O Custo Oculto dos Dados de Telemetria em WLANs Corporativas
Este guia detalha os custos ocultos de largura de banda e conformidade da telemetria IoT não solicitada em WLANs corporativas. Ele fornece estratégias de arquitetura acionáveis, incluindo segmentação de VLAN e filtragem de borda DNS, para mitigar riscos e recuperar a taxa de transferência para serviços de negócios críticos.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada
- A Anatomia do Tráfego de Telemetria
- Implicações de Segurança e Conformidade
- O Imperativo da Filtragem de Borda
- Guia de Implementação
- Fase 1: Segmentação de Rede
- Fase 2: Auditoria e Definição de Linha de Base do Tráfego
- Fase 3: Sinkholing de DNS
- Fase 4: Filtragem de Saída e DPI
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios
- Ouça o Briefing
Resumo Executivo
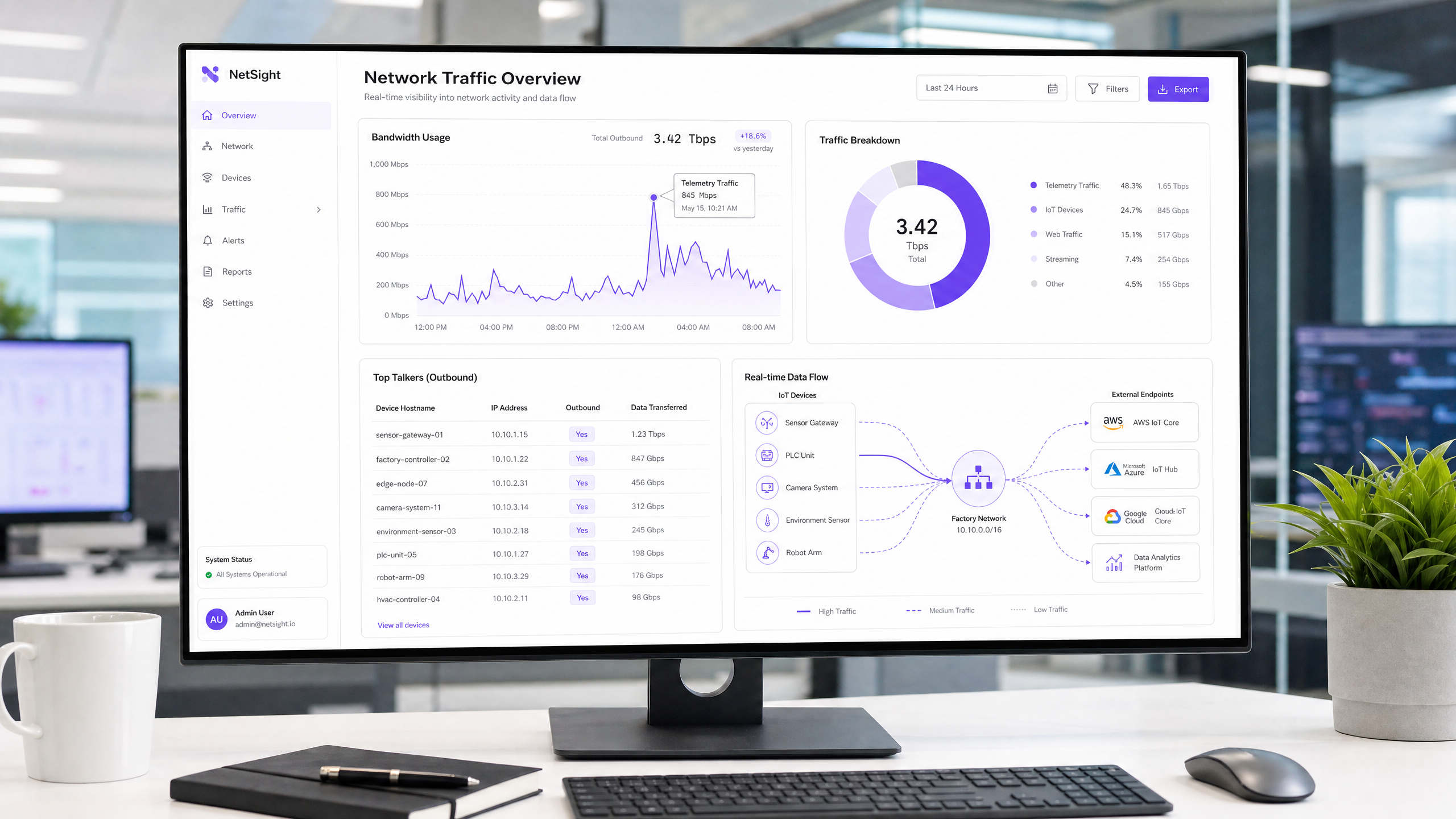
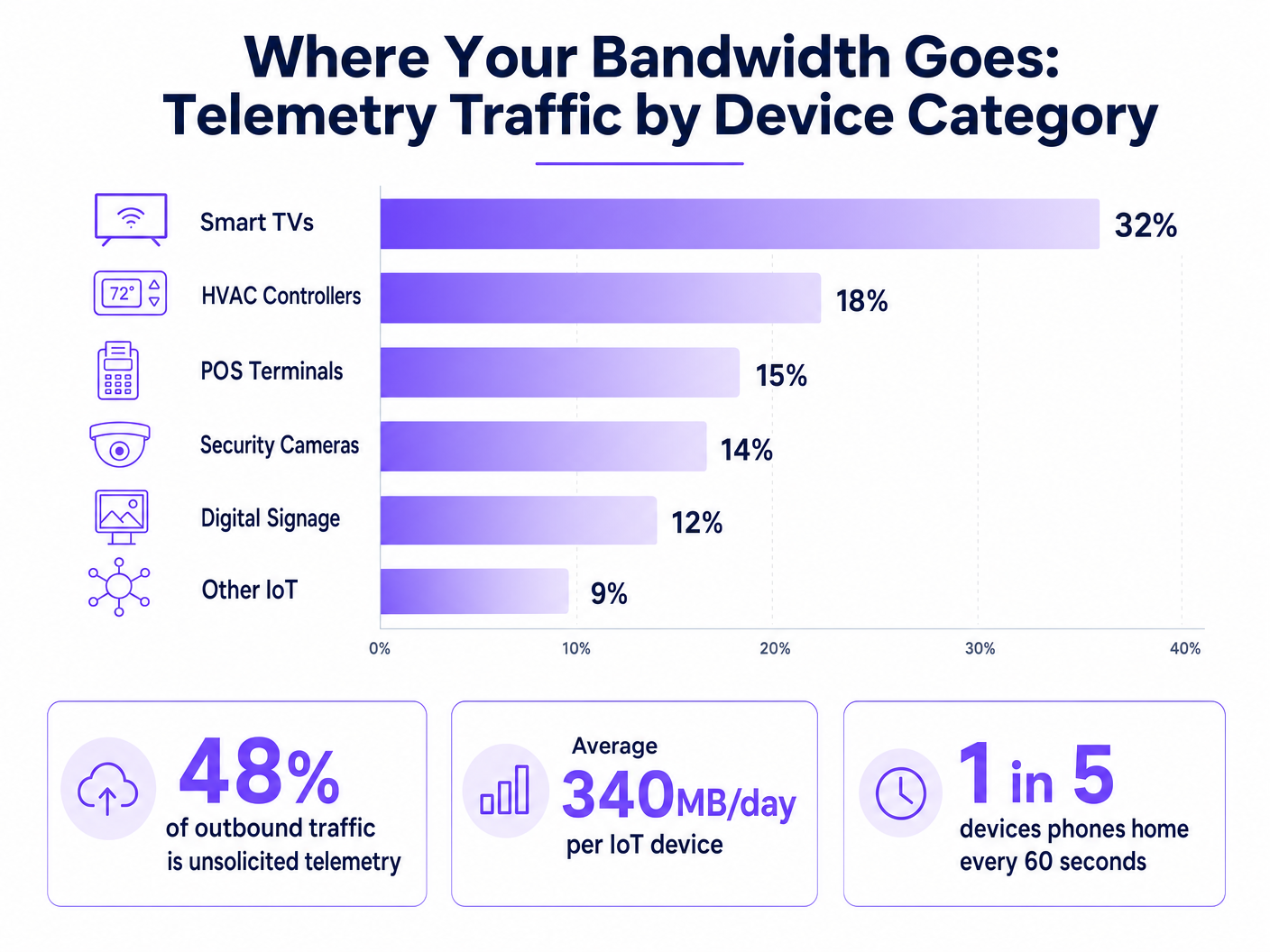
Para CTOs e arquitetos de rede que gerenciam ambientes de alta densidade nos setores de hotelaria, varejo e público, a explosão de dispositivos IoT introduziu um custo oculto nas WLANs corporativas: dados de telemetria não solicitados. Cada smart TV, controlador HVAC e terminal POS envia continuamente sinais para casa, enviando dados de diagnóstico, estatísticas de uso e verificações de firmware para endpoints de fornecedores. No total, este tráfego pode consumir até 48% da largura de banda de saída, impactando severamente o legítimo Guest WiFi e as operações corporativas. Além da degradação da taxa de transferência, a telemetria descontrolada representa um risco significativo de conformidade sob GDPR e PCI DSS, criando vetores de exfiltração de dados não auditados. Este guia fornece um plano técnico para identificar, isolar e filtrar o tráfego de telemetria na borda, permitindo que as equipes de TI recuperem largura de banda, apliquem políticas de segurança e melhorem o ROI geral da rede sem interromper a funcionalidade crítica do dispositivo.
