What Is WiFi Analytics? A Complete Guide
This complete technical guide explains how WiFi analytics transforms standard network infrastructure into a business intelligence engine, covering data capture mechanisms (footfall, dwell time, device type, repeat visits), architectural considerations, and measurable ROI. It is designed for IT managers, network architects, and venue operations directors who need to evaluate and deploy WiFi analytics in enterprise environments.
🎧 Listen to this Guide
View Transcript
Executive Summary
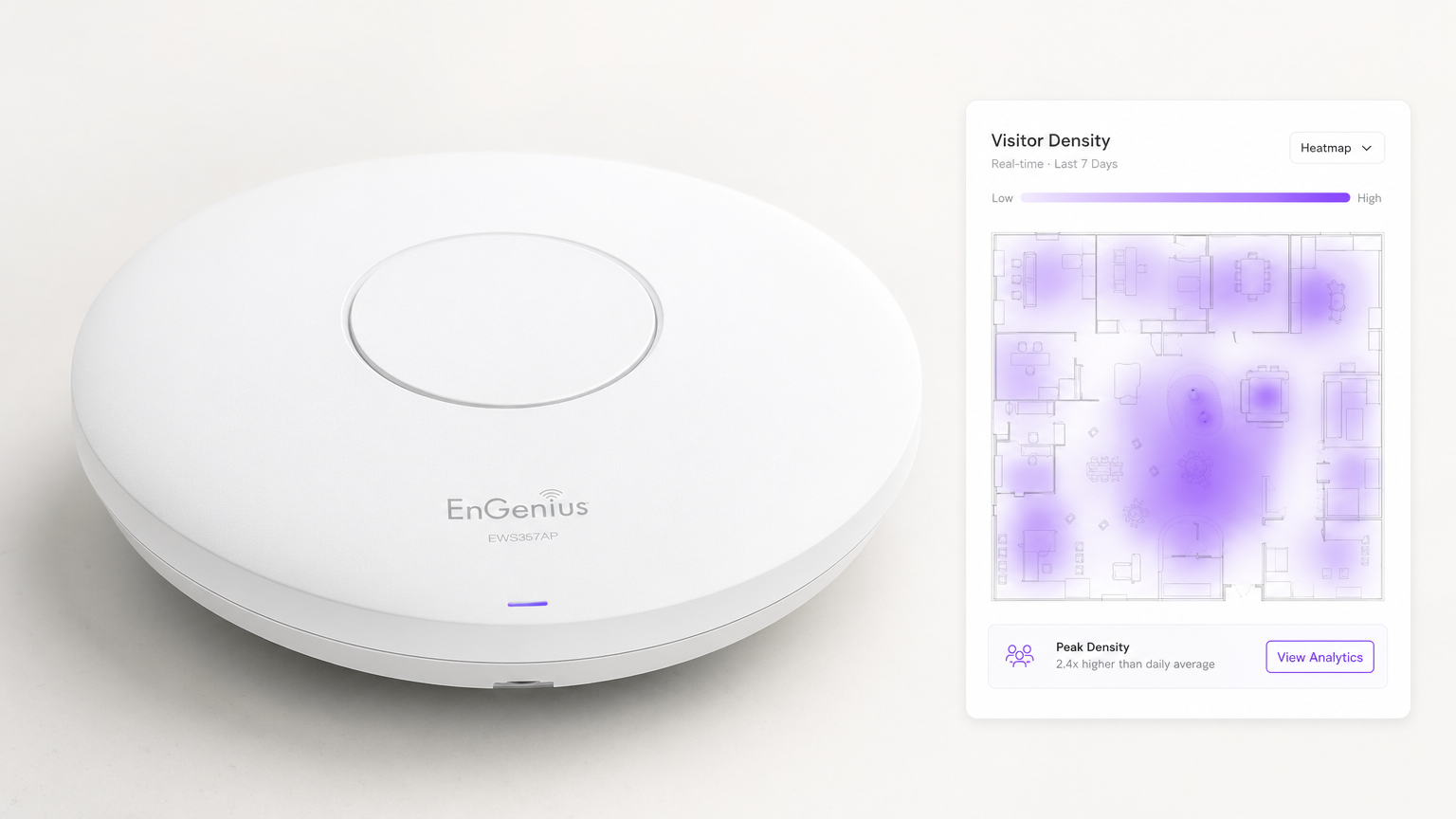
For modern enterprise venues, providing Guest WiFi is no longer simply a cost centre or an expected utility — it is a critical infrastructure layer for business intelligence. WiFi Analytics is the process of capturing, processing, and visualising data generated by devices connecting to, or probing, a wireless network. For IT managers, network architects, and venue operations directors, deploying a robust analytics solution bridges the gap between IT expenditure and measurable business value.
