Proteger o Trabalho Híbrido: Combinar NAC com ZTNA para Acesso Contínuo
Este guia técnico abrangente aborda a convergência arquitetónica de Network Access Control (NAC) e Zero Trust Network Access (ZTNA) para proteger ambientes de trabalho híbridos em locais corporativos, retalho, hotelaria e setor público. Fornece um plano de implementação faseado, estudos de caso reais e orientação de conformidade para arquitetos de TI e CTOs que precisam de eliminar as lacunas de segurança criadas por domínios de acesso isolados no local e na nuvem.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada: A Arquitetura de Convergência
- As Limitações dos Domínios de Segurança Isolados
- Corretagem Unificada de Identidade e Contexto
- Guia de Implementação: Implementação Passo a Passo
- Fase 1: Descoberta de Identidade e Ativos
- Fase 2: Definição de Políticas e Micro-Segmentação
- Fase 3: Aplicação e Otimização
- Melhores Práticas para Ambientes Empresariais
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios

Resumo Executivo
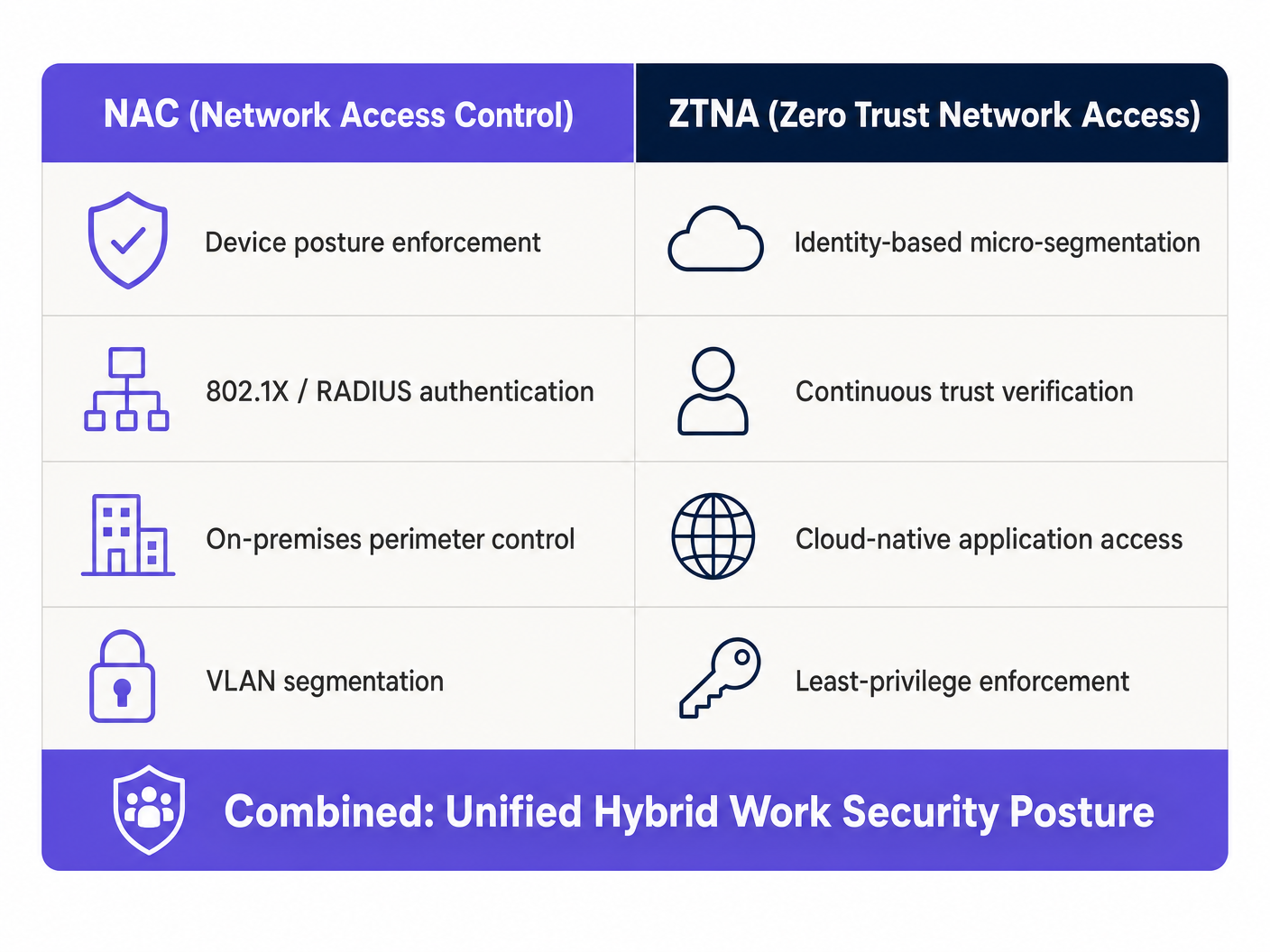
Para arquitetos de rede empresariais e CTOs que gerem ambientes distribuídos, o perímetro dissolveu-se irrevogavelmente. O modelo tradicional de proteger uma sede corporativa com um robusto Network Access Control (NAC) enquanto se baseia em VPNs legadas para acesso remoto já não é viável. As empresas modernas exigem uma postura de segurança unificada que ligue perfeitamente a infraestrutura no local com aplicações nativas da nuvem. Este guia detalha a integração arquitetónica de NAC e Zero Trust Network Access (ZTNA), fornecendo um plano para proteger ambientes de trabalho híbridos sem comprometer a experiência do utilizador ou o débito da rede.
