Implementación de WPA3-Enterprise para una Seguridad Inalámbrica Mejorada
Esta guía de referencia técnica proporciona una hoja de ruta completa y práctica para los líderes de TI que realizan la transición de WPA2 a WPA3-Enterprise. Cubre los cambios arquitectónicos, las mejoras de seguridad obligatorias como EAP-TLS y PMF, y las estrategias de implementación prácticas para proteger las redes corporativas en entornos empresariales complejos.
Escucha esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectura de WPA3-Enterprise
- Autenticación e Intercambio de Claves
- Mejoras Criptográficas
- Marcos de Gestión Protegidos (PMF)
- Guía de Implementación: Despliegue de WPA3-Enterprise
- Fase 1: Auditoría de Infraestructura y Preparación de PKI
- Fase 2: Habilitación del Modo de Transición WPA3
- Fase 3: Segmentación de Red y Aislamiento de Dispositivos Heredados
- Fase 4: Aplicación Completa de WPA3
- Mejores Prácticas para Entornos Empresariales
- Solución de Problemas y Mitigación de Riesgos
- Síntoma: Los clientes no logran conectarse cuando el Modo de Transición está habilitado.
- Síntoma: Fallas generalizadas de autenticación en todos los dispositivos.
- Síntoma: Alta latencia durante el roaming entre puntos de acceso.
- ROI e Impacto Comercial

Resumen Ejecutivo
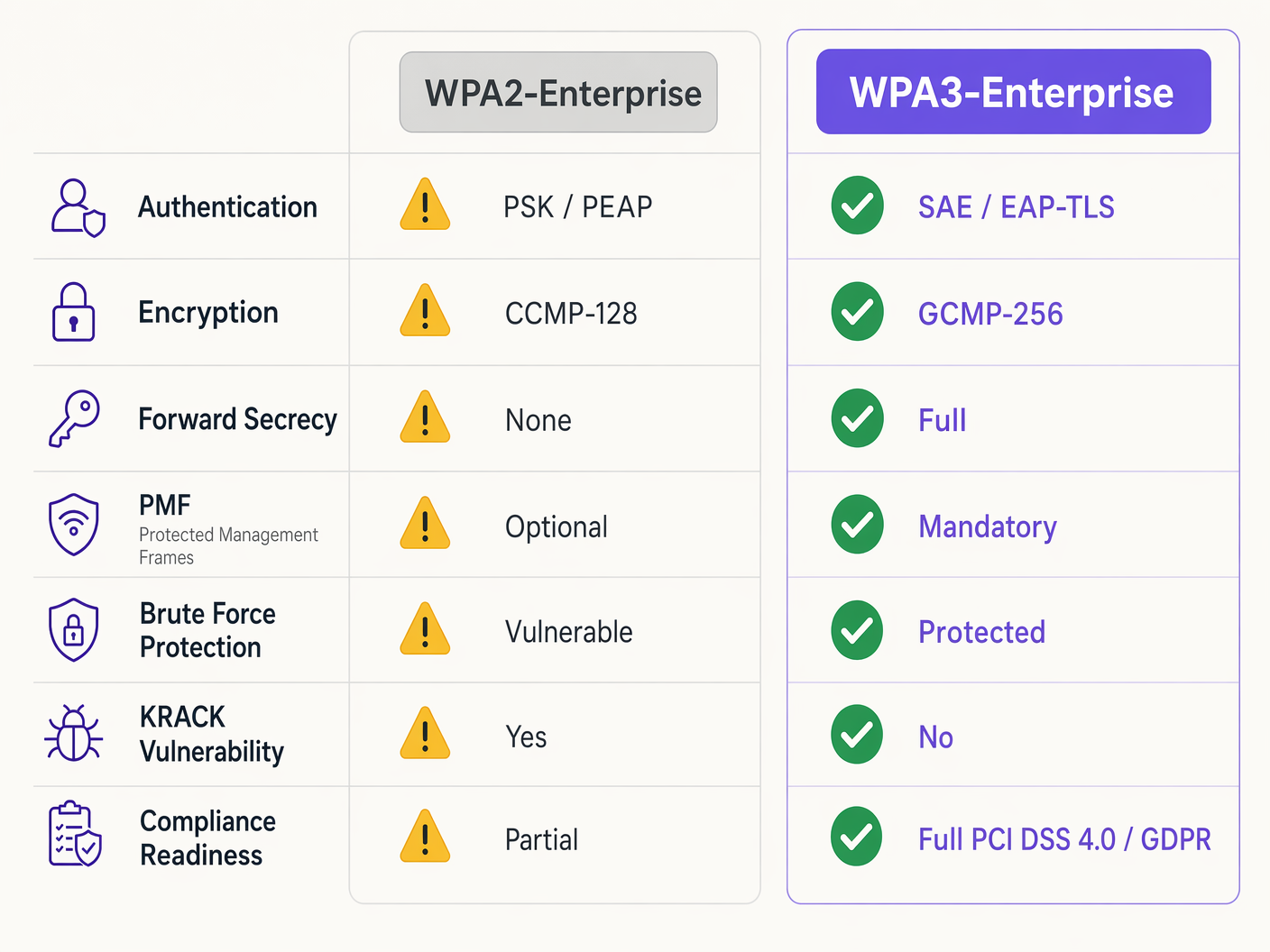
