What Is WiFi Marketing for Hotels? A Hotelier's Guide
This authoritative guide details how hotel IT and operations teams can leverage guest WiFi infrastructure to capture first-party data, drive direct bookings, and personalise the guest experience at scale. It covers technical architecture from captive portal authentication through to CRM integration, compliance obligations under GDPR and PCI DSS, and practical deployment strategies for properties of any size. Venue operators and IT teams will find concrete implementation steps, worked scenarios, and measurable ROI frameworks to justify and execute a WiFi marketing deployment this quarter.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: How WiFi Marketing Works
- Authentication Architecture
- Presence Analytics and MAC Address Tracking
- Network Architecture and Vendor Compatibility
- Implementation Guide: Deploying WiFi Marketing in a Hotel
- Phase 1: Infrastructure Assessment
- Phase 2: Captive Portal Design and Configuration
- Phase 3: CRM and Marketing Automation Integration
- Best Practices for Hotel WiFi Marketing
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
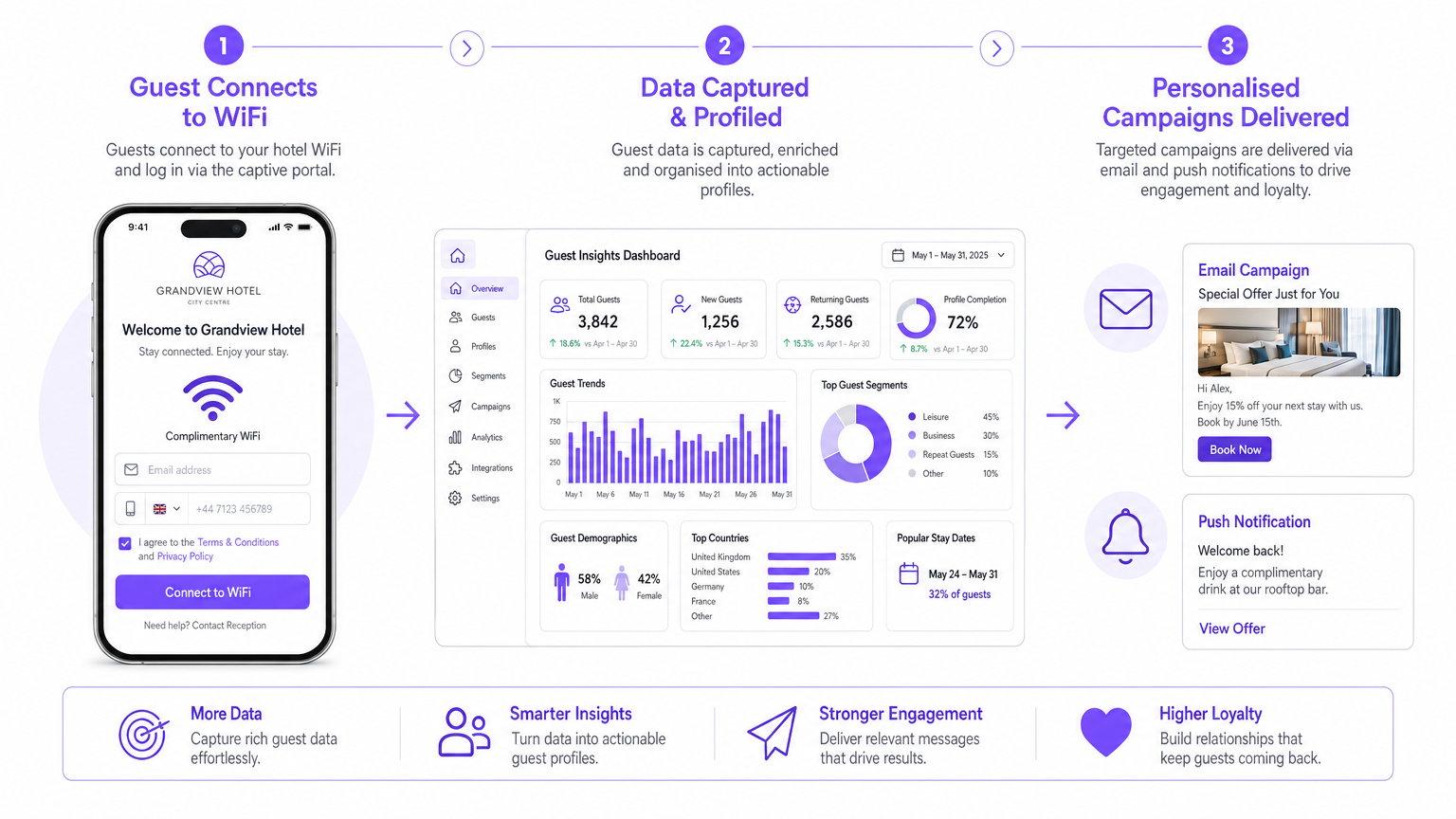
For modern hoteliers and venue operators, guest WiFi is no longer merely a cost centre or an expected utility — it is a critical first-party data acquisition channel. WiFi marketing for hotels transforms standard network access into a powerful CRM and marketing automation tool. By capturing authenticated guest data during the login process, hotels can build detailed guest profiles, understand venue analytics, and deploy highly targeted, automated campaigns that drive direct bookings and increase ancillary revenue.
This guide provides a comprehensive technical reference for IT managers, network architects, and operations directors evaluating or deploying a Guest WiFi solution. We explore the underlying architecture of WiFi marketing platforms, data capture mechanisms, compliance obligations, and the strategic deployment of WiFi Analytics to drive measurable ROI. Whether managing a boutique property or a multi-site resort group, understanding the mechanics of WiFi marketing is essential for modernising the guest experience and maximising direct revenue in an increasingly competitive landscape.
Technical Deep-Dive: How WiFi Marketing Works
At its core, WiFi marketing for hotels relies on a captive portal — a web page that intercepts a user's HTTP or HTTPS request before granting network access. Instead of a simple pre-shared key (PSK) printed on a keycard, guests authenticate via email, social media credentials, or loyalty programme login. This authentication event is the primary data capture trigger.
