Student WiFi: What Universities Need to Get Right
This authoritative guide details the critical architecture, security protocols, and analytics required to deliver high-performance student WiFi at scale. It provides IT leaders with actionable strategies for managing BYOD density, implementing robust authentication, and leveraging network intelligence for estate management.
- Executive Summary
- Technical Deep-Dive: Architecture and Standards
- High-Density Network Topology
- Authentication and Security Frameworks
- Implementation Guide: Managing the Device Landscape
- The BYOD Challenge
- Best Practices and Network Intelligence
- Leveraging WiFi Analytics
- Industry Contexts
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
Delivering robust student WiFi is no longer a peripheral IT function; it is a critical operational dependency for modern universities and large-scale educational venues. The explosion of Bring Your Own Device (BYOD) density—now averaging 3 to 5 devices per student—demands a fundamental shift from legacy, flat networks to intelligent, highly segmented architectures. This technical reference guide provides CTOs, Network Architects, and IT Directors with actionable, vendor-neutral strategies to design, deploy, and manage high-performance campus connectivity. We will explore the necessary transition to 802.11ax (Wi-Fi 6) in high-density zones, the implementation of rigorous authentication protocols like 802.1X via eduroam, and the critical role of network analytics in capacity planning and security compliance. Furthermore, we will examine how integrating solutions like Guest WiFi and WiFi Analytics can transform the network from a cost centre into a strategic asset for estate management and user engagement.
