Migliorare la visibilità della rete con l'integrazione NAC e MDM
Questa guida di riferimento tecnico illustra l'architettura, l'integrazione e l'impatto aziendale della combinazione di Network Access Control (NAC) con Mobile Device Management (MDM). Fornisce indicazioni pratiche per la distribuzione a IT manager e architetti di rete che operano in ambienti complessi multiuso come hospitality, retail e luoghi pubblici.
Listen to this guide
View podcast transcript
- Riepilogo Esecutivo
- Approfondimento Tecnico: Architettura e Standard
- Il Livello di Applicazione: Network Access Control (NAC)
- Il Livello di Visibilità: Integrazione MDM e Valutazione della Postura
- Gestione dei Dispositivi Non Gestiti: Guest e IoT
- Guida all'Implementazione
- Fase 1: Scoperta e Tassonomia dei Dispositivi
- Fase 2: Integrazione MDM in Sola Lettura
- Fase 3: Applicazione dell'accesso basato sulla postura
- Fase 4: Segmentazione per ospiti e IoT
- Best Practice
- Risoluzione dei problemi e mitigazione del rischio
- ROI e impatto sul business
Riepilogo Esecutivo
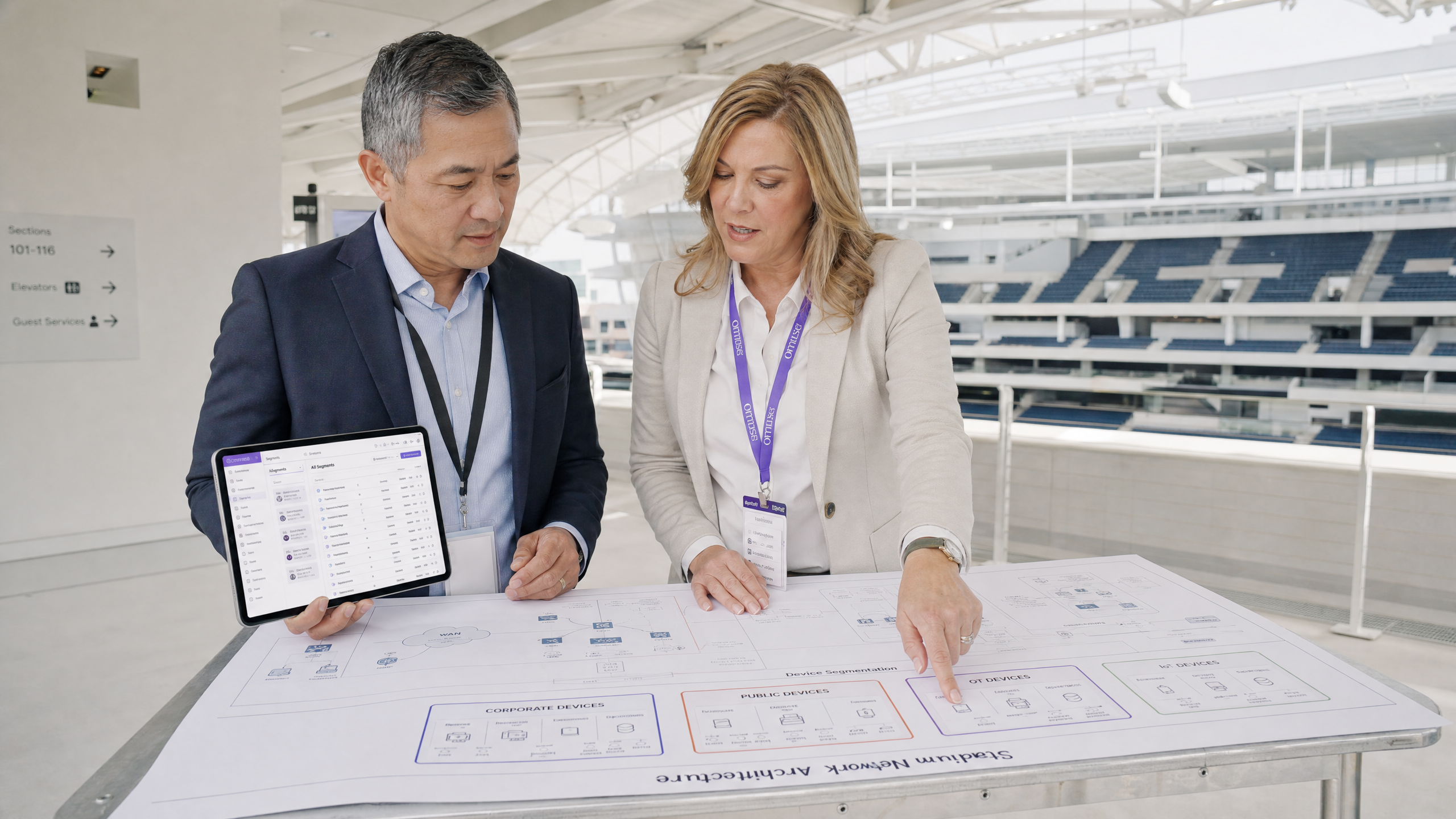
Per i team IT aziendali che gestiscono grandi strutture fisiche — che si tratti di un hotel di 500 camere, di un grande stadio o di una catena di negozi al dettaglio nazionale — il perimetro della rete si è dissolto. L'infrastruttura di rete fisica odierna veicola un mix volatile di endpoint aziendali, smartphone BYOD, dispositivi guest non gestiti, terminali di pagamento e una flotta in rapida espansione di sensori IoT headless. Operare in questi ambienti senza una visibilità di rete granulare e in tempo reale rappresenta un significativo rischio di compliance e sicurezza.
