WPA2 vs. 802.1X: What's the Difference?
This guide demystifies the relationship between WPA2 encryption and the IEEE 802.1X authentication framework — two complementary standards that are frequently conflated in vendor documentation and network design discussions. It provides IT directors, network architects, and venue operations leaders with a clear technical breakdown of how these protocols interact, practical deployment strategies across hospitality, retail, and public-sector environments, and actionable guidance on compliance, risk mitigation, and guest WiFi integration.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: Deconstructing the Standards
- WPA2: The Encryption Standard
- 802.1X: The Authentication Framework
- How WPA2 and 802.1X Work Together
- Implementation Guide: Architecting for Your Venue
- Corporate Office: Zero Trust Architecture
- Retail Chain: Segmented Security for PCI DSS
- Hospitality and Public Venues: Seamless Onboarding at Scale
- Best Practices for Enterprise Deployments
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
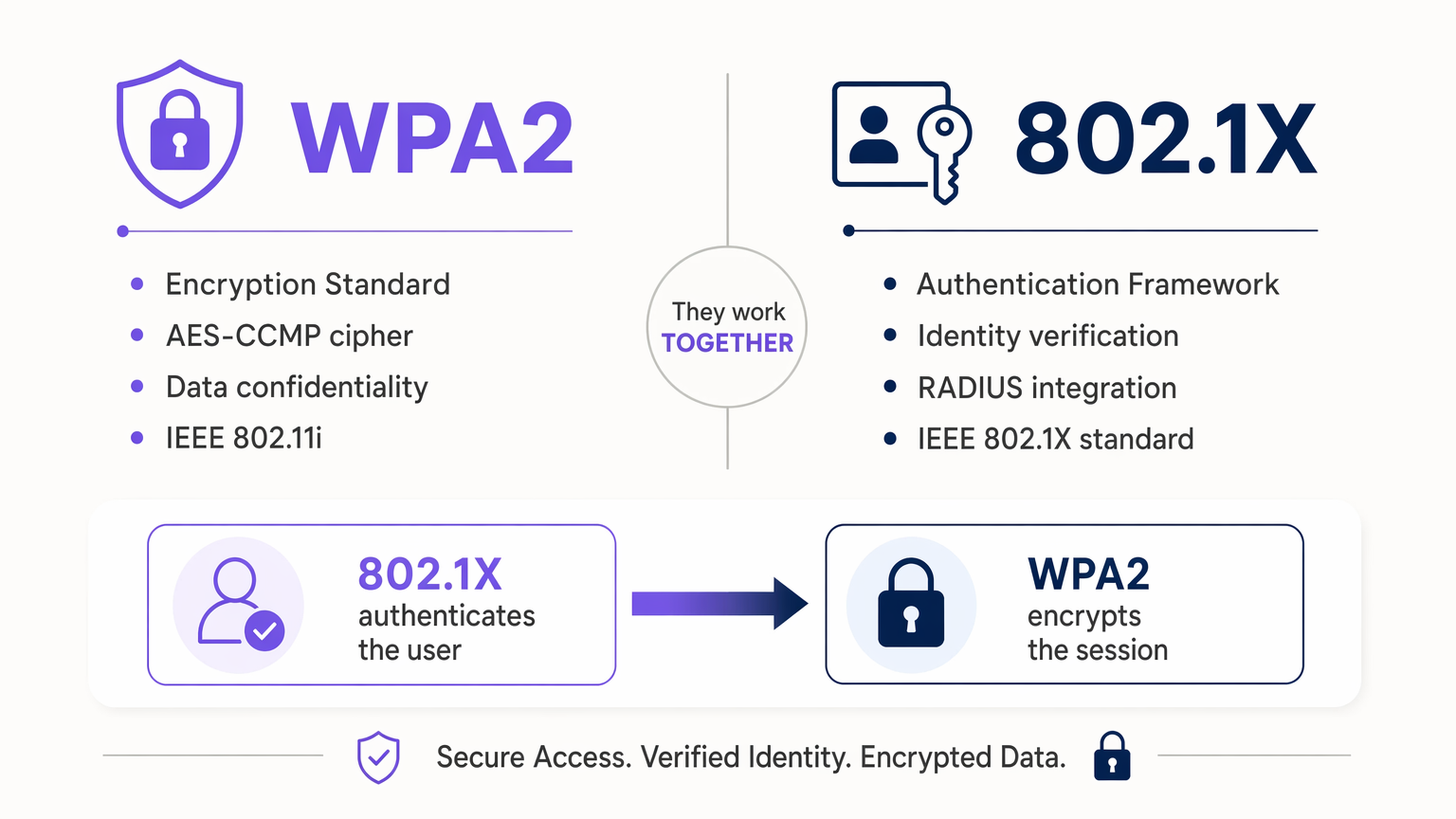
For IT directors and network architects managing enterprise environments, the distinction between WPA2 and 802.1X is often blurred in vendor documentation. WPA2 is a security certification program that dictates how wireless data is encrypted over the air. Conversely, IEEE 802.1X is a port-based Network Access Control (PNAC) framework that dictates how a user or device proves their identity before being allowed onto the network.