Authentication Architecture
When a guest's device associates with the hotel SSID, the access point (AP) or wireless LAN controller places the device in a restricted VLAN. All outbound HTTP traffic is intercepted and redirected to the captive portal URL via a DNS hijack or HTTP 302 redirect. The portal itself is served from the WiFi marketing platform's cloud infrastructure — in Purple's case, a globally distributed, highly available environment.
The portal communicates with a RADIUS (Remote Authentication Dial-In User Service) server to handle AAA: Authentication, Authorisation, and Accounting. Upon successful submission of credentials, the RADIUS server signals the controller to move the device to the unrestricted VLAN, granting full internet access. Simultaneously, the captured profile data — name, email address, demographic information, and consent flags — is transmitted via a secure REST API call to the hotel's CRM or Property Management System (PMS).
Modern deployments support IEEE 802.1X port-based access control for corporate guest segments, while consumer-facing SSIDs use the captive portal flow described above. WPA3 encryption should be enforced on all SSIDs to protect data in transit, replacing the increasingly vulnerable WPA2 standard.
Presence Analytics and MAC Address Tracking
Data capture begins before a guest ever opens a browser. As a device powers on and scans for available networks, it broadcasts probe requests containing its MAC address. The hotel's AP infrastructure captures these probe requests and forwards them to the analytics platform. This enables presence analytics — the ability to calculate dwell times, count unique visitors versus repeat visitors, and map movement patterns across the property without requiring active authentication.
This data is particularly valuable for Hospitality operators seeking to understand guest flow between the lobby, restaurant, spa, and conference facilities. It is the WiFi equivalent of footfall counting in Retail environments, providing a continuous, passive data stream that informs staffing decisions and venue layout optimisation. For a deeper look at location intelligence methodologies, see our Indoor Positioning System: UWB, BLE, & WiFi Guide .
Note on MAC Randomisation: iOS 14+ and Android 10+ devices use randomised MAC addresses for probe requests, which limits the accuracy of pre-authentication presence analytics. Authenticated sessions, however, use the device's true MAC address, preserving the integrity of post-login tracking and return-visit recognition.
