eduroam e 802.1X: Autenticazione WiFi sicura per l'istruzione superiore
Questa guida tecnica di riferimento autorevole spiega l'architettura, l'implementazione e la sicurezza dell'autenticazione eduroam e 802.1X. Progettata per i responsabili IT e gli architetti di rete, copre i passaggi pratici di implementazione, la selezione del metodo EAP e come gli operatori delle sedi possono supportare in modo sicuro il roaming accademico.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Riepilogo Esecutivo
- Approfondimento Tecnico: 802.1X e l'Architettura eduroam
- Il Triangolo 802.1X
- La Gerarchia Proxy RADIUS di eduroam
- Metodi EAP: Sicurezza vs. Implementabilità
- Guida all'Implementazione
- 1. Preparazione dell'Infrastruttura
- 2. Gestione dei Certificati
- 3. Configurazione del client (Lo strumento CAT)
- 4. Assegnazione e segmentazione VLAN
- Migliori pratiche e raccomandazioni indipendenti dal fornitore
- Risoluzione dei problemi e mitigazione dei rischi
- ROI e impatto aziendale

Riepilogo Esecutivo
Per le istituzioni di istruzione superiore e le sedi che ospitano i loro studenti e personale, fornire connettività wireless sicura e senza interruzioni non è più un lusso, ma un mandato operativo. Lo standard per questa connettività è eduroam, un servizio di roaming globale basato sul framework IEEE 802.1X.
Questa guida fornisce a responsabili IT, architetti di rete e direttori delle operazioni delle sedi un riferimento completo e indipendente dal fornitore per comprendere, implementare e risolvere i problemi di 802.1X e eduroam. Andiamo oltre i modelli teorici di base per affrontare le realtà pratiche del WiFi aziendale, inclusa la gestione dei certificati, l'architettura proxy RADIUS e l'integrazione con strategie di rete ospiti più ampie.