Análise Técnica Detalhada
O desafio fundamental com a telemetria IoT é que ela opera autonomamente, fora do escopo das políticas de rede padrão. Os dispositivos são programados para se comunicar com endpoints controlados por fornecedores, frequentemente usando lógica de nova tentativa agressiva se a conectividade for interrompida.
A Anatomia do Tráfego de Telemetria
As cargas úteis de telemetria variam por fornecedor, mas geralmente incluem métricas de saúde do dispositivo, logs de erro e padrões de uso. Por exemplo, uma smart TV em um quarto de hotel pode "pingar" servidores Samsung ou LG a cada poucos minutos. Embora os pacotes individuais sejam pequenos, o volume agregado em milhares de dispositivos é substancial. Nossa análise mostra que o dispositivo IoT empresarial médio gera aproximadamente 340MB de tráfego de saída diariamente.
Implicações de Segurança e Conformidade
A telemetria não filtrada cria um ponto cego na segurança da rede. Quando os dispositivos ignoram os controles organizacionais para se comunicar externamente, eles violam o princípio do menor privilégio. Isso é particularmente problemático em ambientes sujeitos a estruturas regulatórias rigorosas.
Sob o PCI DSS v4.0, qualquer dispositivo que compartilhe um segmento de rede com ambientes de dados de titulares de cartão (CDE) está no escopo de conformidade. Se um terminal POS gerar telemetria de saída, ele deve ser estritamente isolado. Da mesma forma, o Artigo 32 do GDPR exige medidas técnicas apropriadas para proteger os dados. Conexões de saída não auditadas, mesmo que supostamente benignas, não atendem a este padrão. Embora o IEEE 802.1X forneça autenticação robusta no nível da porta, ele não inspeciona nem controla a carga útil de dispositivos autenticados. O WPA3 protege a transmissão sem fio, mas não faz nada para impedir que o dispositivo inicie a conexão de telemetria.
O Imperativo da Filtragem de Borda
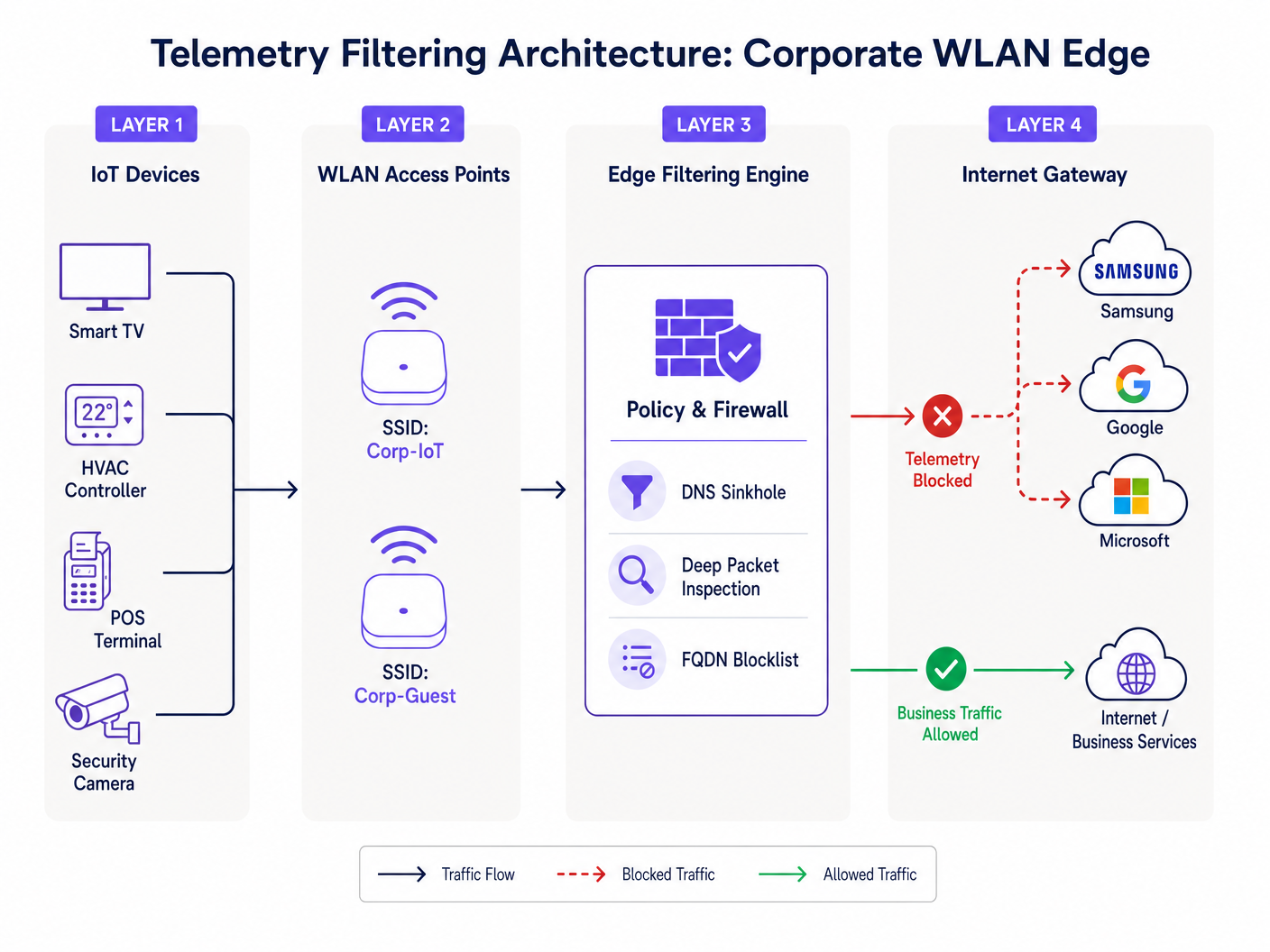