Para los líderes de TI empresariales, la transición a WPA3-Enterprise ya no es un elemento de la hoja de ruta futura; es un requisito operativo actual. Desde 2020, WPA3 ha sido obligatorio para todos los dispositivos Wi-Fi CERTIFIED, sin embargo, muchas redes empresariales —que abarcan hostelería, comercio minorista y lugares del sector público— permanecen ancladas a WPA2. Esta brecha representa una exposición significativa al riesgo, particularmente a medida que los marcos de cumplimiento como PCI DSS 4.0 y GDPR exigen cada vez más controles de seguridad de red robustos y de última generación.
Esta guía proporciona un desglose técnico completo de WPA3-Enterprise, centrándose en sus mejoras arquitectónicas fundamentales sobre WPA2. Detallamos el cambio obligatorio hacia una encriptación más fuerte (GCMP-256), la necesidad de Marcos de Gestión Protegidos (PMF) y la implementación crítica de la autenticación mutua basada en certificados a través de EAP-TLS. Diseñado para arquitectos de red y CTOs, este documento omite la teoría académica en favor de estrategias de implementación prácticas, metodologías de resolución de problemas y estudios de casos reales para garantizar una infraestructura inalámbrica segura, escalable y compatible.
Escuche el podcast de resumen técnico complementario para una visión general ejecutiva:
Análisis Técnico Detallado: Arquitectura de WPA3-Enterprise
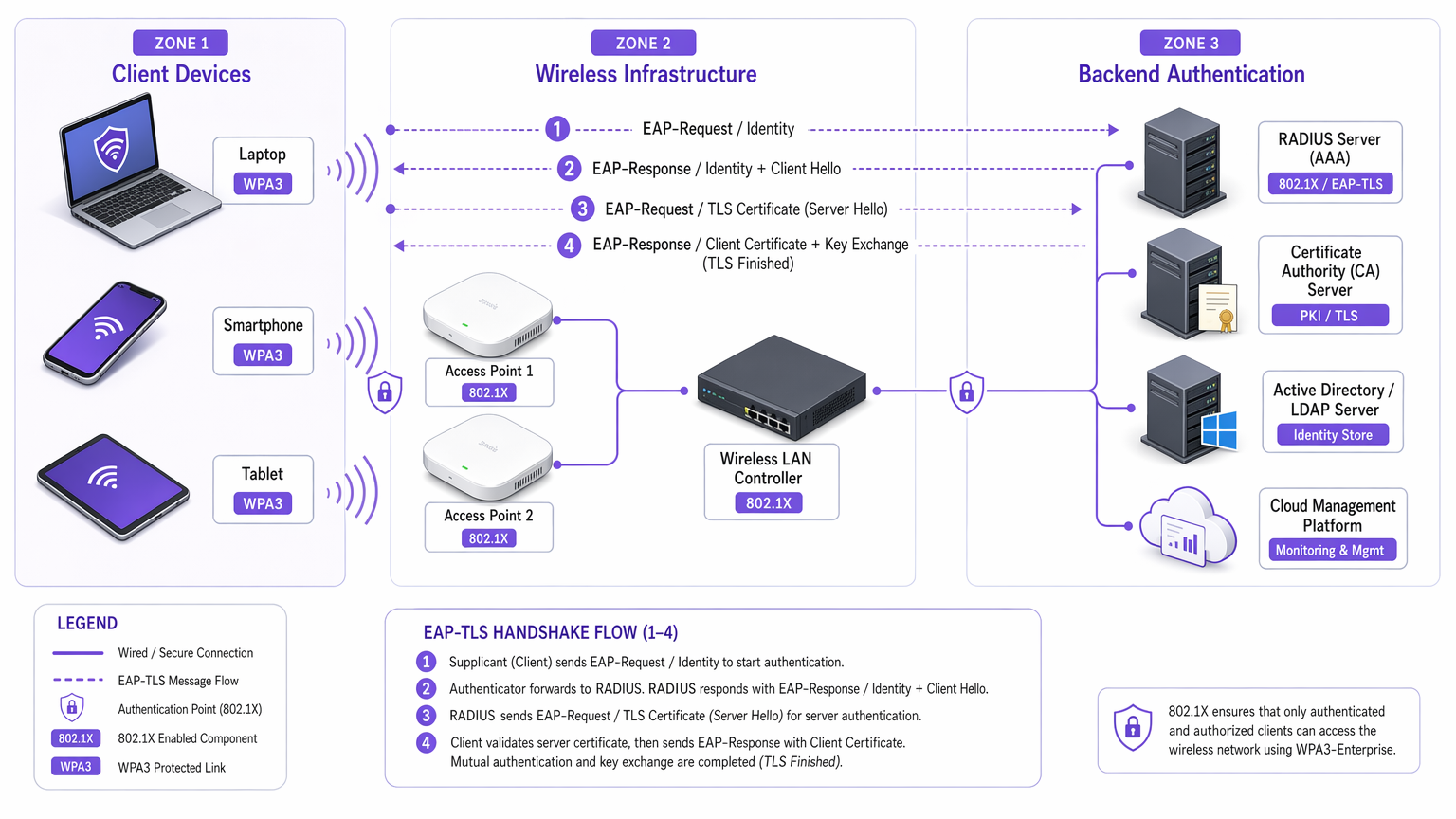