Network Architecture and Vendor Compatibility
Enterprise WiFi marketing platforms are designed as vendor-agnostic overlays, integrating with existing infrastructure via cloud controller APIs. Purple supports integrations with Cisco Meraki, Aruba Central, Ruckus SmartZone, Ubiquiti UniFi, and others. The integration model typically involves:
| Integration Method | Description | Use Case |
|---|---|---|
| Cloud Controller API | Platform polls or receives webhooks from the controller | Real-time session data, policy enforcement |
| RADIUS Proxy | Platform acts as intermediary RADIUS server | Authentication for enterprise SSIDs |
| Splash Page URL | Controller redirects to externally hosted captive portal | Consumer-facing guest WiFi |
| SNMP / Syslog | Passive monitoring of network events | Presence analytics, anomaly detection |
Bandwidth management policies can be applied per user segment: basic throughput for unauthenticated users, standard for authenticated guests, and premium for loyalty members or conference delegates — all enforced at the controller level via RADIUS attributes.
Implementation Guide: Deploying WiFi Marketing in a Hotel
A structured deployment approach reduces risk and accelerates time-to-value. The following phases apply to properties of any scale.
Phase 1: Infrastructure Assessment
Before any platform configuration, conduct a thorough site survey. Verify AP coverage density in all guest-facing areas — lobbies, restaurants, meeting rooms, pool areas, and corridors. Assess the controller's compatibility with external captive portal redirect and RADIUS proxy configurations. Document existing VLAN architecture and firewall rules, as the captive portal requires specific DNS and HTTP traffic to be permitted through the walled garden.
Phase 2: Captive Portal Design and Configuration
The captive portal is the primary brand touchpoint in the WiFi marketing flow. It must be responsive across all device form factors and load within two seconds on a 3G connection to minimise abandonment. Key configuration decisions include:
Authentication Methods: Offer a minimum of two options — email registration and social login (Google, Facebook). For business hotels, LinkedIn authentication is highly effective for capturing professional demographic data. For loyalty-heavy brands, direct PMS integration allows returning members to authenticate with their loyalty number, enriching the existing profile rather than creating a duplicate.
Progressive Profiling: Collect data incrementally across multiple visits. On the first connection, require only an email address and explicit consent to marketing communications. On the second visit, recognised via MAC address, prompt for an additional data point — reason for travel, preferred room type, or F&B preferences — in exchange for a bandwidth upgrade or a complimentary amenity voucher.
Consent and Compliance: The portal must present a clear, plain-language privacy notice and a separate, unticked checkbox for marketing consent, in compliance with GDPR Article 7. Do not bundle WiFi access consent with marketing consent — these must be distinct, granular opt-ins. Retain consent records with timestamps for audit purposes.
Phase 3: CRM and Marketing Automation Integration
The WiFi platform's value is realised through its integrations. Connect the platform to the hotel's CRM (e.g., Salesforce, HubSpot) and PMS (e.g., Opera, Mews) via REST API or native connector. Configure the following automated campaign triggers as a baseline:
| Trigger Event | Campaign | Channel | Timing |
|---|---|---|---|
| First WiFi login | Welcome message + F&B offer | Within 15 minutes | |
| Check-out detected | Review request | 2 hours post-departure | |
| OTA booking detected | Direct booking incentive | 24 hours post-stay | |
| Return visit (MAC match) | Loyalty programme invitation | Email / SMS | On connection |
| Dwell in restaurant zone | Dining promotion | Push / SMS | During meal hours |

Best Practices for Hotel WiFi Marketing
Deployments that consistently deliver strong ROI share several characteristics. The following best practices are drawn from enterprise deployments across the Hospitality sector.
Treat the Captive Portal as a Conversion Page. Apply the same conversion rate optimisation (CRO) principles used for booking engine landing pages. A/B test the headline copy, the incentive offer, and the number of form fields. A reduction from five fields to two at initial login typically increases completion rates by 30–50%.
