¿Cómo la aleatorización de direcciones MAC afecta a los análisis de WiFi para invitados?
Esta guía ofrece un análisis técnico en profundidad sobre cómo la aleatorización de direcciones MAC impacta en los análisis de WiFi para invitados. Proporciona estrategias prácticas para que los líderes de TI y los arquitectos de red restauren la visibilidad, garanticen métricas precisas y mantengan el cumplimiento en implementaciones a gran escala. Cubriendo la mecánica de la aleatorización por red y efímera, la arquitectura de resolución de identidad y los escenarios de implementación en el mundo real, esta es la referencia definitiva para cualquier organización que dependa de datos espaciales derivados de WiFi.
Escuchar esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado
- La Mecánica de la Aleatorización de MAC
- El Impacto en los Análisis de WiFi
- Guía de Implementación
- Restaurando la Visibilidad: La Arquitectura Centrada en la Identidad
- Mejores Prácticas
- Resolución de Problemas y Mitigación de Riesgos
- Modos de Fallo Comunes
- Estrategias de Mitigación
- ROI e Impacto Empresarial
Resumen Ejecutivo
Para los gerentes de TI, arquitectos de red y directores de operaciones de recintos, la adopción generalizada de la aleatorización de direcciones MAC en iOS, Android y Windows ha alterado fundamentalmente los análisis tradicionales de WiFi para invitados. Lo que antes era un identificador de hardware fiable y persistente se ha convertido en un punto de datos efímero, dejando obsoletos los modelos de análisis heredados. Esta guía de referencia técnica explora la mecánica de la aleatorización de MAC, su impacto directo en métricas como el recuento de visitantes únicos, el tiempo de permanencia y las tasas de visitas recurrentes, y los cambios arquitectónicos necesarios para restaurar la integridad de los datos. Al pasar del seguimiento centrado en el hardware a modelos de resolución basados en la identidad, las organizaciones en Retail , Hospitality , Healthcare y Transport pueden mantener análisis precisos respetando la privacidad del usuario y los marcos regulatorios como GDPR y PCI DSS.
Análisis Técnico Detallado
La Mecánica de la Aleatorización de MAC
Históricamente, la dirección Media Access Control (MAC) sirvió como un identificador globalmente único y persistente asignado a un controlador de interfaz de red (NIC). En un entorno previo a la aleatorización, un dispositivo que transmitía solicitudes de sondeo para descubrir redes disponibles enviaría su dirección MAC permanente, grabada en el hardware. Esto permitía a la infraestructura de red rastrear la presencia, el movimiento y las visitas recurrentes de un dispositivo, incluso si el usuario nunca se autenticaba en la red.
A partir de iOS 14 y Android 10, los sistemas operativos móviles introdujeron la aleatorización de direcciones MAC por defecto. En lugar de transmitir la MAC del hardware, el dispositivo genera una dirección MAC aleatorizada y administrada localmente. La implementación varía ligeramente entre proveedores, pero generalmente sigue dos modelos principales:
- Aleatorización por red: El dispositivo genera una dirección MAC única para cada Service Set Identifier (SSID) distinto al que se conecta. Esta MAC permanece consistente para ese SSID específico, permitiendo que el dispositivo se reconecte sin problemas.
- Aleatorización diaria o efímera: Algunas implementaciones rotan la dirección MAC aleatorizada periódicamente (por ejemplo, cada 24 horas) o en cada intento de conexión, ocultando aún más la identidad del dispositivo con el tiempo.
