Implementar WPA3-Enterprise para Segurança Wireless Melhorada
Este guia de referência técnica fornece um roteiro abrangente e acionável para líderes de TI que fazem a transição de WPA2 para WPA3-Enterprise. Abrange as mudanças arquitetónicas, melhorias de segurança obrigatórias como EAP-TLS e PMF, e estratégias práticas de implementação para proteger redes corporativas em ambientes empresariais complexos.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada: Arquitetura WPA3-Enterprise
- Autenticação e Troca de Chaves
- Melhorias Criptográficas
- Protected Management Frames (PMF)
- Guia de Implementação: Implementar WPA3-Enterprise
- Fase 1: Auditoria da Infraestrutura e Preparação da PKI
- Fase 2: Ativar o Modo de Transição WPA3
- Fase 3: Segmentação de Rede e Isolamento de Legado
- Fase 4: Aplicação Total de WPA3
- Melhores Práticas para Ambientes Empresariais
- Resolução de Problemas e Mitigação de Riscos
- Sintoma: Os clientes não conseguem ligar quando o Modo de Transição está ativado.
- Sintoma: Falhas de autenticação generalizadas em todos os dispositivos.
- Sintoma: Alta latência durante o roaming entre pontos de acesso.
- ROI e Impacto nos Negócios

Resumo Executivo
Para os líderes de TI empresariais, a transição para WPA3-Enterprise já não é um item de roteiro futuro; é um requisito operacional presente. Desde 2020, o WPA3 é obrigatório para todos os dispositivos Wi-Fi CERTIFIED, contudo, muitas redes empresariais — abrangendo hotelaria, retalho e locais do setor público — permanecem ancoradas no WPA2. Esta lacuna representa uma exposição significativa ao risco, particularmente à medida que os frameworks de conformidade como PCI DSS 4.0 e GDPR exigem cada vez mais controlos de segurança de rede robustos e de última geração.
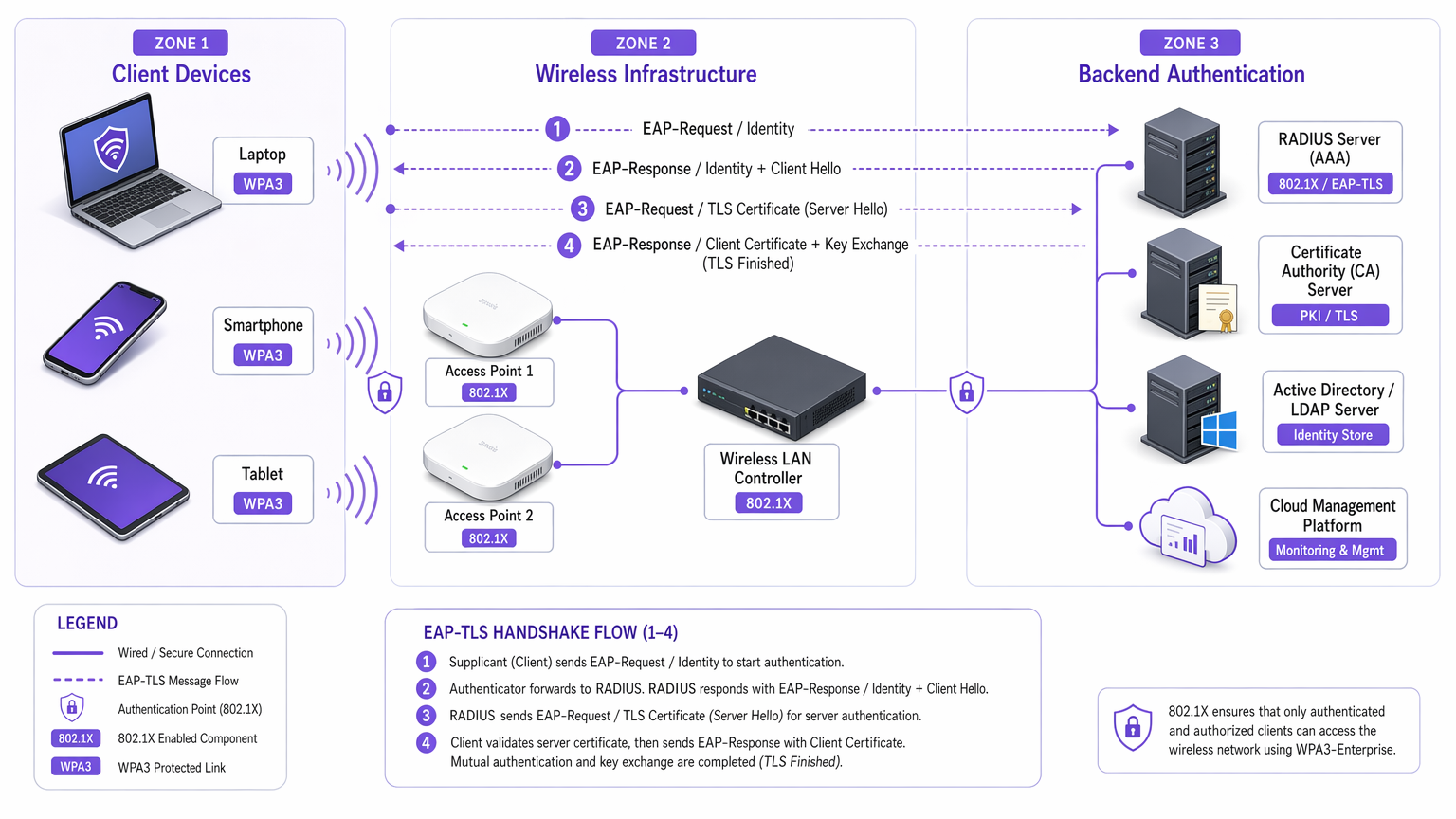