This guide details the technical architecture of WiFi data collection, the specific metrics captured — including footfall, dwell time, device type, and repeat visits — and the integration points necessary to turn raw network telemetry into actionable insights. By leveraging existing infrastructure, whether deploying in Retail , Healthcare , Hospitality , or Transport , organisations can achieve deep visibility into physical spaces without deploying costly overlay sensor networks.
Technical Deep-Dive: How WiFi Analytics Works
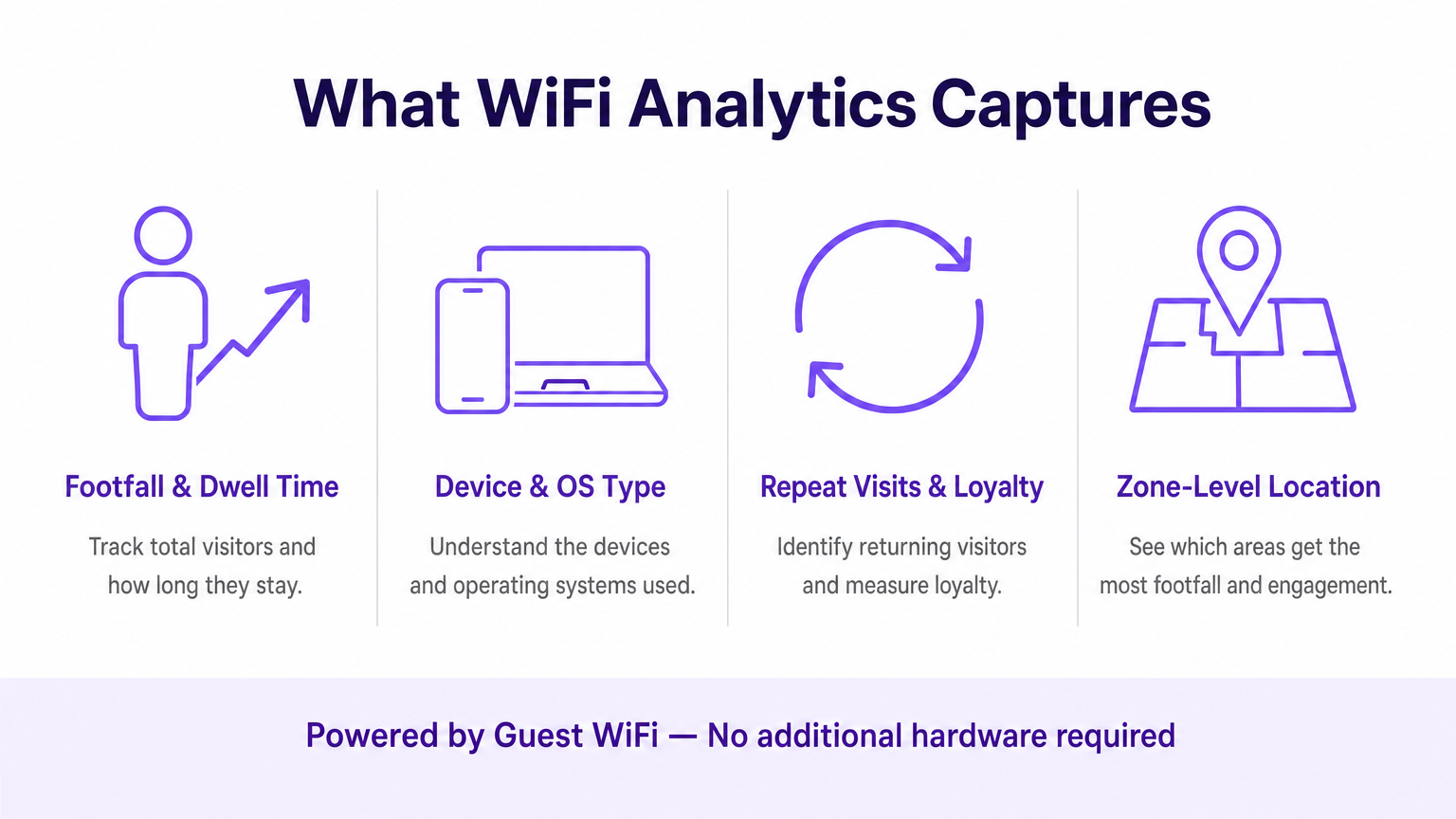
At its core, WiFi analytics relies on the fundamental behaviour of 802.11 client devices. Even before a user authenticates to a network, their device broadcasts probe requests to discover available access points (APs). These management frames, combined with the data generated during authenticated sessions, form the two primary data streams that a WiFi analytics platform processes.