El Impacto en los Análisis de WiFi
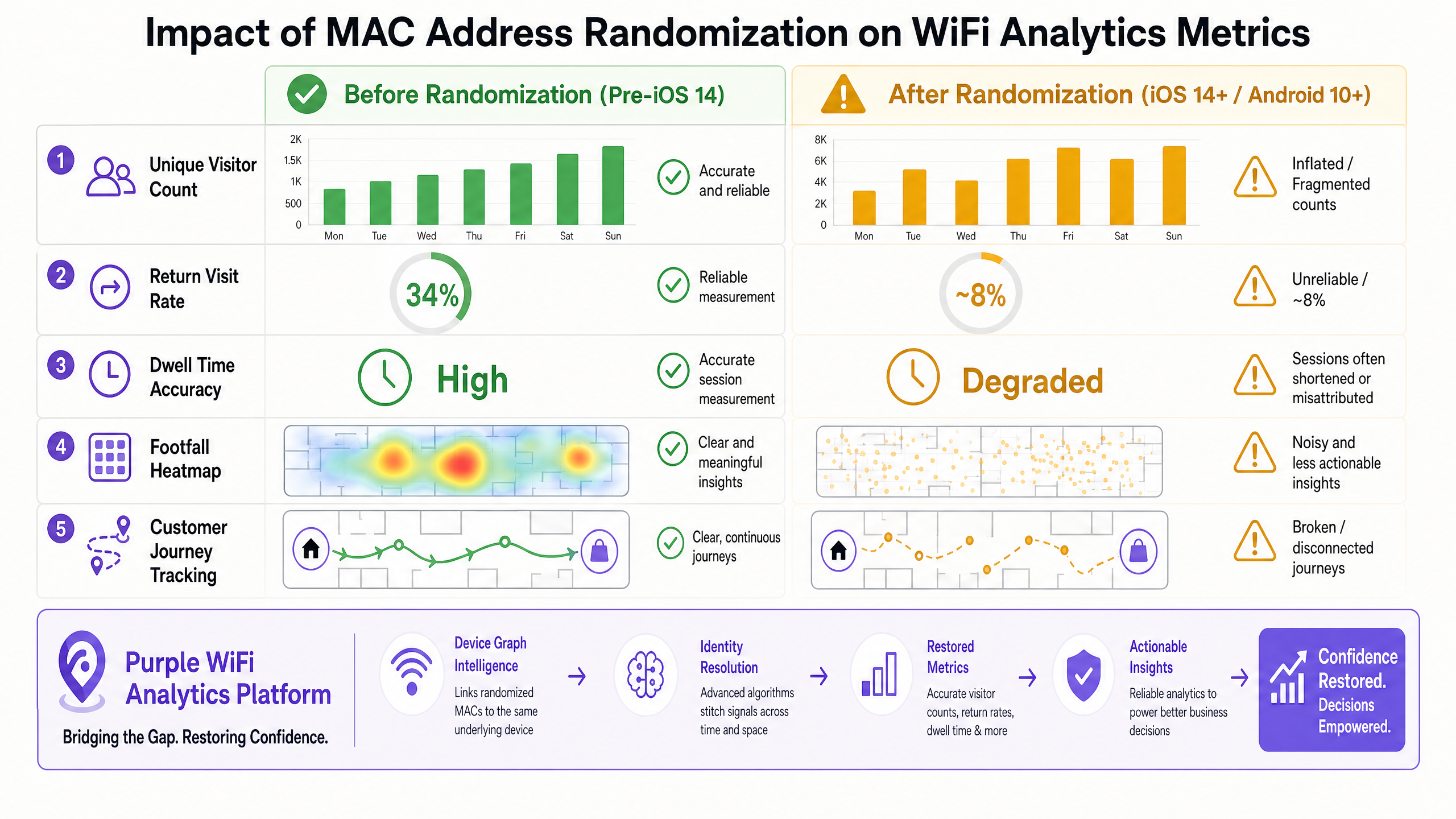
Cuando las plataformas de análisis heredadas encuentran direcciones MAC aleatorizadas, la integridad de los datos se degrada rápidamente. La dependencia de un identificador persistente conduce a distorsiones significativas en métricas clave:
- Recuento de visitantes únicos: Debido a que un solo dispositivo físico puede presentar múltiples direcciones MAC a lo largo del tiempo (o a través de diferentes SSIDs dentro de un recinto), los sistemas heredados lo contarán como múltiples visitantes únicos. Esto lleva a métricas de afluencia infladas artificialmente.
- Tasas de visitas recurrentes: Si un dispositivo rota su dirección MAC entre visitas, la plataforma de análisis no puede vincular la sesión actual a una sesión histórica. El usuario es tratado como un nuevo visitante, lo que provoca que las tasas de visitas recurrentes se desplomen.