Technical Deep-Dive: Architecture and Standards
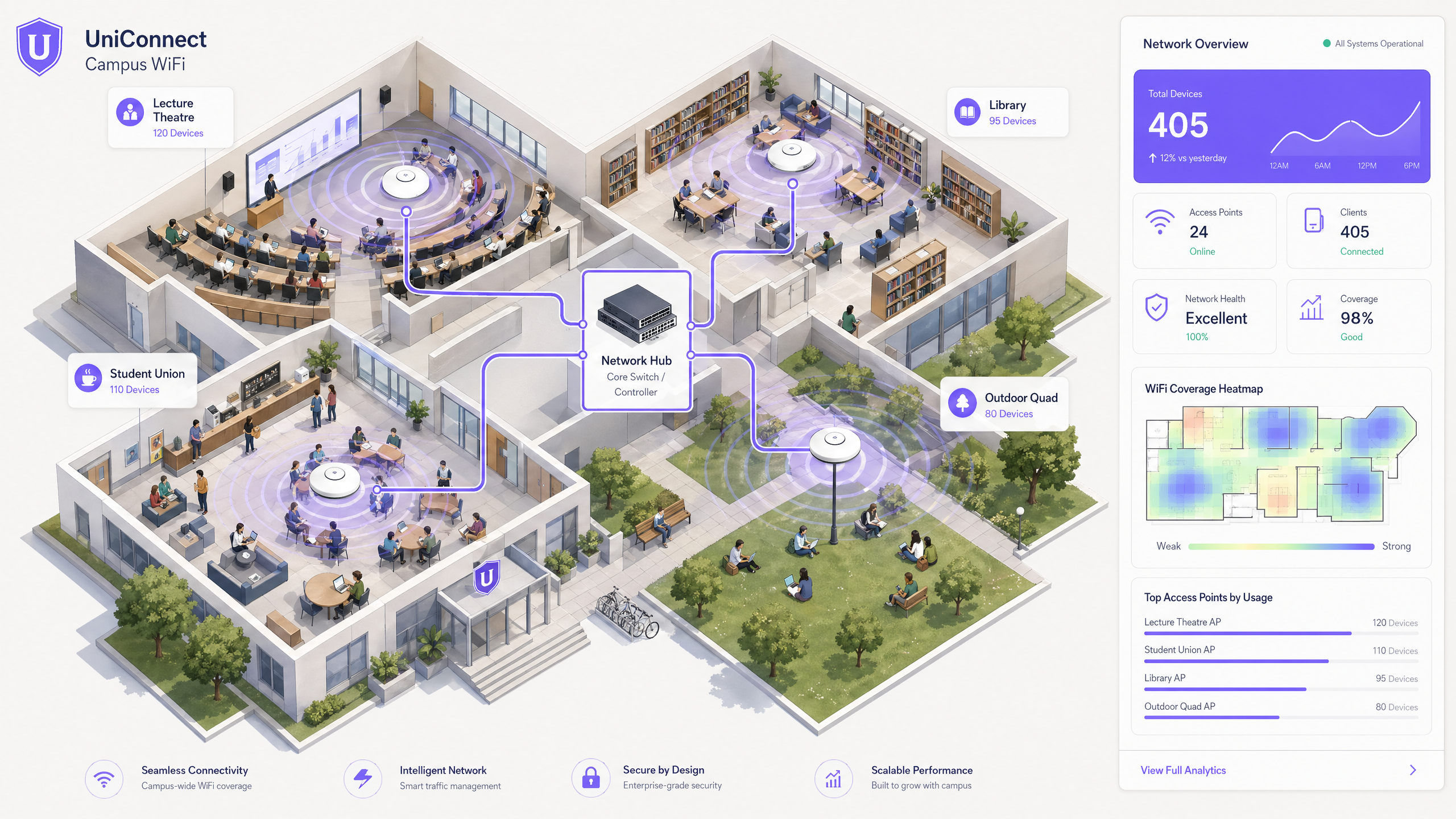
High-Density Network Topology
The foundation of reliable campus WiFi is a resilient, three-tier hierarchical network design. A flat network cannot scale to meet the demands of thousands of concurrent users and devices.
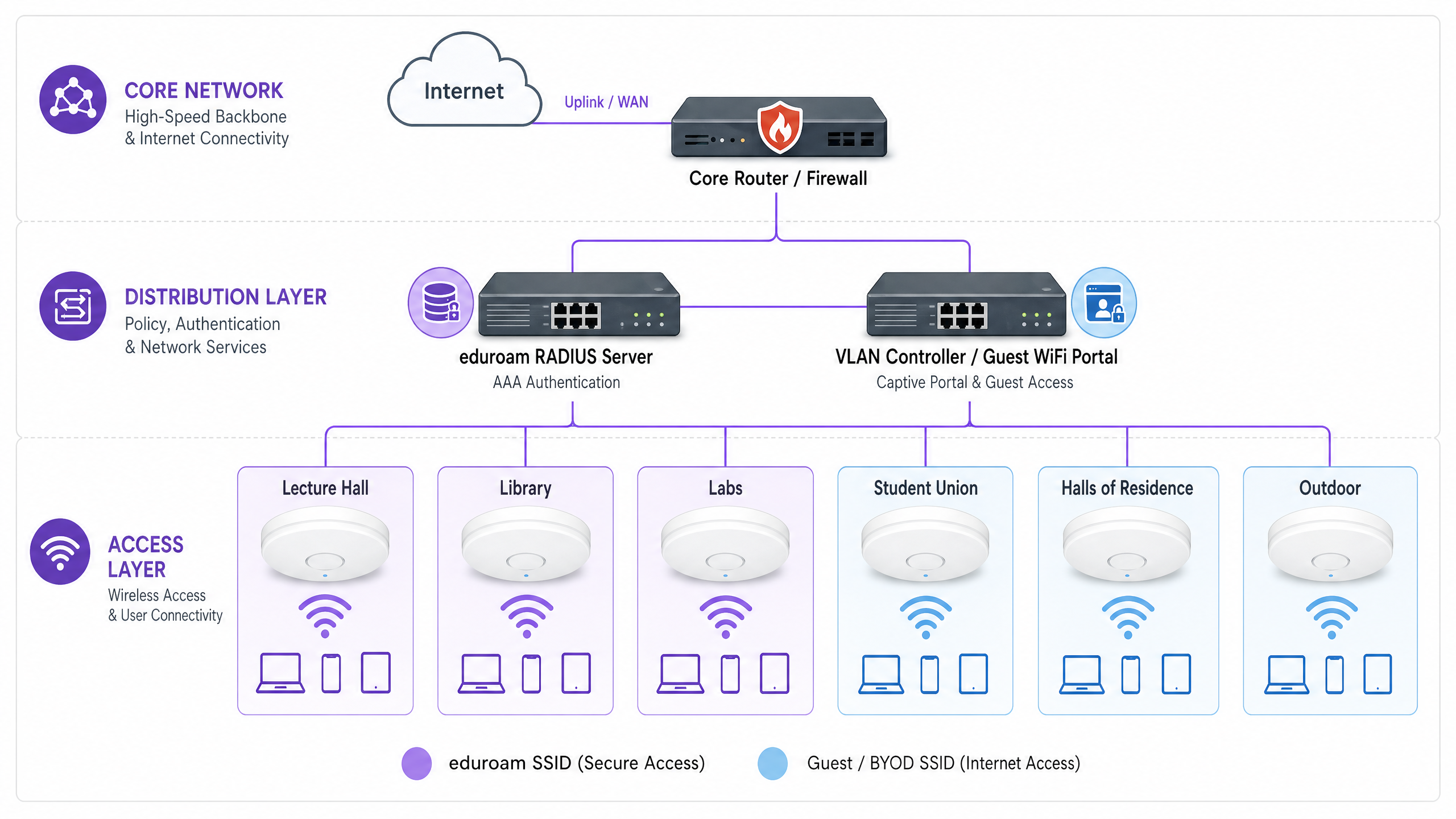
- Core Layer: The high-speed backbone, demanding redundant routers and firewalls with substantial throughput to handle aggregated traffic from the distribution layer. It must support high-capacity uplinks (e.g., 40Gbps or 100Gbps) to the WAN or internet service provider. Consider dedicated connectivity solutions like a leased line to guarantee bandwidth and minimise latency for critical institutional applications.
- Distribution Layer: This layer aggregates access switches, enforces routing policies, and provides critical network services. Here, intelligent VLAN management and access control lists (ACLs) are deployed to segment traffic. For instance, segmenting student BYOD traffic from administrative systems and IoT infrastructure is paramount for security and performance.
- Access Layer: The edge of the network where users connect. In a university context, this involves dense deployments of wireless access points (APs). Upgrading to 802.11ax (Wi-Fi 6) is essential in high-density areas like lecture theatres, libraries, and student unions. Wi-Fi 6 introduces technologies like Orthogonal Frequency-Division Multiple Access (OFDMA) and Multi-User Multiple Input Multiple Output (MU-MIMO), significantly improving spectral efficiency and performance in crowded environments.
Authentication and Security Frameworks
Securing the campus network requires a multi-layered approach to authentication, balancing rigorous security with user accessibility.
- 802.1X and eduroam: For students and staff, IEEE 802.1X is the gold standard, providing port-based Network Access Control (NAC). In higher education, this is almost universally delivered via eduroam, allowing users to authenticate securely using their institutional credentials across participating global institutions. This utilises EAP (Extensible Authentication Protocol) to provide encrypted, authenticated access.
- Guest and BYOD Onboarding: eduroam does not cover all use cases. Guests, contractors, and headless IoT devices (like gaming consoles or smart speakers in halls of residence) require alternative onboarding. This is where a robust captive portal and MAC Authentication Bypass (MAB) are critical. Deploying a dedicated Guest WiFi solution allows IT teams to securely onboard these devices, enforcing acceptable use policies and maintaining visibility without compromising the secure 802.1X network. Protect Your Network with Strong DNS and Security is crucial here to prevent malicious traffic originating from unmanaged guest devices.
- OpenRoaming: Looking forward, OpenRoaming represents the next evolution in seamless connectivity. Purple acts as a free identity provider for OpenRoaming under the Connect license, allowing users to transition securely and automatically between cellular networks and Wi-Fi without manual captive portal interactions.
