Best Practices per la Micro-Segmentazione nelle Reti WiFi Condivise
Questa guida tecnica di riferimento fornisce strategie attuabili per implementare la micro-segmentazione su infrastrutture WiFi condivise. Dettaglia come i responsabili IT e gli architetti di rete possono isolare in modo sicuro il traffico degli ospiti, IoT e del personale per mitigare i rischi, garantire la conformità e ottimizzare le prestazioni della rete.
Ascolta questa guida
Visualizza trascrizione del podcast
- Riepilogo Esecutivo
- Approfondimento Tecnico
- Il Livello di Autenticazione: IEEE 802.1X e WPA3
- I Tre Segmenti Principali
- Guida all'Implementazione
- Fase 1: Scoperta e Audit della Rete
- Fase 2: Definizione delle Policy
- Fase 3: Configurazione dell'Infrastruttura
- Fase 4: Rollout a Fasi
- Best Practices
- Risoluzione dei Problemi e Mitigazione del Rischio
- ROI e Impatto sul Business

Riepilogo Esecutivo
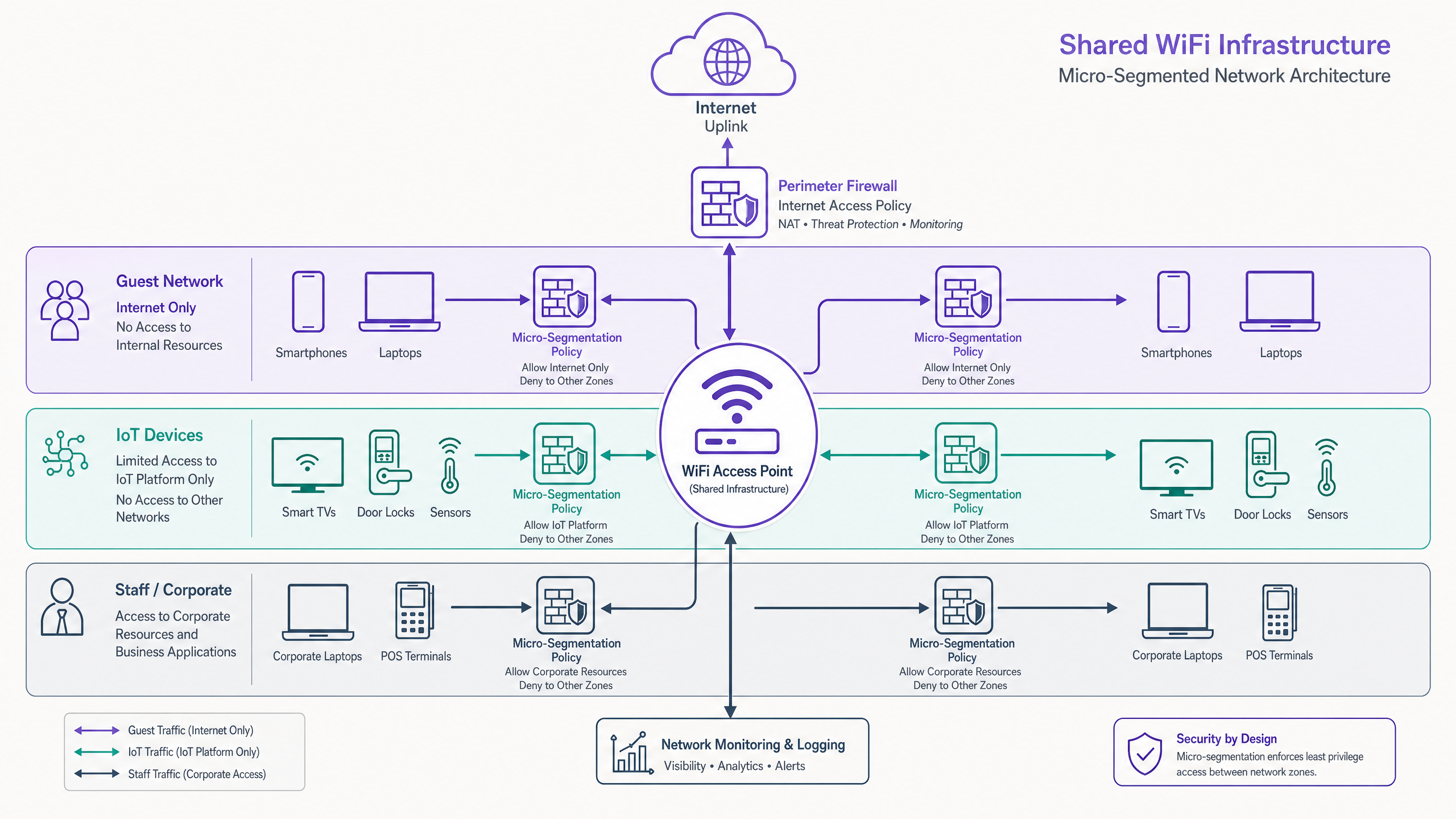
Operare un'infrastruttura WLAN condivisa senza una micro-segmentazione granulare rappresenta una significativa vulnerabilità di sicurezza per le sedi moderne. Man mano che il perimetro si dissolve, la rete interna diventa la principale superficie di attacco. Questa guida descrive i principi architetturali e le metodologie di implementazione necessarie per imporre un isolamento zero-trust tra il traffico degli ospiti, le flotte IoT e gli endpoint aziendali su un livello di accesso fisico unificato.