- Precisión del tiempo de permanencia: En entornos donde un dispositivo podría rotar su MAC durante una sesión prolongada, una sola visita se fragmenta en múltiples sesiones cortas, sesgando los promedios de tiempo de permanencia a la baja.
- Seguimiento del recorrido del cliente: El seguimiento del movimiento de un usuario a través de un recinto grande (por ejemplo, un estadio o un complejo comercial con múltiples SSIDs) se vuelve inconexo. La ruta se interrumpe cada vez que cambia la dirección MAC.
Guía de Implementación
Restaurando la Visibilidad: La Arquitectura Centrada en la Identidad
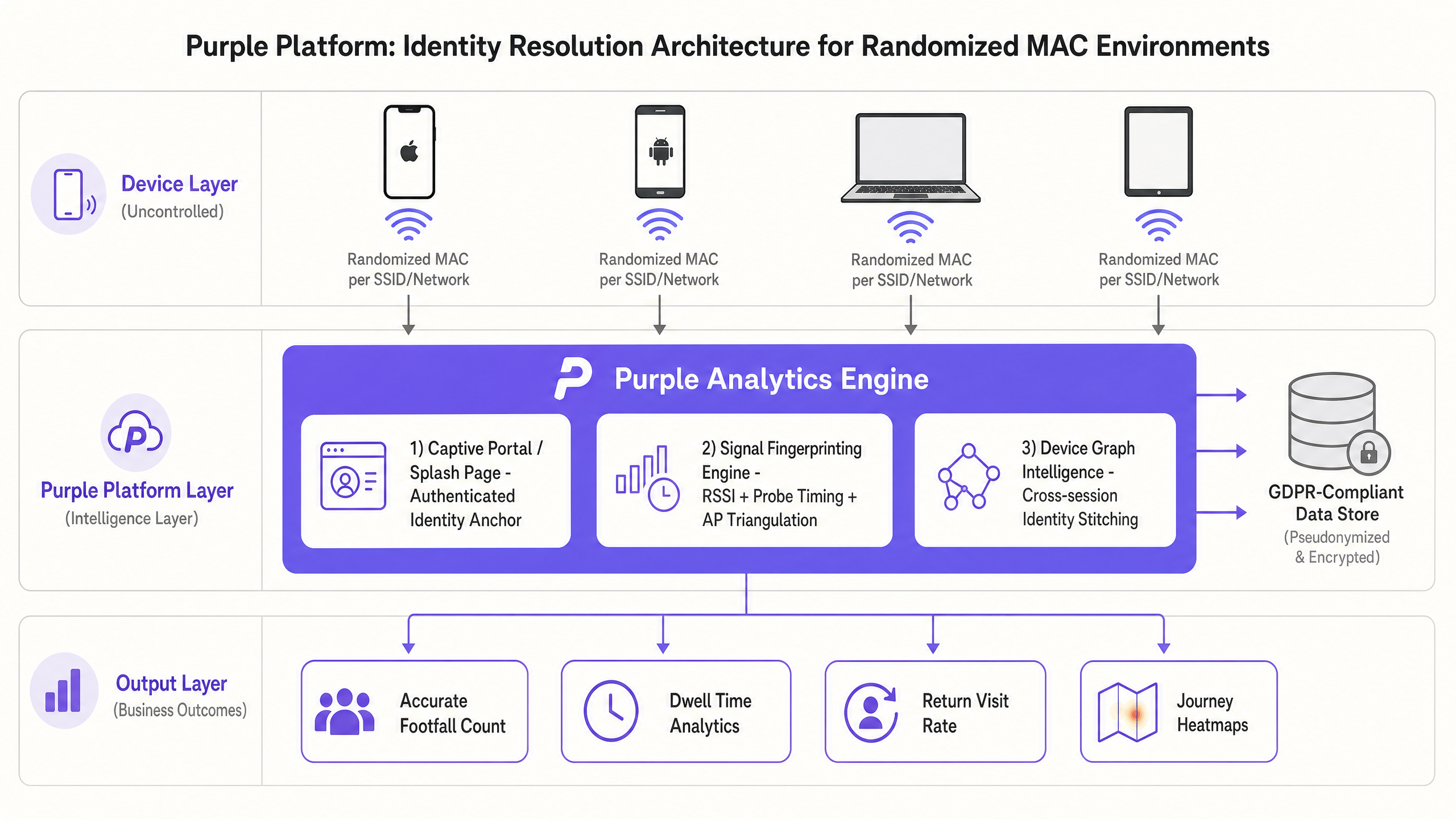
Para superar las limitaciones impuestas por la aleatorización de MAC, los equipos de TI deben pasar del seguimiento basado en hardware a una arquitectura centrada en la identidad. Esto implica desplegar una capa inteligente que resuelva múltiples identificadores efímeros en un único perfil de usuario persistente. La plataforma Guest WiFi debe evolucionar hacia un motor integral de resolución de identidad.