Sia che si stia aggiornando una rete universitaria obsoleta o configurando un centro congressi per supportare i visitatori accademici, l'implementazione corretta di 802.1X mitiga significativi rischi per la sicurezza, in particolare il furto di credenziali, riducendo drasticamente il carico di supporto. Per le sedi al di fuori dell'istruzione superiore tradizionale, comprendere questi standard è fondamentale per valutare le federazioni di roaming commerciali come OpenRoaming, che condividono la stessa architettura sottostante.
Approfondimento Tecnico: 802.1X e l'Architettura eduroam
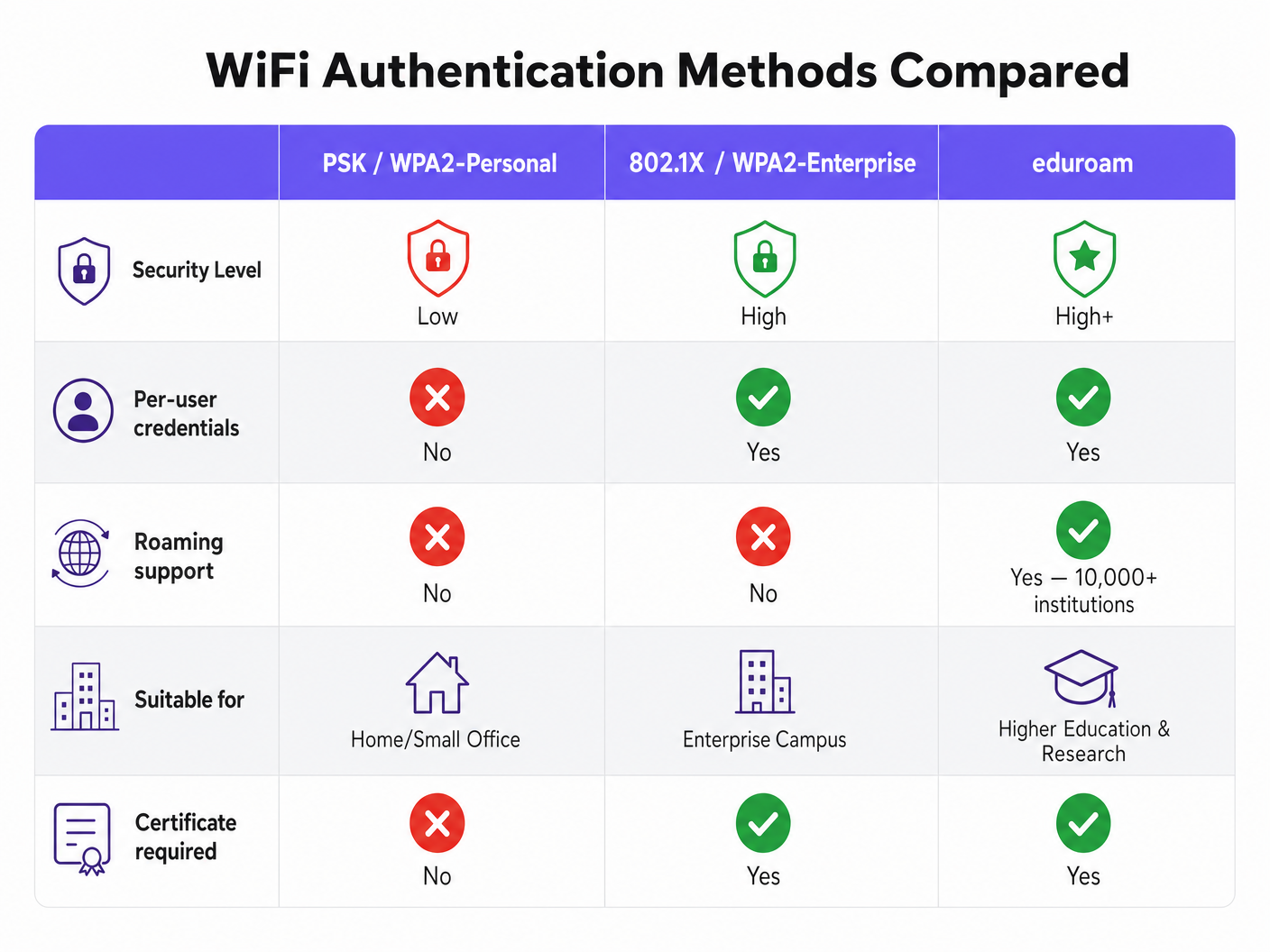
Al suo nucleo, eduroam è un'implementazione di IEEE 802.1X, lo standard per il controllo dell'accesso alla rete basato su porta. Sebbene originariamente progettato per reti cablate, 802.1X costituisce la base della sicurezza WPA2-Enterprise e WPA3-Enterprise.
Il Triangolo 802.1X
Il framework 802.1X si basa su tre componenti distinti che interagiscono per autorizzare l'accesso:
- Supplicant: Il dispositivo client (ad esempio, il laptop o lo smartphone di uno studente) che richiede l'accesso alla rete.
- Autenticatore: Il dispositivo di accesso alla rete (ad esempio, un access point wireless o uno switch gestito). Agisce come un guardiano, bloccando tutto il traffico eccetto i messaggi di autenticazione finché il dispositivo non è autorizzato.
- Server di Autenticazione: Il sistema backend che convalida le credenziali, quasi universalmente un server RADIUS (Remote Authentication Dial-In User Service).
Quando un dispositivo si connette, l'Autenticatore stabilisce una porta controllata. Passa i messaggi del Protocollo di Autenticazione Estensibile (EAP) tra il Supplicant e il Server di Autenticazione. Se le credenziali sono valide, il server restituisce un messaggio RADIUS Access-Accept, e l'Autenticatore apre la porta per il traffico IP standard.