Para resolver isso, as organizações devem implementar a filtragem na borda da rede. Isso envolve uma abordagem multicamadas: sinkholing de DNS para interceptar solicitações de resolução para domínios de telemetria conhecidos, e Deep Packet Inspection (DPI) combinado com blocklists FQDN para capturar comunicações IP programadas. Esta arquitetura garante que apenas o tráfego de negócios autorizado atravesse o gateway da internet, conforme detalhado em nosso guia sobre Melhorando as Velocidades do WiFi Bloqueando Redes de Anúncios na Borda .
Guia de Implementação
A implantação de uma arquitetura robusta de filtragem de telemetria requer uma abordagem sistemática para evitar a interrupção do tráfego operacional legítimo.
Fase 1: Segmentação de Rede
O passo fundamental é a segmentação estrita de VLAN. Dispositivos IoT nunca devem residir na mesma sub-rede que usuários corporativos, redes de convidados ou sistemas no escopo do PCI. Crie VLANs IoT dedicadas com listas de controle de acesso (ACLs) estritas que negam o roteamento inter-VLAN por padrão.
Fase 2: Auditoria e Definição de Linha de Base do Tráfego
Antes de implementar bloqueios, estabeleça uma linha de base de tráfego. Implante ferramentas de análise de fluxo (NetFlow/sFlow) ou utilize uma plataforma abrangente de WiFi Analytics para monitorar conexões de saída. Identifique os principais emissores e mapeie seus endpoints de destino. Esta auditoria revelará a verdadeira escala do problema de telemetria.
Fase 3: Sinkholing de DNS
Configure o escopo DHCP para a VLAN IoT para atribuir um resolvedor DNS interno que aplique políticas. Implemente o bloqueio baseado em categoria para endpoints de telemetria e diagnóstico conhecidos. Utilize blocklists curadas pela comunidade ou feeds de inteligência de ameaças comerciais. Monitore os logs por 72 horas em modo 'somente relatório' para identificar potenciais falsos positivos antes de aplicar os bloqueios.
Fase 4: Filtragem de Saída e DPI
Para dispositivos que ignoram o DNS usando endereços IP programados, implemente a filtragem de saída no firewall de perímetro. Configure regras de DPI para identificar e descartar assinaturas de telemetria. Garanta que essas regras sejam atualizadas regularmente para considerar mudanças na infraestrutura do fornecedor.