Paso 1: Establecer el Anclaje de Identidad Autenticada
El método más fiable para establecer la identidad es a través de un portal cautivo o una página de bienvenida. Cuando un usuario se autentica en la red (a través de correo electrónico, inicio de sesión social o SMS), el sistema crea un registro de anclaje. Este registro vincula la dirección MAC actual (aleatorizada) a una identidad conocida y persistente (por ejemplo, una dirección de correo electrónico o un ID de usuario único).
Este enfoque requiere una plataforma robusta de WiFi Analytics capaz de mantener un gráfico de dispositivos dinámico. Cuando el usuario regresa y se autentica de nuevo (incluso con una nueva MAC aleatorizada), el sistema actualiza el gráfico de dispositivos, vinculando la nueva MAC al perfil de usuario existente.
Paso 2: Implementar la Huella Digital de Señal (Donde sea Permisible)
En escenarios donde la autenticación no es requerida o aún no ha ocurrido, las plataformas avanzadas utilizan la huella digital de señal. Esto implica analizar características secundarias de las transmisiones de radio del dispositivo, como:
- Patrones de Indicador de Fuerza de Señal Recibida (RSSI): Analizar cómo cambia la fuerza de la señal a medida que el dispositivo se mueve por el recinto.
- Tiempo y Frecuencia de Solicitudes de Sondeo: Los dispositivos exhiben patrones distintos en la frecuencia y el momento en que envían solicitudes de sondeo.
- Triangulación de Puntos de Acceso: Utilizar múltiples APs para determinar la ubicación del dispositivo y rastrear su movimiento.
Al combinar estas señales, el motor de análisis puede crear un modelo probabilístico para unir sesiones fragmentadas, aunque este método es menos determinista que la autenticación explícita.
Paso 3: Integrar con Datos del Ecosistema
Para enriquecer aún más el gráfico de identidad, la plataforma WiFi debería integrarse con otras enterprisy sistemas. Por ejemplo, vincular los datos de autenticación WiFi con las bases de datos de programas de fidelización o los sistemas de punto de venta (POS) proporciona una visión holística del recorrido del cliente. El papel de Purple como proveedor de identidad para servicios como OpenRoaming bajo la licencia Connect facilita esta integración sin fisuras en diversos entornos.
Mejores Prácticas
- Priorizar la Autenticación Explícita: Diseñe captive portals que ofrezcan intercambios de valor claros (por ejemplo, acceso gratuito de alta velocidad, descuentos exclusivos) para animar a los usuarios a autenticarse. Esto establece el anclaje de identidad más sólido posible.
- Optimizar la Experiencia del Captive Portal: Asegúrese de que el proceso de autenticación sea fluido. La implementación de tecnologías que permiten un acceso sin fricciones, similar a los conceptos discutidos en How a wi fi assistant Enables Passwordless Access in 2026 , reduce las tasas de abandono y aumenta el porcentaje de usuarios conocidos en la red.
- Aprovechar el Perfilado Progresivo: En lugar de solicitar toda la información del usuario de antemano, recopile datos de forma incremental a lo largo de múltiples visitas. Esto reduce la fricción durante la conexión inicial mientras se construye un perfil completo con el tiempo.