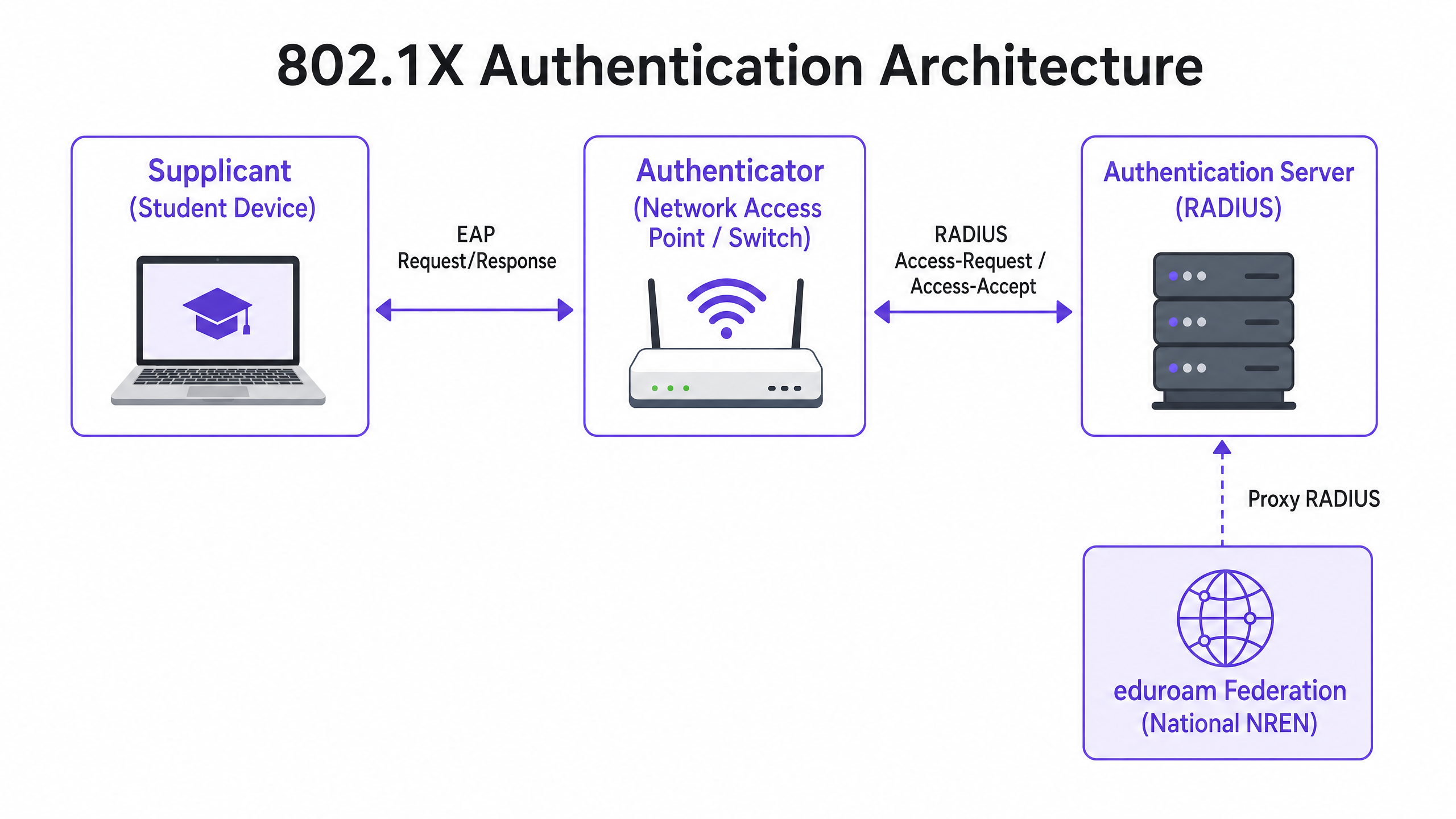
La Gerarchia Proxy RADIUS di eduroam
Ciò che rende eduroam unico è la sua architettura federata. Permette agli utenti di autenticarsi presso qualsiasi istituzione partecipante utilizzando le proprie credenziali di casa, senza che l'istituzione ospitante abbia bisogno di una copia di tali credenziali.
Questo si ottiene tramite una catena proxy RADIUS gerarchica. Quando un utente da username@university.ac.uk si connette all'SSID eduroam in una sede ospitante:
- Il dispositivo dell'utente invia una richiesta di autenticazione nel formato
username@university.ac.uk. - Il server RADIUS della sede ospitante esamina il realm (la parte dopo la
@). Riconoscendolo come un dominio esterno, inoltra la richiesta al server RADIUS nazionale di primo livello (gestito dalla National Research and Education Network, o NREN). - Il server nazionale instrada la richiesta al server RADIUS dell'istituzione di origine (
university.ac.uk). - L'istituzione di origine convalida le credenziali e restituisce un messaggio
Access-AcceptoAccess-Rejectlungo la catena.
L'intero processo si completa tipicamente in meno di due secondi. Fondamentalmente, la password dell'utente non viene mai esposta all'istituzione ospitante o ai proxy intermedi; è protetta all'interno di un tunnel EAP crittografato stabilito direttamente tra il supplicant e il server RADIUS di origine.