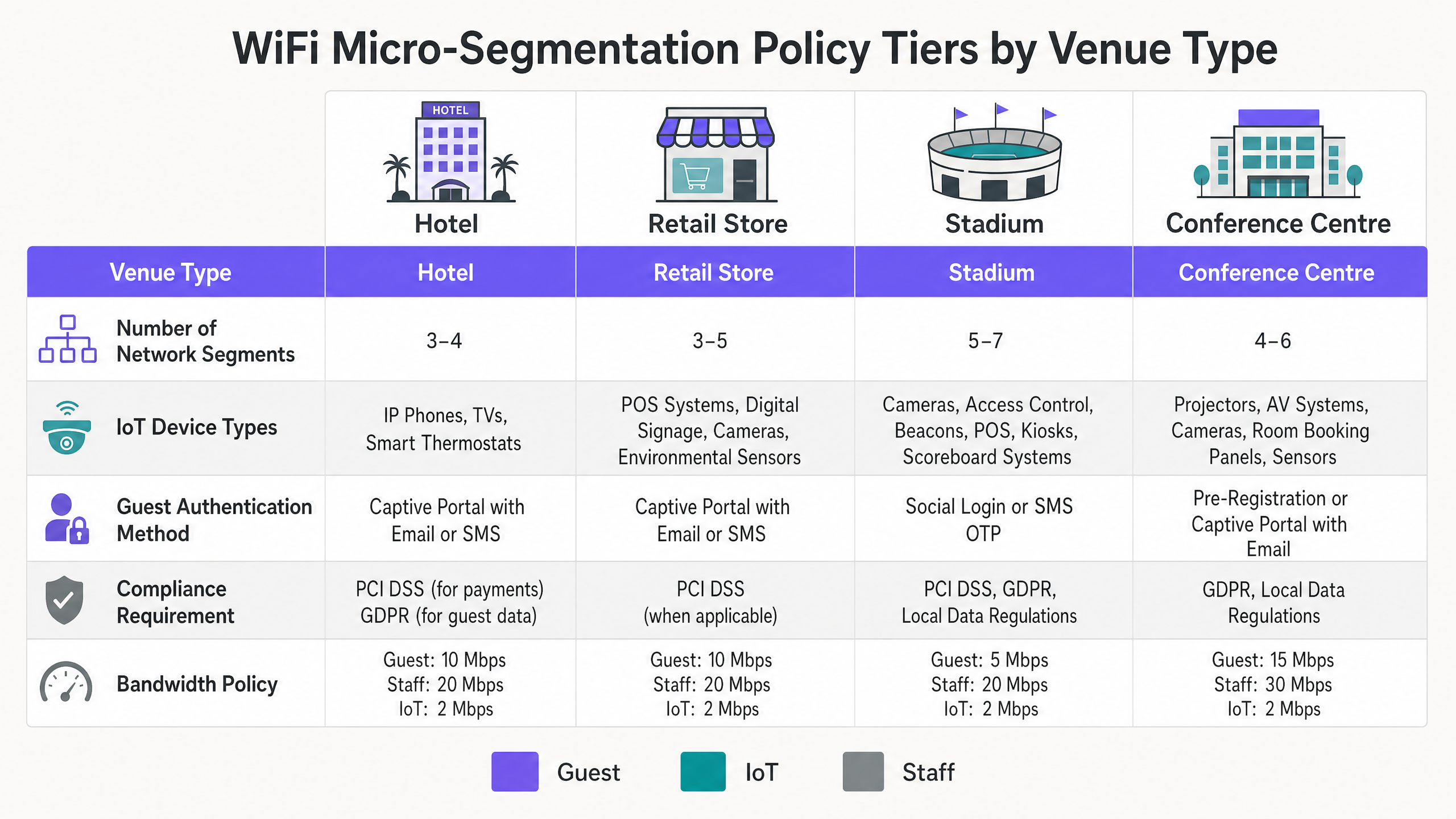
Per i CTO e gli architetti di rete in Ospitalità , Vendita al Dettaglio , Sanità e Trasporti , il mandato è chiaro: le VLAN tradizionali sono insufficienti. Implementando una micro-segmentazione dinamica e basata su policy utilizzando IEEE 802.1X e RADIUS, le organizzazioni possono ridurre significativamente l'ambito di conformità PCI DSS e GDPR, mitigando al contempo il rischio di movimento laterale da dispositivi embedded compromessi.
