Asegurando el trabajo híbrido: Combinando NAC con ZTNA para un acceso sin interrupciones
Esta guía técnica autorizada cubre la convergencia arquitectónica de Network Access Control (NAC) y Zero Trust Network Access (ZTNA) para asegurar entornos de trabajo híbridos en sedes corporativas, minoristas, hosteleras y del sector público. Proporciona un plan de implementación por fases, estudios de casos reales y orientación sobre cumplimiento para arquitectos de TI y CTOs que necesitan eliminar las brechas de seguridad creadas por dominios de acceso aislados en local y en la nube.
Escuchar esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado: La Arquitectura de Convergencia
- Las Limitaciones de los Dominios de Seguridad Aislados
- Intermediación Unificada de Identidad y Contexto
- Guía de Implementación: Despliegue Paso a Paso
- Fase 1: Descubrimiento de Identidades y Activos
- Fase 2: Definición de Políticas y Microsegmentación
- Fase 3: Aplicación y Optimización
- Mejores Prácticas para Entornos Empresariales
- Resolución de Problemas y Mitigación de Riesgos
- ROI e Impacto Empresarial

Resumen Ejecutivo
Para los arquitectos de redes empresariales y los CTOs que gestionan entornos distribuidos, el perímetro se ha disuelto irrevocablemente. El modelo tradicional de asegurar una sede corporativa con un robusto Network Access Control (NAC) mientras se depende de VPNs heredadas para el acceso remoto ya no es viable. Las empresas modernas requieren una postura de seguridad unificada que conecte sin problemas la infraestructura local con las aplicaciones nativas de la nube. Esta guía detalla la integración arquitectónica de NAC y Zero Trust Network Access (ZTNA), proporcionando un plan para asegurar entornos de trabajo híbridos sin comprometer la experiencia del usuario ni el rendimiento de la red.
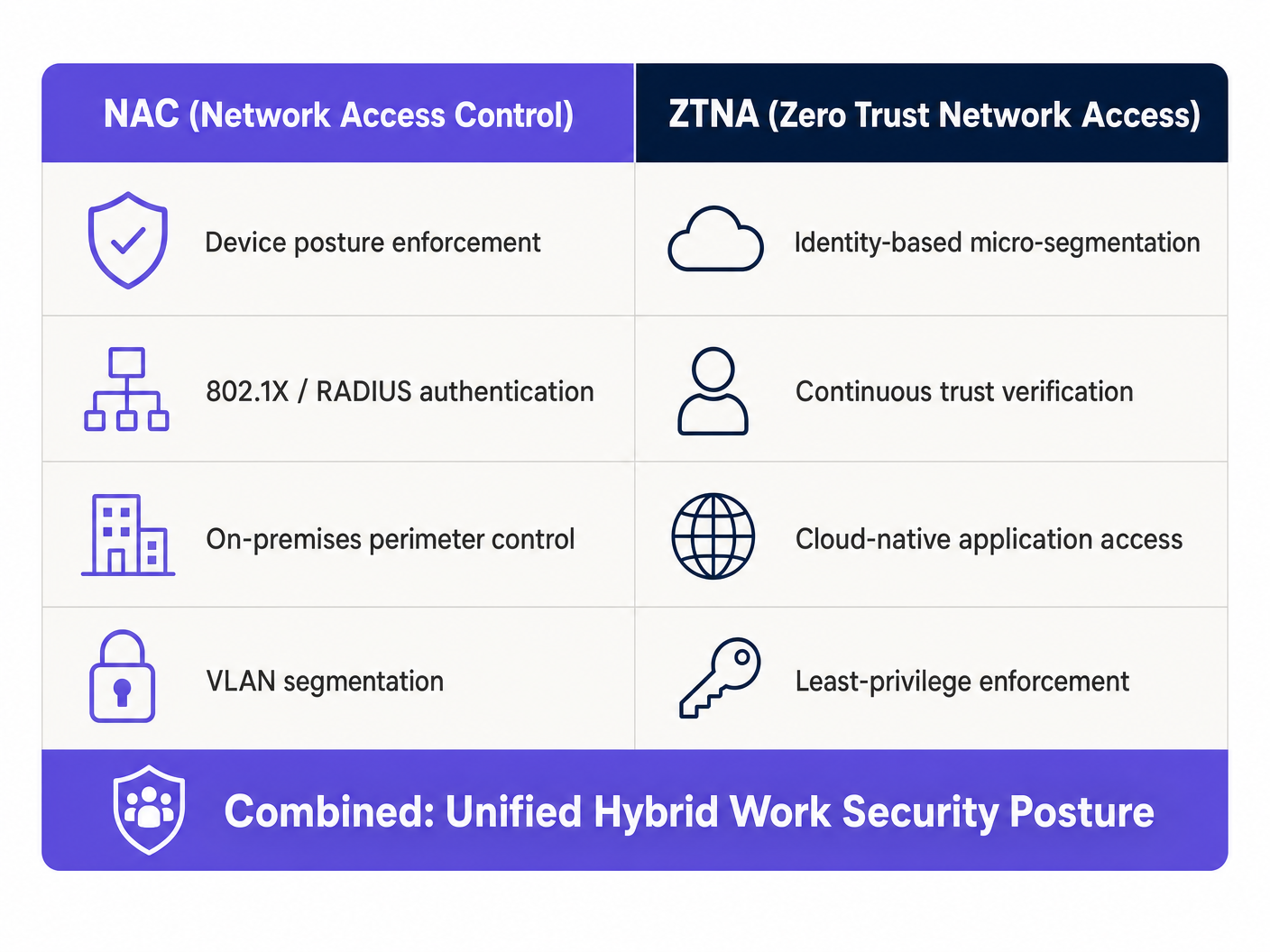