Metodi EAP: Sicurezza vs. Implementabilità
La scelta del metodo EAP determina come viene formato il tunnel crittografato e come vengono scambiate le credenziali. La definizione del servizio di policy eduroam limita fortemente i metodi consentiti per garantire la sicurezza.
- PEAP (Protected EAP): L'implementazione più comune. Stabilisce un tunnel TLS utilizzando un certificato lato server sul server RADIUS. Il client si autentica quindi all'interno di questo tunnel, tipicamente utilizzando MSCHAPv2 (nome utente e password). È relativamente facile da implementare ma vulnerabile ad attacchi da access point non autorizzati se i client non sono configurati per convalidare rigorosamente il certificato del server.
- EAP-TLS: Lo standard d'oro per la sicurezza. Richiede l'autenticazione reciproca, il che significa che sia il server RADIUS che il dispositivo client devono presentare certificati validi. Sebbene immune al phishing delle credenziali, richiede una robusta Infrastruttura a Chiave Pubblica (PKI) per emettere e gestire i certificati client, rendendone più complessa l'implementazione su larga scala.
Guida all'Implementazione
L'implementazione di 802.1X e eduroam richiede un'attenta coordinazione tra infrastruttura di rete, gestione delle identità e configurazione del client.
1. Preparazione dell'Infrastruttura
Assicurati che i tuoi access point wireless e i controller supportino WPA2-Enterprise/WPA3-Enterprise e 802.1X. Qualsiasi hardware moderno di livello enterprise (Cisco, Aruba, Juniper, ecc.) soddisferà questo requisito. Devi anche implementare un'infrastruttura RADIUS robusta (ad esempio, FreeRADIUS, Cisco ISE, Aruba ClearPass) in grado di gestire il carico di autenticazione previsto e di inoltrare le richieste.
2. Gestione dei Certificati
Per le implementazioni PEAP, il tuo server RADIUS richiede un certificato TLS emesso da un'Autorità di Certificazione (CA) fidata dai tuoi client. Non utilizzarecertificati autofirmati per le implementazioni eduroam in produzione. Il certificato deve essere regolarmente rinnovato per prevenire interruzioni dell'autenticazione.
3. Configurazione del client (Lo strumento CAT)
Il punto di errore più comune nelle implementazioni eduroam è la configurazione errata del client. Gli utenti che si connettono manualmente spesso non riescono a configurare la convalida del certificato, rendendoli vulnerabili alla raccolta di credenziali.
Per mitigare ciò, le istituzioni devono utilizzare l'eduroam Configuration Assistant Tool (CAT) o una soluzione MDM per distribuire profili preconfigurati. Questi profili configurano automaticamente il metodo EAP corretto, bloccano il certificato del server RADIUS previsto e impostano i protocolli di autenticazione interni appropriati.
4. Assegnazione e segmentazione VLAN
Un'implementazione matura utilizza gli attributi RADIUS per assegnare dinamicamente le VLAN in base all'identità dell'utente.
- Utenti interni: Assegnati a VLAN interne con accesso appropriato alle risorse del campus.
- Utenti in visita: Assegnati a una VLAN guest ristretta con accesso solo a Internet.
Questa segmentazione è vitale per la sicurezza e la conformità, garantendo che i dispositivi in visita non possano accedere a reti interne sensibili.
Migliori pratiche e raccomandazioni indipendenti dal fornitore
- Dare priorità a WPA3: Per le nuove implementazioni, abilitare WPA3-Enterprise per beneficiare della crittografia obbligatoria a 192 bit e di una migliore protezione contro gli attacchi a dizionario offline.
- Imporre la convalida del certificato: Rendere obbligatorio l'uso di profili di configurazione (tramite CAT o MDM) per garantire che i supplicanti convalidino rigorosamente il certificato del server RADIUS prima di trasmettere le credenziali.
- Utilizzare RadSec: Quando si configurano le connessioni proxy RADIUS alla federazione nazionale, utilizzare RadSec (RADIUS over TLS) anziché UDP semplice. Ciò crittografa il traffico proxy e migliora l'affidabilità sui collegamenti WAN.
- Integrare con soluzioni Guest: eduroam serve solo utenti con credenziali accademiche. È necessario mantenere una soluzione Guest WiFi separata e sicura per appaltatori, visitatori pubblici e partecipanti a eventi.