Ao combinar a aplicação da postura ao nível do dispositivo de NAC com a micro-segmentação centrada na identidade de ZTNA, as organizações podem alcançar uma verificação contínua da confiança, independentemente da localização do utilizador. Esta convergência é particularmente crítica para setores com grande afluência e requisitos de conformidade complexos, como Retalho , Saúde e Hotelaria . Além disso, o aproveitamento de plataformas como a infraestrutura Guest WiFi da Purple pode estender estes princípios de confiança zero a redes de convidados, garantindo um isolamento robusto e proteção de dados alinhados com as obrigações do GDPR e PCI DSS.
Análise Técnica Detalhada: A Arquitetura de Convergência
As Limitações dos Domínios de Segurança Isolados
Historicamente, NAC e ZTNA operavam como domínios de segurança isolados. O NAC, aproveitando o IEEE 802.1X e o RADIUS, destacava-se no controlo do acesso físico e sem fios dentro do perímetro corporativo. Fornecia um robusto perfil de dispositivos, avaliação de postura e atribuição de VLAN. Por outro lado, o ZTNA surgiu para proteger o acesso remoto a aplicações na nuvem e no local, operando com base no princípio de "nunca confiar, sempre verificar", baseado na identidade e contexto do utilizador, em vez da localização da rede.
O atrito surge quando os trabalhadores híbridos fazem a transição entre estes domínios. Um utilizador que se autentica de forma contínua via ZTNA em casa, muitas vezes enfrenta uma experiência desarticulada ao entrar no escritório corporativo, onde as políticas de NAC podem não estar alinhadas com o seu contexto ZTNA. Esta fragmentação introduz pontos cegos de segurança e sobrecarga operacional que impactam diretamente tanto a eficiência de TI quanto a produtividade do utilizador final.
Corretagem Unificada de Identidade e Contexto
A solução arquitetónica reside no estabelecimento de uma camada unificada de corretagem de identidade e contexto que sincroniza a telemetria entre os motores de política de NAC e ZTNA. Esta integração permite uma avaliação contínua da postura que persiste através dos limites da rede.