The Data Capture Mechanisms
Presence Analytics (Unauthenticated): When a smartphone has WiFi enabled, it periodically sends probe requests containing its MAC address and signal strength (RSSI). Access points detect these probes. By triangulating the RSSI across multiple APs, the system calculates the device's approximate location within a venue. This provides baseline footfall and conversion metrics — passers-by versus active visitors — without requiring any user interaction.
Authenticated Analytics: When a user actively connects to the captive portal, the analytics engine captures rich first-party data. This typically includes demographic information, contact details, and CRM identifiers, bridging the gap between an anonymous MAC address and a known, persistent customer profile. This is the data layer that enables personalised marketing and loyalty programmes.
Location Services (RTLS): Advanced deployments utilise techniques such as Time Difference of Arrival (TDOA) or Fine Timing Measurement (802.11mc/802.11az) to provide highly accurate indoor positioning, often augmented by Bluetooth Low Energy (BLE) beacons. For a detailed breakdown of these positioning technologies, see our Indoor Positioning System: UWB, BLE, & WiFi Guide .
Architecture and Integration
The architecture typically involves edge hardware — wireless LAN controllers and APs — forwarding telemetry data via API or syslog to a cloud-based analytics engine. The platform ingests this high-velocity data stream, normalises it, and applies spatial mapping algorithms against uploaded floor plans to produce zone-level analytics.
Crucially, the system must integrate seamlessly with the existing network vendor stack. Whether you are evaluating Purple vs Cisco Spaces (DNA Spaces): When to Choose Each or deploying on Aruba, Ruckus, or Meraki, the analytics platform acts as an overlay — extracting value without requiring hardware replacement. This is a fundamental distinction from proprietary sensor-based solutions.
The data pipeline follows this flow: APs capture probe requests and connection events → the WLAN controller aggregates and forwards telemetry → the analytics engine normalises and maps the data → the dashboard surfaces insights to operations and marketing teams → API webhooks push authenticated user profiles to CRM and marketing automation platforms.
Standards and Compliance Considerations
Deployments must account for several regulatory and technical standards:
| Standard | Relevance |
|---|---|
| IEEE 802.11ax (Wi-Fi 6/6E) | Provides the OFDMA and BSS Colouring features that improve AP density and location accuracy |
| IEEE 802.11mc / 802.11az | Fine Timing Measurement (FTM) enables sub-metre ranging accuracy for RTLS deployments |
| WPA3-Enterprise | Mandatory for deployments handling sensitive data; provides 192-bit security mode |
| GDPR / UK GDPR | Requires explicit, auditable consent before capturing personal data via captive portal |
| PCI DSS | Guest WiFi traffic must be isolated from payment card networks via dedicated VLANs |
| CCPA | Applies to deployments serving California residents; requires opt-out mechanisms |
Implementation Guide
Deploying a WiFi analytics solution requires careful coordination between network engineering and business stakeholders. The following steps represent a vendor-neutral deployment framework.
Step 1 — Network Readiness Assessment: Evaluate current AP density and placement against location analytics requirements. Standard coverage design (APs centred in rooms) is insufficient for accurate triangulation. Perimeter AP placement is essential. Conduct an active site survey using tools such as Ekahau or iBwave to identify RF dead zones and interference sources.
Step 2 — Floor Plan Mapping: Upload accurate, scaled floor plans to the analytics platform. Define zones that align with business objectives — for example, 'Checkout Area', 'Promotional End-Cap Zone', or 'Lobby'. Inaccurate floor plan scaling is one of the most common causes of poor location data quality.