- Garantizar el Cumplimiento Normativo: El cambio hacia el seguimiento centrado en la identidad requiere una estricta adhesión a las regulaciones de privacidad como GDPR y CCPA. Asegúrese de que su plataforma anonimiza o seudonimiza los datos de forma adecuada y proporciona mecanismos claros de opt-in/opt-out para los usuarios.
- Revisar la Configuración de la Red: Asegúrese de que su infraestructura inalámbrica esté configurada para manejar la carga creciente de solicitudes de autenticación y la gestión dinámica de direcciones MAC. Al planificar las asignaciones de canales, tenga en cuenta DFS Channels: What They Are and When to Avoid Them (o para implementaciones italianas, [Canali DFS: Cosa sono e quando evitarli](/guides/canali-dfs-cosa-sono-e-quando evitarli)) para mantener la estabilidad de la red y optimizar el rendimiento para la recopilación de datos de análisis.
Resolución de Problemas y Mitigación de Riesgos
Modos de Fallo Comunes
- Excesiva Dependencia de Datos No Autenticados: Seguir basando las decisiones empresariales en datos de sondeo brutos y no autenticados en un entorno MAC aleatorizado conducirá a conclusiones erróneas y a una asignación incorrecta de recursos.
- Silos de Identidad Fragmentados: Si la plataforma de análisis WiFi no se integra con otros sistemas empresariales (por ejemplo, CRM, aplicaciones de fidelización), la organización mantendrá vistas fragmentadas del cliente, reduciendo la eficacia de las estrategias de engagement personalizadas.
- Mal Diseño del Captive Portal: Un proceso de autenticación engorroso disuadirá a los usuarios de conectarse, lo que resultará en una baja tasa de conexión y un tamaño de muestra pequeño de usuarios autenticados, lo que disminuye el valor de los datos de análisis.
Estrategias de Mitigación
- Implementar un Grafo de Dispositivos: Implemente una plataforma que utilice algoritmos avanzados para unir sesiones fragmentadas y resolver identidades a través de múltiples direcciones MAC.
- Monitorizar las Tasas de Conexión: Realice un seguimiento exhaustivo del porcentaje de visitantes que se autentican en la red frente al número total de dispositivos detectados. Una baja tasa de conexión indica la necesidad de optimizar la experiencia del captive portal o la propuesta de valor ofrecida al usuario.
- Auditar Regularmente la Integridad de los Datos: Compare periódicamente los datos de análisis WiFi con otras fuentes de datos (por ejemplo, contadores de afluencia, datos de POS) para identificar discrepancias y garantizar la precisión del motor de resolución de identidad.
ROI e Impacto Empresarial
La transición a un modelo de análisis WiFi centrado en la identidad requiere inversión, pero el retorno de la inversión (ROI) es significativo para las organizaciones que dependen de datos espaciales precisos.
- Asignación Precisa de Recursos: Las métricas fiables de afluencia y tiempo de permanencia permiten una dotación de personal y una asignación de recursos precisas, optimizando la eficiencia operativa en entornos como tiendas minoristas y centros de transporte.
- Engagement del Cliente Mejorado: Al comprender el verdadero recorrido del cliente y las tasas de visitas recurrentes, los equipos de marketing pueden ofrecer campañas dirigidas y personalizadas que impulsen la lealtad y aumenten los ingresos.
- Toma de Decisiones Estratégicas: Los datos de alta fidelidad respaldan iniciativas estratégicas, como la optimización de la distribución de las tiendas, la evaluación de la eficacia de las campañas de marketing y la toma de decisiones inmobiliarias. Las iniciativas destinadas a impulsar la inclusión digital, como se destaca en Purple Appoints Iain Fox as VP Growth - Public Sector to Drive Digital Inclusion and Smart City Innovation , dependen en gran medida de datos de uso precisos para medir el impacto.
- Nuevas Fuentes de Ingresos: En entornos como estadios y centros de conferencias, los datos de ubicación precisos permiten servicios basados en la ubicación, como publicidad dirigida y marketing de proximidad, creando nuevas oportunidades de monetización. Funcionalidades como Purple Launches Offline Maps Mode for Seamless, Secure Navigation to WiFi Hotspots mejoran aún más la propuesta de valor para el usuario, impulsando un mayor engagement y la recopilación de datos.