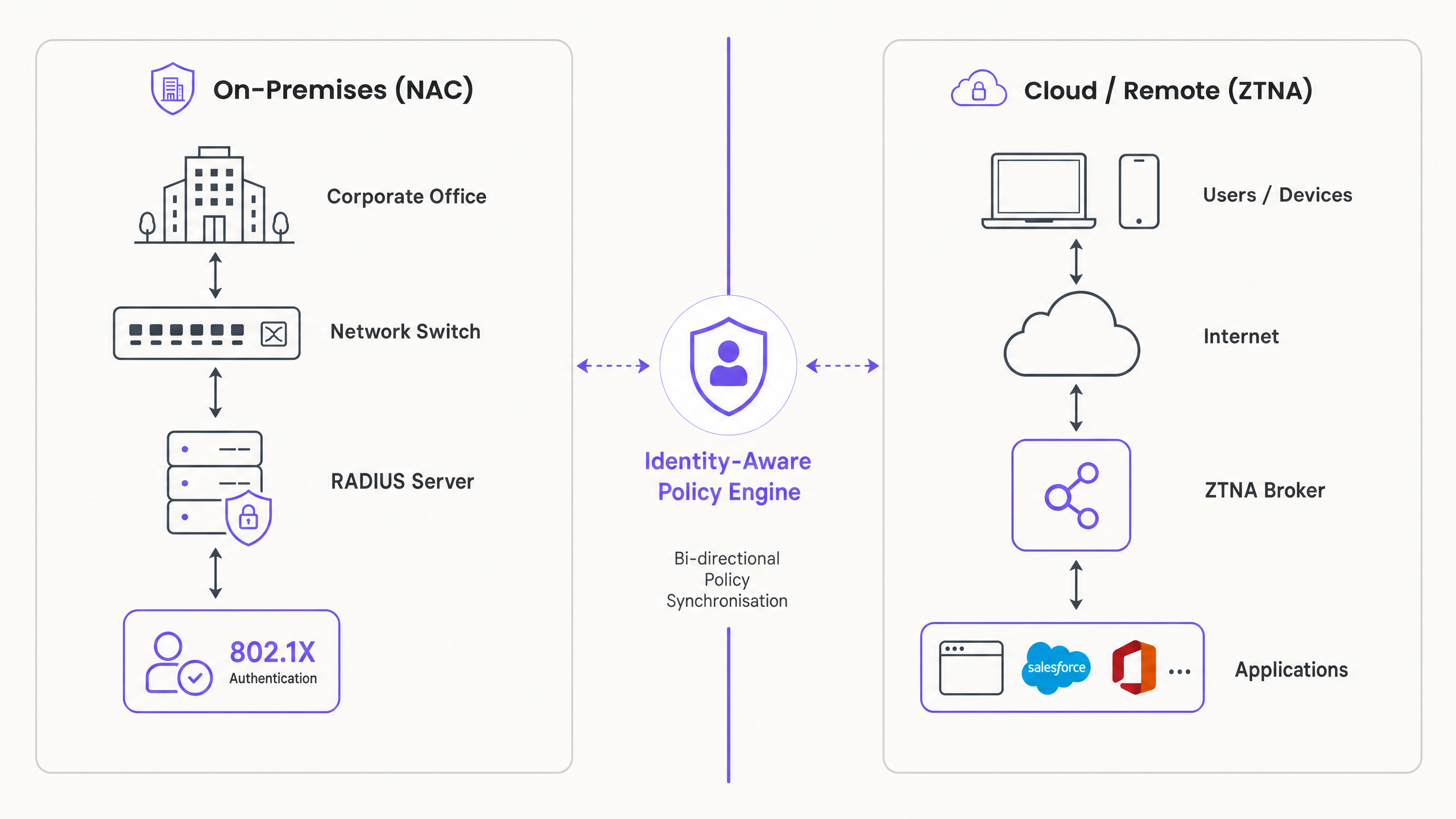
A integração opera através de três mecanismos chave. Primeiro, Avaliação Contínua da Postura: quando um dispositivo se conecta à rede corporativa, a solução NAC realiza uma verificação abrangente da postura, cobrindo a versão do SO, o estado do AV e a validação do certificado. Este contexto é imediatamente partilhado com o broker ZTNA via API integração. Segundo, Aplicação Dinâmica de Políticas: se a postura do dispositivo se degradar — por exemplo, for detetado malware — o sistema NAC coloca o dispositivo em quarentena na rede local, enquanto simultaneamente instrui o broker ZTNA a revogar o acesso a aplicações críticas na nuvem. Terceiro, Transição Contínua: à medida que o utilizador se move do escritório para um local remoto, o cliente ZTNA mantém o contexto de confiança estabelecido, eliminando a necessidade de reautenticação e garantindo acesso ininterrupto aos recursos autorizados.