They are not competing standards — they are complementary layers of a secure wireless architecture. When an enterprise deploys "WPA2-Enterprise," they are inherently deploying WPA2 for encryption and 802.1X for authentication. Understanding how these protocols interact is critical for mitigating rogue access, ensuring compliance with frameworks such as PCI DSS and GDPR, and deploying scalable infrastructure across distributed venues. This guide dissects the mechanics of both standards, provides vendor-neutral implementation strategies, and details how modern platforms like Purple's Guest WiFi integrate seamlessly into these secure architectures.
Technical Deep-Dive: Deconstructing the Standards
To architect a secure wireless network, one must separate the concepts of data confidentiality (encryption) from identity verification (authentication). These are distinct problems, solved by distinct standards, that operate in sequence.
WPA2: The Encryption Standard
Wi-Fi Protected Access 2 (WPA2) is a certification program developed by the Wi-Fi Alliance to secure wireless computer networks. It is based on the IEEE 802.11i standard. Its primary function is to ensure that data transmitted between a client device (supplicant) and an access point (authenticator) cannot be intercepted and read by malicious actors.
WPA2 mandates the use of AES (Advanced Encryption Standard) combined with CCMP (Counter Mode Cipher Block Chaining Message Authentication Code Protocol). This replaced the vulnerable TKIP cipher used in the original WPA standard. WPA2 operates in two primary modes: WPA2-Personal (PSK), which uses a Pre-Shared Key where every device uses the same password to generate encryption keys, and WPA2-Enterprise, which integrates with an 802.1X authentication server and generates unique, dynamic encryption keys for every individual session.
The critical vulnerability of WPA2-Personal is that a single compromised PSK exposes the entire network. In a retail chain of 400 locations, rotating a PSK across every AP and every device is operationally prohibitive. WPA2-Enterprise, backed by 802.1X, eliminates this problem entirely.
802.1X: The Authentication Framework
IEEE 802.1X is a standard for port-based Network Access Control (PNAC). Originally designed for wired Ethernet, it was adapted for wireless networks to provide robust, per-user authentication. It does not encrypt data — it acts as a digital gatekeeper, keeping the network port logically "closed" until the device proves its identity to a centralised authentication server.