Definiciones clave
Locally Administered MAC Address
A MAC address generated by the device's software rather than assigned by the hardware manufacturer. It is indicated by setting the second least significant bit of the first octet to 1 (e.g., x2:xx:xx:xx:xx:xx).
IT teams use this bit flag in raw packet captures or RADIUS logs to identify which devices on the network are using randomized addresses versus persistent hardware addresses. A high proportion of locally administered MACs in your logs is a diagnostic signal that randomization is active.
Device Graph
A dynamic database that maps multiple identifiers (e.g., various randomized MAC addresses, email addresses, loyalty IDs) to a single, persistent user profile.
This is the core technology required to restore analytics accuracy in a post-randomization environment, allowing platforms to stitch together fragmented sessions across multiple visits and MAC address rotations.
Probe Request
A management frame sent by a client device to actively discover available wireless networks in its vicinity. It contains the device's MAC address (which may be randomized).
Historically used for passive tracking of unauthenticated users. Now highly unreliable for long-term analytics due to randomization. Probe request data should be treated as a rough footfall indicator only, not a source of identity.
Identity Resolution
The process of analyzing various data points and signals to determine that multiple distinct identifiers actually belong to the same physical user or device.
The critical function performed by advanced analytics platforms to counteract the obfuscation caused by MAC randomization. It transforms fragmented, ephemeral data points into coherent, actionable user profiles.
Attach Rate
The percentage of total detected devices in a venue that successfully complete the authentication process and connect to the network.
A key operational metric for evaluating the effectiveness of a captive portal. A low attach rate means the analytics platform has a smaller sample size of reliable, authenticated data, directly impacting the statistical confidence of all downstream analytics.
Captive Portal
A web page that users are forced to view and interact with before access is granted to a public WiFi network, typically requiring a form of authentication or consent.
The primary mechanism for establishing an Identity Anchor by requiring users to provide credentials in exchange for network access. The design and value proposition of the captive portal directly determines the attach rate.
Signal Fingerprinting
A technique that uses secondary characteristics of a device's radio transmissions (like RSSI patterns, probe timing, and channel behavior) to probabilistically identify it, rather than relying solely on the MAC address.
Used as a supplementary tracking method when explicit authentication is not available. It is less reliable in high-density RF environments and should be treated as a probabilistic supplement to, not a replacement for, authenticated identity resolution.
Ephemeral Randomization
A more aggressive form of MAC randomization where the device rotates its MAC address periodically (e.g., daily) even when connected to the same SSID, rather than maintaining a consistent per-network MAC.
This completely breaks analytics platforms that rely on per-network MAC consistency. It forces the adoption of identity-centric architectures and is becoming more common as OS vendors increase privacy protections.
Ejemplos prácticos
A large retail chain with 500 locations is experiencing a sudden, inexplicable 40% spike in reported unique visitors across all stores, while POS transaction volume remains flat. The IT Director suspects an issue with the WiFi analytics platform.
- Diagnosis: The IT team analyzes the raw MAC address logs and identifies a high volume of locally administered MAC addresses (indicated by the second least significant bit of the first octet being set to 1). This confirms the spike is due to mobile OS updates enabling MAC randomization, not an actual increase in foot traffic.
- Architecture Shift: The chain migrates from their legacy, hardware-centric analytics tool to Purple's identity-centric platform.
- Captive Portal Optimization: They redesign the splash page to offer a 10% discount code in exchange for email authentication.
- Identity Resolution: Purple's device graph engine begins linking the randomized MAC addresses to the authenticated email profiles.
- Result: Within 30 days, the unique visitor count normalizes, accurately reflecting true footfall. Return visit rates, which had dropped to near zero, are restored as the platform successfully identifies returning customers despite their changing MAC addresses.
A multi-building corporate campus needs to track employee and guest movement for space utilization analysis. However, devices are rotating MAC addresses as they roam between different SSIDs (e.g., Corp-WiFi and Guest-WiFi).
- Network Consolidation (Where Possible): The network architect reviews the SSID strategy and consolidates redundant networks to minimize the need for devices to switch SSIDs, reducing the frequency of MAC rotation.