Enforce Network Segmentation. Guest WiFi must be isolated from the hotel's operational network (PMS terminals, door lock systems, payment infrastructure) using dedicated VLANs and firewall rules. This is a PCI DSS requirement for any property processing card payments over the network and a fundamental security baseline regardless.
Leverage Analytics for Operational Decisions. The presence analytics dashboard is not just a marketing tool. Peak connection hour data informs front desk staffing schedules. Heatmaps of dwell time identify underutilised revenue spaces. Visitor frequency data distinguishes transient guests from repeat visitors, enabling targeted loyalty acquisition campaigns.
Integrate with the Broader Martech Stack. WiFi data is most powerful when combined with PMS booking data, email engagement metrics, and loyalty programme activity. A guest who connects to WiFi, opens a post-stay email, and then books directly within 30 days represents a fully attributable, WiFi-influenced direct booking — a metric that directly quantifies the channel's ROI.
For a broader view of how WiFi marketing operates across the full guest journey, see How Does WiFi Marketing Work? .
Troubleshooting & Risk Mitigation
The following failure modes are the most commonly encountered in hotel WiFi marketing deployments.
Captive Portal Non-Appearance. The most frequent support ticket. Root causes include: DNS not resolving the portal URL (check walled garden configuration), HTTPS-only browser behaviour blocking the HTTP redirect (ensure the portal URL is HTTP for the initial redirect), or device-level captive portal detection failing (common on iOS with aggressive firewall rules). Resolution: whitelist Apple's captive portal detection endpoints (captive.apple.com, www.apple.com/library/test/success.html) in the walled garden.
Low Opt-In Rates. If fewer than 60% of connected devices are completing the portal login, the value exchange is failing. Audit the portal for: excessive form fields, unclear incentive, slow load time, or a missing social login option. A/B test a simplified two-field version.
Data Duplication in CRM. When guests connect on multiple devices or return after a device change, duplicate profiles can be created. Implement email-based deduplication logic in the CRM integration layer. Purple's platform supports profile merging based on email address as the primary key.
Integration Failures. API changes in the CRM or PMS can silently break the data sync. Implement webhook monitoring and alerting. Set up a daily reconciliation job that compares the count of WiFi sessions to the count of CRM records created, flagging discrepancies above a defined threshold.
ROI & Business Impact
The business case for WiFi marketing in hotels is well-established across the Hospitality sector. The primary ROI drivers are:
First-Party Database Growth. A mid-scale hotel with 150 rooms and 70% occupancy will generate approximately 38,000 guest nights per year. Even at a 65% portal completion rate, this represents over 24,000 net-new, opted-in profiles added to the marketing database annually — at a cost-per-acquisition significantly lower than any paid digital channel.
Direct Booking Uplift. Automated post-stay campaigns targeting OTA bookers with a direct booking incentive consistently achieve 3–8% conversion rates in hospitality deployments. For a 150-room property with an average daily rate of £120, converting just 5% of OTA bookings to direct saves approximately £18,000–£25,000 per year in OTA commission (at a 15–20% commission rate).
Ancillary Revenue. Location-triggered F&B promotions delivered via WiFi-connected devices during dwell time near restaurant zones have demonstrated 12–18% uplift in restaurant covers in multi-site hospitality deployments.
Operational Efficiency. Presence analytics data used to optimise housekeeping schedules and front desk staffing has delivered 5–10% reductions in labour costs in documented deployments.
The total cost of ownership for a cloud-managed WiFi marketing platform is typically recovered within 6–12 months at a 150-room property, with ongoing ROI driven by the compounding value of the first-party database and automated campaign performance.
Key Terms & Definitions
Captive Portal
A web page that intercepts a user's network request and requires interaction — typically authentication or consent — before granting full internet access.
The primary interface for guest data capture in WiFi marketing. IT teams configure the network controller to redirect unauthenticated devices to the portal URL.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorisation, and Accounting (AAA) for network access. Defined in RFC 2865.
The underlying protocol used to authenticate users against a database when they log in via the captive portal. The WiFi marketing platform acts as a RADIUS proxy or server.