Al combinar la aplicación de la postura a nivel de dispositivo de NAC con la microsegmentación centrada en la identidad de ZTNA, las organizaciones pueden lograr una verificación continua de la confianza independientemente de la ubicación del usuario. Esta convergencia es particularmente crítica para sectores con gran afluencia de público y requisitos de cumplimiento complejos, como Retail , Healthcare y Hospitality . Además, el aprovechamiento de plataformas como la infraestructura de Guest WiFi de Purple puede extender estos principios de confianza cero a las redes de invitados, asegurando un aislamiento robusto y protección de datos alineados con las obligaciones de GDPR y PCI DSS.
Análisis Técnico Detallado: La Arquitectura de Convergencia
Las Limitaciones de los Dominios de Seguridad Aislados
Históricamente, NAC y ZTNA operaban como dominios de seguridad aislados. NAC, aprovechando IEEE 802.1X y RADIUS, destacaba en el control del acceso físico e inalámbrico dentro del perímetro corporativo. Proporcionaba un robusto perfilado de dispositivos, evaluación de la postura y asignación de VLAN. Por el contrario, ZTNA surgió para asegurar el acceso remoto a aplicaciones en la nube y locales, operando bajo el principio de "nunca confiar, siempre verificar" basado en la identidad y el contexto del usuario, en lugar de la ubicación de la red.
La fricción surge cuando los trabajadores híbridos transitan entre estos dominios. Un usuario que se autentica sin problemas a través de ZTNA en casa a menudo se enfrenta a una experiencia inconexa al entrar en la oficina corporativa, donde las políticas de NAC pueden no alinearse con su contexto de ZTNA. Esta fragmentación introduce puntos ciegos de seguridad y una sobrecarga operativa que impacta directamente tanto en la eficiencia de TI como en la productividad del usuario final.
Intermediación Unificada de Identidad y Contexto
La solución arquitectónica reside en establecer una capa unificada de intermediación de identidad y contexto que sincronice la telemetría entre los motores de políticas de NAC y ZTNA. Esta integración permite una evaluación continua de la postura que persiste a través de los límites de la red.