Ascolta il podcast del briefing tecnico per un riassunto audio:
Approfondimento Tecnico
La micro-segmentazione su una WLAN condivisa richiede di andare oltre la mappatura statica SSID-to-VLAN. Richiede l'applicazione dinamica delle policy basata sull'identità al bordo della rete.
Il Livello di Autenticazione: IEEE 802.1X e WPA3
La base di una segmentazione efficace è un'autenticazione robusta. Affidarsi esclusivamente a Pre-Shared Keys (PSK) su più SSID fornisce un'illusione di separazione. La vera micro-segmentazione sfrutta IEEE 802.1X per autenticare il dispositivo o l'utente rispetto a un backend RADIUS, assegnando dinamicamente il client alla VLAN appropriata e applicando Access Control Lists (ACL) specifiche basate sull'identità.
Per le implementazioni moderne, WPA3 è irrinunciabile. Le reti ospiti dovrebbero utilizzare WPA3-Personal con Simultaneous Authentication of Equals (SAE) per proteggere dagli attacchi di dizionario offline, mentre i segmenti aziendali devono imporre WPA3-Enterprise (modalità a 192 bit dove l'hardware lo consente).
I Tre Segmenti Principali
Traffico Ospiti (Non Affidabile): Gli ospiti rappresentano il segmento con il volume più alto e la fiducia più bassa. L'autenticazione è tipicamente gestita tramite un Captive Portal ( Guest WiFi ) utilizzando email, SMS o social login. Il controllo critico qui è l'Isolamento Client (isolamento Layer 2) per prevenire la comunicazione peer-to-peer tra i dispositivi degli ospiti. Il traffico deve essere strettamente solo internet, con filtraggio DNS applicato per bloccare i domini dannosi. Consulta la nostra guida su Cos'è il Filtraggio DNS? Come Bloccare Contenuti Dannosi sul Guest WiFi per i dettagli di implementazione.
Dispositivi IoT (Semi-Affidabili, Alto Rischio): I dispositivi IoT—dalle smart TV ai sensori HVAC—sono noti per la scarsa igiene di sicurezza. Devono risiedere in un segmento isolato con policy di sola uscita. Un dispositivo IoT dovrebbe essere in grado di comunicare solo con la sua specifica piattaforma di gestione. L'implementazione di reti di tracciamento o sensori BLE Low Energy Explained for Enterprise richiede questo stretto isolamento per prevenire il movimento laterale.
Personale e Aziendale (Affidabile): Questo segmento gestisce dati sensibili, incluse transazioni POS e sistemi HR. L'accesso deve richiedere l'autenticazione reciproca basata su certificati (EAP-TLS). I dispositivi aziendali dovrebbero essere registrati tramite MDM, garantendo una connettività fluida e sicura.
Guida all'Implementazione
L'implementazione della micro-segmentazione in un ambiente distribuito richiede un approccio graduale e metodico.
Fase 1: Scoperta e Audit della Rete
Non puoi segmentare ciò che non puoi vedere. Inizia con un audit completo di tutti i dispositivi connessi, mappandoli ai loro livelli di accesso alla rete richiesti. Utilizza il monitoraggio del flusso (NetFlow/sFlow) per stabilire i modelli di comunicazione normali.
Fase 2: Definizione delle Policy
Definisci la tua matrice di segmentazione. Mappa ogni classe di dispositivo a una VLAN specifica e definisci le regole di routing inter-VLAN. La postura predefinita deve essere deny-all, con eccezioni di permesso esplicite solo dove strettamente necessario.