Para uma compreensão mais aprofundada das tecnologias sem fios subjacentes que suportam estas implementações, consulte o nosso guia sobre Frequências Wi-Fi: Um Guia para as Frequências Wi-Fi em 2026 .
Guia de Implementação: Implementação Passo a Passo
A implementação de uma arquitetura NAC/ZTNA convergente requer uma abordagem faseada para minimizar a interrupção e garantir uma aplicação robusta de políticas.
Fase 1: Descoberta de Identidade e Ativos
Antes de implementar políticas de aplicação, deve obter visibilidade completa do seu ambiente de rede. Implemente a sua solução NAC em modo apenas de monitorização — configure-a para descobrir e perfilar todos os dispositivos conectados, incluindo laptops corporativos, BYOD, IoT e dispositivos de convidados, sem bloquear o acesso. Consolide as identidades dos utilizadores integrando as soluções NAC e ZTNA com um Provedor de Identidade central, como Azure AD ou Okta. Isso garante políticas de autenticação consistentes em ambos os domínios. Simultaneamente, utilize a sua solução ZTNA para monitorizar padrões de acesso a aplicações, identificando quais utilizadores necessitam de acesso a aplicações específicas e formando a base para as suas políticas de micro-segmentação.
Fase 2: Definição de Políticas e Micro-Segmentação
Faça a transição da visibilidade para o controlo, definindo políticas de acesso granulares baseadas no princípio do menor privilégio. Estabeleça requisitos de segurança de base para dispositivos corporativos, incluindo a versão mínima do SO e os requisitos de agente EDR ativo, e configure a solução NAC para aplicar estes requisitos para acesso no local. Defina políticas ZTNA que restrinjam o acesso a aplicações com base na função do utilizador e no contexto do dispositivo, garantindo o alinhamento com os requisitos de postura definidos na solução NAC. Criticamente, configure a integração da API entre as suas plataformas NAC e ZTNA para permitir a partilha bidirecional de contexto, garantindo que uma alteração na postura do dispositivo detetada pelo NAC imaciona imediatamente uma atualização de política no broker ZTNA.
Fase 3: Aplicação e Otimização
Ative gradualmente o modo de aplicação, monitorizando anomalias e refinando políticas conforme necessário. Transicione a solução NAC do modo de monitorização para o modo de aplicação, começando com um grupo piloto de utilizadores ou localizações, e monitorize as falhas de autenticação. Implemente o cliente ZTNA em todos os endpoints corporativos, garantindo acesso contínuo a aplicações na cloud e on-premises. Estenda políticas robustas de acesso de convidados usando plataformas como o Guest WiFi da Purple, garantindo que o tráfego de convidados seja estritamente isolado dos recursos corporativos. Aproveite o WiFi Analytics para monitorizar padrões de uso e detetar potenciais anomalias em toda a rede de convidados.