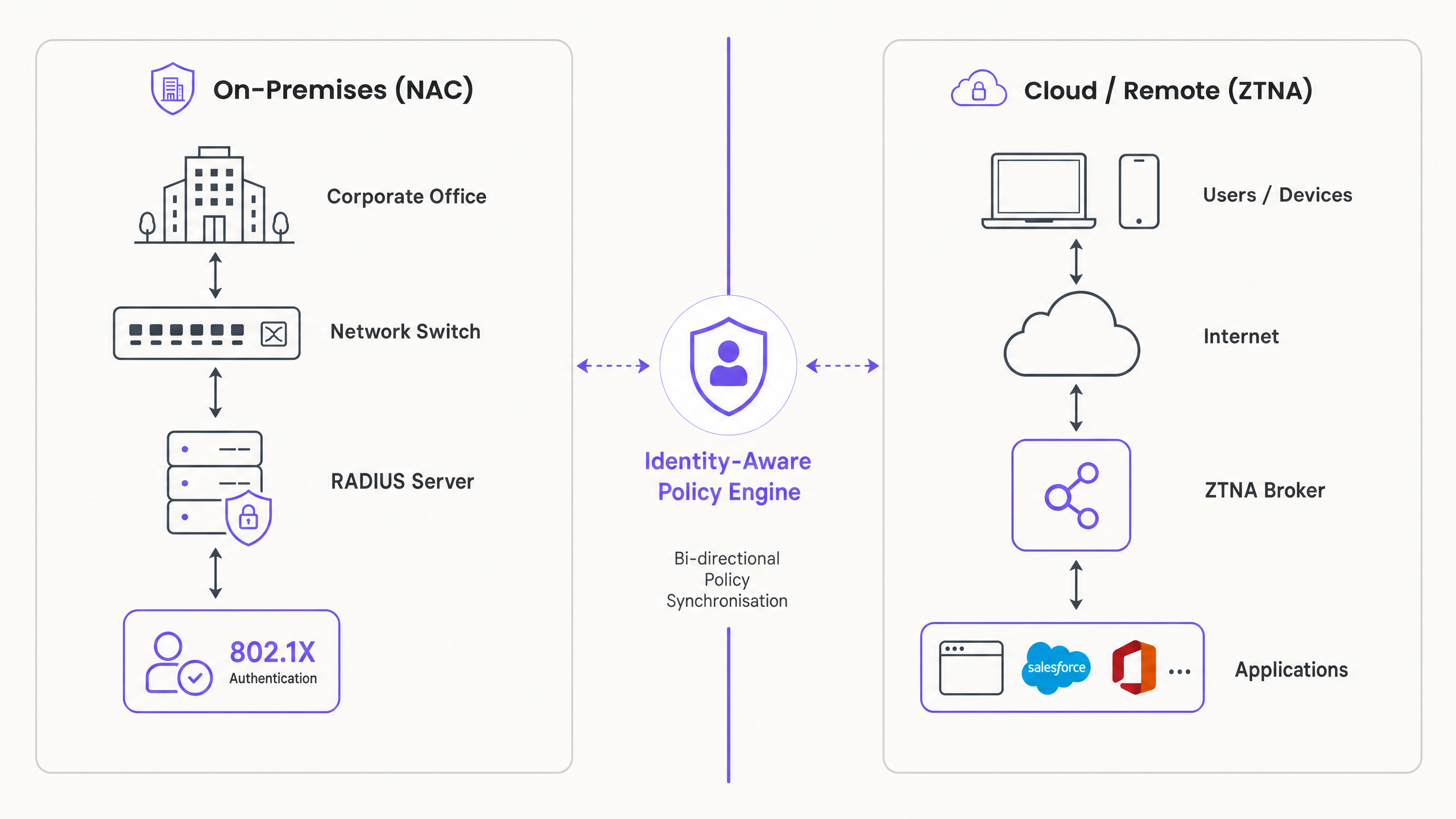
La integración opera a través de tres mecanismos clave. Primero, Evaluación Continua de la Postura: cuando un dispositivo se conecta a la red corporativa, la solución NAC realiza una verificación exhaustiva de la postura que cubre la versión del sistema operativo, el estado del antivirus y la validación del certificado. Este contexto se comparte inmediatamente con el intermediario de ZTNA a través de la integración de API. Segundo, Aplicación Dinámica de Políticas: si la postura del dispositivo se degrada —por ejemplo, se detecta malware—, el sistema NAC pone en cuarentena el dispositivo en la red local, mientras instruye simultáneamente al intermediario de ZTNA para que revoque el acceso a aplicaciones críticas en la nube. Tercero, Transición Sin Interrupciones: a medida que el usuario se mueve de la oficina a una ubicación remota, el cliente ZTNA mantiene el contexto de confianza establecido, eliminando la necesidad de reautenticación y asegurando un acceso ininterrumpido a los recursos autorizados.