Melhores Práticas
- Adote uma Postura de Negação por Padrão para IoT: Por padrão, as VLANs IoT não devem ter acesso à internet. Apenas liste explicitamente os FQDNs e portas necessários para a funcionalidade principal do dispositivo (por exemplo, NTP, endpoints de API específicos).
- Implemente Limitação de Taxa: Mesmo o tráfego autorizado deve estar sujeito à modelagem de largura de banda. Aplique políticas de QoS para limitar a taxa de transferência máxima disponível para segmentos IoT, garantindo que eles não saturem o uplink durante atualizações de firmware em massa.
- Manutenção Regular da Blocklist: Os endpoints de telemetria evoluem. Automatize a ingestão de blocklists FQDN atualizadas empara o seu motor de filtragem de borda para manter a eficácia.
- Monitorar Redes de Convidados: Aplique princípios de filtragem semelhantes à rede de convidados. Embora você não possa controlar os dispositivos dos convidados, pode impedir que a telemetria deles degrade a experiência compartilhada.
Solução de Problemas e Mitigação de Riscos
O risco mais significativo na filtragem de telemetria é o bloqueio excessivo, que pode prejudicar a funcionalidade do dispositivo. Por exemplo, bloquear a CDN de um fornecedor pode inadvertidamente bloquear atualizações de segurança críticas.
- Sintoma: Dispositivos mostram status offline no console de gerenciamento.
- Mitigação: Revise os logs de DNS para consultas bloqueadas do IP do dispositivo afetado. Adicione temporariamente o domínio bloqueado à lista de permissões e verifique se a funcionalidade é restaurada. Frequentemente, os fornecedores usam subdomínios distintos para telemetria versus gerenciamento (por exemplo,
telemetry.vendor.comvsapi.vendor.com).
Outro modo de falha comum é a segmentação incompleta, onde uma VLAN de gerenciamento inadvertidamente conecta o segmento IoT à rede corporativa. Testes de penetração regulares e auditorias de VLAN são essenciais para verificar o isolamento.
ROI e Impacto nos Negócios
A implementação da filtragem de telemetria gera retornos imediatos e mensuráveis.
- Recuperação de Largura de Banda: As organizações geralmente observam uma redução de 15-30% na utilização da WAN de saída, adiando atualizações caras de largura de banda.
- Experiência do Usuário Aprimorada: A largura de banda recuperada se traduz diretamente em conectividade mais rápida e confiável para convidados e funcionários, melhorando os índices de satisfação em ambientes de Hotelaria e Varejo .
- Redução de Riscos: A eliminação de conexões de saída não autorizadas reduz significativamente a superfície de ataque e simplifica as auditorias de conformidade, mitigando o risco de multas regulatórias.
Para implantações no setor público, onde os orçamentos são apertados e o escrutínio é alto, essas eficiências são críticas para a entrega de serviços confiáveis, alinhando-se com iniciativas para impulsionar a inclusão digital, conforme discutido em nosso recente anúncio: Purple Appoints Iain Fox as VP Growth – Public Sector to Drive Digital Inclusion and Smart City Innovation .
Ouça o Briefing
Para uma análise mais aprofundada das considerações arquitetônicas, ouça nosso briefing técnico de 10 minutos:
Definições principais
Telemetry Data
Automated transmission of operational, diagnostic, or usage data from a connected device back to its manufacturer or a third-party cloud service.
Often transmitted without explicit IT authorization, consuming bandwidth and creating compliance blind spots.
DNS Sinkhole
A DNS server configured to hand out incorrect IP addresses (often 0.0.0.0) for specific domain names, effectively preventing devices from connecting to those domains.
Used as a lightweight, highly effective method to block known telemetry and tracking endpoints at the network edge.
Deep Packet Inspection (DPI)
Advanced network packet filtering that examines the data part (and possibly the header) of a packet as it passes an inspection point, searching for protocol non-compliance, viruses, spam, intrusions, or defined criteria.
Necessary for identifying and blocking telemetry traffic that uses hardcoded IP addresses or non-standard ports, bypassing DNS controls.
FQDN Blocklist
A list of Fully Qualified Domain Names (e.g., telemetry.vendor.com) that are explicitly denied access through the network gateway or DNS resolver.
More precise than IP blocking, as cloud-hosted telemetry endpoints frequently change IP addresses but maintain consistent domain names.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic, improve performance, and enhance security.
The critical first step in managing IoT devices, ensuring their telemetry traffic cannot traverse corporate or PCI-scoped network segments.