Melhores Práticas para Ambientes Empresariais
Priorize a experiência do utilizador durante toda a implementação. A segurança não deve impedir a produtividade, e a transição entre o acesso on-premises e remoto deve ser transparente para o utilizador, aproveitando o single sign-on e mecanismos de autenticação contínua. Para acesso on-premises, exija a autenticação IEEE 802.1X para todos os dispositivos corporativos, pois isso fornece uma validação criptográfica robusta da identidade do dispositivo ao nível da porta.
Integre capacidades de deteção de ameaças impulsionadas por IA nas suas soluções NAC e ZTNA para identificar comportamentos anómalos e colocar automaticamente em quarentena dispositivos comprometidos. Para uma perspetiva futura sobre esta capacidade, consulte The Future of Wi-Fi Security: AI-Driven NAC and Threat Detection e o equivalente em espanhol El Futuro de la Seguridad Wi-Fi: NAC Impulsado por IA y Detección de Amenazas . Para empresas distribuídas, a integração de ZTNA com SD-WAN pode otimizar o encaminhamento de aplicações e melhorar o desempenho em vários sites — reveja a nossa comparação em SD WAN vs MPLS: The 2026 Enterprise Network Guide .
Resolução de Problemas e Mitigação de Riscos
Atrasos na Sincronização de Contexto representam o modo de falha mais crítico. Se a integração da API entre NAC e ZTNA apresentar latência, um dispositivo comprometido pode reter o acesso a aplicações na cloud por mais tempo do que o aceitável. A mitigação é implementar notificações push baseadas em webhooks em vez de depender apenas de mecanismos de polling, garantindo atualizações de políticas quase em tempo real.
Políticas Excessivamente Restritivas podem causar picos significativos de tickets de helpdesk ao implementar verificações de postura rigorosas sem comunicação adequada com o utilizador. Utilize captive portals para informar os utilizadores sobre a não conformidade e fornecer instruções de remediação de autoatendimento antes de bloquear completamente o acesso.
Falhas de Autenticação de Dispositivos IoT são inevitáveis em ambientes de locais. Dispositivos IoT headless não podem suportar clientes 802.1X ou ZTNA. A solução é o MAC Authentication Bypass (MAB) combinado com um rigoroso perfil de dispositivo e segmentação VLAN estrita para isolar o tráfego IoT dos recursos corporativos.
Monitorização da Saúde da Integração da API é frequentemente negligenciada. Se a sincronização entre NAC e ZTNA for interrompida, existe uma falha de segurança que nenhum dos sistemas pode resolver independentemente. Implemente monitorização e alertas dedicados sobre a saúde da integração e defina políticas de segurança que acionem restrições automáticas de acesso se a sincronização for perdida por mais de um limite definido.
ROI e Impacto nos Negócios
A convergência de NAC e ZTNA oferece valor de negócio mensurável para além da mitigação de riscos. A consolidação da gestão de políticas reduz a carga administrativa nas equipas de TI, permitindo-lhes focar-se em iniciativas estratégicas em vez de gerir silos de segurança díspares. A eliminação de VPNs legadas melhora significativamente a experiência de trabalho híbrido, reduzindo o tempo de inatividade e a frustração, ao mesmo tempo que melhora o desempenho das aplicações para utilizadores remotos.
A capacidade de demonstrar avaliação contínua da postura e controlo de acesso baseado na identidade simplifica a elaboração de relatórios de conformidade para frameworks como PCI DSS e GDPR, particularmente relevante em ambientes de Transport e retalho onde as obrigações de proteção de dados de titulares de cartões e dados pessoais são rigorosas. Organizações que implementaram arquiteturas convergentes relatam consistentemente uma redução no tempo médio para conter (MTTC) incidentes de segurança, uma vez que a aplicação bidirecional de políticas permite a quarentena automatizada sem exigir intervenção manual.
Definições Principais
Network Access Control (NAC)
A security solution that enforces policy on devices seeking access to a network infrastructure, typically utilising IEEE 802.1X for authentication and posture assessment to determine VLAN assignment and access rights.