Para una comprensión más profunda de las tecnologías inalámbricas subyacentes que soportan estas implementaciones, consulte nuestra guía sobre Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
Guía de Implementación: Despliegue Paso a Paso
El despliegue de una arquitectura NAC/ZTNA convergente requiere un enfoque por fases para minimizar las interrupciones y asegurar una aplicación robusta de las políticas.
Fase 1: Descubrimiento de Identidades y Activos
Antes de implementar políticas de aplicación, debe lograr una visibilidad completa de su entorno de red. Despliegue su solución NAC en modo de solo monitoreo — configúrela para descubrir y perfilar todos los dispositivos conectados, incluyendo portátiles corporativos, BYOD, IoT y dispositivos de invitados, sin bloquear el acceso. Consolide las identidades de usuario integrando las soluciones NAC y ZTNA con un proveedor de identidad central como Azure AD u Okta. Esto asegura políticas de autenticación consistentes en ambos dominios. Simultáneamente, utilice su solución ZTNA para monitorear los patrones de acceso a las aplicaciones, identificando qué usuarios requieren acceso a aplicaciones específicas y formando la base de sus políticas de microsegmentación.
Fase 2: Definición de Políticas y Microsegmentación
Pase de la visibilidad al control definiendo políticas de acceso granular basadas en el principio de mínimo privilegio. Establezca requisitos de seguridad de referencia para los dispositivos corporativos, incluyendo la versión mínima del sistema operativo y los requisitos de agente EDR activo, y configure la solución NAC para aplicar estos requisitos para el acceso local. Defina políticas de ZTNA que restrinjan el acceso a las aplicaciones basándose en el rol del usuario y el contexto del dispositivo, asegurando la alineación con los requisitos de postura definidos en la solución NAC. Fundamentalmente, configure la integración de API entre sus plataformas NAC y ZTNA para permitir el intercambio bidireccional de contexto, asegurando que un cambio en la postura del dispositivo detectado por NAC iminmediatamente activa una actualización de política en el bróker ZTNA.
Fase 3: Aplicación y Optimización
Habilite gradualmente el modo de aplicación, supervisando las anomalías y ajustando las políticas según sea necesario. Transicione la solución NAC del modo de monitorización al modo de aplicación, comenzando con un grupo piloto de usuarios o ubicaciones, y supervise los fallos de autenticación. Implemente el cliente ZTNA en todos los endpoints corporativos, asegurando un acceso sin interrupciones a las aplicaciones en la nube y locales. Extienda políticas robustas de acceso para invitados utilizando plataformas como Guest WiFi de Purple, asegurando que el tráfico de invitados esté estrictamente aislado de los recursos corporativos. Aproveche WiFi Analytics para monitorizar los patrones de uso y detectar posibles anomalías en la red de invitados.