Questa guida fornisce un progetto tecnico per migliorare la visibilità della rete con l'integrazione NAC e MDM. Colmando il divario tra identità, postura del dispositivo e controllo degli accessi alla rete, gli architetti IT possono passare da assegnazioni VLAN statiche a segmentazioni dinamiche basate sulla postura. Esploreremo l'architettura tecnica necessaria per raggiungere questo obiettivo, i punti di integrazione con piattaforme di autenticazione guest come Guest WiFi e i passaggi pratici di implementazione necessari per proteggere ambienti multiuso senza interrompere le operazioni.
Approfondimento Tecnico: Architettura e Standard
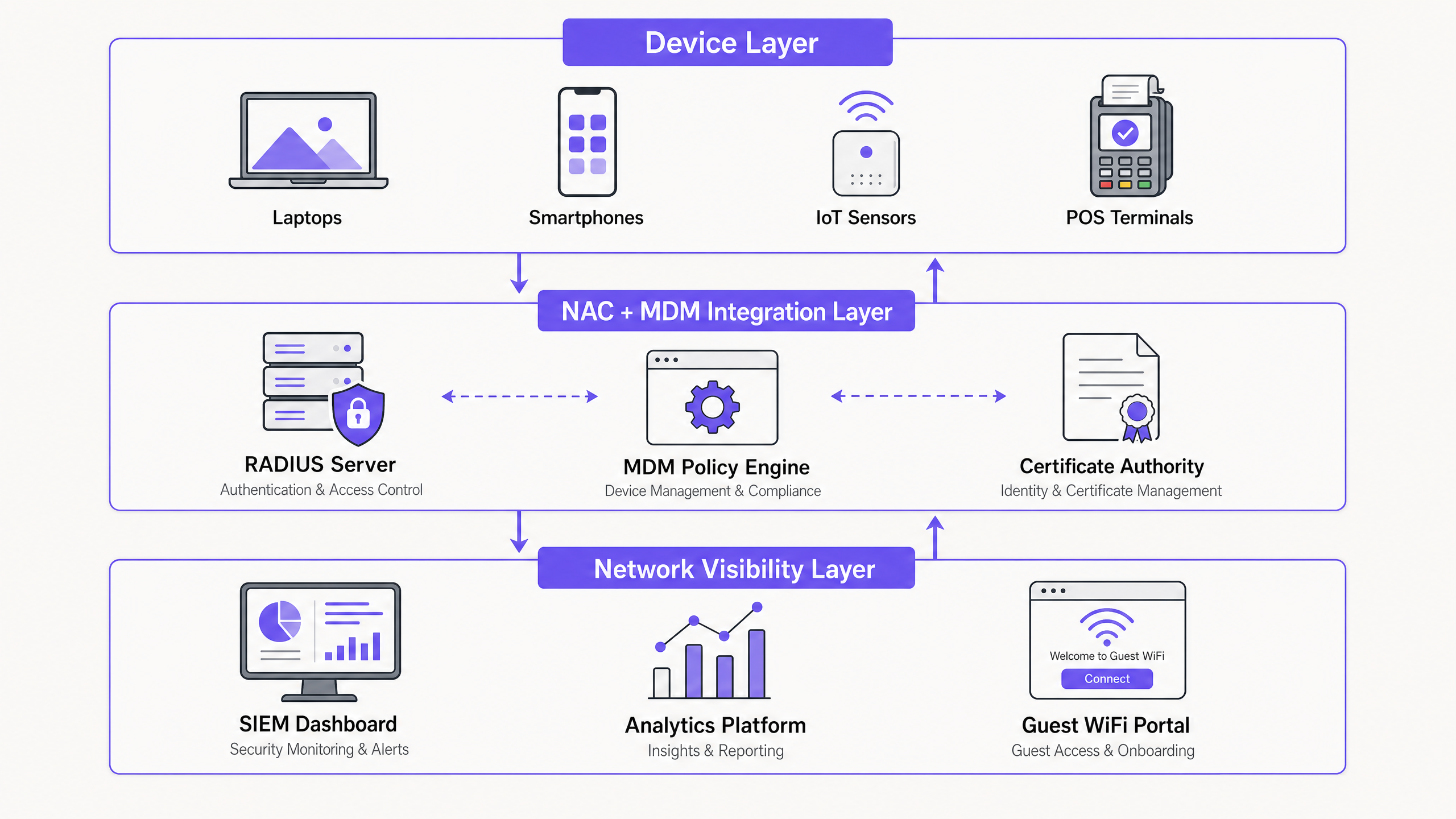
La visibilità della rete richiede fondamentalmente di rispondere a tre domande in tempo reale: Cosa si sta connettendo? Chi ne è il proprietario? È conforme? Rispondere a queste domande richiede un'architettura integrata che comprenda il bordo della rete, il provider di identità e la piattaforma di gestione dei dispositivi.
Il Livello di Applicazione: Network Access Control (NAC)
Al centro dell'architettura c'è il sistema Network Access Control (NAC), che funge da Policy Decision Point (PDP). Lo standard di settore per una robusta implementazione NAC rimane IEEE 802.1X, che utilizza un server RADIUS per autenticare i supplicanti prima di concedere l'accesso alla rete.