Fase 3: Configurazione dell'Infrastruttura
Configura il tuo server RADIUS per restituire gli attributi specifici del fornitore (VSA) corretti per l'assegnazione dinamica delle VLAN. Assicurati che i tuoi access point e gli switch upstream siano configurati per taggare e trunkare correttamente queste VLAN.
Fase 4: Rollout a Fasi
Non tentare una migrazione "big bang". Inizia isolando la flotta IoT—questo offre il più alto ritorno di sicurezza immediato con minima interruzione per l'utente. Prosegui con il segmento ospiti e, infine, migra i dispositivi aziendali al segmento sicuro 802.1X.
Best Practices
- Applica l'Isolamento Client: Abilita sempre l'isolamento client sugli SSID ospiti per prevenire attacchi laterali tra dispositivi non affidabili.
- Utilizza l'Assegnazione Dinamica delle VLAN: Abbandona la mappatura statica degli SSID. Usa RADIUS per assegnare le VLAN in base al ruolo dell'utente o alla profilazione del dispositivo.
- Implementa il Filtraggio DNS: Applica policy di filtraggio DNS specifiche per segmento per prevenire la comunicazione di malware e far rispettare le policy di utilizzo accettabile.
- Ottimizza per il Tuo Ambiente: Adatta il tuo design RF e la strategia di segmentazione al tuo specifico tipo di sede. Leggi di più su Office Wi Fi: Ottimizza la Tua Moderna Rete Wi-Fi per Ufficio e comprendi l'impatto di Wi Fi Frequencies: Una Guida alle Frequenze Wi-Fi nel 2026 .
- LSfrutta gli Analytics: Utilizza WiFi Analytics per monitorare l'utilizzo dei segmenti e identificare comportamenti anomali.

Risoluzione dei Problemi e Mitigazione del Rischio
La modalità di errore più comune nelle implementazioni di micro-segmentazione è il routing inter-VLAN configurato in modo errato. Se una regola del firewall consente inavvertitamente il traffico tra i segmenti IoT e Corporate, la segmentazione è compromessa.
Errori Comuni:
- Esposizione dell'Interfaccia di Gestione: Lasciare le interfacce di gestione degli AP o degli switch accessibili dai segmenti guest o IoT. Il traffico di gestione deve risiedere su una VLAN dedicata, altamente ristretta e fuori banda.
- Guasti RADIUS: Un server RADIUS configurato in modo errato che rifiuta le autenticazioni 802.1X comporterà un guasto diffuso della connettività per i dispositivi aziendali. Implementare un'infrastruttura RADIUS ridondante.
- Routing Asimmetrico: Assicurarsi che i percorsi del traffico di ritorno siano definiti correttamente nelle policy del firewall per prevenire interruzioni delle connessioni.
ROI e Impatto sul Business
L'implementazione di una robusta micro-segmentazione offre un valore aziendale misurabile:
- Ambito di Conformità Ridotto: Isolando crittograficamente i terminali POS e i sistemi di pagamento, si riducono significativamente l'ambito e i costi degli audit PCI DSS.
- Mitigazione del Rischio: Contenere una potenziale violazione a un singolo segmento (ad esempio, un lettore di digital signage compromesso) previene movimenti laterali catastrofici nei sistemi aziendali centrali.
- Efficienza Operativa: L'assegnazione dinamica delle VLAN riduce il sovraccarico amministrativo della configurazione manuale delle porte degli switch e della gestione di più SSID statici.
Definizioni chiave
Micro-Segmentation
The practice of dividing a network into granular, isolated zones to enforce strict security policies and contain potential breaches.
Essential for venue operators running diverse device types (Guest, IoT, Staff) on a single physical network infrastructure.
IEEE 802.1X
A standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The engine for dynamic VLAN assignment and robust corporate device onboarding.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the access point or switch which VLAN a client should be placed in upon successful authentication.
Allows a single SSID to securely serve multiple user roles without static configuration.
Client Isolation
A wireless network feature that prevents connected clients from communicating directly with each other.
A mandatory configuration for any guest WiFi network to prevent peer-to-peer attacks and ensure privacy.
MAC Authentication Bypass (MAB)
A technique used to authenticate devices that do not support 802.1X by using their MAC address as the credential.
Commonly used to onboard headless IoT devices like smart TVs or sensors onto a segmented network.
EAP-TLS
Extensible Authentication Protocol-Transport Layer Security; a highly secure authentication method requiring client and server certificates.
The gold standard for authenticating corporate devices and POS systems to prevent credential theft.
WPA3-Enterprise
The latest WiFi security standard for enterprise networks, offering stronger encryption and robust authentication.