- Rivedere l'infrastruttura correlata: Assicurarsi che la rete sottostante sia sicura. Leggere la nostra guida su Proteggi la tua rete con DNS e sicurezza robusti per maggiori dettagli. Se si implementa un'infrastruttura temporanea per eventi universitari, consultare Event WiFi: Pianificazione e implementazione di reti wireless temporanee o la versione portoghese Event WiFi: Planeamento e Implementação de Redes Sem Fios Temporárias .
Risoluzione dei problemi e mitigazione dei rischi
Quando l'autenticazione fallisce, la risoluzione sistematica dei problemi è essenziale.
- Isolare il dominio di errore: Determinare se l'errore è locale (che interessa i propri utenti sulla propria rete), remoto (che interessa i propri utenti altrove) o in entrata (che interessa i visitatori sulla propria rete).
- Controllare i log RADIUS: I log del server RADIUS sono la fonte definitiva di verità. Cercare messaggi
Access-Reject(che indicano credenziali errate o violazioni delle policy) o timeout (che indicano problemi di connettività proxy). - Verificare la validità del certificato: Assicurarsi che il certificato del server RADIUS non sia scaduto e che l'intera catena di certificati sia presentata al client.
- Monitorare la latenza upstream: Un'elevata latenza sulla connessione al proxy RADIUS nazionale può causare timeout del client, con conseguenti connessioni fallite anche con credenziali corrette.
ROI e impatto aziendale
Per le istituzioni di istruzione superiore, il ROI di un'implementazione eduroam adeguata si misura in una drastica riduzione dei ticket di supporto. Eliminando i captive portal e l'inserimento manuale delle password, gli helpdesk IT registrano un calo significativo delle chiamate relative alla connettività. (L'impegno di Purple in questo settore è evidente; vedi Purple Signals Higher Education Ambitions with Appointment of VP Education Tim Peers ).
Per le sedi commerciali, come quelle in Ospitalità , Vendita al dettaglio , Sanità o Trasporti , il supporto di eduroam Visitor Access (eVA) o federazioni simili come OpenRoaming offre un'esperienza senza attriti per demografie di alto valore. Garantisce che i visitatori accademici possano connettersi automaticamente e in modo sicuro, migliorando la soddisfazione e consentendo alla sede di mantenere una rigorosa segmentazione della rete. Se la tua sede richiede una larghezza di banda dedicata per supportare questo, considera di leggere Cos'è una linea dedicata? Internet aziendale dedicato .
Quando si pianificano gli aggiornamenti di rete, l'integrazione delle capacità 802.1X garantisce che l'infrastruttura sia pronta per il networking moderno basato sull'identità, ponendo le basi per WiFi Analytics avanzati e servizi basati sulla posizione.
GuidesSlugPage.keyDefinitionsTitle
802.1X
An IEEE standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enterprise-grade WiFi security, replacing shared passwords (PSKs) with individualised authentication.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend server in an 802.1X deployment that actually checks the user's credentials against a directory (like Active Directory).
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections. It provides for the transport and usage of various authentication mechanisms.
The language spoken between the client device and the RADIUS server during the 802.1X handshake.
Supplicant
The client device (e.g., laptop, smartphone) or the software on that device attempting to authenticate to a network using 802.1X.
The entity requesting access. Its configuration (especially regarding certificate validation) is critical for security.
Authenticator
The network device (e.g., wireless access point, Ethernet switch) that facilitates the 802.1X authentication process by passing messages between the Supplicant and the Authentication Server.
The gatekeeper that blocks network traffic until the RADIUS server gives the green light.
PEAP (Protected Extensible Authentication Protocol)
An EAP method that encapsulates the EAP transaction within a TLS tunnel established using a server-side certificate, protecting the inner authentication (usually a password).
The most common authentication method for eduroam, balancing security with ease of deployment.
RadSec
A protocol for transmitting RADIUS data over TCP and TLS, rather than the traditional UDP.
Recommended for securing the proxy connections between institutions and the national eduroam federation, preventing interception of authentication traffic.
Realm
The portion of a user's identity following the '@' symbol (e.g., 'university.ac.uk' in 'user@university.ac.uk').