Step 3 — Captive Portal Configuration: Design the authentication flow to balance user experience with data acquisition. Implement social login options (Google, Apple ID) to reduce friction. Ensure the portal is fully responsive across device types. Purple can act as an identity provider for OpenRoaming under the Connect licence, enabling seamless onboarding for returning users without repeated portal interactions.
Step 4 — Consent and Privacy Framework: Implement GDPR-compliant consent capture. Consent must be granular (separate opt-ins for analytics, marketing, and third-party sharing), explicit (no pre-ticked boxes), and auditable (timestamped records stored per user profile).
Step 5 — Data Integration: Configure webhooks and REST API integrations to push authenticated user data into CRM platforms (Salesforce, HubSpot) and marketing automation tools (Marketo, Klaviyo). This step is where the IT deployment directly enables marketing ROI and is frequently deprioritised — do not let it be.
Step 6 — Alerting and Reporting: Configure operational alerts (e.g., dwell time thresholds triggering staff notifications) and automated reports for non-technical stakeholders. Data that remains in an IT dashboard generates no business value.
Best Practices
MAC Randomisation Mitigation: Modern operating systems (iOS 14+, Android 10+) use per-network randomised MAC addresses. Analytics platforms must rely on authenticated sessions and behavioural stitching algorithms rather than persistent hardware addresses for repeat visitor tracking. Prioritise captive portal authentication rates as a KPI.
AP Density for Location Accuracy: A minimum of three APs with overlapping coverage is required for basic triangulation. For sub-3-metre accuracy, deploy APs at 8–10 metre intervals in high-value zones. For sub-metre RTLS, supplement with BLE beacons or deploy 802.11az-capable hardware.
Network Segmentation: Isolate Guest WiFi traffic from corporate and payment networks using dedicated VLANs, firewall ACLs, and DNS filtering. This is non-negotiable for PCI DSS compliance and significantly reduces the attack surface.
Data Governance: Establish a clear data retention policy. Most analytics use cases are well-served by 13 months of data (enabling year-on-year comparison). Longer retention periods increase compliance risk and storage costs without proportional analytical benefit.
Troubleshooting & Risk Mitigation
Inaccurate Location Data: Most commonly caused by insufficient AP density, incorrect floor plan scaling, or RF interference from adjacent networks. Validate AP placement against the site survey, verify floor plan scale in the analytics platform, and use the spectrum analysis tools in your WLAN controller to identify interference sources.
Low Authentication Rates: If visitors are not completing the captive portal, audit the user journey. Measure drop-off at each step. Common causes include slow portal load times (optimise for mobile on 3G/4G fallback connections), excessive data fields, and unclear value propositions. A/B test the portal design.
Data Silos: The most commercially damaging failure mode. Proactively build automated reports for operations and marketing teams. Establish a cross-functional 'WiFi Data' working group with representatives from IT, marketing, and operations to review insights monthly.
Vendor Lock-In: Avoid analytics platforms that require proprietary hardware. Ensure the platform supports your existing AP vendor via standard APIs and can export data in open formats (CSV, JSON) to prevent dependency on a single vendor's ecosystem.
ROI & Business Impact
The ultimate measure of a WiFi analytics deployment is its contribution to business outcomes. The following framework maps analytics capabilities to measurable KPIs.