Quando un endpoint aziendale tenta di associarsi a un access point o di autenticarsi a una porta switch, il framework 802.1X trasporta in modo sicuro le credenziali del dispositivo (tipicamente tramite EAP-TLS utilizzando certificati digitali) al server RADIUS. Il server RADIUS valuta queste credenziali rispetto a una matrice di policy definita per determinare il segmento di rete appropriato, assegnando dinamicamente la VLAN tramite attributi RADIUS.
Tuttavia, 802.1X da solo verifica solo l'identità; non verifica la postura di sicurezza dell'endpoint. È qui che l'integrazione MDM diventa fondamentale.
Il Livello di Visibilità: Integrazione MDM e Valutazione della Postura
Le piattaforme Mobile Device Management (MDM) (ad esempio, Microsoft Intune, Jamf, Workspace ONE) mantengono un inventario continuo dei dispositivi gestiti, monitorando le versioni del OS, i livelli di patch, le applicazioni installate e gli stati generali di compliance.
L'integrazione tra NAC e MDM avviene tipicamente tramite API REST. Quando un dispositivo si autentica tramite 802.1X, il sistema NAC intercetta la richiesta di autenticazione e interroga la piattaforma MDM utilizzando l'indirizzo MAC o l'identità del certificato del dispositivo. La piattaforma MDM restituisce la postura di compliance in tempo reale del dispositivo.
Se l'MDM segnala il dispositivo come conforme, il sistema NAC autorizza l'accesso alla corporate VLAN. Se il dispositivo non è conforme (ad esempio, mancano aggiornamenti critici del OS o è in esecuzione software non autorizzato), il sistema NAC assegna dinamicamente il dispositivo a una remediation VLAN con routing limitato, consentendo al dispositivo di raggiungere solo il server MDM o i server di aggiornamento per auto-ripararsi.