Presence Analytics
The use of WiFi probe request data (MAC addresses and RSSI signal strength) to track the physical presence, dwell time, and movement of devices within a venue, without requiring active authentication.
Enables passive footfall counting and venue heatmapping. Accuracy is reduced by MAC randomisation on modern iOS and Android devices.
Walled Garden
A network policy that permits unauthenticated devices to access a defined list of URLs or IP addresses before completing captive portal authentication.
Required to allow the captive portal page itself to load, and to permit Apple and Google captive portal detection endpoints — preventing the portal from failing to appear on iOS and Android devices.
Progressive Profiling
A data collection strategy that gathers customer information incrementally across multiple interactions, rather than requesting all data at the point of first contact.
Applied to captive portals to reduce friction at initial login. The platform recognises returning devices via MAC address and prompts for additional data on subsequent visits.
First-Party Data
Data collected directly from customers through owned channels, with explicit consent, as opposed to data purchased from third-party brokers or inferred from third-party cookies.
The primary output of WiFi marketing. First-party data is more accurate, more compliant, and more durable than third-party data, particularly in a post-cookie digital landscape.
MAC Address Randomisation
A privacy feature in iOS 14+, Android 10+, and Windows 10+ that assigns a randomised MAC address to probe requests, preventing passive tracking of devices before authentication.
Limits the accuracy of pre-authentication presence analytics. Post-authentication sessions use the device's true MAC address, preserving return-visit recognition for logged-in guests.
IEEE 802.1X
An IEEE standard for port-based network access control, providing an authentication mechanism for devices wishing to connect to a LAN or WLAN.
Recommended for enterprise guest segments (e.g., conference delegates, corporate accounts) requiring certificate-based or credential-based authentication rather than a captive portal flow.
Geofencing
The definition of a virtual geographic boundary within a venue, enabling the platform to trigger automated actions when an authenticated device enters, dwells within, or exits the defined zone.
Used in hotel WiFi marketing to deliver location-contextual offers — for example, a dining promotion triggered when a guest's device dwells near a restaurant entrance during meal service hours.
WPA3 (Wi-Fi Protected Access 3)
The third generation of the WPA security certification programme, providing stronger encryption (SAE replacing PSK) and improved protection against brute-force attacks.
The current recommended security standard for hotel guest SSIDs. WPA2 remains widely deployed but is increasingly vulnerable to KRACK and dictionary attacks.
Case Studies
A 200-room city-centre business hotel currently offers free, unauthenticated WiFi via a shared WPA2 password distributed on keycards. The commercial director wants to reduce OTA dependency and increase direct bookings. The IT manager needs to implement a solution without replacing the existing Cisco Meraki infrastructure.
- Deploy Purple's cloud-managed captive portal, integrating with the existing Meraki dashboard via API. Configure a dedicated guest SSID with splash page redirect enabled, pointing to the Purple-hosted portal URL. 2. Design a two-field portal (email + marketing consent checkbox) with a LinkedIn social login option, given the business traveller demographic. 3. Configure a VLAN for guest traffic, isolated from the hotel's operational network, with firewall rules blocking inter-VLAN routing. 4. Integrate the Purple platform with the hotel's CRM via REST API, mapping the captured email address and consent flag to the CRM contact schema. 5. Build three automated email campaigns: a welcome email with a direct booking discount code (triggered on first login), a post-stay review request (triggered 2 hours after the last session ends), and a 'book direct next time' campaign targeting guests whose booking source in the PMS is flagged as an OTA (triggered 48 hours post-departure). 6. Set up the analytics dashboard to track weekly database growth, campaign open rates, and attributed direct bookings.
A 450-room resort with multiple F&B outlets, a spa, and a conference centre wants to use WiFi data to increase in-stay ancillary spend. The marketing team has no visibility into which guests are using which facilities, and the current WiFi system provides no analytics beyond basic uptime monitoring.