| Analytics Capability | Business KPI | Typical Improvement |
|---|---|---|
| Footfall counting | Visitor volume tracking | Replaces manual counting; 99%+ accuracy |
| Dwell time by zone | Queue management, staff allocation | 15–25% reduction in peak wait times |
| Repeat visit rate | Customer loyalty measurement | Baseline for loyalty programme ROI |
| Spatial conversion rate | Window-to-door conversion | Informs exterior display investment |
| Authenticated profiles | CRM enrichment, campaign targeting | 3–5x improvement in email campaign relevance |
| Zone flow analysis | Layout optimisation | Measurable uplift in secondary spend |
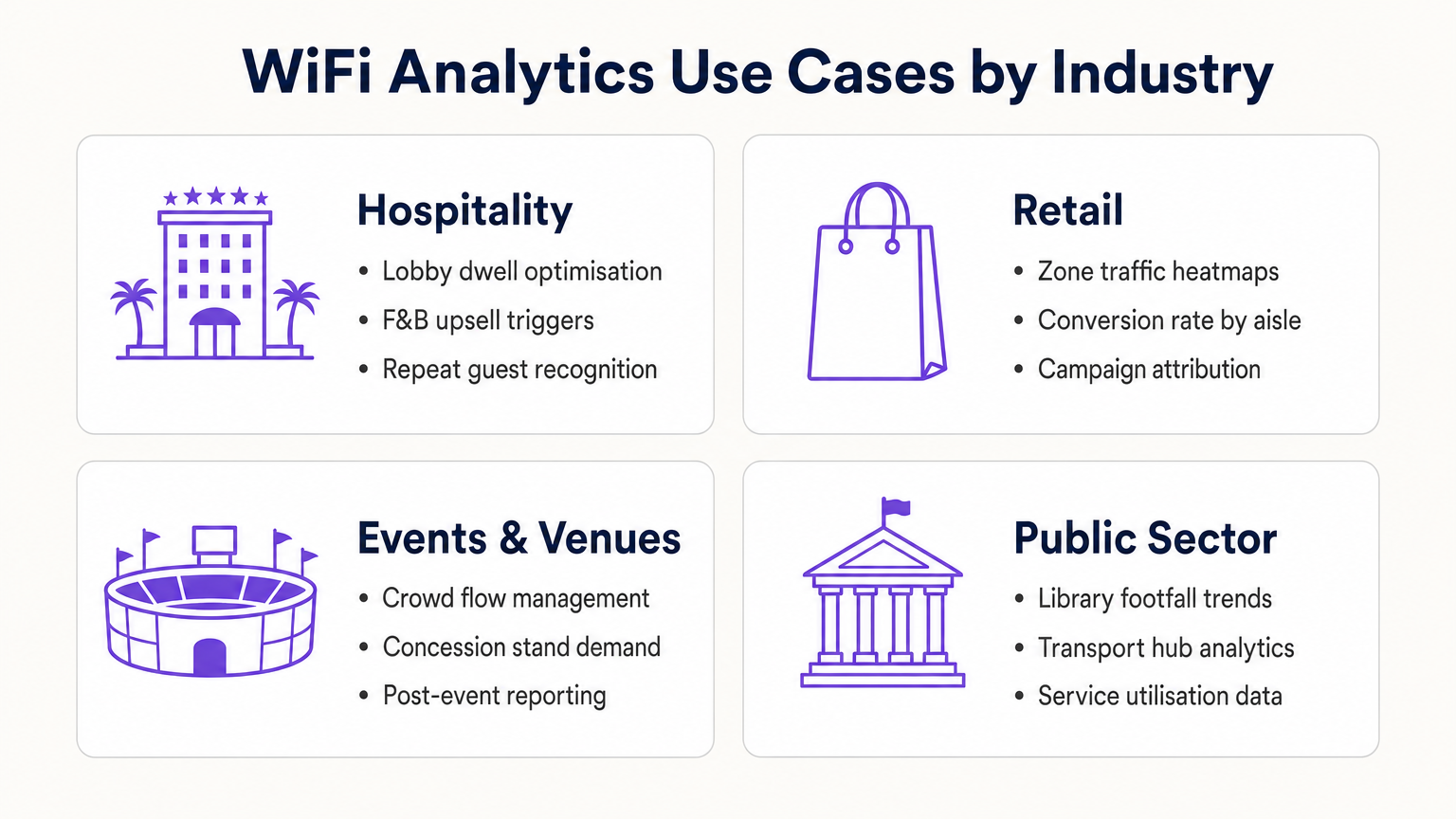
For Hospitality operators, WiFi analytics enables repeat guest recognition, lobby congestion management, and F&B upsell triggers. For Retail chains, it provides heatmap-driven layout optimisation and campaign attribution. For transport hubs and public sector venues, it delivers service utilisation data and crowd flow management. For a detailed look at connected venue applications, see our Internet of Things Architecture: A Complete Guide .
By treating the WiFi network as a strategic data asset rather than a utility, IT leaders transition from cost-centre managers to business enablers — delivering concrete ROI through enhanced operational efficiency, improved customer engagement, and evidence-based decision-making.