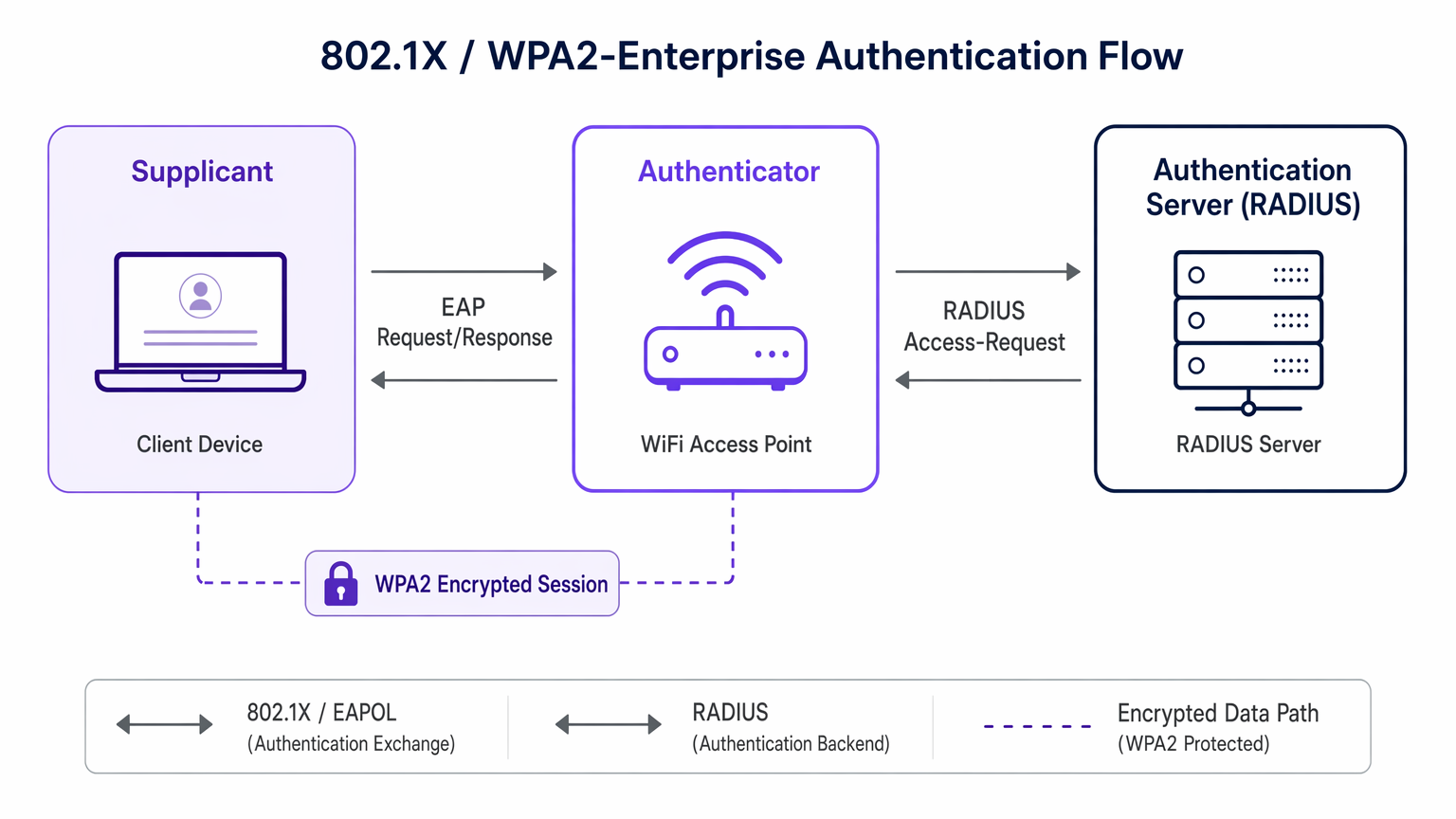
The 802.1X framework is built on three roles. The Supplicant is the client device (laptop, smartphone, IoT sensor) requesting network access. The Authenticator is the network access device — typically a wireless access point or managed switch — that facilitates the authentication exchange without making the access decision itself. The Authentication Server (typically a RADIUS server) is the centralised system that verifies the supplicant's credentials against a directory such as Active Directory or LDAP and issues the access decision.
802.1X relies on the Extensible Authentication Protocol (EAP) to transport authentication data between the supplicant and the authentication server. EAP is highly flexible, supporting a range of inner methods. EAP-TLS uses mutual certificate-based authentication and is considered the gold standard for zero-trust environments. PEAP encapsulates credentials within a TLS tunnel, requiring only a server-side certificate. For a detailed comparison of these methods, see our guide on EAP-TLS vs. PEAP: Which authentication protocol is right for your network? .
How WPA2 and 802.1X Work Together
When a device connects to a WPA2-Enterprise SSID, the following sequence occurs. First, the device associates with the AP, but the AP blocks all traffic except 802.1X EAP messages. Second, the device and the RADIUS server exchange credentials via the AP — this is the 802.1X authentication phase. If successful, the RADIUS server sends an "Access-Accept" message to the AP, along with a Master Session Key (MSK). Third, the AP and the device use the MSK to perform the WPA2 4-way handshake, deriving the specific Pairwise Transient Key (PTK) used to encrypt that session's data traffic via AES-CCMP. Finally, the port is "opened," and encrypted data flows. Every user has a unique encryption key, meaning that capturing one user's traffic provides no insight into another's.