La diferencia fundamental entre WPA2 y WPA3-Enterprise no reside en el marco 802.1X subyacente, que sigue siendo el estándar para el control de acceso a la red basado en puertos, sino en los protocolos criptográficos y las protecciones de marcos de gestión construidos a su alrededor. WPA3 aborda las vulnerabilidades sistémicas de su predecesor, apuntando específicamente a los ataques de diccionario fuera de línea y la manipulación de marcos de gestión.
Autenticación e Intercambio de Claves
WPA2-Enterprise se basa en el handshake de 4 vías para derivar claves de sesión, un proceso que ha demostrado ser vulnerable a los ataques de reinstalación de claves (KRACK) y a la fuerza bruta de diccionario fuera de línea si se utilizan credenciales débiles. WPA3 mitiga esto implementando la Autenticación Simultánea de Iguales (SAE), un protocolo de intercambio de claves basado en Diffie-Hellman. SAE garantiza la confidencialidad directa; incluso si un atacante compromete una clave a largo plazo, no puede descifrar retroactivamente el tráfico capturado, ya que cada sesión utiliza claves efímeras y únicas.
Para entornos empresariales, el mecanismo de autenticación central se desplaza decisivamente hacia EAP-TLS (Extensible Authentication Protocol-Transport Layer Security). Si bien WPA2 permitía métodos más débiles basados en credenciales como PEAP o EAP-TTLS, WPA3-Enterprise fomenta encarecidamente, y en el modo de alta seguridad de 192 bits lo exige, EAP-TLS. Esto requiere autenticación mutua basada en certificados, eliminando por completo las contraseñas y neutralizando los vectores de robo de credenciales.