Gestione dei Dispositivi Non Gestiti: Guest e IoT
La sfida principale in ambienti come Hospitality e Retail è l'enorme volume di dispositivi non gestiti. Questi endpoint non possono partecipare all'autenticazione 802.1X o all'iscrizione MDM.
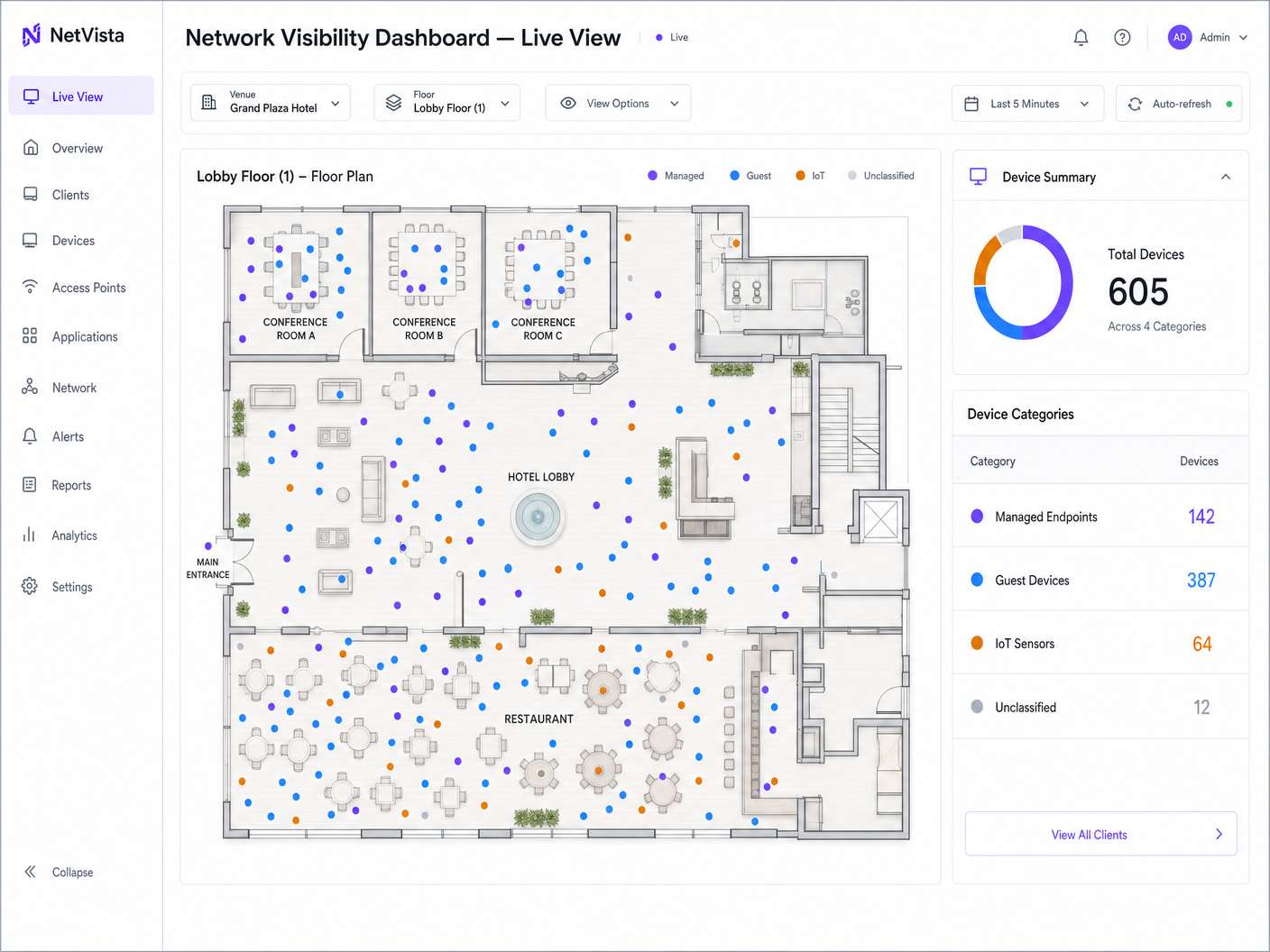
Guest Devices: Per i guest devices non gestiti, la visibilità è ottenuta tramite un'architettura captive portal. Piattaforme come WiFi Analytics di Purple intercettano la richiesta HTTP/HTTPS iniziale, reindirizzando l'utente a un portale di autenticazione. Questo livello cattura l'identità dell'utente, applica i termini di servizio e gestisce il consenso in conformità con il GDPR. Il guest viene quindi collocato su una guest VLAN isolata, fisicamente o logicamente separata dal traffico aziendale.
