution: Switch to Adaptive 802.11r. If your vendor does not support Adaptive mode, create a parallel SSID without 802.11r for legacy devices, and enforce device-type-based SSID assignment via RADIUS attributes or MAC OUI filtering.
Common Failure Mode 2: Sticky Clients Persisting Despite 802.11v BTM Requests
Symptom: WLAN controller logs show BTM Requests being sent to clients, but clients are not roaming. Users on those devices report poor performance.
Root Cause: The client operating system is ignoring BTM Requests. This is common with certain Android OEM firmware builds and some Windows 10 configurations.
Resolution: Enable Disassociation Imminent in your BTM Request configuration. This sets a timer after which the AP will forcibly disassociate the client, compelling it to reassociate with a better AP. Use this as a last resort, as forced disassociation will briefly interrupt the connection. For Windows devices, verify that the WLAN AutoConfig service is not configured with a static AP preference.
Common Failure Mode 3: Roaming Loops
Symptom: A client repeatedly roams between two adjacent APs in rapid succession, causing repeated brief disconnections.
Root Cause: The RSSI difference between the two APs is within the hysteresis margin, causing the client to oscillate. This is often caused by misconfigured transmit power resulting in excessive cell overlap, or by a physical obstruction creating an RF null between two APs.
Resolution: Reduce transmit power on the affected APs to create more distinct cell boundaries. Increase the roaming hysteresis threshold on your WLAN controller (typically a 5–10 dBm hysteresis margin is recommended). Conduct an RF survey to identify any physical obstructions or reflective surfaces causing multipath interference.
Risk Mitigation: Change Management
Fast roaming protocol changes should be tested in a representative lab environment before deployment to production. Create a rollback plan that includes the ability to revert SSID configurations within 15 minutes. In environments subject to compliance frameworks such as PCI DSS or ISO 27001, document all WLAN configuration changes in your change management system and obtain sign-off from the information security team before deployment. Changes to Mobility Domain boundaries or RADIUS configuration should be treated as significant changes with appropriate testing windows.
ROI & Business Impact
Quantifying the Cost of Poor Roaming
The business case for investing in fast roaming infrastructure is straightforward when the cost of failure is quantified. In a 300-room hotel, if 10% of guests experience a dropped Wi-Fi call during their stay and 5% of those guests leave a negative review citing connectivity, the reputational and revenue impact is measurable. In a retail distribution centre where warehouse operatives use Wi-Fi-connected mobile terminals for pick-and-pack operations, a 500ms roaming delay multiplied across thousands of scan events per day translates directly to reduced throughput and increased labour cost.
For hospitality operators, the Wi-Fi experience is now a primary factor in guest satisfaction scores. Properties that invest in enterprise-grade WLAN infrastructure with properly configured fast roaming consistently outperform competitors on connectivity-related review metrics.
Measuring Success
Establish baseline metrics before implementing fast roaming optimisations, and measure against them post-deployment. Key performance indicators should include:
| KPI | Baseline (Pre-Optimisation) | Target (Post-Optimisation) |
|---|---|---|
| Average roaming handoff latency | 500–1,200ms | < 50ms |
| VoIP MOS score (Mean Opinion Score) | 2.5–3.0 | > 4.0 |
| Sticky client incidents per day | 15–30 | < 5 |
| Help desk tickets: WiFi connectivity | Baseline count | 40–60% reduction |
| Guest/staff WiFi satisfaction score | Baseline NPS | +15–25 points |
For organisations using WiFi Analytics platforms, roaming event data and client association metrics can be surfaced in real time, enabling proactive identification of problem areas before they generate support tickets. The ability to correlate roaming failure events with specific AP locations, time of day, and device types is a significant operational advantage over reactive troubleshooting.
Total Cost of Ownership
The incremental cost of enabling fast roaming protocols on existing enterprise-grade infrastructure is effectively zero — these are software configuration changes. The investment lies in the RF survey, the protocol analyser validation work, and the engineering time to configure and test. For a typical 50-AP enterprise deployment, budget 3–5 days of senior wireless engineer time for a full fast roaming optimisation engagement. The ROI payback period, measured against reduced help desk load and improved operational efficiency, is typically under six months.
Key Definitions
Fast BSS Transition (FT / 802.11r)
An IEEE 802.11 amendment that pre-distributes cryptographic key material to neighbouring access points within a Mobility Domain, allowing a client device to complete a roaming handoff in under 50ms by bypassing the full 802.1X RADIUS re-authentication process.
Essential for any deployment supporting VoIP, Wi-Fi calling, or real-time collaboration applications. Without 802.11r, 802.1X re-authentication during a roam can take 500ms–1,200ms, which is sufficient to drop a voice call.