Este guia fornece uma análise técnica abrangente do WPA3-Enterprise, focando nas suas melhorias arquitetónicas fundamentais em relação ao WPA2. Detalhamos a mudança obrigatória para uma encriptação mais forte (GCMP-256), a necessidade de Protected Management Frames (PMF) e a implementação crítica de autenticação mútua baseada em certificados via EAP-TLS. Projetado para arquitetos de rede e CTOs, este documento ignora a teoria académica em favor de estratégias de implementação acionáveis, metodologias de resolução de problemas e estudos de caso reais para garantir uma infraestrutura wireless segura, escalável e compatível.
Ouça o podcast de briefing técnico complementar para uma visão geral executiva:
Análise Técnica Detalhada: Arquitetura WPA3-Enterprise
A diferença fundamental entre WPA2 e WPA3-Enterprise não reside na framework 802.1X subjacente, que permanece o padrão para controlo de acesso à rede baseado em portas, mas nos protocolos criptográficos e proteções de frames de gestão construídos em torno dela. O WPA3 aborda as vulnerabilidades sistémicas do seu predecessor, visando especificamente ataques de dicionário offline e manipulação de frames de gestão.
Autenticação e Troca de Chaves
O WPA2-Enterprise baseia-se no handshake de 4 vias para derivar chaves de sessão, um processo que se provou vulnerável a Key Reinstallation Attacks (KRACK) e a ataques de força bruta de dicionário offline se forem usadas credenciais fracas. O WPA3 mitiga isto implementando a Simultaneous Authentication of Equals (SAE), um protocolo de troca de chaves baseado em Diffie-Hellman. O SAE garante a confidencialidade direta; mesmo que um atacante comprometa uma chave de longo prazo, não pode desencriptar retroativamente o tráfego capturado, uma vez que cada sessão utiliza chaves efémeras e únicas.