Implementation Guide: Managing the Device Landscape
The BYOD Challenge
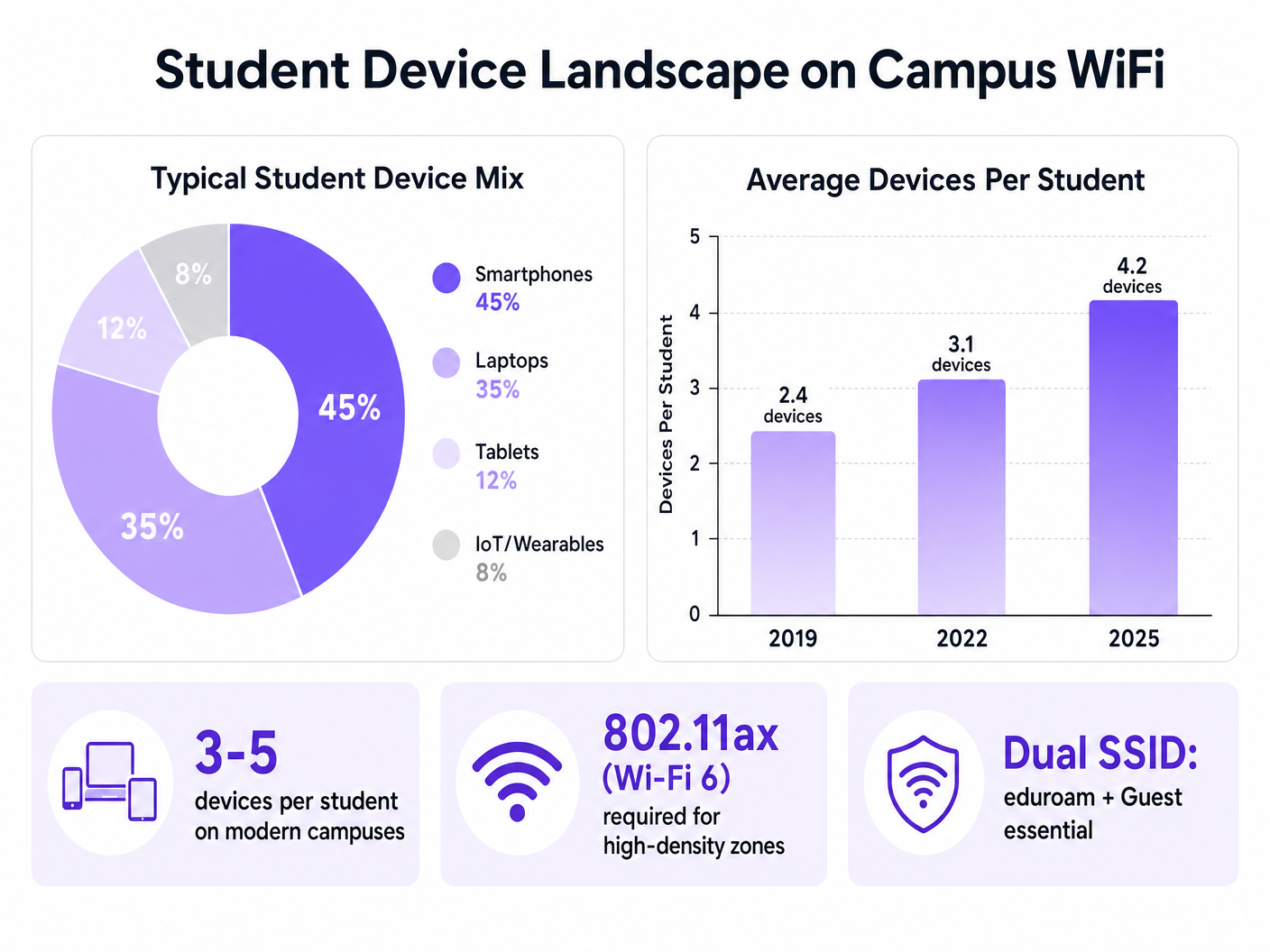
The sheer volume and variety of devices present a significant challenge. IT teams must plan for capacity, not just coverage.
- RF Planning and Site Surveys: Deployment must begin with comprehensive predictive and active site surveys. This involves mapping attenuation across different building materials (e.g., thick stone walls in historic buildings vs. modern glass structures) and planning AP placement to minimise co-channel interference while maximising signal-to-noise ratio (SNR).