Mobility Domain
A logical grouping of access points, identified by a two-byte Mobility Domain Identifier (MDID), within which a client device can perform fast BSS transitions without re-authenticating with the RADIUS server. All APs sharing a MDID must be managed by the same WLAN controller or mobility anchor.
Network architects must define Mobility Domain boundaries carefully. A Mobility Domain should align with a single security zone — do not span guest and corporate SSIDs across the same Mobility Domain.
Neighbour Report (802.11k)
A structured data frame provided by an access point to a client device, listing nearby BSSIDs, their operating channels, and capability information. Enables the client to perform a targeted scan of only the listed channels rather than a full channel sweep, reducing AP discovery time by up to 60%.
Neighbour Reports are the 802.11k feature most directly relevant to roaming performance. They are typically requested by the client after association and can also be sent unsolicited by the AP when the client's RSSI begins to degrade.
BSS Transition Management Request (802.11v)
A management frame sent by an access point or WLAN controller to a client device, suggesting or directing the client to transition to a specified target AP. Can include a list of candidate APs ranked by preference, and optionally a Disassociation Imminent flag that sets a timer after which the AP will forcibly disassociate the client.
The primary mechanism for AP-directed load balancing in enterprise WLANs. Effectiveness depends on client OS support — iOS responds reliably; Android behaviour varies by manufacturer and firmware version.
Sticky Client
A client device that remains associated with a distant or degraded access point rather than roaming to a closer, stronger AP. Caused by conservative client-side roaming algorithms and excessively large AP cells created by high transmit power.
One of the most common causes of poor Wi-Fi performance in enterprise environments. Addressed through a combination of transmit power reduction, minimum RSSI thresholds, and 802.11v BTM Requests.
Opportunistic Key Caching (OKC)
A mechanism complementary to 802.11r that caches the Pairwise Master Key (PMK) at the access point level. When a client returns to a previously visited AP, it can re-associate using the cached PMK without a full 802.1X exchange. Unlike 802.11r, OKC does not pre-distribute keys to neighbouring APs.
Useful in environments where clients frequently return to the same APs (e.g., retail store staff following regular routes). Should be enabled alongside 802.11r, not as a replacement for it.
RSSI Threshold
A configurable signal strength value (expressed in dBm) at which the WLAN controller takes action — either preventing new associations below the threshold (minimum association RSSI) or triggering a BTM Request or disassociation for existing clients (minimum operational RSSI).
Critical for addressing sticky client behaviour. For voice deployments, a minimum operational RSSI of -70 dBm is the standard recommendation. Setting this threshold too aggressively (e.g., -60 dBm) can cause excessive roaming events; too conservatively (e.g., -80 dBm) allows clients to degrade before roaming.
WMM AC_VO (Wi-Fi Multimedia Access Category Voice)
A QoS access category defined in the IEEE 802.11e amendment and Wi-Fi Alliance WMM certification that provides the highest priority queuing for voice traffic at the AP radio level. Maps to DSCP EF (Expedited Forwarding, DSCP 46) in the wired network.
Must be enabled on any SSID carrying VoIP traffic. Without WMM AC_VO, voice packets compete equally with data traffic at the AP radio queue, resulting in jitter and packet loss during periods of high network utilisation — including the brief period of increased overhead during a roaming event.
Adaptive 802.11r (Mixed-Mode FT)
A vendor-specific implementation of 802.11r that includes both standard RSN and FT Information Elements in AP beacon frames, allowing 802.11r-capable clients to use fast transition while legacy clients that do not support 802.11r can still associate using standard authentication.
The recommended default configuration for any enterprise SSID with a mixed device fleet. Eliminates the risk of legacy device incompatibility without any performance penalty for capable clients.
Worked Examples
A 400-room full-service hotel has deployed a new WLAN using 802.11ax (Wi-Fi 6) APs throughout all guest floors, conference facilities, and public areas. The hotel uses a cloud-managed WLAN controller. Staff use Wi-Fi calling on iOS and Android devices for internal communications, and guests frequently report dropped calls when moving between the lobby and restaurant areas. The existing SSID configuration has WPA3-Personal for guests and WPA2-Enterprise with 802.1X for staff. Neither SSID has fast roaming protocols enabled. How should the network architect approach this?
Step 1 — RF Validation: Before any protocol changes, conduct a post-installation RF survey to validate coverage. Target -65 dBm at all cell edges with 15–20% overlap. Verify that transmit power is not set to maximum — in a dense hotel environment, this almost certainly creates excessively large cells and sticky client conditions. Enable TPC targeting -67 dBm cell edge.