IoT Endpoints: I dispositivi headless come i controller HVAC, la segnaletica digitale e i terminali POS si basano tipicamente sul MAC Authentication Bypass (MAB). Poiché gli indirizzi MAC sono facilmente spoofabili, il MAB deve essere combinato con una profilazione approfondita del dispositivo. I moderni sistemi NAC analizzano le impronte digitali DHCP, gli user agent HTTP e i modelli di comportamento del traffico per classificare accuratamente i dispositivi IoT e assegnarli a IoT VLAN fortemente limitate e micro-segmentate.
Guida all'Implementazione
La distribuzione di un'architettura integrata NAC e MDM richiede un approccio graduale e metodico per evitare interruzioni operative diffuse.
Fase 1: Scoperta e Tassonomia dei Dispositivi
Prima di configurare qualsiasi policy di applicazione, è necessario stabilire una baseline completa dello stato attuale della rete. Distribuire il sistema NAC in "Monitor Mode" (spesso utilizzando porte SPAN o dati NetFlow) per osservare passivamente il traffico e catalogare ogni endpoint connesso.
Sviluppare una tassonomia rigorosa dei dispositivi. Definire categorie distinte: Corporate Managed, BYOD, Guest, IoT (sottocategorizzato per funzione) e Contractor. Ogni categoria deve essere mappata a un metodo di autenticazione, un set di policy e una target VLAN specifici.
Fase 2: Integrazione MDM in Sola Lettura
Integrare il sistema NAC con l'API MDM, ma configurareriguardo alle policy per registrare i fallimenti di conformità senza imporre la quarantena. Questa fase di sola lettura è critica. Nelle implementazioni aziendali, il controllo iniziale della postura rivela frequentemente un'alta percentuale di dispositivi non conformi a causa di cicli di patch ritardati o problemi di sincronizzazione dei certificati. L'applicazione dei controlli di postura prima di comprendere questa baseline si tradurrà in un denial of service auto-inflitto. Utilizzare questa fase per rimediare alla baseline attraverso processi IT standard.
Fase 3: Applicazione dell'accesso basato sulla postura
Una volta che la baseline di conformità è stabile, passare le policy aziendali dalla modalità di monitoraggio a quella di applicazione. Iniziare con un gruppo pilota di utenti IT prima di estendere l'implementazione all'intera organizzazione. Assicurarsi che la VLAN di remediation sia correttamente instradata per consentire l'accesso alla piattaforma MDM e ai server di aggiornamento necessari, ma strettamente protetta da firewall rispetto alle risorse interne.
Fase 4: Segmentazione per ospiti e IoT
Implementare il portale di autenticazione per gli ospiti e la profilazione MAB per l'IoT. Per gli ambienti soggetti a PCI DSS, assicurarsi che la VLAN del terminale POS sia completamente isolata dai segmenti ospiti e aziendali. Convalidare la segmentazione utilizzando strumenti di penetration testing automatizzati per confermare che il routing tra VLAN sia esplicitamente negato.
Best Practice
- Dare priorità all'autenticazione basata su certificati (EAP-TLS): Affidarsi a nomi utente e password per 802.1X (PEAP-MSCHAPv2) è sempre più vulnerabile al furto di credenziali. Implementare un'infrastruttura PKI robusta e utilizzare la piattaforma MDM per il provisioning automatico dei certificati macchina e utente agli endpoint gestiti.