Key Terms & Definitions
Probe Request
An 802.11 management frame broadcast by a client device to discover available wireless networks in its vicinity, containing the device's MAC address and supported data rates.
The foundational mechanism for unauthenticated presence analytics. Access points capture these frames to detect and locate devices before any user interaction occurs.
RSSI (Received Signal Strength Indicator)
A measurement of the power level of a received radio signal, expressed in dBm (typically ranging from 0 to -100 dBm).
Analytics platforms use RSSI readings from multiple APs simultaneously to triangulate a device's physical location. Lower (more negative) values indicate greater distance from the AP.
MAC Address Randomisation
A privacy feature in modern operating systems (iOS 14+, Android 10+) that assigns a randomised hardware address to a device on a per-network basis, replacing the device's permanent MAC address.
Significantly limits the reliability of unauthenticated presence analytics for repeat visitor tracking, making captive portal authentication essential for building persistent customer profiles.
Captive Portal
A web-based authentication interface that intercepts a user's HTTP/HTTPS traffic and redirects them to a login or registration page before granting network access.
The primary mechanism for capturing first-party customer data and securing GDPR-compliant consent. Portal design and friction level directly determine data capture rates.
Dwell Time
The duration a specific authenticated or detected device remains within a defined physical zone, measured from first detection to last detection within that zone.
A critical operational metric used to identify queue congestion, measure engagement with promotional displays, and trigger time-based marketing automations.
Footfall
The total count of unique devices detected within a defined venue or zone over a specified time period.
Provides the baseline traffic metric analogous to website sessions. Used to measure overall venue performance, compare locations, and calculate spatial conversion rates.
Spatial Conversion Rate
The percentage of devices detected in an outer zone (e.g., a street or main walkway) that subsequently enter an inner zone (e.g., a store or aisle).
Used by retail operators to evaluate the effectiveness of exterior displays and entrance signage. A low conversion rate despite high footfall indicates an attraction problem at the threshold.
OpenRoaming
A Wireless Broadband Alliance (WBA) federation standard that enables seamless, secure Wi-Fi onboarding across participating networks without requiring repeated captive portal interactions.
Purple can act as an identity provider for OpenRoaming under the Connect licence, enabling venues to offer seamless connectivity while retaining the ability to capture analytics data from returning users.
RTLS (Real-Time Location System)
A system that uses radio frequency technologies (WiFi, BLE, UWB, or RFID) to determine and track the real-time location of objects or people within a defined space.
Relevant when sub-3-metre location accuracy is required — for example, asset tracking in healthcare or turn-by-turn indoor navigation in large venues. Standard WiFi RSSI triangulation is typically insufficient for these use cases.
TDOA (Time Difference of Arrival)
A location technique that calculates position by measuring the difference in the time a signal arrives at multiple reference points (APs or anchors).
Provides significantly higher location accuracy than RSSI-based triangulation, but requires hardware support and precise clock synchronisation across APs.
Case Studies
A 400-room resort hotel wants to reduce congestion at check-in desks during peak hours (15:00–17:00) and increase revenue at the lobby bar. The IT team has a Cisco Meraki deployment with 24 APs across the ground floor.
- Map the lobby floor plan in the analytics platform with three distinct zones: 'Check-In Queue', 'Lobby Seating', and 'Bar Area'. Verify that at least three APs provide overlapping coverage in each zone for accurate triangulation.
- Configure a real-time operational alert: if the device count in the 'Check-In Queue' zone exceeds 20 simultaneously AND average dwell time exceeds 15 minutes, trigger an automated SMS to the Duty Manager via the platform's webhook integration.
- Configure a marketing trigger: if a device dwells in the 'Lobby Seating' zone for more than 10 minutes, push a personalised notification (via the captive portal session or email if authenticated) offering a 10% discount at the bar, valid for 30 minutes.
- Integrate the authenticated user profiles with the hotel PMS (Property Management System) to automatically recognise returning guests and suppress the captive portal for them, surfacing a personalised welcome message instead.
- Review weekly dwell time reports to identify whether the check-in queue alert is triggering at consistent times, enabling proactive staffing adjustments rather than reactive responses.
A 50-store retail chain has deployed WiFi analytics across all locations. The Head of Merchandising reports that a specific promotional aisle in their flagship Manchester store generates high footfall but below-average sales per square foot. They want to understand why before rolling out the same layout to 15 other stores.