Mejoras Criptográficas
WPA2 utiliza CCMP-128 (Counter Mode with Cipher Block Chaining Message Authentication Code Protocol) basado en AES-128. WPA3-Enterprise introduce un conjunto de seguridad opcional pero altamente recomendado de 192 bits, alineado con la Commercial National Security Algorithm (CNSA) Suite. Este modo exige GCMP-256 (Galois/Counter Mode Protocol con claves de 256 bits) para una encriptación robusta, junto con criptografía de curva elíptica de 384 bits para el establecimiento y la gestión de claves.
Marcos de Gestión Protegidos (PMF)
Bajo IEEE 802.11w, los Marcos de Gestión Protegidos aseguran las señales de control que gestionan la asociación, disociación y autenticación del cliente. En WPA2, PMF era opcional, dejando las redes vulnerables a marcos de desautenticación falsificados, un precursor común de ataques de denegación de servicio o de intermediario (man-in-the-middle). WPA3 hace que PMF sea obligatorio para todas las conexiones, cerrando fundamentalmente este vector de ataque.
Guía de Implementación: Despliegue de WPA3-Enterprise
La transición de una red empresarial a través de cientos de ubicaciones minoristas o un extenso complejo hotelero requiere un enfoque por fases y metódico. Los siguientes pasos describen una estrategia de despliegue independiente del proveedor.
Fase 1: Auditoría de Infraestructura y Preparación de PKI
El requisito previo para WPA3-Enterprise, específicamente utilizando EAP-TLS, es una Infraestructura de Clave Pública (PKI) robusta.
- Evaluar Capacidades RADIUS: Asegúrese de que sus servidores RADIUS (por ejemplo, Cisco ISE, Aruba ClearPass, FreeRADIUS) admitan los parámetros WPA3 y estén configurados para EAP-TLS.
- Establecer Autoridad de Certificación (CA): Implemente una CA interna (como Microsoft AD CS) o aproveche un servicio PKI basado en la nube.
- Integración MDM: Utilice plataformas de Gestión de Dispositivos Móviles (MDM) (Intune, Jamf) para automatizar el despliegue de certificados de cliente en dispositivos gestionados. Esto es crítico para la escalabilidad.
Para más información sobre el despliegue de certificados, consulte Autenticación de Certificados WiFi: Cómo los Certificados Digitales Protegen las Redes Inalámbricas .
Fase 2: Habilitación del Modo de Transición WPA3
Un cambio drástico rara vez es factible en entornos empresariales diversos. La mayoría de los controladores de LAN inalámbrica empresariales admiten el Modo de Transición WPA3, lo que permite que un solo SSID acepte clientes WPA2 y WPA3 simultáneamente.
- Configurar SSID de Transición: Habilite el Modo de Transición WPA3 en el SSID corporativo.
- Monitorear Asociación de Clientes: Utilice su panel de gestión inalámbricatablero para monitorear las conexiones de los clientes. Asegúrese de que los dispositivos modernos negocien WPA3 con éxito, mientras que los dispositivos heredados recurran a WPA2.
- Abordar Problemas de Compatibilidad: Identifique los dispositivos que no logran asociarse. A menudo, los controladores inalámbricos heredados tienen dificultades con el requisito PMF obligatorio de WPA3, incluso en modo de transición. Actualice los controladores siempre que sea posible.
Fase 3: Segmentación de Red y Aislamiento de Dispositivos Heredados
No todos los dispositivos serán compatibles con WPA3. Los dispositivos IoT heredados, los sistemas de punto de venta más antiguos o el equipo médico especializado en entornos de Healthcare a menudo carecen de las actualizaciones de hardware o firmware necesarias.
- Aislar Dispositivos Heredados: Cree una VLAN dedicada y aislada y un SSID WPA2-only separado específicamente para estos dispositivos.