- Segmenting IoT and Headless Devices: Halls of residence present unique challenges due to the proliferation of consumer IoT devices. These devices often lack 802.1X support. IT teams must implement self-service portals where students can register device MAC addresses, which are then assigned to specific, isolated VLANs via MAB. This prevents broadcast storms and isolates potential security vulnerabilities.
- Dual SSID Strategy: A standard best practice is broadcasting a minimal number of SSIDs to reduce management overhead. Typically, this involves one secure SSID (eduroam/802.1X) and one open SSID with a captive portal for guests and legacy device onboarding.
Best Practices and Network Intelligence
Deploying the infrastructure is only the first step; continuous monitoring and optimisation are required.
Leveraging WiFi Analytics
Network telemetry provides invaluable insights beyond basic uptime metrics. By utilising WiFi Analytics , IT and estate management teams can understand spatial utilisation and user behaviour.
- Capacity Planning: Heatmaps and location analytics reveal which areas are consistently over capacity, informing targeted infrastructure upgrades rather than blanket deployments.
- Estate Management: Data on dwell times and footfall can inform decisions on building utilisation, cleaning schedules, and resource allocation across the campus.
Industry Contexts
While this guide focuses on higher education, the principles of high-density WiFi design and secure onboarding apply equally to other sectors. For example, large-scale deployments in Retail environments rely on similar analytics to understand shopper behaviour, while Hospitality venues require robust guest onboarding systems to manage conference attendees and hotel guests securely. Similar complex, multi-zone environments can be seen in transport hubs; for insights into these deployments, refer to our guide on Airport WiFi: How Operators Deliver Connectivity Across Terminals (or the Italian version: WiFi Aeroportuale: Come gli Operatori Forniscono Connettività tra i Terminal ).
Troubleshooting & Risk Mitigation
- Co-Channel Interference (CCI): In dense deployments, APs transmitting on the same channel can interfere with each other, degrading performance. Mitigation: Implement dynamic Radio Resource Management (RRM) to automatically adjust channel assignments and transmit power levels.
- Rogue Access Points: Students plugging in personal routers in halls of residence can disrupt the managed RF environment and introduce security vulnerabilities. Mitigation: Deploy Wireless Intrusion Prevention Systems (WIPS) to detect and automatically suppress unauthorised APs.
- Captive Portal Issues: A poorly configured captive portal can lead to high abandonment rates and helpdesk tickets. Mitigation: Ensure the portal is mobile-responsive, uses valid SSL certificates to avoid browser warnings, and integrates seamlessly with backend RADIUS/Active Directory systems.
ROI & Business Impact
Investing in enterprise-grade student WiFi delivers measurable returns:
- Reduced Support Costs: A robust, self-service onboarding process for BYOD and IoT devices significantly reduces Tier 1 helpdesk tickets.
- Optimised Estate Utilisation: Network analytics provide the data needed to optimise space usage, potentially delaying or avoiding costly new building projects.
- Enhanced Student Experience: Reliable connectivity is a key metric in student satisfaction surveys, directly impacting recruitment and retention. The recent appointment of industry experts highlights the strategic importance of this sector; see Purple Signals Higher Education Ambitions with Appointment of VP Education Tim Peers for more context.
By treating the network as a strategic asset and leveraging intelligent analytics and secure onboarding platforms, universities can deliver the high-performance connectivity that modern education demands.
Key Terms & Definitions
802.11ax (Wi-Fi 6)
The latest standard in wireless networking, designed specifically to improve efficiency and performance in high-density environments through technologies like OFDMA.
Essential for deployment in crowded areas like lecture halls and libraries to handle the high volume of concurrent student devices.
802.1X
An IEEE standard for port-based Network Access Control (NAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The underlying security protocol used by eduroam to ensure only authenticated students and staff can access the secure campus network.
eduroam
An international roaming service for users in research, higher education, and further education, providing secure network access using their home institution credentials.
The primary secure SSID broadcast across most university campuses globally.
MAC Authentication Bypass (MAB)
A technique used to authenticate devices that do not support 802.1X (like gaming consoles or printers) by using their MAC address as the credential.
Crucial for onboarding headless student IoT devices in halls of residence without compromising the main 802.1X network.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs, allowing them to communicate as if they were on the same physical network.