Critical for securing on-premises environments, ensuring only compliant and authorised devices can connect to corporate switches and wireless access points. IT teams encounter this when managing physical office and venue networks.
Zero Trust Network Access (ZTNA)
An IT security solution that provides secure remote access to applications and services based on defined access control policies, operating on the principle of least privilege and continuous identity verification rather than network location.
Replaces legacy VPNs by providing identity-based micro-segmentation, granting access only to specific applications rather than the entire network. Relevant when securing remote workers and cloud application access.
Micro-segmentation
The practice of dividing a network into isolated segments to reduce the attack surface and prevent lateral movement by threat actors, applied at the application or workload level rather than the network perimeter.
ZTNA applies this concept at the application level, ensuring a compromised endpoint cannot pivot to access unauthorised resources. IT teams encounter this when designing zero-trust architectures.
Posture Assessment
The process of evaluating a device's security state — including OS version, active antivirus, installed certificates, and patch level — before granting network or application access.
A core function of NAC, ensuring that vulnerable or compromised devices are quarantined or remediated before they can interact with the corporate network. Relevant during device onboarding and continuous monitoring.
IEEE 802.1X
An IEEE standard for port-based Network Access Control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN, using EAP (Extensible Authentication Protocol) over the network medium.
The gold standard for enterprise network authentication, providing robust cryptographic validation of device identity. IT teams encounter this when configuring switches, wireless controllers, and RADIUS servers.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service, acting as the communication layer between NAC and identity providers.
The backend protocol utilised by NAC solutions to communicate with identity providers and enforce access policies. Relevant when integrating NAC with Active Directory or cloud IdPs.
MAC Authentication Bypass (MAB)
A fallback authentication method used by NAC solutions for devices that do not support 802.1X, relying on the device's MAC address as an identifier to assign network access policies.
Necessary for accommodating headless devices — printers, IoT sensors, digital signage — in enterprise environments. Less secure than 802.1X and requires strict VLAN segmentation to mitigate MAC spoofing risks.
Identity Provider (IdP)
A system entity that creates, maintains, and manages identity information for principals while providing authentication services to relying applications within a federation or distributed network.
The central source of truth for user identities, integrating with both NAC and ZTNA to ensure consistent authentication policies. IT teams encounter this when configuring SSO and MFA across enterprise systems.
VLAN (Virtual Local Area Network)
A logical subdivision of a physical network that groups devices into isolated broadcast domains, enabling traffic segmentation without requiring separate physical infrastructure.
The primary mechanism for isolating different device classes — corporate, guest, IoT — within a shared physical network. Critical for compliance with PCI DSS requirements for cardholder data environment isolation.
Exemplos Práticos
A global retail chain with 500 locations needs to secure access for regional managers who frequently travel between stores, corporate headquarters, and remote home offices. They currently experience frequent VPN disconnects and inconsistent access to cloud-hosted inventory management applications.
Implement a converged NAC/ZTNA architecture across all locations. Deploy 802.1X via NAC for seamless, secure access when managers are physically in-store or at HQ, authenticating against a centralised RADIUS server integrated with Azure AD. Deploy a ZTNA client on all corporate laptops. Integrate the NAC and ZTNA policy engines via API, configuring webhook notifications for immediate posture updates. When a manager connects to the in-store network, the NAC authenticates the device and shares the 'trusted internal' context with the ZTNA broker. The ZTNA broker then grants direct, optimised access to the cloud-hosted inventory application without requiring a VPN tunnel, reducing latency and eliminating disconnection issues. When the manager works from home, the ZTNA client establishes a secure micro-tunnel to the application, maintaining the same access policies without relying on the corporate network perimeter. Guest and IoT devices in-store are isolated on separate VLANs managed via Purple's Guest WiFi platform.