Para ambientes empresariais, o mecanismo de autenticação central muda decisivamente para EAP-TLS (Extensible Authentication Protocol-Transport Layer Security). Embora o WPA2 permitisse métodos baseados em credenciais mais fracos como PEAP ou EAP-TTLS, o WPA3-Enterprise encoraja fortemente, e no modo de alta segurança de 192 bits, exige EAP-TLS. Isto requer autenticação mútua baseada em certificados, eliminando completamente as palavras-passe e neutralizando os vetores de roubo de credenciais.
Melhorias Criptográficas
O WPA2 utiliza CCMP-128 (Counter Mode with Cipher Block Chaining Message Authentication Code Protocol) baseado em AES-128. O WPA3-Enterprise introduz um conjunto de segurança opcional, mas altamente recomendado, de 192 bits, alinhado com a Commercial National Security Algorithm (CNSA) Suite. Este modo exige GCMP-256 (Galois/Counter Mode Protocol with 256-bit keys) para uma encriptação robusta, juntamente com criptografia de curva elíptica de 384 bits para estabelecimento e gestão de chaves.
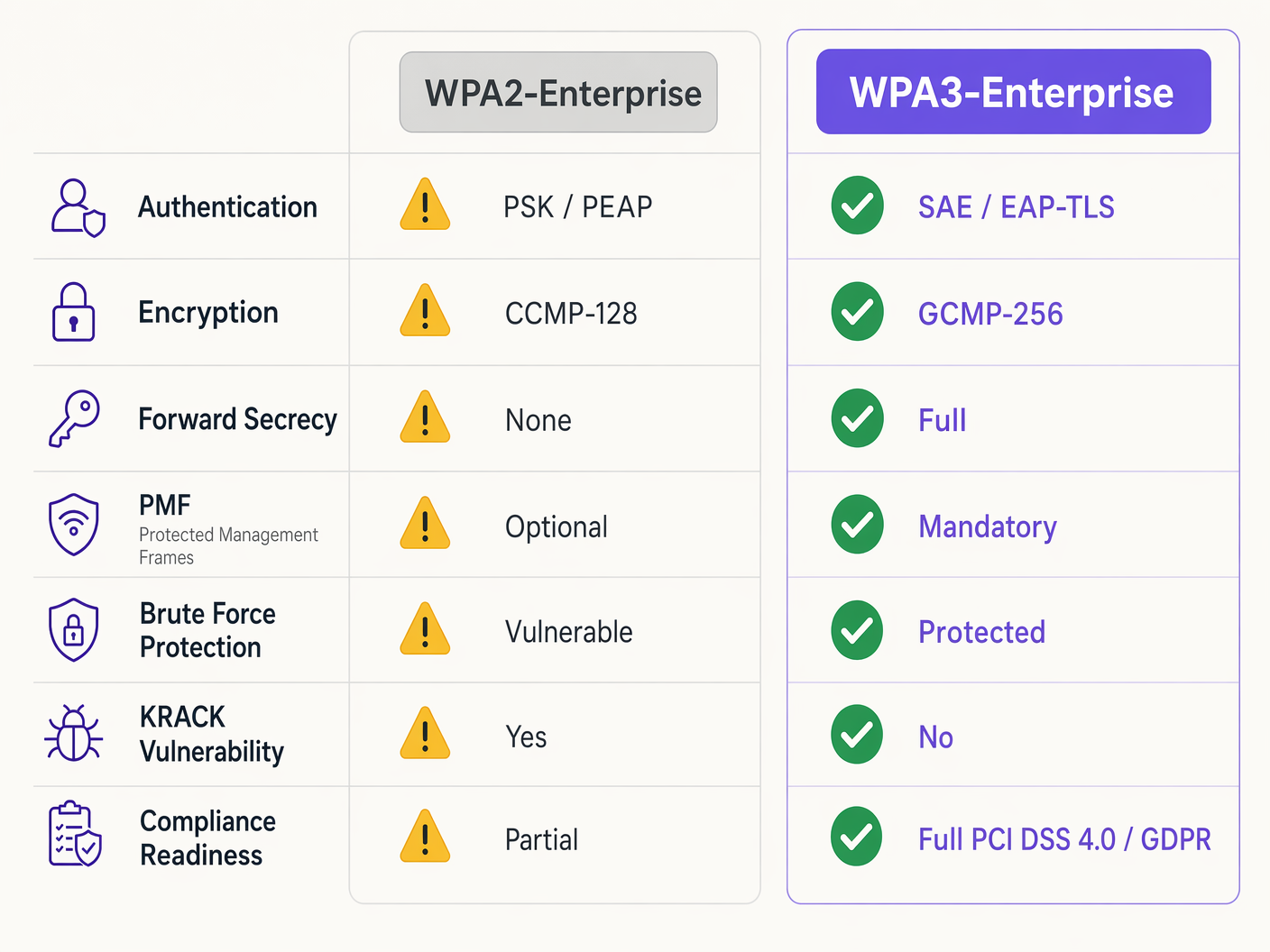
Protected Management Frames (PMF)
Sob o IEEE 802.11w, os Protected Management Frames protegem os sinais de controlo que gerem a associação, desassociação e autenticação de clientes. No WPA2, o PMF era opcional, deixando as redes vulneráveis a frames de desautenticação forjados — um precursor comum de ataques de negação de serviço ou man-in-the-middle. O WPA3 torna o PMF obrigatório para todas as ligações, fechando fundamentalmente este vetor de ataque.
Guia de Implementação: Implementar WPA3-Enterprise
A transição de uma rede empresarial em centenas de locais de retalho ou num complexo hoteleiro extenso requer uma abordagem faseada e metódica. Os passos seguintes descrevem uma estratégia de implementação neutra em relação ao fornecedor.
Fase 1: Auditoria da Infraestrutura e Preparação da PKI
O pré-requisito para WPA3-Enterprise, especificamente utilizando EAP-TLS, é uma Public Key Infrastructure (PKI) robusta.