Used extensively to segment network traffic, isolating student BYOD devices from critical administrative or financial systems.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
Used on the Guest SSID to present acceptable use policies and authenticate visitors or non-802.1X devices.
Co-Channel Interference (CCI)
Interference that occurs when two or more wireless access points are transmitting on the same frequency channel within range of each other.
A primary cause of poor network performance in dense deployments, mitigated by careful RF planning and dynamic channel assignment.
OpenRoaming
A federation of Wi-Fi networks that allows users to automatically and securely connect to participating networks without manual login or captive portals.
The future of seamless campus connectivity, reducing friction for users moving between cellular and Wi-Fi networks.
Case Studies
A university is upgrading a historic, 500-seat lecture theatre from Wi-Fi 4 to Wi-Fi 6. The walls are thick masonry, and previous deployments suffered from severe dead spots and dropped connections during peak lecture times. How should the IT team approach this deployment?
- Conduct a pre-deployment active site survey to measure the specific attenuation of the masonry walls. 2. Instead of placing APs in the hallways to penetrate the walls, deploy high-density, directional Wi-Fi 6 APs inside the theatre, mounted on the ceiling or walls, pointing towards the seating areas. 3. Configure narrow channel widths (e.g., 20MHz) to maximize the number of available non-overlapping channels and reduce co-channel interference in the dense environment. 4. Enable OFDMA and MU-MIMO features on the controller to handle the high volume of concurrent client connections efficiently.
The IT helpdesk is overwhelmed with tickets at the start of term from students in halls of residence unable to connect their gaming consoles and smart TVs to the 802.1X eduroam network.
- Deploy a dedicated Guest/BYOD SSID alongside eduroam. 2. Implement a self-service device registration portal integrated with the network access control (NAC) system. 3. Students log into the portal using their university credentials and register the MAC addresses of their headless devices. 4. The NAC system uses MAC Authentication Bypass (MAB) to assign these specific devices to an isolated 'Student IoT' VLAN, granting them internet access while keeping them separated from the secure academic network.
Scenario Analysis
Q1. A university is planning to deploy Wi-Fi in a new, high-density student union building. The IT director suggests using wide 80MHz channels to maximize the advertised bandwidth per user. Is this the correct approach?
💡 Hint:Consider the impact of wide channels on the number of available non-overlapping channels in a dense RF environment.
Show Recommended Approach
No, this is not recommended for high-density environments. While 80MHz channels offer higher theoretical peak throughput for a single client, they drastically reduce the number of available non-overlapping channels. In a dense environment like a student union, this will lead to severe Co-Channel Interference (CCI), degrading performance for everyone. The best practice is to use narrow 20MHz channels to maximize channel re-use and overall network capacity.
Q2. The security team requires that all student devices in halls of residence be isolated from each other to prevent lateral movement in case of a malware infection. However, students complain they cannot cast from their phones to their smart TVs. How can network architecture solve this?
💡 Hint:Look into technologies that manage broadcast/multicast traffic across segmented networks.
Show Recommended Approach
The network should be configured with Client Isolation (or AP Isolation) enabled on the student VLAN to prevent direct device-to-device communication. To solve the casting issue, the IT team must implement a Multicast DNS (mDNS) gateway or Bonjour gateway service on the network controller. This service selectively proxies discovery protocols (like AirPlay or Chromecast) across the isolated network segments, allowing students to discover and cast to their own devices without exposing them to the entire subnet.
Q3. A university wants to monetize its guest WiFi network during large sporting events held at the campus stadium, while ensuring the academic network remains secure and unaffected. What architecture should be deployed?
💡 Hint:Consider the integration of analytics platforms and strict network segmentation.
Show Recommended Approach
The university should deploy a dedicated Guest SSID for the stadium, completely isolated from the academic network via VLANs and firewall rules. This SSID should route traffic through a captive portal integrated with a platform like Purple's Guest WiFi. The portal can require data capture (e.g., email or SMS auth) or display sponsored advertising before granting access. Crucially, the traffic must be routed directly to the internet, bypassing internal routing, to ensure the academic core network is protected from potential spikes in guest traffic.