Mejores Prácticas para Entornos Empresariales
Priorice la experiencia del usuario durante toda la implementación. La seguridad no debe impedir la productividad, y la transición entre el acceso local y remoto debe ser transparente para el usuario, aprovechando el inicio de sesión único y los mecanismos de autenticación continua. Para el acceso local, exija la autenticación IEEE 802.1X para todos los dispositivos corporativos, ya que esto proporciona una validación criptográfica robusta de la identidad del dispositivo a nivel de puerto.
Integre capacidades de detección de amenazas impulsadas por IA en sus soluciones NAC y ZTNA para identificar comportamientos anómalos y poner en cuarentena automáticamente los dispositivos comprometidos. Para una perspectiva de futuro sobre esta capacidad, consulte The Future of Wi-Fi Security: AI-Driven NAC and Threat Detection y su equivalente en español El Futuro de la Seguridad Wi-Fi: NAC Impulsado por IA y Detección de Amenazas . Para empresas distribuidas, la integración de ZTNA con SD-WAN puede optimizar el enrutamiento de aplicaciones y mejorar el rendimiento en múltiples sitios; revise nuestra comparación en SD WAN vs MPLS: The 2026 Enterprise Network Guide .
Resolución de Problemas y Mitigación de Riesgos
Los Retrasos en la Sincronización de Contexto representan el modo de fallo más crítico. Si la integración de la API entre NAC y ZTNA experimenta latencia, un dispositivo comprometido podría retener el acceso a las aplicaciones en la nube durante más tiempo del aceptable. La mitigación consiste en implementar notificaciones push basadas en webhooks en lugar de depender únicamente de mecanismos de sondeo, asegurando actualizaciones de políticas casi en tiempo real.
Las Políticas Demasiado Restrictivas pueden causar picos significativos en los tickets de soporte técnico al implementar comprobaciones estrictas de postura sin una comunicación adecuada con el usuario. Utilice Captive Portals para informar a los usuarios sobre el incumplimiento y proporcionar instrucciones de remediación de autoservicio antes de bloquear completamente el acceso.
Los Fallos de Autenticación de Dispositivos IoT son inevitables en entornos de recintos. Los dispositivos IoT sin interfaz de usuario no pueden soportar clientes 802.1X o ZTNA. La solución es MAC Authentication Bypass (MAB) combinado con un riguroso perfilado de dispositivos y una estricta segmentación VLAN para aislar el tráfico IoT de los recursos corporativos.
La Monitorización del Estado de la Integración de la API se pasa por alto con frecuencia. Si la sincronización entre NAC y ZTNA se interrumpe, existe una brecha de seguridad que ninguno de los sistemas puede resolver de forma independiente. Implemente una monitorización y alerta dedicadas sobre el estado de la integración, y defina políticas a prueba de fallos que activen restricciones de acceso automáticas si la sincronización se pierde durante más de un umbral definido.
ROI e Impacto Empresarial
La convergencia de NAC y ZTNA ofrece un valor empresarial medible más allá de la mitigación de riesgos. La consolidación de la gestión de políticas reduce la carga administrativa de los equipos de TI, permitiéndoles centrarse en iniciativas estratégicas en lugar de gestionar silos de seguridad dispares. La eliminación de las VPN heredadas mejora significativamente la experiencia de trabajo híbrido, reduciendo el tiempo de inactividad y la frustración, al tiempo que mejora el rendimiento de las aplicaciones para los usuarios remotos.
La capacidad de demostrar una evaluación continua de la postura y un control de acceso basado en la identidad simplifica la elaboración de informes de cumplimiento para marcos como PCI DSS y GDPR, particularmente relevante en entornos de Transport y minoristas donde las obligaciones de protección de datos de titulares de tarjetas y datos personales son estrictas. Las organizaciones que han implementado arquitecturas convergentes informan consistentemente una reducción en el tiempo medio de contención (MTTC) de incidentes de seguridad, ya que la aplicación bidireccional de políticas permite la cuarentena automatizada sin requerir intervención manual.