A large conference centre needs to provide secure WiFi for corporate staff while isolating thousands of daily guest connections and third-party vendor IoT devices including digital signage, BLE beacons, and environmental sensors.
Deploy a robust NAC solution configured with strict VLAN segmentation across three distinct tiers. Tier one: corporate staff devices authenticate via 802.1X and are assigned to a secure internal VLAN with full access to internal management systems. Tier two: implement Purple's Guest WiFi platform to manage public access, capturing valuable analytics while ensuring complete isolation from the corporate network via a dedicated guest VLAN with internet-only access. Tier three: for vendor IoT devices, utilise MAC Authentication Bypass (MAB) combined with deep device profiling — analysing DHCP fingerprints, HTTP user agents, and traffic patterns — to accurately identify device types and assign them to restricted, internet-only VLANs. Integrate ZTNA for corporate staff to access internal management applications securely from any location within the venue or remotely. For BLE beacon infrastructure, refer to the guide on BLE Low Energy Explained for Enterprise for integration considerations.
Perguntas de Prática
Q1. Your organisation is deploying ZTNA to replace a legacy VPN. However, users returning to the corporate office are experiencing latency when accessing applications hosted locally in the on-premises data centre, as ZTNA traffic is routing through a cloud-hosted broker. What is the recommended architectural solution?
Dica: Consider how the ZTNA client determines the optimal path to the application based on the user's physical network context.
Ver resposta modelo
Implement a Local Edge or On-Premises ZTNA Broker within the corporate data centre. Configure the ZTNA client to detect when the device is authenticated on the internal corporate network via NAC and route traffic directly to the local application via the internal broker, rather than hair-pinning through the cloud-hosted broker. This reduces latency for on-premises applications while maintaining the same identity-based access controls. The NAC context sharing via API should signal to the ZTNA broker that the device is on a trusted internal network, enabling the local routing decision.
Q2. A hospital IT team needs to secure hundreds of connected medical devices — infusion pumps, patient monitors, imaging equipment — that cannot run 802.1X supplicants or ZTNA clients. How should these devices be secured within a converged NAC/ZTNA architecture?
Dica: Consider fallback authentication methods and the principle of network-level isolation for devices that cannot participate in identity-based controls.
Ver resposta modelo
Utilise MAC Authentication Bypass (MAB) on the NAC solution, combined with deep device profiling using DHCP fingerprints, HTTP user agents, and traffic behaviour analysis to accurately identify and classify each medical device type. Once identified, the NAC dynamically assigns these devices to highly restricted, isolated VLANs that only permit communication with specific, required medical servers and systems — blocking all other traffic by default. ZTNA is not applicable to these devices; security relies entirely on strict network segmentation and continuous traffic monitoring for anomalous behaviour. Ensure the medical device VLANs are completely isolated from the cardholder data environment to maintain PCI DSS compliance.
Q3. During a production deployment, the API integration between your NAC and ZTNA solutions fails silently — no alerts are triggered. A user's laptop on the corporate network subsequently becomes infected with malware. Describe the expected security outcome and identify the architectural gap that allowed it.
Dica: Analyse the impact of broken context synchronisation on each policy engine independently, and consider what monitoring should have been in place.
Ver resposta modelo
The NAC solution will detect the degraded posture via EDR integration and quarantine the device on the local network, preventing lateral movement within the corporate environment. However, because the API integration has failed silently, the ZTNA broker has not received the updated posture context. If the user attempts to access a cloud application, the ZTNA client may still establish a connection if the initial identity authentication token remains valid and has not expired. The architectural gap is twofold: first, the absence of health monitoring on the API integration itself; second, the lack of a fail-safe policy that triggers automatic access restrictions if context synchronisation is lost beyond a defined threshold. The remediation is to implement dedicated monitoring with alerting on integration health, configure the ZTNA broker to require periodic posture re-validation (not just initial authentication), and define a default-deny policy that activates if the NAC context feed is unavailable for more than a specified interval.