- Implementare WPA3-Enterprise: Quando si implementa una nuova infrastruttura wireless, imporre WPA3-Enterprise. La modalità di sicurezza a 192 bit offre miglioramenti crittografici che proteggono lo scambio di autenticazione dagli attacchi a dizionario offline. Per maggiori informazioni sugli standard wireless moderni, fare riferimento alla nostra guida su Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 .
- Unificare la visibilità in un SIEM: La visibilità della rete è utilizzabile solo se centralizzata. Inoltrare tutti i log di autenticazione NAC, gli eventi di conformità MDM e le analisi guest WiFi a una piattaforma centrale di Security Information and Event Management (SIEM). Ciò consente la correlazione tra il comportamento della rete, la postura del dispositivo e la posizione fisica (sfruttando Indoor WiFi Positioning Systems: How They Work and How to Deploy Them ).
Risoluzione dei problemi e mitigazione del rischio
- Modalità di fallimento: API Rate Limiting: Ambienti ad alta densità (come uno stadio in giorno di partita) possono generare migliaia di autenticazioni simultanee. Se il sistema NAC interroga l'API MDM per ogni richiesta, potrebbe attivare limiti di frequenza (rate limits), causando il fallimento delle autenticazioni in modalità fail open o fail closed.
- Mitigazione: Implementare il caching sul sistema NAC per lo stato della postura MDM, tipicamente memorizzando il risultato per 15-30 minuti, o utilizzare notifiche push basate su webhook dall'MDM al NAC per cambiamenti di stato in tempo reale.
- Modalità di fallimento: Scadenza del certificato: Un certificato CA root o intermedio scaduto invaliderà istantaneamente tutte le autenticazioni EAP-TLS, bloccando tutti i dispositivi gestiti fuori dalla rete.
- Mitigazione: Implementare un monitoraggio e un sistema di allerta aggressivi per l'infrastruttura PKI. Assicurarsi che le policy di auto-enrollment nell'MDM funzionino e che i dispositivi si connettano regolarmente.
- Modalità di fallimento: MAB Spoofing: Un attaccante clona l'indirizzo MAC di una stampante autorizzata per ottenere accesso alla VLAN interna.
- Mitigazione: Non affidarsi esclusivamente a MAB. Implementare la profilazione degli endpoint che monitora continuamente il comportamento del dispositivo. Se una "stampante" avvia improvvisamente una connessione SSH o esegue una scansione Nmap, il sistema NAC deve rilevare l'anomalia e mettere immediatamente in quarantena la porta.
ROI e impatto sul business
Il business case per l'integrazione di NAC e MDM va oltre la conformità alla sicurezza. Il principale ritorno sull'investimento si realizza attraverso la mitigazione del rischio e l'efficienza operativa.
Automatizzando l'onboarding dei dispositivi e l'applicazione della postura, gli helpdesk IT registrano una significativa riduzione dei ticket relativi all'accesso alla rete e alla remediation della conformità. Da una prospettiva di sicurezza, la segmentazione dinamica riduce drasticamente il raggio d'azione di un endpoint compromesso, abbassando il costo potenziale e l'impatto operativo di una violazione.
Inoltre, in luoghi pubblici come hub di Transport o centri commerciali, separare la complessa infrastruttura aziendale e IoT dall'esperienza degli ospiti garantisce che i servizi per gli ospiti rimangano altamente disponibili e performanti, supportando obiettivi di business più ampi legati all'engagement dei clienti e all'acquisizione di dati.
Key Definitions
Network Access Control (NAC)
A security solution that enforces policy on devices attempting to access a network, acting as the gatekeeper to ensure only authorized and compliant devices connect.
IT teams deploy NAC to prevent unauthorized devices from plugging into switch ports or connecting to corporate SSIDs.
Mobile Device Management (MDM)
Software used by IT departments to monitor, manage, and secure employees' mobile devices, laptops, and tablets across multiple operating systems.
MDM is the source of truth for device compliance, telling the network whether a device is patched and secure.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
This is the underlying protocol that allows a laptop to securely present its certificate to the network infrastructure.
MAC Authentication Bypass (MAB)
A fallback authentication method for devices that do not support 802.1X (like printers or IoT sensors), using the device's MAC address as its identity.
Crucial for venue operations where headless IoT devices must connect to the network without user intervention.