- Deploy a WiFi marketing platform with presence analytics enabled across all APs, including those in the restaurant, spa reception, pool bar, and conference lobby. 2. Define geofence zones corresponding to each revenue centre. 3. Configure location-triggered campaigns: when a guest's authenticated device dwells in the pool zone for more than 20 minutes between 12:00 and 14:00, trigger an SMS offering a 15% discount at the poolside bar, valid for 2 hours. When a device is detected in the spa reception zone, trigger an email promoting available treatment slots for that day. 4. Integrate the WiFi platform with the PMS to cross-reference room type and length of stay, enabling segmentation of leisure guests (more likely to respond to spa offers) versus conference delegates (more likely to respond to F&B and evening entertainment offers). 5. Build a weekly analytics report tracking geofence trigger volume, campaign redemption rate, and incremental revenue per triggered campaign.
Scenario Analysis
Q1. A hotel IT manager is configuring the captive portal for a new 180-room property. The commercial director wants to maximise the volume of marketing-opted-in profiles captured. The IT manager is concerned that a long registration form will cause guests to abandon the portal and use mobile data instead. How should the portal be configured to balance data acquisition with user experience?
💡 Hint:Consider how much data is strictly necessary for the initial connection versus what can be gathered on subsequent visits using device recognition.
Show Recommended Approach
Implement progressive profiling. For the initial connection, require only an email address and a separate, unticked marketing consent checkbox. On subsequent visits, the platform recognises the returning device via MAC address and prompts for one additional data point — reason for travel, preferred room type, or loyalty number — in exchange for a tangible incentive such as a bandwidth upgrade or a complimentary amenity. This approach typically achieves 70–80% initial completion rates versus 40–50% for a five-field form, while still building a rich profile over time. The commercial director's objective is served by maximising the number of opted-in email addresses captured, which is best achieved by minimising friction at the point of first contact.
Q2. During a network security audit, the CTO of a 300-room hotel discovers that the guest WiFi SSID shares a VLAN with the hotel's PMS terminals and door lock management system. The current setup uses a single WPA2 pre-shared key for all devices. What are the primary risks, and what remediation steps should be prioritised?
💡 Hint:Evaluate both the security implications of shared network access and the compliance obligations under PCI DSS for payment-adjacent systems.
Show Recommended Approach
The primary risks are: (1) Network lateral movement — a compromised guest device on the shared VLAN could attempt to access PMS terminals or door lock systems, representing a significant physical security and data breach risk. (2) PCI DSS non-compliance — any system that processes, stores, or transmits cardholder data must be isolated from untrusted networks; a shared guest/PMS VLAN is a direct violation of PCI DSS Requirement 1.3. (3) Zero data capture — the shared PSK provides no authentication event, meaning no guest profiles are being built. Remediation priority: (1) Immediately create a dedicated guest VLAN with firewall rules blocking all inter-VLAN routing to operational systems. (2) Deploy a captive portal on the guest SSID to replace the shared PSK. (3) Engage a QSA (Qualified Security Assessor) to validate the new network segmentation against PCI DSS requirements before the next assessment cycle.
Q3. A venue operations director at a large conference hotel reviews the presence analytics dashboard and notices that a high volume of devices are detected near the hotel's business centre between 08:00 and 10:00, but very few devices are authenticated (logged in via the captive portal) during that period. What does this data indicate, and what actions should be taken?
💡 Hint:Differentiate between passive presence detection (MAC probe requests) and active authentication (captive portal login). Consider why the gap might exist and what it costs the business.
Show Recommended Approach
The data indicates that a significant number of guests are physically present in the business centre but are not connecting to the hotel WiFi — they are likely using mobile data or a corporate VPN that bypasses the captive portal. This represents a lost data acquisition opportunity. Actions to take: (1) Investigate whether the captive portal is appearing correctly on corporate devices — enterprise security configurations often suppress captive portal detection. Consider offering an alternative authentication method (e.g., a QR code linking directly to the portal URL) displayed on signage in the business centre. (2) Review the portal's value proposition for business travellers — a higher bandwidth tier or a complimentary printing credit may be a more compelling incentive than a generic welcome message. (3) Assess whether IEEE 802.1X authentication would be more appropriate for this segment, as it integrates with corporate device management and removes the captive portal friction entirely while still capturing an authenticated identity.