- Unified Authentication: The campus implements a unified authentication framework (e.g., 802.1X for employees, a streamlined captive portal for guests) integrated with a central RADIUS server and the Purple analytics platform.
- Cross-SSID Stitching: The Purple platform is configured to ingest authentication logs from the RADIUS server. When a device authenticates to Corp-WiFi using an employee's credentials, and later authenticates to Guest-WiFi, the platform uses the shared identity credential to stitch the sessions together.
- Result: The facilities management team regains accurate visibility into space utilization across the entire campus, enabling data-driven decisions regarding real estate optimization.
Preguntas de práctica
Q1. Your marketing team reports that a new promotional campaign launched last week drove a 300% increase in unique footfall to your flagship store. However, the store manager reports that the venue felt unusually quiet, and sales data shows a 5% decline. What is the most likely technical explanation for this discrepancy, and what is your immediate diagnostic step?
Sugerencia: Consider what metric legacy analytics platforms use to count unique visitors and how modern mobile operating systems handle that identifier.
Ver respuesta modelo
The most likely explanation is that the legacy WiFi analytics platform is counting randomized MAC addresses as unique physical visitors. A recent OS update or a change in how devices behave in that specific RF environment has caused devices to rotate their MAC addresses more frequently. The platform sees multiple MACs from the same physical device and counts each as a separate unique person, leading to an artificially inflated footfall metric that does not correlate with actual physical presence or sales data. The immediate diagnostic step is to examine the raw MAC address logs and calculate the proportion of locally administered addresses (second least significant bit of the first octet set to 1). A high proportion confirms randomization is the cause. The solution is to transition to an identity-centric analytics model with a captive portal.
Q2. You are deploying a new guest WiFi network across a large hospital campus. The primary goal is to provide seamless connectivity for patients and visitors while gathering accurate data on dwell times in various waiting areas. You have a choice between an open network with no captive portal or a network requiring email authentication. Which approach do you recommend and why?
Sugerencia: Think about the Identity Anchor principle and how MAC randomization affects long-term tracking without explicit authentication. Also consider GDPR implications of each approach.
Ver respuesta modelo
The network requiring email authentication via a captive portal is strongly recommended. An open network relies entirely on passive probe requests and MAC addresses for tracking. Due to MAC randomization, devices will appear as new visitors every time their MAC changes, completely breaking dwell time analytics and making it impossible to track a patient's journey across different waiting areas over time. By requiring email authentication, you establish a persistent Identity Anchor. The analytics platform can then use a device graph to link the user's email to whatever randomized MAC they are currently using, ensuring accurate dwell time and journey tracking across the campus. From a GDPR perspective, the captive portal also provides a clear consent mechanism, which is legally required when collecting personal data. The open network approach, while seemingly less intrusive, actually creates a more complex compliance situation as it relies on probabilistic tracking without explicit consent.
Q3. A stadium IT director wants to track the movement of VIP guests to optimize staffing in premium lounges. They are currently using a system that relies on signal fingerprinting (RSSI patterns) because they want to avoid forcing VIPs to use a captive portal. The data is proving to be highly inaccurate. What is the architectural flaw in this approach, and what is the recommended solution that maintains a premium user experience?
Sugerencia: Consider the deterministic versus probabilistic nature of different tracking methods in a high-density, complex RF environment like a stadium.
Ver respuesta modelo
The architectural flaw is relying on probabilistic signal fingerprinting as the primary identification method in a complex, high-density RF environment like a stadium. Signal fingerprinting is imprecise; RSSI values fluctuate wildly due to physical obstructions (crowds, concrete, steel), device orientation, and competing RF sources. When combined with MAC randomization, the system cannot reliably stitch together fragmented sessions, producing inaccurate journey data. The director must implement a deterministic Identity Anchor. To maintain a premium, frictionless experience for VIPs, the recommended solution is to integrate the WiFi authentication with the VIP ticketing or access management app using a technology like Passpoint (Hotspot 2.0 / IEEE 802.11u). This allows the device to authenticate automatically and silently based on the VIP's profile credentials, providing accurate, deterministic tracking without requiring a manual captive portal login. This delivers the premium experience the director requires while restoring data integrity.