- Avaliar Capacidades RADIUS: Certifique-se de que os seus servidores RADIUS (por exemplo, Cisco ISE, Aruba ClearPass, FreeRADIUS) suportam os parâmetros WPA3 e estão configurados para EAP-TLS.
- Estabelecer Autoridade de Certificação (CA): Implemente uma CA interna (como Microsoft AD CS) ou utilize um serviço PKI baseado na cloud.
- Integração MDM: Utilize plataformas de Mobile Device Management (MDM) (Intune, Jamf) para automatizar a implementação de certificados de cliente em dispositivos geridos. Isto é crítico para a escalabilidade.
Para leitura adicional sobre a implementação de certificados, consulte WiFi Certificate Authentication: How Digital Certificates Secure Wireless Networks .
Fase 2: Ativar o Modo de Transição WPA3
Uma transição abrupta raramente é viável em ambientes empresariais diversos. A maioria dos controladores de LAN wireless empresariais suporta o Modo de Transição WPA3, permitindo que um único SSID aceite clientes WPA2 e WPA3 simultaneamente.
- Configurar SSID de Transição: Ative o Modo de Transição WPA3 no SSID corporativo.
- Monitorizar Associação de Clientes: Utilize o seu painel de gestão wireless dashboard para monitorizar as ligações dos clientes. Garanta que os dispositivos modernos negoceiam com sucesso WPA3, enquanto os dispositivos legados revertem para WPA2.
- Resolver Problemas de Compatibilidade: Identifique os dispositivos que não conseguem associar. Frequentemente, os drivers wireless legados têm dificuldades com o requisito PMF obrigatório do WPA3, mesmo em modo de transição. Atualize os drivers sempre que possível.
Fase 3: Segmentação de Rede e Isolamento de Legado
Nem todos os dispositivos suportarão WPA3. Dispositivos IoT legados, sistemas de ponto de venda mais antigos ou equipamentos médicos especializados em ambientes de Healthcare frequentemente não possuem o hardware ou as atualizações de firmware necessárias.
- Isolar Dispositivos Legados: Crie uma VLAN dedicada e isolada e um SSID separado apenas com WPA2 especificamente para estes dispositivos.