Implementation Guide: Architecting for Your Venue
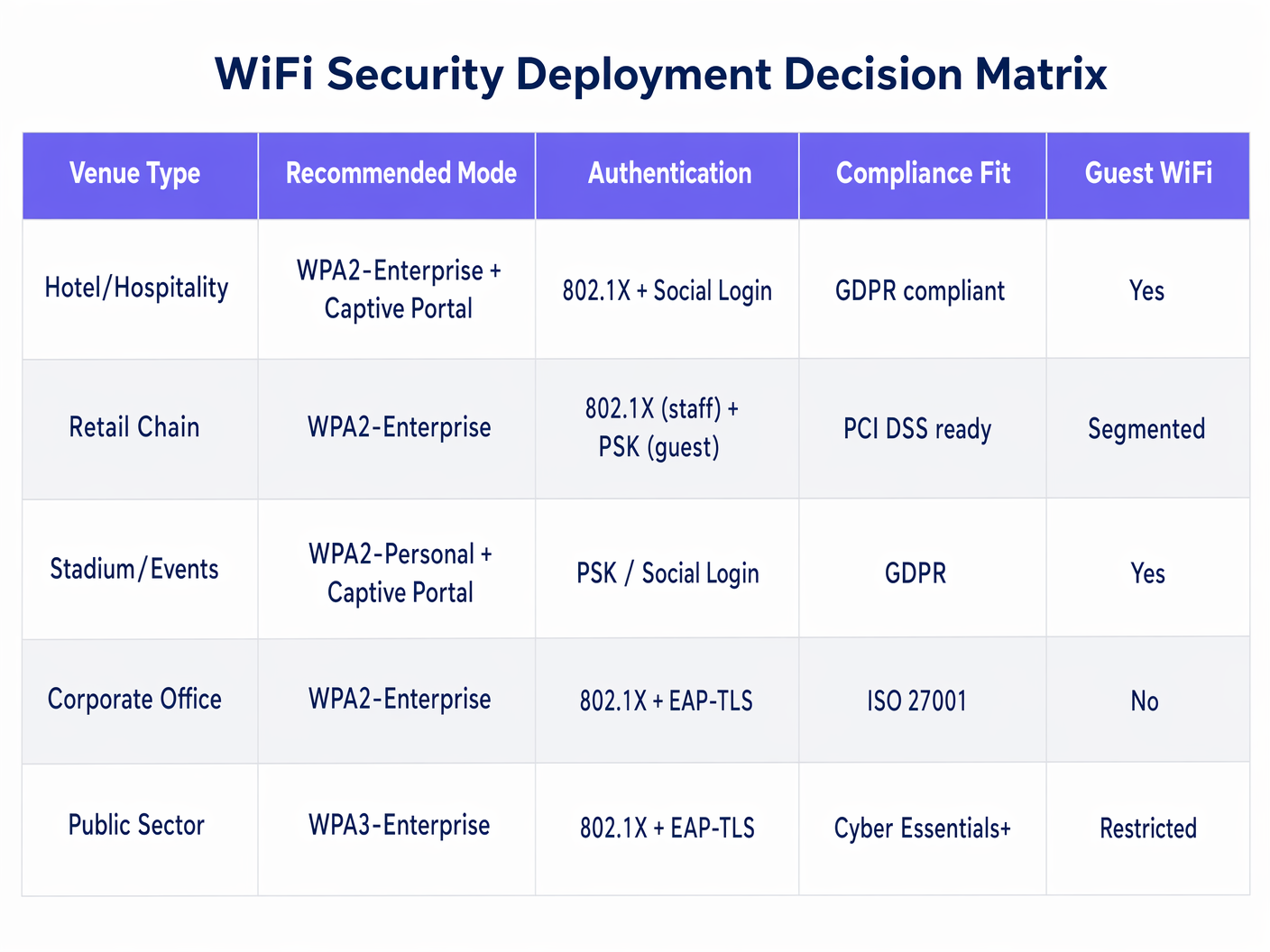
Deploying these standards requires aligning technical capabilities with business requirements. The approach varies significantly depending on the venue type and user demographic.