Used by RADIUS proxy servers to determine where to route the authentication request in a federated environment like eduroam.
GuidesSlugPage.workedExamplesTitle
A 400-room conference hotel adjacent to a major university frequently hosts academic symposiums. The IT Director wants to allow visiting academics to connect automatically without using the hotel's standard captive portal, but must ensure these visitors cannot access the hotel's corporate network or the standard guest network VLAN.
The hotel should implement eduroam Visitor Access (eVA) or join a commercial federation like OpenRoaming.
- The hotel configures a new SSID ('eduroam' or 'OpenRoaming') on their enterprise access points.
- The APs are configured to use WPA2-Enterprise/802.1X.
- The hotel deploys a local RADIUS server configured to proxy authentication requests for external realms to the national federation (for eduroam) or the OpenRoaming hub.
- Crucially, the local RADIUS server is configured to return a specific VLAN ID attribute in the
Access-Acceptmessage for all proxied authentications. - The access points place these authenticated users onto an isolated, internet-only VLAN, completely segmented from the hotel's corporate and standard guest traffic.
A university IT team notices a spike in compromised student accounts. Investigation reveals that students are connecting to a rogue access point broadcasting the 'eduroam' SSID at a local coffee shop. The rogue AP is using a self-signed certificate to harvest credentials via PEAP.
The IT team must immediately enforce strict certificate validation on all client devices.
- They must stop advising students to manually connect to the SSID and 'accept the certificate warning'.
- They deploy the eduroam Configuration Assistant Tool (CAT) for BYOD devices and update MDM profiles for managed devices.
- These profiles configure the supplicant to only trust the specific Certificate Authority (CA) that issued the university's RADIUS server certificate, and to verify the server's Common Name (CN).
- Once configured, if a student's device encounters the rogue AP, the EAP tunnel establishment will fail because the rogue certificate does not match the pinned CA/CN, preventing the transmission of credentials.
A retail chain wants to offer OpenRoaming across 50 locations using their existing guest WiFi infrastructure, which currently relies on an open SSID with a captive portal.
The retail chain must upgrade their network to support 802.1X and RADIUS proxying.
- The network team enables a new SSID broadcasting the OpenRoaming Consortium OI (Organization Identifier).
- They configure the access points to authenticate via 802.1X.
- They configure their central RADIUS server to proxy requests to the OpenRoaming federation hub.
- They ensure their internet backhaul can support the expected increase in automated connections, potentially upgrading to dedicated leased lines if necessary.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your university is deploying a new wireless network. The CISO mandates that credential phishing via rogue access points must be mathematically impossible. Which EAP method must you select?
GuidesSlugPage.hintPrefixConsider which method relies on passwords versus which relies entirely on cryptographic keys.
GuidesSlugPage.viewModelAnswer
You must select EAP-TLS. Unlike PEAP, which relies on a password inside a TLS tunnel, EAP-TLS requires mutual certificate authentication. Because the client device authenticates using a cryptographic certificate rather than a password, there are no credentials for a rogue access point to phish.
Q2. A visiting researcher from another university complains they cannot connect to your eduroam network. Your local users are connecting fine. You check your local RADIUS server logs and see the request arriving, but it times out before an Access-Accept is received. What is the most likely cause?
GuidesSlugPage.hintPrefixThink about the path the authentication request takes for a visiting user versus a local user.
GuidesSlugPage.viewModelAnswer
The most likely cause is a connectivity or latency issue between your local RADIUS server and the national NREN RADIUS proxy. Because local users authenticate directly against your server, they are unaffected. The visiting user's request must be proxied upstream, and a timeout indicates the response from the home institution is not returning in time.
Q3. You are a network architect for a retail chain located near a large university. You want to offer seamless WiFi to students using eduroam Visitor Access (eVA), but you must comply with PCI DSS for your point-of-sale terminals. How do you securely integrate eVA?
GuidesSlugPage.hintPrefixHow does 802.1X allow the network access point to differentiate traffic after authentication?
GuidesSlugPage.viewModelAnswer
You integrate eVA by configuring your RADIUS server to assign all successful eVA authentications to a dedicated, internet-only guest VLAN. The Access-Accept message from the RADIUS server must include the specific VLAN ID. This ensures student devices are completely segmented from the PCI-compliant VLAN used by the point-of-sale terminals, satisfying compliance requirements.