- Implementar Controles de Acceso Estrictos: Aplique reglas de firewall estrictas a esta VLAN heredada, evitando el movimiento lateral hacia la red corporativa segura WPA3.
Fase 4: Aplicación Completa de WPA3
Una vez que la gran mayoría de la flota corporativa esté utilizando WPA3 con éxito y los dispositivos heredados estén segmentados, haga la transición del SSID corporativo principal a WPA3-Enterprise solamente.
Mejores Prácticas para Entornos Empresariales
Implementar la tecnología es solo la mitad de la batalla; mantener su integridad requiere una disciplina operativa continua.
- Automatizar la Gestión del Ciclo de Vida de los Certificados: La causa más común de falla de EAP-TLS son los certificados caducados. Implemente procesos de renovación automatizados y mecanismos de alerta 90, 60 y 30 días antes del vencimiento del certificado del servidor RADIUS.
- Garantizar la Redundancia de RADIUS: Un solo servidor RADIUS es un único punto de falla. Implemente servidores RADIUS primarios y secundarios en ubicaciones geográficamente diversas, configurando una conmutación por error sin interrupciones en los controladores inalámbricos.
- Separar Redes de Invitados y Corporativas: Nunca confunda las políticas de seguridad corporativas con el acceso de invitados. Las redes corporativas requieren WPA3-Enterprise con EAP-TLS. Las redes de invitados deben utilizar VLANs aisladas, típicamente gestionadas a través de captive portals. Las soluciones de Guest WiFi de Purple proporcionan acceso seguro y conforme para invitados, mientras capturan valiosos WiFi Analytics .
- Aprovechar OpenRoaming: Para una conectividad segura y sin interrupciones en diferentes ubicaciones, considere implementar Passpoint/Hotspot 2.0. Purple actúa como un proveedor de identidad gratuito para servicios como OpenRoaming bajo la licencia Connect, facilitando un acceso seguro y sin fricciones sin comprometer los estándares de seguridad empresarial.
Solución de Problemas y Mitigación de Riesgos
Incluso con una planificación meticulosa, las implementaciones encuentran fricción. Aquí se presentan los modos de falla comunes y las estrategias de mitigación.
Síntoma: Los clientes no logran conectarse cuando el Modo de Transición está habilitado.
Causa Raíz: Los controladores de cliente heredados a menudo fallan cuando encuentran la transmisión PMF (Protected Management Frames) obligatoria por parte del punto de acceso en Modo de Transición, incluso si están intentando una conexión WPA2. Mitigación: Actualice los controladores de la interfaz de red inalámbrica (NIC) del cliente. Si no hay actualizaciones disponibles, el dispositivo debe moverse al SSID WPA2-only heredado y aislado.
Síntoma: Fallas generalizadas de autenticación en todos los dispositivos.
Causa Raíz: El certificado del servidor RADIUS ha caducado, o el certificado de la CA raíz ha sido revocado o eliminado de los almacenes de confianza del cliente. Mitigación: Renueve y despliegue inmediatamente el certificado del servidor RADIUS. Revise las alertas de gestión automatizada del ciclo de vida para evitar recurrencias.
Síntoma: Alta latencia durante el roaming entre puntos de acceso.
Causa Raíz: 802.11r (Fast BSS Transition) está mal configurado o es incompatible con el método EAP específico en uso. Mitigación: Asegúrese de que 802.11r esté explícitamente habilitado y sea compatible tanto con el controlador WLAN como con los dispositivos cliente para el SSID WPA3. Pruebe el rendimiento del roaming durante las ventanas de mantenimiento.
ROI e Impacto Comercial
La transición a WPA3-Enterprise requiere inversión en servicios profesionales, posibles actualizaciones de hardware e infraestructura PKI. Sin embargo, el retorno de la inversión se mide en la mitigación de riesgos y el cumplimiento normativo.
Para una gran cadena de Retail , el costo de una violación de datos que involucre información de tarjetas de pago supera con creces los costos de implementación de WPA3. El cumplimiento de PCI DSS 4.0 requiere una encriptación y autenticación robustas; WPA3-Enterprise satisface directamente estos requisitos, agilizando las auditorías de cumplimiento y evitando posibles multas.