- Implementar Controlos de Acesso Rígidos: Aplique regras de firewall rigorosas a esta VLAN legada, impedindo o movimento lateral para a rede corporativa segura WPA3.
Fase 4: Aplicação Total de WPA3
Assim que a grande maioria da frota corporativa estiver a utilizar com sucesso WPA3, e os dispositivos legados estiverem segmentados, transicione o SSID corporativo principal para apenas WPA3-Enterprise.
Melhores Práticas para Ambientes Empresariais
Implementar a tecnologia é apenas metade da batalha; manter a sua integridade requer disciplina operacional contínua.
- Automatizar a Gestão do Ciclo de Vida dos Certificados: A causa mais comum de falha de EAP-TLS são os certificados expirados. Implemente processos de renovação automatizados e mecanismos de alerta 90, 60 e 30 dias antes da expiração do certificado do servidor RADIUS.
- Garantir Redundância RADIUS: Um único servidor RADIUS é um único ponto de falha. Implemente servidores RADIUS primários e secundários em locais geograficamente diversos, configurando failover contínuo nos controladores wireless.
- Separar Redes de Convidados e Corporativas: Nunca confunda as políticas de segurança corporativas com o acesso de convidados. As redes corporativas requerem WPA3-Enterprise com EAP-TLS. As redes de convidados devem utilizar VLANs isoladas, tipicamente geridas através de captive portals. As soluções de Guest WiFi da Purple fornecem acesso seguro e compatível para convidados, enquanto capturam WiFi Analytics valiosos.
- Aproveitar o OpenRoaming: Para conectividade contínua e segura em diferentes locais, considere implementar Passpoint/Hotspot 2.0. A Purple atua como um provedor de identidade gratuito para serviços como o OpenRoaming sob a licença Connect, facilitando o acesso sem atritos e seguro sem comprometer os padrões de segurança empresarial.
Resolução de Problemas e Mitigação de Riscos
Mesmo com um planeamento meticuloso, as implementações encontram atritos. Aqui estão os modos de falha comuns e as estratégias de mitigação.
Sintoma: Os clientes não conseguem ligar quando o Modo de Transição está ativado.
Causa Raiz: Os drivers de cliente legados frequentemente falham quando encontram o PMF (Protected Management Frames) obrigatório transmitido pelo ponto de acesso no Modo de Transição, mesmo que estejam a tentar uma ligação WPA2. Mitigação: Atualize os drivers da interface de rede wireless (NIC) do cliente. Se as atualizações não estiverem disponíveis, o dispositivo deve ser movido para o SSID isolado apenas com WPA2 legado.
Sintoma: Falhas de autenticação generalizadas em todos os dispositivos.
Causa Raiz: O certificado do servidor RADIUS expirou, ou o certificado Root CA foi revogado ou removido dos armazenamentos de confiança do cliente. Mitigação: Renove e implemente imediatamente o certificado do servidor RADIUS. Reveja os alertas de gestão automatizada do ciclo de vida para evitar a recorrência.
Sintoma: Alta latência durante o roaming entre pontos de acesso.
Causa Raiz: O 802.11r (Fast BSS Transition) está mal configurado ou é incompatível com o método EAP específico em uso. Mitigação: Garanta que o 802.11r está explicitamente ativado e suportado tanto pelo controlador WLAN quanto pelos dispositivos cliente para o SSID WPA3. Teste o desempenho do roaming durante as janelas de manutenção.
ROI e Impacto nos Negócios
A transição para WPA3-Enterprise requer investimento em serviços profissionais, potenciais atualizações de hardware e infraestrutura PKI. No entanto, o retorno do investimento é medido na mitigação de riscos e na adesão à conformidade.
Para uma grande cadeia de Retail , o custo de uma violação de dados envolvendo informações de cartões de pagamento excede em muito os custos de implementação de WPA3. A conformidade com PCI DSS 4.0 exige criptografia e autenticação robustas; o WPA3-Enterprise satisfaz diretamente estes requisitos, simplificando as auditorias de conformidade e evitando potenciais multas.