Corporate Office: Zero Trust Architecture
For organisations targeting ISO 27001 or Cyber Essentials+ compliance, the recommended deployment is WPA2-Enterprise (or WPA3-Enterprise for new builds) with 802.1X using EAP-TLS. This requires deploying digital certificates to all corporate devices via an MDM solution such as Microsoft Intune or Jamf. It eliminates password-based vulnerabilities entirely — only company-owned, managed devices can authenticate. Unmanaged or personal devices are automatically relegated to a segmented guest SSID. Dynamic VLAN assignment via RADIUS attributes allows further segmentation by role: IT administrators, standard staff, and contractors can each be assigned to different VLANs with appropriate ACLs, all from a single SSID.
Retail Chain: Segmented Security for PCI DSS
For a large retail chain, the challenge is dual-purpose: securing PoS terminals for PCI DSS compliance while offering frictionless guest access to drive loyalty programme sign-ups. The architecture requires two distinct security postures on the same physical infrastructure. The staff and PoS SSID should use WPA2-Enterprise with 802.1X (PEAP-MSCHAPv2 tied to Active Directory for staff, EAP-TLS with machine certificates for PoS terminals). This ensures individual accountability and keeps PoS traffic on a strictly isolated, PCI-compliant VLAN. The guest SSID uses an open network routed directly to a captive portal. Purple's WiFi Analytics platform handles guest authentication via social login or form fill, capturing first-party data compliantly under GDPR while maintaining complete network segmentation from the PoS environment.
Hospitality and Public Venues: Seamless Onboarding at Scale
For hospitality environments — hotels, conference centres, stadiums — 802.1X is too operationally complex for transient guests who have no relationship with the corporate directory. The emerging standard for this use case is Passpoint (Hotspot 2.0), which uses 802.1X and WPA2-Enterprise under the hood but automates the device provisioning process. Purple acts as a free identity provider for services like OpenRoaming under the Connect licence, allowing guests to authenticate seamlessly using their existing profiles without any manual network configuration. For venues in the transport and public-sector space, this approach also supports compliance with GDPR data capture requirements by integrating consent management directly into the authentication flow.
Best Practices for Enterprise Deployments
Enforce strict certificate validation on all supplicants. When using PEAP, ensure that client devices are configured to validate the RADIUS server's certificate. Failure to do so exposes the network to Evil Twin attacks, where a rogue AP harvests credentials from devices that blindly trust any server presenting an EAP challenge. Deploy this configuration via Group Policy or MDM — never rely on end users to make this decision manually.
Implement dynamic VLAN assignment. Leverage RADIUS attributes (specifically Tunnel-Type, Tunnel-Medium-Type, and Tunnel-Private-Group-ID) to assign users to specific VLANs based on their Active Directory group membership upon successful 802.1X authentication. This enables role-based network segmentation without requiring separate SSIDs for each user class.
Deprecate legacy cipher suites. Ensure TKIP and WEP are entirely disabled on all wireless controllers and access points. Both are cryptographically broken. A network advertising WPA2 but permitting TKIP fallback is not meaningfully more secure than WEP.
Plan RADIUS capacity for high-density environments. In stadiums, conference centres, and large healthcare campuses, thousands of devices may attempt to authenticate simultaneously. Ensure RADIUS infrastructure is load-balanced and that network paths between APs and authentication servers have sub-10ms latency. Connectivity reliability for distributed deployments is a key consideration — see The Core SD-WAN Benefits for Modern Businesses for guidance on ensuring resilient WAN paths to centralised authentication services.
Troubleshooting & Risk Mitigation
The Silent Failure. A device fails to connect, but the user receives no meaningful error. This is almost always a certificate trust issue — the supplicant is rejecting the RADIUS server's certificate. Mitigation: ensure the Root CA issuing the RADIUS certificate is distributed to all client devices via GPO or MDM, and that the wireless profile is pre-configured to trust it.