Además, la modernización de la infraestructura inalámbrica proporciona una base estable y de alto rendimiento para futuras iniciativas digitales, ya sea implementando sensores IoT avanzados en Hospitality o habilitando sistemas seguros de punto de venta móviles. El impacto comercial es una arquitectura de red resiliente, compatible y preparada para el futuro.
Definiciones clave
WPA3-Enterprise
The current standard for enterprise wireless security, mandating stronger encryption, protected management frames, and forward secrecy, typically deployed with 802.1X and RADIUS.
Required for compliance (PCI DSS, GDPR) and securing corporate data against modern cryptographic attacks.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security)
An authentication framework requiring both the client and the RADIUS server to present digital certificates to verify each other's identity.
The gold standard for WPA3-Enterprise authentication, eliminating the reliance on vulnerable user passwords.
PMF (Protected Management Frames)
A security standard (802.11w) that encrypts the control frames used for client association and disassociation.
Mandatory in WPA3, PMF prevents attackers from forging deauthentication packets to knock users off the network or execute man-in-the-middle attacks.
SAE (Simultaneous Authentication of Equals)
A secure key establishment protocol used in WPA3 that replaces the vulnerable 4-way handshake of WPA2.
SAE provides forward secrecy and protects against offline dictionary attacks, ensuring that even if a password is weak, the handshake cannot be brute-forced.
GCMP-256 (Galois/Counter Mode Protocol)
A highly secure, efficient encryption protocol utilizing 256-bit keys.
Mandated for the WPA3-Enterprise 192-bit security suite, required for environments handling highly sensitive data like government or financial records.
RADIUS (Remote Authentication Dial-In User Service)
A centralized networking protocol that provides Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service.
The core backend server in a WPA3-Enterprise deployment that validates client certificates or credentials before granting network access.
Forward Secrecy
A cryptographic feature ensuring that session keys are ephemeral; compromising a long-term key in the future will not allow an attacker to decrypt past recorded sessions.
A critical enhancement in WPA3 provided by the SAE handshake, protecting historical data.
PKI (Public Key Infrastructure)
The framework of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates.
The necessary prerequisite infrastructure for deploying EAP-TLS authentication in a WPA3-Enterprise environment.
Ejemplos resueltos
A 200-room luxury hotel is upgrading its corporate network to WPA3-Enterprise. They have a mix of modern corporate laptops, iPads used by concierge staff, and legacy Wi-Fi-enabled door locks that only support WPA2. How should the network architect design the SSIDs and VLANs to ensure maximum security without breaking operational functionality?
The architect must employ network segmentation.
- Create a primary corporate SSID ('HotelCorp_Secure') configured for WPA3-Enterprise only, utilizing EAP-TLS. Deploy certificates to all corporate laptops and iPads via the hotel's MDM solution. Assign this SSID to the primary corporate VLAN.
- Create a secondary, hidden SSID ('Hotel_IoT_Legacy') configured for WPA2-Personal (PSK) or WPA2-Enterprise (if supported by the locks), utilizing a complex, rotated passphrase or MAC authentication bypass (MAB).
- Assign the legacy SSID to a heavily restricted, isolated VLAN. Configure firewall rules to allow the door locks to communicate ONLY with the specific on-premise or cloud-based door management server, blocking all lateral movement to the corporate VLAN or the internet.
A public sector organization has deployed WPA3-Enterprise with EAP-TLS. On a Monday morning, no staff can connect to the wireless network. The wireless controller shows clients associating, but failing RADIUS authentication. What is the most likely cause, and what is the immediate remediation step?
The most likely cause is an expired RADIUS server certificate. Because EAP-TLS relies on mutual authentication, if the server presents an expired certificate, the clients will immediately reject the connection and terminate the handshake.
Immediate remediation: The IT team must generate a new Certificate Signing Request (CSR) from the RADIUS server, have it signed by the internal CA, and bind the new certificate to the EAP-TLS authentication policy on the RADIUS server. Services must then be restarted.