- Define two zones in the analytics platform for the Manchester store: 'Main Walkway' (the primary traffic artery adjacent to the aisle) and 'Promotional Aisle' (the target zone).
- Pull a 30-day report comparing: (a) the spatial conversion rate — the percentage of devices in the Main Walkway that subsequently enter the Promotional Aisle — and (b) the average dwell time within the Promotional Aisle for devices that do enter.
- Scenario A — High conversion, low dwell time: Visitors are entering the aisle but leaving quickly. This indicates the product placement or signage within the aisle is confusing or unappealing once inside. Recommendation: redesign the aisle layout and test with a 14-day A/B comparison.
- Scenario B — Low conversion despite high walkway traffic: Visitors are not being drawn into the aisle from the walkway. This indicates the end-cap display or entrance signage is ineffective. Recommendation: redesign the entrance display and measure conversion rate change over the following 14 days.
- Correlate the WiFi analytics data with POS transaction data by time-of-day to identify whether dwell time correlates with purchase probability, establishing a venue-specific 'engagement threshold' for future campaign design.
Scenario Analysis
Q1. A retail client reports that their 'Repeat Visitor' metric has dropped by 40% over the past eight months, despite sales remaining steady and no significant change in marketing activity. Their analytics deployment relies entirely on unauthenticated presence tracking. What is the most likely technical cause, and what is the recommended remediation?
💡 Hint:Consider the timeline of major mobile OS updates and their privacy features.
Show Recommended Approach
The most likely cause is the progressive adoption of MAC address randomisation across the client's customer base. iOS 14 (released September 2020) and Android 10+ introduced per-network MAC randomisation, causing returning devices to appear as new, unique visitors to presence analytics engines. As the proportion of customers running these OS versions has increased, the repeat visitor metric has degraded. The remediation is to implement a captive portal authentication layer. When users authenticate with a persistent identifier (email address, social login), the analytics platform can build a customer profile tied to that identifier rather than the rotating MAC address. This restores repeat visitor tracking accuracy and simultaneously generates first-party marketing data.
Q2. You are the network architect for a new 80,000-seat stadium. The venue operations team wants WiFi analytics to manage crowd flow through concourse areas and identify concession stand congestion in real time. The IT budget allows for 400 APs. How should you prioritise AP placement to maximise analytics accuracy, and what accuracy level can you realistically expect?
💡 Hint:Think about the geometric requirements of triangulation and the difference between coverage and analytics design principles.
Show Recommended Approach
Prioritise perimeter placement over central coverage. For each concourse zone, ensure APs are placed at the zone boundaries rather than the centre. This enables the analytics engine to accurately determine when a device crosses from one zone to another. Aim for a minimum of three APs with overlapping coverage in each defined zone, with AP spacing of 8–10 metres in high-priority areas (concession stands, entry/exit gates). With standard RSSI triangulation on 802.11ax hardware, expect 3–5 metre location accuracy in open concourse areas. For sub-3-metre accuracy at specific chokepoints (e.g., individual concession windows), supplement with BLE beacons or deploy 802.11az-capable APs at those locations.
Q3. A hospital IT director wants to use the existing WiFi network to track the location of 200 high-value mobile medical assets (infusion pumps, portable ECG monitors). They do not want to deploy any additional hardware. The analytics platform currently provides 5-metre RSSI triangulation accuracy. Is this deployment viable, and what are the key risks?
💡 Hint:Consider both the technical accuracy requirements and the behaviour of the devices being tracked.
Show Recommended Approach
This deployment is not reliably viable for two reasons. First, medical equipment frequently enters low-power or sleep states, causing the device to stop broadcasting WiFi probe requests. When a device is not actively probing, it is invisible to the presence analytics engine. This creates gaps in tracking that are unacceptable for asset management. Second, 5-metre RSSI accuracy is insufficient to determine whether an asset is in Room 4A or Room 4B in a typical hospital ward layout. The recommended alternative is a dedicated RTLS solution using active RFID tags or BLE beacons attached to the assets, which actively broadcast at regular intervals regardless of the asset's power state, and which can achieve sub-2-metre accuracy. The existing WiFi infrastructure can serve as the receiver network for BLE beacons, avoiding the need for a completely separate sensor network.