Should be mandated for all new deployments to protect sensitive corporate and staff traffic.
Quality of Service (QoS)
Technologies that manage data traffic to reduce packet loss, latency, and jitter on the network.
Used in conjunction with segmentation to ensure critical applications (like POS) are prioritized over guest or IoT traffic.
Esempi pratici
A 200-room hotel needs to deploy new smart TVs in every guest room, upgrade their POS systems in the restaurant, and provide high-speed guest WiFi, all on the existing physical network infrastructure. How should they architect the segmentation?
- Implement three distinct VLANs: Guest (VLAN 10), IoT (VLAN 20), and Corporate/POS (VLAN 30).
- Configure the APs to broadcast two SSIDs: 'Hotel_Guest' (Open with Captive Portal, mapped to VLAN 10) and 'Hotel_Secure' (802.1X).
- Enable Client Isolation on the 'Hotel_Guest' SSID.
- Use MAC-based RADIUS authentication (MAB) for the Smart TVs to dynamically assign them to VLAN 20.
- Use EAP-TLS certificate authentication for the POS terminals to assign them to VLAN 30.
- Configure the perimeter firewall to deny all inter-VLAN traffic, permitting VLAN 10 and 20 internet-only access, and restricting VLAN 30 to the corporate VPN tunnel.
A large retail chain is experiencing network congestion and suspects their digital signage media players (IoT) are saturating the uplink, impacting the performance of their mobile POS tablets.
- Audit the current network configuration to confirm if digital signage and POS tablets share the same segment.
- Implement micro-segmentation by moving the digital signage players to a dedicated IoT VLAN.
- Apply Quality of Service (QoS) policies at the access switch or AP level: rate-limit the IoT VLAN to 5 Mbps per device, and prioritize traffic from the POS VLAN.
- Ensure the IoT VLAN has a strict egress-only firewall policy to the specific content delivery network (CDN) used by the signage vendor.
Domande di esercitazione
Q1. You are deploying a new WiFi network for a large conference centre. The venue requires a public guest network, a dedicated network for AV equipment (projectors, digital signage), and a secure network for venue staff. You have been instructed to minimize the number of broadcasted SSIDs. How do you architect the wireless access layer?
Suggerimento: Consider how different device types authenticate and how RADIUS can dynamically assign VLANs.
Visualizza risposta modello
Broadcast two SSIDs. SSID 1 ('Conference_Guest'): Open network with a captive portal for guest access, mapped to a Guest VLAN with client isolation and internet-only firewall rules. SSID 2 ('Conference_Secure'): 802.1X enabled. Venue staff authenticate via EAP-TLS (certificates) and are dynamically assigned to the Staff VLAN. AV equipment authenticates via MAC Authentication Bypass (MAB) against the RADIUS server and is dynamically assigned to the isolated AV/IoT VLAN.
Q2. During a security audit, a penetration tester successfully compromises a smart thermostat in the hotel lobby. From the thermostat, they are able to access the hotel's reservation database server. What architectural failure allowed this, and how should it be remediated?
Suggerimento: Consider inter-VLAN routing policies and the principle of least privilege.
Visualizza risposta modello
The architectural failure is a lack of micro-segmentation and permissive inter-VLAN routing. The IoT device (thermostat) was either placed on the same VLAN as the corporate servers, or the firewall separating the VLANs allowed inbound traffic from the IoT segment to the corporate segment. Remediation: Move all thermostats to a dedicated IoT VLAN. Configure the perimeter firewall with a default-deny policy between VLANs. The IoT VLAN should only be permitted egress traffic to the specific cloud controller required for the thermostats, with no access to internal corporate resources.
Q3. A retail client complains that their guest WiFi is extremely slow during peak hours, and they notice that the POS systems are also experiencing latency. Both are running on the same physical access points. What is the most likely cause, and what are the recommended steps to resolve it?
Suggerimento: Think about bandwidth contention and traffic prioritization.
Visualizza risposta modello
The likely cause is bandwidth contention on the shared uplink, with guest traffic saturating the connection and impacting critical POS traffic. Resolution: Implement Quality of Service (QoS) and rate-limiting. 1. Ensure POS and Guest traffic are on separate VLANs. 2. Apply a rate-limit policy to the Guest VLAN (e.g., 5 Mbps per client) to prevent any single guest from hogging bandwidth. 3. Configure QoS rules on the switch and firewall to prioritize traffic originating from the POS VLAN over the Guest VLAN.