RADIUS Timeout. The AP stops forwarding traffic because the RADIUS server exceeded the response timeout threshold. Mitigation: implement RADIUS server redundancy (primary and secondary), ensure the authentication server is not co-located on a congested network segment, and tune the AP's RADIUS timeout and retry parameters appropriately.
MAC Authentication Bypass (MAB) Vulnerabilities. For headless IoT devices that cannot run an 802.1X supplicant, administrators often fall back to MAB, which authenticates based on MAC address. MAC addresses are trivially spoofed. Mitigation: place all MAB-authenticated devices in highly restricted, isolated VLANs with strict ACLs permitting only the specific traffic flows required for device operation. Treat all MAB devices as untrusted by default.
Evil Twin Attacks. A rogue AP broadcasts the corporate SSID and harvests credentials from devices that do not validate the server certificate. Mitigation: enforce certificate validation (as above) and deploy rogue AP detection on the wireless LAN controller. Most enterprise-grade controllers include this capability natively.
ROI & Business Impact
Transitioning from WPA2-Personal to an 802.1X-backed WPA2-Enterprise architecture requires investment in RADIUS infrastructure and, for EAP-TLS deployments, a PKI (Public Key Infrastructure). However, the business case is compelling.
Risk reduction is the primary driver. Eliminating shared PSKs removes the single largest attack vector in wireless networks. When an employee leaves, their specific access is revoked centrally in Active Directory — no PSK rotation required across potentially thousands of access points. The operational cost saving in a 400-location retail estate is significant.
Compliance enablement is the secondary driver. PCI DSS Requirement 8 mandates unique user IDs and individual accountability. 802.1X provides this natively. HIPAA's technical safeguard requirements for access control and audit logging are similarly satisfied by 802.1X's per-user authentication records in the RADIUS accounting log.
Operational efficiency at scale is the long-term benefit. Day-to-day management is streamlined through central directory integration. New starters get network access the moment their AD account is provisioned. Leavers lose access the moment it is disabled. No helpdesk tickets for forgotten WiFi passwords.
By decoupling encryption (WPA2) from authentication (802.1X), enterprise IT teams build wireless networks that are scalable, auditable, and resilient — capable of supporting both the most demanding corporate security postures and the most seamless guest experiences.
Key Definitions
WPA2 (Wi-Fi Protected Access 2)
A Wi-Fi Alliance certification program based on IEEE 802.11i that mandates AES-CCMP encryption for wireless data in transit.
IT teams encounter this when configuring SSIDs on wireless controllers. The choice between WPA2-Personal and WPA2-Enterprise determines whether authentication is handled by a shared password or an 802.1X server.
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication framework for devices attempting to connect to a network.
Referenced when configuring RADIUS integration on wireless controllers and switches. It is the underlying mechanism that enables WPA2-Enterprise to provide per-user authentication.
Supplicant
The client device (laptop, smartphone, IoT sensor) that initiates the 802.1X authentication exchange and provides credentials or certificates.
In troubleshooting, the supplicant is often the source of configuration issues — particularly around certificate validation settings in the wireless network profile.
Authenticator
The network access device (typically a wireless AP or managed switch) that relays EAP messages between the supplicant and the authentication server without making the access decision itself.
The authenticator blocks all non-EAP traffic until it receives an Access-Accept from the RADIUS server, at which point it opens the logical port.
RADIUS (Remote Authentication Dial-In User Service)
A centralised AAA (Authentication, Authorisation, and Accounting) protocol server that verifies credentials, enforces policies, and logs access events.
The RADIUS server is the backbone of any 802.1X deployment. It integrates with Active Directory or LDAP and returns dynamic VLAN assignments and other policy attributes upon successful authentication.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A certificate-based EAP method requiring digital certificates on both the client and the server, providing mutual authentication.
Considered the most secure EAP method. Used in zero-trust corporate environments where devices are managed via MDM and certificates can be deployed automatically.
PEAP (Protected Extensible Authentication Protocol)
An EAP method that encapsulates the inner authentication exchange within a TLS tunnel, requiring only a server-side certificate.
Widely deployed in BYOD and mixed-device environments because it allows users to authenticate with standard AD username and password credentials without requiring client certificates.
AES-CCMP
The mandatory encryption cipher suite in WPA2, combining the AES block cipher with the CCMP protocol for data confidentiality and integrity.