Definiciones clave
Network Access Control (NAC)
A security solution that enforces policy on devices seeking access to a network infrastructure, typically utilising IEEE 802.1X for authentication and posture assessment to determine VLAN assignment and access rights.
Critical for securing on-premises environments, ensuring only compliant and authorised devices can connect to corporate switches and wireless access points. IT teams encounter this when managing physical office and venue networks.
Zero Trust Network Access (ZTNA)
An IT security solution that provides secure remote access to applications and services based on defined access control policies, operating on the principle of least privilege and continuous identity verification rather than network location.
Replaces legacy VPNs by providing identity-based micro-segmentation, granting access only to specific applications rather than the entire network. Relevant when securing remote workers and cloud application access.
Micro-segmentation
The practice of dividing a network into isolated segments to reduce the attack surface and prevent lateral movement by threat actors, applied at the application or workload level rather than the network perimeter.
ZTNA applies this concept at the application level, ensuring a compromised endpoint cannot pivot to access unauthorised resources. IT teams encounter this when designing zero-trust architectures.
Posture Assessment
The process of evaluating a device's security state — including OS version, active antivirus, installed certificates, and patch level — before granting network or application access.
A core function of NAC, ensuring that vulnerable or compromised devices are quarantined or remediated before they can interact with the corporate network. Relevant during device onboarding and continuous monitoring.
IEEE 802.1X
An IEEE standard for port-based Network Access Control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN, using EAP (Extensible Authentication Protocol) over the network medium.
The gold standard for enterprise network authentication, providing robust cryptographic validation of device identity. IT teams encounter this when configuring switches, wireless controllers, and RADIUS servers.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service, acting as the communication layer between NAC and identity providers.
The backend protocol utilised by NAC solutions to communicate with identity providers and enforce access policies. Relevant when integrating NAC with Active Directory or cloud IdPs.
MAC Authentication Bypass (MAB)
A fallback authentication method used by NAC solutions for devices that do not support 802.1X, relying on the device's MAC address as an identifier to assign network access policies.
Necessary for accommodating headless devices — printers, IoT sensors, digital signage — in enterprise environments. Less secure than 802.1X and requires strict VLAN segmentation to mitigate MAC spoofing risks.
Identity Provider (IdP)
A system entity that creates, maintains, and manages identity information for principals while providing authentication services to relying applications within a federation or distributed network.
The central source of truth for user identities, integrating with both NAC and ZTNA to ensure consistent authentication policies. IT teams encounter this when configuring SSO and MFA across enterprise systems.
VLAN (Virtual Local Area Network)
A logical subdivision of a physical network that groups devices into isolated broadcast domains, enabling traffic segmentation without requiring separate physical infrastructure.
The primary mechanism for isolating different device classes — corporate, guest, IoT — within a shared physical network. Critical for compliance with PCI DSS requirements for cardholder data environment isolation.
Ejemplos prácticos
A global retail chain with 500 locations needs to secure access for regional managers who frequently travel between stores, corporate headquarters, and remote home offices. They currently experience frequent VPN disconnects and inconsistent access to cloud-hosted inventory management applications.
Implement a converged NAC/ZTNA architecture across all locations. Deploy 802.1X via NAC for seamless, secure access when managers are physically in-store or at HQ, authenticating against a centralised RADIUS server integrated with Azure AD. Deploy a ZTNA client on all corporate laptops. Integrate the NAC and ZTNA policy engines via API, configuring webhook notifications for immediate posture updates. When a manager connects to the in-store network, the NAC authenticates the device and shares the 'trusted internal' context with the ZTNA broker. The ZTNA broker then grants direct, optimised access to the cloud-hosted inventory application without requiring a VPN tunnel, reducing latency and eliminating disconnection issues. When the manager works from home, the ZTNA client establishes a secure micro-tunnel to the application, maintaining the same access policies without relying on the corporate network perimeter. Guest and IoT devices in-store are isolated on separate VLANs managed via Purple's Guest WiFi platform.