Além disso, modernizar a infraestrutura wireless fornece uma base estável e de alto desempenho para futuras iniciativas digitais, seja a implementação de sensores IoT avançados em Hospitality ou a ativação de sistemas de ponto de venda móveis seguros. O impacto nos negócios é uma arquitetura de rede resiliente, compatível e preparada para o futuro.
Definições Principais
WPA3-Enterprise
The current standard for enterprise wireless security, mandating stronger encryption, protected management frames, and forward secrecy, typically deployed with 802.1X and RADIUS.
Required for compliance (PCI DSS, GDPR) and securing corporate data against modern cryptographic attacks.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security)
An authentication framework requiring both the client and the RADIUS server to present digital certificates to verify each other's identity.
The gold standard for WPA3-Enterprise authentication, eliminating the reliance on vulnerable user passwords.
PMF (Protected Management Frames)
A security standard (802.11w) that encrypts the control frames used for client association and disassociation.
Mandatory in WPA3, PMF prevents attackers from forging deauthentication packets to knock users off the network or execute man-in-the-middle attacks.
SAE (Simultaneous Authentication of Equals)
A secure key establishment protocol used in WPA3 that replaces the vulnerable 4-way handshake of WPA2.
SAE provides forward secrecy and protects against offline dictionary attacks, ensuring that even if a password is weak, the handshake cannot be brute-forced.
GCMP-256 (Galois/Counter Mode Protocol)
A highly secure, efficient encryption protocol utilizing 256-bit keys.
Mandated for the WPA3-Enterprise 192-bit security suite, required for environments handling highly sensitive data like government or financial records.
RADIUS (Remote Authentication Dial-In User Service)
A centralized networking protocol that provides Authentication, Authorization, and Accounting (AAA) management for users connecting to a network service.
The core backend server in a WPA3-Enterprise deployment that validates client certificates or credentials before granting network access.
Forward Secrecy
A cryptographic feature ensuring that session keys are ephemeral; compromising a long-term key in the future will not allow an attacker to decrypt past recorded sessions.
A critical enhancement in WPA3 provided by the SAE handshake, protecting historical data.
PKI (Public Key Infrastructure)
The framework of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates.
The necessary prerequisite infrastructure for deploying EAP-TLS authentication in a WPA3-Enterprise environment.
Exemplos Práticos
A 200-room luxury hotel is upgrading its corporate network to WPA3-Enterprise. They have a mix of modern corporate laptops, iPads used by concierge staff, and legacy Wi-Fi-enabled door locks that only support WPA2. How should the network architect design the SSIDs and VLANs to ensure maximum security without breaking operational functionality?
The architect must employ network segmentation.
- Create a primary corporate SSID ('HotelCorp_Secure') configured for WPA3-Enterprise only, utilizing EAP-TLS. Deploy certificates to all corporate laptops and iPads via the hotel's MDM solution. Assign this SSID to the primary corporate VLAN.
- Create a secondary, hidden SSID ('Hotel_IoT_Legacy') configured for WPA2-Personal (PSK) or WPA2-Enterprise (if supported by the locks), utilizing a complex, rotated passphrase or MAC authentication bypass (MAB).
- Assign the legacy SSID to a heavily restricted, isolated VLAN. Configure firewall rules to allow the door locks to communicate ONLY with the specific on-premise or cloud-based door management server, blocking all lateral movement to the corporate VLAN or the internet.
A public sector organization has deployed WPA3-Enterprise with EAP-TLS. On a Monday morning, no staff can connect to the wireless network. The wireless controller shows clients associating, but failing RADIUS authentication. What is the most likely cause, and what is the immediate remediation step?
The most likely cause is an expired RADIUS server certificate. Because EAP-TLS relies on mutual authentication, if the server presents an expired certificate, the clients will immediately reject the connection and terminate the handshake.