Device Profiling
The process of analyzing network traffic, DHCP requests, and behavioral patterns to accurately identify the type and operating system of an unmanaged device.
Used alongside MAB to ensure a device claiming to be a printer actually behaves like a printer, mitigating MAC spoofing attacks.
Dynamic VLAN Assignment
The ability of the network infrastructure to assign a device to a specific Virtual LAN based on its authentication credentials and posture, rather than the physical port it connects to.
Allows a single physical switch or access point to securely service corporate, guest, and IoT devices simultaneously.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary mechanism for managing guest WiFi access, capturing marketing data, and enforcing terms of service.
Posture-Based Access Control
An access model where network privileges are dynamically adjusted based on the real-time security state (posture) of the connecting device.
The ultimate goal of NAC and MDM integration, ensuring compromised devices are automatically quarantined.
Worked Examples
A 400-room hotel needs to secure its network infrastructure. The current setup uses a single flat network for staff laptops, smart TVs in guest rooms, point-of-sale (POS) terminals in the restaurant, and guest WiFi. How should the IT architect redesign this using NAC and MDM integration?
- Deploy a NAC appliance and integrate it with the corporate MDM. 2. Create distinct VLANs: Corporate, Guest, IoT (Smart TVs), and PCI (POS). 3. Push EAP-TLS certificates to staff laptops via MDM; configure NAC to assign these to the Corporate VLAN only if the MDM reports them as compliant. 4. Configure MAB with device profiling for the Smart TVs, assigning them to the IoT VLAN with strict ACLs preventing internet access. 5. Isolate POS terminals on the PCI VLAN with hardcoded MAC access lists and micro-segmentation. 6. Deploy Purple Guest WiFi for the public SSID, capturing user consent and assigning them to the isolated Guest VLAN.
A national retail chain is deploying new handheld inventory scanners across 500 stores. The scanners are Android-based and managed by an MDM. Store managers report that scanners frequently drop off the network when moving between the stockroom and the shop floor.
- Review the roaming configuration on the wireless LAN controller (WLC) to ensure 802.11r (Fast Transition) is enabled for the corporate SSID. 2. Check the NAC policy: ensure that the MDM API query isn't introducing latency during the roam. 3. Implement posture caching on the NAC system so that an MDM compliance check is only performed upon initial association, not during every AP transition. 4. Verify that the MDM is pushing the correct WPA3-Enterprise profile to the scanners.
Practice Questions
Q1. Your organization is rolling out a new MDM platform and wants to enforce strict posture checks (e.g., OS patched within 30 days) via the NAC system starting next Monday. What is the primary risk of this approach?
Hint: Consider the difference between theoretical compliance and actual device state in a large enterprise.
View model answer
The primary risk is a widespread denial of service for legitimate users. It is highly likely that a significant portion of the fleet is currently non-compliant due to delayed update cycles or offline devices. The correct approach is to run the integration in 'Monitor Mode' first to establish a baseline, remediate the non-compliant devices through standard IT processes, and only enforce the posture check once the compliance rate is acceptable.
Q2. A stadium IT director wants to use 802.1X for all devices connecting to the network, including digital signage and POS terminals, to maximize security. Why is this architecturally flawed?
Hint: Think about the capabilities of headless devices.
View model answer
This is flawed because most IoT devices, digital signage, and many legacy POS terminals are 'headless' and do not have an 802.1X supplicant; they cannot present credentials or certificates. Attempting to force 802.1X will result in these devices failing to connect. The architect must use MAC Authentication Bypass (MAB) combined with deep device profiling to secure these endpoints on dedicated, restricted VLANs.
Q3. During a PCI DSS audit, the QSA asks you to prove that the guest WiFi network cannot communicate with the POS terminals in the retail stores. How does your NAC architecture demonstrate this?
Hint: Focus on the outcome of the authentication process.
View model answer
The NAC architecture demonstrates this through dynamic VLAN assignment. When a guest connects, they are routed through the captive portal and assigned to an isolated Guest VLAN. When a POS terminal connects, it is profiled via MAB and assigned to a dedicated PCI VLAN. The core network switches and firewalls are configured with Access Control Lists (ACLs) that explicitly deny routing between the Guest VLAN and the PCI VLAN, satisfying the segmentation requirement.