A large conference centre needs to provide secure WiFi for corporate staff while isolating thousands of daily guest connections and third-party vendor IoT devices including digital signage, BLE beacons, and environmental sensors.
Deploy a robust NAC solution configured with strict VLAN segmentation across three distinct tiers. Tier one: corporate staff devices authenticate via 802.1X and are assigned to a secure internal VLAN with full access to internal management systems. Tier two: implement Purple's Guest WiFi platform to manage public access, capturing valuable analytics while ensuring complete isolation from the corporate network via a dedicated guest VLAN with internet-only access. Tier three: for vendor IoT devices, utilise MAC Authentication Bypass (MAB) combined with deep device profiling — analysing DHCP fingerprints, HTTP user agents, and traffic patterns — to accurately identify device types and assign them to restricted, internet-only VLANs. Integrate ZTNA for corporate staff to access internal management applications securely from any location within the venue or remotely. For BLE beacon infrastructure, refer to the guide on BLE Low Energy Explained for Enterprise for integration considerations.
Preguntas de práctica
Q1. Your organisation is deploying ZTNA to replace a legacy VPN. However, users returning to the corporate office are experiencing latency when accessing applications hosted locally in the on-premises data centre, as ZTNA traffic is routing through a cloud-hosted broker. What is the recommended architectural solution?
Sugerencia: Consider how the ZTNA client determines the optimal path to the application based on the user's physical network context.
Ver respuesta modelo
Implement a Local Edge or On-Premises ZTNA Broker within the corporate data centre. Configure the ZTNA client to detect when the device is authenticated on the internal corporate network via NAC and route traffic directly to the local application via the internal broker, rather than hair-pinning through the cloud-hosted broker. This reduces latency for on-premises applications while maintaining the same identity-based access controls. The NAC context sharing via API should signal to the ZTNA broker that the device is on a trusted internal network, enabling the local routing decision.
Q2. A hospital IT team needs to secure hundreds of connected medical devices — infusion pumps, patient monitors, imaging equipment — that cannot run 802.1X supplicants or ZTNA clients. How should these devices be secured within a converged NAC/ZTNA architecture?
Sugerencia: Consider fallback authentication methods and the principle of network-level isolation for devices that cannot participate in identity-based controls.
Ver respuesta modelo
Utilise MAC Authentication Bypass (MAB) on the NAC solution, combined with deep device profiling using DHCP fingerprints, HTTP user agents, and traffic behaviour analysis to accurately identify and classify each medical device type. Once identified, the NAC dynamically assigns these devices to highly restricted, isolated VLANs that only permit communication with specific, required medical servers and systems — blocking all other traffic by default. ZTNA is not applicable to these devices; security relies entirely on strict network segmentation and continuous traffic monitoring for anomalous behaviour. Ensure the medical device VLANs are completely isolated from the cardholder data environment to maintain PCI DSS compliance.
Q3. During a production deployment, the API integration between your NAC and ZTNA solutions fails silently — no alerts are triggered. A user's laptop on the corporate network subsequently becomes infected with malware. Describe the expected security outcome and identify the architectural gap that allowed it.
Sugerencia: Analyse the impact of broken context synchronisation on each policy engine independently, and consider what monitoring should have been in place.
Ver respuesta modelo
The NAC solution will detect the degraded posture via EDR integration and quarantine the device on the local network, preventing lateral movement within the corporate environment. However, because the API integration has failed silently, the ZTNA broker has not received the updated posture context. If the user attempts to access a cloud application, the ZTNA client may still establish a connection if the initial identity authentication token remains valid and has not expired. The architectural gap is twofold: first, the absence of health monitoring on the API integration itself; second, the lack of a fail-safe policy that triggers automatic access restrictions if context synchronisation is lost beyond a defined threshold. The remediation is to implement dedicated monitoring with alerting on integration health, configure the ZTNA broker to require periodic posture re-validation (not just initial authentication), and define a default-deny policy that activates if the NAC context feed is unavailable for more than a specified interval.