Step 2 — Staff SSID (WPA2-Enterprise / 802.1X): This is the highest priority. Enable 802.11r in Adaptive (Mixed) mode on the staff SSID. Configure the Mobility Domain to include all APs across the property. Enable 802.11k Neighbour Reports and 802.11v BTM Requests. Set a minimum operational RSSI of -70 dBm for voice, with Disassociation Imminent enabled at -75 dBm. Verify RADIUS server response times are under 100ms.
Step 3 — Guest SSID (WPA3-Personal): WPA3 with SAE (Simultaneous Authentication of Equals) supports fast transition via SAE-FT. Enable 802.11r Adaptive, 802.11k, and 802.11v on the guest SSID. Note that WPA3-Personal with 802.11r requires SAE-FT support on both the AP and client — verify this is supported on your cloud controller platform.
Step 4 — QoS: Configure DSCP EF marking for voice traffic on the staff SSID and ensure WMM AC_VO prioritisation is enabled. This is critical for maintaining voice quality during the brief transition period.
Step 5 — Validation: Use a Wi-Fi protocol analyser to capture a roaming event on both iOS and Android staff devices. Measure the actual handoff time. Target under 50ms. If handoff times are 50–150ms, investigate RADIUS latency. If over 150ms, check that 802.11r is actually being used (look for FT Authentication frames in the capture).
A large retail chain operates 120 stores, each with 8–12 APs managed by a centralised cloud WLAN controller. Each store uses a single SSID for both staff mobile devices (modern Android handsets running a warehouse management application) and legacy barcode scanners (Zebra TC51 series, approximately 40% of the device fleet, running Android 8.1). The WMS application is latency-sensitive but not voice. The scanners frequently lose connectivity when staff move between the stockroom and the shop floor, causing WMS session timeouts. How should fast roaming be configured?
Step 1 — Device Audit: Confirm 802.11r support on the Zebra TC51 running Android 8.1. Zebra's LifeGuard security update for Android 8.1 includes 802.11r support, but it must be explicitly enabled via Zebra's StageNow MDM tool or via the WLAN configuration profile. Do not assume it is enabled by default.
Step 2 — SSID Strategy: Given the mixed device fleet, enable Adaptive 802.11r on the existing SSID. This protects any devices that do not support 802.11r while enabling fast transition for capable devices. If the Zebra TC51 devices are confirmed to support 802.11r after the firmware audit, they will benefit from fast transition automatically.
Step 3 — Roaming Thresholds: For a WMS application (not voice), a roaming threshold of -72 to -75 dBm is appropriate. Set a minimum association RSSI of -80 dBm to prevent devices from associating with distant APs. Enable 802.11v BTM Requests to steer devices proactively.
Step 4 — Channel Planning: In a retail environment with metal shelving, RF propagation is highly directional and attenuated. Ensure that the stockroom-to-shop-floor transition area has adequate AP coverage with proper overlap. A common mistake is placing APs only in the sales floor and relying on signal bleed into the stockroom — this creates exactly the coverage gap that causes the observed session timeouts.
Step 5 — OKC: Enable Opportunistic Key Caching as a complement to 802.11r. If a device returns to a previously visited AP (common in store environments where staff follow regular routes), OKC allows fast re-association without a full 802.1X exchange, even for devices that do not support 802.11r.
Step 6 — WMS Session Timeout: Review the WMS application's TCP keepalive and session timeout settings. Even with fast roaming, a brief connectivity interruption during a roaming event can cause a TCP session to time out if the application's timeout is set too aggressively. Work with the WMS vendor to increase the session timeout to at least 30 seconds.
Practice Questions
Q1. A conference centre hosts events with up to 5,000 attendees. During a recent large event, the event coordinator reported that staff using Wi-Fi calling on iOS devices experienced dropped calls when moving between the main hall and the breakout rooms. The WLAN uses WPA2-Enterprise with 802.1X. 802.11r is enabled in strict mode. Post-event logs show that 23% of client associations during the event were on 2.4 GHz. What are the three most likely contributing factors to the dropped calls, and what specific changes would you make?
Hint: Consider the interaction between strict 802.11r mode, 2.4 GHz band characteristics, and high-density event environments. Think about what happens to cell boundaries when hundreds of devices are competing for airtime.