Egress Filtering
The practice of monitoring and potentially restricting the flow of information outbound from one network to another, typically the internet.
Crucial for preventing unauthorized data exfiltration and enforcing the 'Default-Deny' posture for IoT segments.
PCI DSS Scope
All system components, people, and processes that are included in or connected to the Cardholder Data Environment (CDE).
Uncontrolled telemetry from devices on the same network segment as payment terminals can inadvertently bring those devices into audit scope.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
While it secures network entry, it does not inspect or control the telemetry payloads sent by authenticated devices.
Exemplos práticos
A 400-room resort is experiencing severe network congestion every morning between 2:00 AM and 4:00 AM, impacting early-rising guests and back-office operations. The network team suspects the recently installed smart TVs in every room are responsible. How should they diagnose and resolve this?
- Diagnosis: Deploy a NetFlow collector on the core switch to analyze traffic during the congestion window. The analysis reveals that all 400 TVs are simultaneously downloading firmware updates and uploading aggregated daily usage telemetry to the manufacturer's CDN. 2. Resolution: First, ensure the TVs are on a dedicated IoT VLAN. Second, implement a QoS policy on the firewall to rate-limit outbound and inbound traffic for the IoT VLAN to 10% of the total WAN link capacity. Third, implement DNS sinkholing to block the specific FQDNs used for telemetry upload, while allowing the FQDNs used for firmware updates. Finally, stagger the update windows if the vendor management console permits.
A large retail chain with 200 locations uses a mix of legacy and modern POS systems. During a PCI DSS audit, the assessor notes that several modern POS terminals are generating outbound HTTPS traffic to unknown cloud endpoints. How should the network architect remediate this finding?
- Immediate Containment: Verify that the POS terminals are on a strictly isolated CDE (Cardholder Data Environment) VLAN. 2. Traffic Analysis: Perform packet captures (PCAP) on the egress interface for the CDE VLAN. Identify the destination IP addresses and attempt reverse DNS lookups to determine the vendor. 3. Policy Enforcement: Implement a 'Default-Deny' egress rule on the firewall for the CDE VLAN. Only explicitly whitelist the IP addresses and ports required for payment processing and authorized management traffic. 4. Documentation: Document the whitelisted endpoints and the business justification for each in the firewall rule base, providing this documentation to the PCI assessor.
Questões práticas
Q1. You are deploying a new fleet of smart HVAC controllers across a corporate campus. The vendor states that the controllers require internet access to report diagnostic data to their cloud platform for warranty support. How do you integrate these devices securely?
Dica: Consider the principle of least privilege and how to balance operational requirements with security controls.
Ver resposta modelo
- Place the HVAC controllers on a dedicated, isolated IoT VLAN. 2. Request the specific FQDNs and ports required for the diagnostic reporting from the vendor. 3. Configure the perimeter firewall with a default-deny egress rule for the IoT VLAN. 4. Create an explicit allow rule only for the vendor-provided FQDNs and ports. 5. Implement rate limiting on the VLAN to prevent the controllers from consuming excessive bandwidth.
Q2. During a routine log review, you notice a significant volume of DNS requests from the IoT VLAN being blocked by the DNS sinkhole. However, the operations team reports that the digital signage displays are no longer updating their content. What is the likely cause and remediation?
Dica: Think about how vendors often structure their cloud services and the risks of over-blocking.
Ver resposta modelo
The likely cause is over-blocking. The vendor is probably using the same domain (or a closely related subdomain) for both telemetry reporting and content delivery. Remediation: 1. Identify the specific blocked domain in the DNS logs. 2. Temporarily whitelist the domain. 3. Use packet capture to analyze the traffic to that domain. 4. If possible, use DPI on the firewall to block the specific telemetry URI paths while allowing the content update paths, or work with the vendor to identify distinct FQDNs for each function.
Q3. A stadium IT director wants to implement telemetry filtering but is concerned about the processing overhead on the core firewall during game days when 50,000 fans are connected. What architecture provides the most efficient filtering?
Dica: Which filtering method consumes the least CPU cycles on the firewall?
Ver resposta modelo
The most efficient approach is to rely heavily on DNS sinkholing for the bulk of the filtering. By configuring the DHCP servers to point client devices to an internal DNS resolver that blocks known telemetry domains, the traffic is dropped before a connection is even attempted, saving firewall state table entries and DPI processing cycles. The firewall should only be used as a secondary measure for hardcoded IPs or highly specific block rules.