Immediate remediation: The IT team must generate a new Certificate Signing Request (CSR) from the RADIUS server, have it signed by the internal CA, and bind the new certificate to the EAP-TLS authentication policy on the RADIUS server. Services must then be restarted.
Perguntas de Prática
Q1. You are the network architect for a large retail chain rolling out WPA3-Enterprise. During the pilot phase at three stores using WPA3 Transition Mode, several older barcode scanners frequently drop off the network and require manual reboots to reconnect. Modern tablets connect without issue. What is the most appropriate architectural response?
Dica: Consider how legacy wireless drivers handle unfamiliar management frames broadcast in Transition Mode.
Ver resposta modelo
The barcode scanners are likely crashing due to the mandatory Protected Management Frames (PMF) broadcast by the APs in Transition Mode. The appropriate response is to abandon Transition Mode for these devices. Create a dedicated, hidden WPA2-only SSID mapped to an isolated VLAN specifically for the scanners, and configure the primary corporate SSID to WPA3-Enterprise only for the modern tablets.
Q2. A CTO mandates the deployment of WPA3-Enterprise across all corporate offices within 60 days to meet new compliance requirements. The current environment uses WPA2-Enterprise with PEAP-MSCHAPv2 (username/password). The organization does not currently have an internal Certificate Authority (CA) or a Mobile Device Management (MDM) solution. Is this timeline realistic, and what is the critical path?
Dica: Evaluate the prerequisites for the recommended WPA3 authentication method (EAP-TLS).
Ver resposta modelo
The 60-day timeline is highly unrealistic. To properly implement WPA3-Enterprise, the organization should migrate to EAP-TLS to eliminate credential vulnerabilities. The critical path requires designing and deploying a PKI (Certificate Authority) and implementing an MDM solution to distribute client certificates. Building this infrastructure from scratch, testing it, and enrolling all corporate devices will almost certainly exceed 60 days. The architect must communicate this dependency to the CTO.
Q3. During a security audit, an examiner notes that your RADIUS servers are configured for EAP-TLS, but the 'Certificate Revocation List (CRL) checking' feature is disabled on the wireless controllers and RADIUS servers. Why is this a significant security finding in a WPA3 environment?
Dica: What happens if a corporate laptop is stolen, but its certificate has not yet expired?
Ver resposta modelo
Without CRL or OCSP checking enabled, the RADIUS server has no way of knowing if a presented certificate has been revoked by the CA prior to its natural expiration date. If a device is lost or an employee is terminated, their certificate must be revoked. If revocation checking is disabled, that compromised certificate can still be used to successfully authenticate and access the WPA3-Enterprise network, entirely defeating the purpose of mutual authentication.
Continue a ler esta série
Como Configurar o SCEP para BYOD Seguro e Autenticação de Rede 802.1X
Este guia fornece uma referência técnica abrangente para configurar o SCEP para implementar a autenticação de rede 802.1X baseada em certificados. Abrange a transição arquitetónica de palavras-passe partilhadas para EAP-TLS, a integração de Gestão de Dispositivos Móveis (MDM) e a segmentação de rede rigorosa para acesso BYOD seguro em ambientes empresariais.
Guia de Configuração de Guest WiFi Empresarial: Segmentação de VLAN, Segurança e Captive Portals
Este guia fornece um plano técnico para a implementação de guest WiFi empresarial, focando-se na segmentação de VLAN, protocolos de segurança e arquitetura de Captive Portal. Detalha como isolar o tráfego, aplicar normas de encriptação e recolher dados first-party de forma segura em locais complexos.
Políticas de WiFi para Colaboradores no Retalho: Proteger as Redes Back-of-House
Este guia aborda os requisitos técnicos e de políticas críticos para proteger as redes WiFi back-of-house no retalho - desde a segmentação de VLAN e conformidade com o PCI DSS 4.0 até à gestão de BYOD de funcionários na loja. Oferece aos gestores de TI, arquitetos de rede e diretores de operações um plano prático e neutro em termos de fornecedor que podem implementar já este trimestre.