View model answer
The three most likely contributing factors are: (1) Strict 802.11r mode causing legacy device failures — if any iOS devices are running older firmware that does not fully support FT, strict mode may cause association failures or fallback to slower authentication paths. Switch to Adaptive 802.11r immediately. (2) 23% of clients on 2.4 GHz — in a high-density event environment, 2.4 GHz cells are large and heavily congested. The limited non-overlapping channels (1, 6, 11) mean significant co-channel interference, which degrades RSSI readings and makes roaming decisions unreliable. Enable aggressive band steering to push capable clients to 5 GHz, and consider disabling 2.4 GHz radios entirely for event SSIDs if all staff devices support 5 GHz. (3) Cell boundary distortion under high load — in a 5,000-person event, the RF environment changes dramatically compared to an empty venue. High client density increases airtime utilisation and interference, effectively shrinking usable cell sizes. The roaming thresholds configured during the initial deployment may be too conservative for event conditions. Reduce AP transmit power to create tighter cells, and lower the minimum operational RSSI threshold to -68 dBm for event SSIDs to encourage earlier roaming. Additionally, verify that QoS with WMM AC_VO is enabled for the staff SSID to protect voice traffic from data congestion.
Q2. You are advising a 600-bed NHS hospital trust on upgrading their WLAN to support clinical mobility — nurses and doctors carrying iOS and Android devices running a clinical communications platform (similar to Vocera or Ascom). The trust's information security team has mandated that all clinical devices must use 802.1X with certificate-based EAP-TLS authentication. The trust also has a significant fleet of legacy nurse call handsets that do not support 802.11r. How do you architect the SSID and fast roaming configuration to meet both the clinical performance requirements and the security mandate?
Hint: Consider how to segment the device fleet across SSIDs while maintaining security compliance. Think about the RADIUS infrastructure requirements for EAP-TLS at scale, and how Mobility Domain boundaries interact with VLAN segmentation.
View model answer
The correct architecture separates the device fleet into two SSIDs on the same physical infrastructure: (1) Clinical SSID (WPA2-Enterprise / EAP-TLS): For all modern iOS and Android clinical devices. Enable Adaptive 802.11r with FT-EAP, 802.11k Neighbour Reports, and 802.11v BTM Requests. Configure a dedicated Mobility Domain covering all clinical floor APs. Set minimum operational RSSI at -70 dBm with Disassociation Imminent at -75 dBm. Ensure the RADIUS infrastructure (Microsoft NPS or FreeRADIUS in an active-active cluster) is sized for EAP-TLS certificate validation — this is more computationally intensive than PEAP-MSCHAPv2. Target RADIUS response times under 80ms. (2) Legacy Nurse Call SSID: For legacy handsets that do not support 802.11r. Use WPA2-Personal with a complex PSK (or WPA2-Enterprise with PEAP if the handsets support it), with 802.11r disabled. Enable OKC to provide some key caching benefit. Keep this SSID on a separate VLAN from the clinical SSID. The Mobility Domain for the clinical SSID must not include APs serving the legacy SSID — this is both a security and a compatibility requirement. From a compliance perspective, this architecture satisfies NHS DSPT requirements by maintaining network segmentation between clinical and non-clinical traffic, and aligns with the principle of least privilege by ensuring legacy devices cannot access clinical data VLANs. Refer to the micro-segmentation guidance for detailed VLAN architecture recommendations.
Q3. A retail chain's IT director reports that since upgrading their WLAN controller firmware last month, warehouse staff using Android-based mobile terminals are experiencing 2–3 second connectivity gaps when crossing between the warehouse and the dispatch bay. Before the firmware upgrade, roaming was seamless. The WLAN configuration has not changed. 802.11r Adaptive, 802.11k, and 802.11v are all enabled. What is your diagnostic approach?
Hint: The firmware upgrade is the most significant recent change. Consider what aspects of the WLAN controller firmware could affect roaming behaviour without a configuration change. Think about Mobility Domain key distribution and PMK-R1 pre-distribution mechanisms.
View model answer
The firmware upgrade is almost certainly the root cause, even though the configuration has not changed. The diagnostic approach is: (1) Check vendor release notes for the firmware version applied, specifically looking for changes to 802.11r key distribution, Mobility Domain handling, or PMK-R1 pre-distribution behaviour. Many firmware updates include changes to fast roaming implementation that are not prominently documented. (2) Capture a roaming event using a Wi-Fi protocol analyser. Determine whether FT Authentication frames are present in the capture. If they are absent, the Android devices are falling back to full 802.1X re-authentication — this would explain the 2–3 second gap. (3) Check the Mobility Domain configuration in the controller post-upgrade. Some firmware updates reset MDID values or change the default Mobility Domain scope. Verify that all APs in the warehouse and dispatch bay are in the same Mobility Domain. (4) Test with a known-good device: If an iOS device roams seamlessly between the same APs, the issue is Android-specific. Check whether the firmware update changed the BTM Request format or the Neighbour Report structure in a way that is incompatible with the Android OEM firmware on the mobile terminals. (5) Rollback test: If the above steps do not identify the cause, arrange a maintenance window to roll back the firmware to the previous version and test. If roaming is restored, raise a support case with the WLAN vendor with the protocol capture as evidence.