IT teams must ensure all APs and client devices support AES-CCMP. Any deployment permitting TKIP fallback undermines the security guarantees of WPA2.
4-Way Handshake
The WPA2 cryptographic exchange between a client device and an access point that derives the session-specific Pairwise Transient Key (PTK) used to encrypt data traffic.
Occurs after successful 802.1X authentication, using the Master Session Key provided by the RADIUS server. Each user's PTK is unique, ensuring traffic isolation between sessions.
Captive Portal
A web-based authentication or consent page presented to users before granting access to a public or guest WiFi network.
Used in hospitality, retail, and public venues where 802.1X is impractical for transient users. Platforms like Purple's Guest WiFi use captive portals to capture first-party data compliantly while keeping guest traffic isolated from corporate infrastructure.
Worked Examples
A 400-location retail chain currently uses a single WPA2-Personal password (PSK) shared across both staff tablets and PoS terminals. They are failing their PCI DSS audit under Requirement 8 (unique user IDs) and Requirement 1 (network segmentation). They need to secure the internal network without disrupting the existing guest WiFi captive portal. How should they re-architect their wireless security?
Step 1: Deploy a RADIUS server (e.g., Cisco ISE, Microsoft NPS, or FreeRADIUS) integrated with the corporate Active Directory. For a distributed estate, deploy RADIUS proxies at regional hubs to reduce authentication latency at remote sites.
Step 2: Reconfigure the corporate SSID on all wireless controllers to use WPA2-Enterprise. Configure 802.1X with PEAP-MSCHAPv2 for staff tablets (authenticating against AD user credentials) and EAP-TLS with machine certificates (deployed via MDM) for PoS terminals.
Step 3: Configure the RADIUS server to return dynamic VLAN assignment attributes. Staff tablets are assigned to a staff VLAN; PoS terminals are assigned to a strictly isolated PCI VLAN with ACLs permitting only traffic to the payment processor's IP range.
Step 4: Leave the guest SSID unchanged. It remains open (or WPA2-Personal with a publicly known PSK) but is mapped to a separate VLAN that routes directly to the Purple Guest WiFi captive portal. Guest traffic never touches the PCI VLAN.
Step 5: Enable RADIUS accounting on all APs to generate per-user authentication logs, satisfying PCI DSS audit trail requirements.
A university campus is experiencing credential harvesting attacks. Students are connecting to rogue access points broadcasting the official 'CampusNet' SSID. The network uses WPA2-Enterprise with PEAP-MSCHAPv2, but the student devices are not configured to validate the RADIUS server certificate. What is the attack vector, and how should the network team remediate it?
The attack is an Evil Twin. The attacker deploys a rogue AP broadcasting 'CampusNet' with a higher signal strength. Student devices, configured to trust any server presenting a PEAP challenge, connect to the rogue AP and complete the PEAP handshake, transmitting their hashed AD credentials to the attacker's server.
Remediation Step 1: Identify the Root CA that issued the RADIUS server's TLS certificate. If using an internal CA, ensure this CA certificate is distributed to all student and staff devices.
Remediation Step 2: Create a wireless network profile (via MDM for university-managed devices, or a downloadable configuration profile for BYOD) that specifies: (a) the exact RADIUS server hostname to validate against, (b) the trusted Root CA, and (c) the 'Validate Server Certificate' flag set to true.
Remediation Step 3: Deploy rogue AP detection on the wireless LAN controllers. Configure alerts for any AP broadcasting 'CampusNet' that is not in the authorised AP inventory.
Remediation Step 4: For BYOD devices, consider deploying an onboarding tool (such as Cloudpath or Cisco ISE's BYOD portal) that automates the supplicant configuration, removing the burden from end users.
Practice Questions
Q1. Your organisation is migrating from WPA2-Personal to WPA2-Enterprise across 50 office locations. During pilot testing, users report that their Windows laptops display a prompt asking them to 'Accept a Certificate' before they can enter their username and password. Several users click 'Reject' and cannot connect. What is causing this behaviour, and how should it be resolved before the full rollout?
Hint: Consider the role of the supplicant in PEAP authentication and how it verifies the identity of the RADIUS server before transmitting credentials.