Preguntas de práctica
Q1. You are the network architect for a large retail chain rolling out WPA3-Enterprise. During the pilot phase at three stores using WPA3 Transition Mode, several older barcode scanners frequently drop off the network and require manual reboots to reconnect. Modern tablets connect without issue. What is the most appropriate architectural response?
Sugerencia: Consider how legacy wireless drivers handle unfamiliar management frames broadcast in Transition Mode.
Ver respuesta modelo
The barcode scanners are likely crashing due to the mandatory Protected Management Frames (PMF) broadcast by the APs in Transition Mode. The appropriate response is to abandon Transition Mode for these devices. Create a dedicated, hidden WPA2-only SSID mapped to an isolated VLAN specifically for the scanners, and configure the primary corporate SSID to WPA3-Enterprise only for the modern tablets.
Q2. A CTO mandates the deployment of WPA3-Enterprise across all corporate offices within 60 days to meet new compliance requirements. The current environment uses WPA2-Enterprise with PEAP-MSCHAPv2 (username/password). The organization does not currently have an internal Certificate Authority (CA) or a Mobile Device Management (MDM) solution. Is this timeline realistic, and what is the critical path?
Sugerencia: Evaluate the prerequisites for the recommended WPA3 authentication method (EAP-TLS).
Ver respuesta modelo
The 60-day timeline is highly unrealistic. To properly implement WPA3-Enterprise, the organization should migrate to EAP-TLS to eliminate credential vulnerabilities. The critical path requires designing and deploying a PKI (Certificate Authority) and implementing an MDM solution to distribute client certificates. Building this infrastructure from scratch, testing it, and enrolling all corporate devices will almost certainly exceed 60 days. The architect must communicate this dependency to the CTO.
Q3. During a security audit, an examiner notes that your RADIUS servers are configured for EAP-TLS, but the 'Certificate Revocation List (CRL) checking' feature is disabled on the wireless controllers and RADIUS servers. Why is this a significant security finding in a WPA3 environment?
Sugerencia: What happens if a corporate laptop is stolen, but its certificate has not yet expired?
Ver respuesta modelo
Without CRL or OCSP checking enabled, the RADIUS server has no way of knowing if a presented certificate has been revoked by the CA prior to its natural expiration date. If a device is lost or an employee is terminated, their certificate must be revoked. If revocation checking is disabled, that compromised certificate can still be used to successfully authenticate and access the WPA3-Enterprise network, entirely defeating the purpose of mutual authentication.
Continúe leyendo esta serie
Guía paso a paso: Configuración de controladores inalámbricos Ruijie para Captive Portals de WiFi de invitados
Esta guía proporciona un recorrido técnico completo para configurar controladores inalámbricos y gateways Ruijie para implementar Captive Portals de WiFi de invitados de nivel empresarial. Cubre la segmentación de VLAN, la autenticación RADIUS externa a través del protocolo WISPr, la configuración de walled garden y la integración perfecta con la plataforma de Redes Basadas en Identidad de Purple para capturar datos de primera mano y generar un valor comercial medible en entornos de hotelería, retail y sector público.
Cómo configurar SCEP para un BYOD seguro y autenticación de red 802.1X
Esta guía proporciona una referencia técnica completa para configurar SCEP con el fin de implementar la autenticación de red 802.1X basada en certificados. Cubre la transición arquitectónica de contraseñas compartidas a EAP-TLS, la integración de Mobile Device Management y una segmentación de red estricta para un acceso BYOD seguro en entornos empresariales.
Guía de configuración de WiFi para invitados empresariales: segmentación de VLAN, seguridad y Captive Portals
Esta guía proporciona un plan técnico para la implementación de WiFi para invitados empresariales, centrándose en la segmentación de VLAN, los protocolos de seguridad y la arquitectura de Captive Portal. Detalla cómo aislar el tráfico, aplicar estándares de cifrado y capturar datos de primera mano de forma segura en entornos complejos.