View model answer
The Windows supplicant is performing server certificate validation as part of the PEAP TLS handshake. Because the RADIUS server's certificate was issued by an internal CA that is not in the device's trusted root store, Windows prompts the user to manually accept it. Relying on users to accept certificates is both a poor user experience and a security risk — users who click 'Accept' on any certificate are equally susceptible to Evil Twin attacks. The correct resolution is to use Group Policy (GPO) to distribute the internal Root CA certificate to all corporate devices and to pre-configure the Windows wireless profile to automatically trust it and validate the RADIUS server hostname. This eliminates the prompt entirely and enforces certificate validation without user intervention.
Q2. A hospital IT director needs to connect IoT medical devices (infusion pumps, patient monitoring systems) to the wireless network. These devices run embedded firmware with no 802.1X supplicant capability and can only connect using a static Pre-Shared Key. How should the network architect handle these devices without compromising the overall security posture?
Hint: Think about network segmentation, VLAN isolation, and the risks associated with MAC Authentication Bypass as an alternative to 802.1X.
View model answer
Since these devices cannot perform 802.1X, the architect has two options: WPA2-Personal (PSK) on a dedicated SSID, or MAC Authentication Bypass (MAB) on the corporate SSID. MAB is generally preferable for auditability but carries spoofing risks. Regardless of the authentication method chosen, the critical control is network segmentation. These devices must be placed on a dedicated, isolated VLAN with strict ACLs permitting only the specific traffic flows required — for example, communication to the clinical management server on a specific port, with all other traffic blocked. The SSID or MAB VLAN must have no routing path to the corporate network, the PoS environment, or the internet. Additionally, the PSK (if used) should be rotated periodically and managed centrally. Devices should be inventoried by MAC address, and any unrecognised MAC attempting to join the medical device VLAN should trigger an alert.
Q3. A stadium CIO is evaluating Passpoint (Hotspot 2.0) to improve the fan WiFi onboarding experience at a 60,000-capacity venue. The CIO asks: 'Does Passpoint replace WPA2 and 802.1X, or does it use them?' How do you respond, and what are the key operational considerations for a deployment at this scale?
Hint: Consider what Passpoint actually automates versus what it replaces, and the RADIUS capacity requirements for a high-density venue.
View model answer
Passpoint does not replace WPA2 or 802.1X — it automates and abstracts them. Passpoint is a provisioning and discovery layer built on top of WPA2-Enterprise (or WPA3-Enterprise) and 802.1X. It uses 802.1X for authentication (typically via credentials from a mobile carrier or a loyalty app identity provider) and WPA2/WPA3 to encrypt the resulting session. From the fan's perspective, their device connects automatically without any manual configuration. From the network's perspective, every connection is a full 802.1X exchange. The key operational considerations at 60,000 capacity are: (1) RADIUS infrastructure must be sized to handle concurrent authentication storms — particularly at kick-off when thousands of devices attempt to connect simultaneously; (2) RADIUS servers should be deployed with load balancing and geographic redundancy; (3) the identity provider (such as Purple under the OpenRoaming framework) must have sufficient throughput agreements; and (4) the wireless controller must support fast BSS transition (802.11r) to minimise re-authentication overhead as fans move around the venue.
Continue reading in this series
Per-Device PSK by Vendor: iPSK, DPSK, MPSK and PPSK Compared (and WPA3 Support)
A comprehensive comparison of per-device PSK implementations across Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet, and Ubiquiti UniFi. Learn how WPA3-SAE impacts per-device key strategies and when to deploy transition modes versus moving to 802.1X.
Per-Device PSK by Vendor: iPSK, DPSK, MPSK and PPSK Compared (and WPA3 Support)
A comprehensive comparison of per-device PSK implementations across Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet, and Ubiquiti UniFi. Learn how WPA3-SAE impacts per-device key strategies and when to deploy transition modes versus moving to 802.1X.
Captive Portal Authentication Methods Compared
This authoritative technical reference guide evaluates the architectural, operational, and compliance trade-offs of five core captive portal authentication methods. It provides network architects, IT directors, and marketing managers with the quantitative data and decision frameworks required to balance guest onboarding friction with data-collection requirements across enterprise venues.