Café WiFi: How to Set Up, Secure and Monetise Your Guest Network
A comprehensive technical reference for IT managers and venue operators on designing, securing, and monetising café WiFi networks. It covers essential network segmentation, Wi-Fi 6 hardware deployment, GDPR-compliant captive portals, and marketing automation to drive measurable ROI.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Network Architecture and Segmentation
- Wireless Standards and Hardware Selection
- Security Protocols
- Implementation Guide
- Step 1: Site Survey and Bandwidth Planning
- Step 2: Infrastructure Configuration
- Step 3: Captive Portal Deployment
- Step 4: Compliance and Consent Management
- Step 5: Marketing Automation Integration
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For modern hospitality venues, café WiFi is no longer a mere operational utility—it is a critical first-party data asset, a marketing automation channel, and a stringent compliance obligation. This technical reference guide provides IT managers, network architects, and venue operations directors with a comprehensive framework for designing, deploying, and monetising guest networks.
From independent coffee shops to multi-site enterprise chains, the architectural principles remain consistent. You must enforce strict network segmentation to maintain PCI DSS compliance, deploy business-grade 802.11ax (Wi-Fi 6) hardware for dense client environments, and implement a robust captive portal to capture explicit, GDPR-compliant marketing consent.
By transitioning from unmanaged consumer-grade routers to an enterprise Guest WiFi platform, venues can transform a cost centre into a measurable revenue driver. This guide outlines the exact hardware specifications, security standards, bandwidth calculations, and marketing automation workflows required to build a resilient, profitable guest network.
Technical Deep-Dive
Network Architecture and Segmentation
The foundational principle of any public-facing network is absolute logical separation from operational infrastructure. Deploying a single flat network that hosts both your point-of-sale (POS) systems and your guest traffic is a critical failure in both security and compliance.
VLAN Implementation: Your routing and switching infrastructure must support IEEE 802.1Q VLAN tagging. A standard deployment requires a minimum of two Virtual Local Area Networks:
- VLAN 10 (Operational): Dedicated to POS terminals, back-office PCs, and IoT devices.
- VLAN 20 (Guest): Dedicated exclusively to the café WiFi guest network.
Traffic between these VLANs must be blocked at the firewall level. Access points (APs) will broadcast distinct Service Set Identifiers (SSIDs) mapped directly to their respective VLANs. This isolation is a non-negotiable requirement for PCI DSS compliance, ensuring that the cardholder data environment (CDE) cannot be compromised by malicious actors connected to the guest network.
Wireless Standards and Hardware Selection
For environments with high device density—such as a busy café where 40-80 clients may be streaming, browsing, and syncing simultaneously—consumer-grade hardware will rapidly degrade.
802.11ax (Wi-Fi 6) Requirements: Modern deployments should exclusively utilise Wi-Fi 6 access points. The critical advantage of Wi-Fi 6 in hospitality environments is Orthogonal Frequency-Division Multiple Access (OFDMA). Unlike older standards that serve clients sequentially, OFDMA allows a single AP to communicate with multiple devices simultaneously by dividing channels into smaller subcarriers. This drastically reduces latency and improves throughput in congested environments.
Hardware Sizing:
- Single Site (50-150 sqm): 1-2 ceiling-mounted Wi-Fi 6 APs, a PoE+ managed switch, and a business-grade firewall/router.
- Multi-Site Deployments: Cloud-managed infrastructure is mandatory for centralised visibility, firmware management, and remote troubleshooting across distributed retail footprints.
Security Protocols
The era of open, unencrypted public WiFi is ending. While WPA2-Personal remains common, new deployments should leverage WPA3.
For guest networks utilising a captive portal, the underlying wireless transmission should still be encrypted. WPA3-SAE (Simultaneous Authentication of Equals) provides forward secrecy, mitigating offline dictionary attacks. If deploying an open network with a captive portal (often done for maximum compatibility), ensure client isolation is enabled at the AP level so devices cannot communicate with each other over the local subnet.
Implementation Guide
Deploying a secure, monetised café WiFi network requires a structured approach. Follow this vendor-neutral deployment sequence:
Step 1: Site Survey and Bandwidth Planning
Before purchasing hardware, conduct a physical site survey to identify RF interference (e.g., microwaves, structural steel) and determine optimal AP placement.
Calculate your bandwidth requirements. A standard rule of thumb is provisioning 2 Mbps per concurrent user for general browsing, and 5 Mbps if video streaming is common. For a café expecting 50 concurrent users, a minimum 100 Mbps symmetric connection is advised. If your venue hosts business events or requires guaranteed uptime, review our guide on What Is a Leased Line? Dedicated Business Internet for enterprise connectivity options. For detailed bandwidth calculations, see our Hotel WiFi Speed: What Guests Expect and How to Deliver It guide.
Step 2: Infrastructure Configuration
Install your router, managed switch, and access points. Configure your VLANs and firewall rules before connecting the APs. Ensure DHCP pools for the guest VLAN are sized appropriately (e.g., a /23 subnet providing 510 IP addresses) with short lease times (e.g., 2 hours) to prevent IP exhaustion during high footfall periods.
Step 3: Captive Portal Deployment
The captive portal is the critical interface between your network and your marketing database.
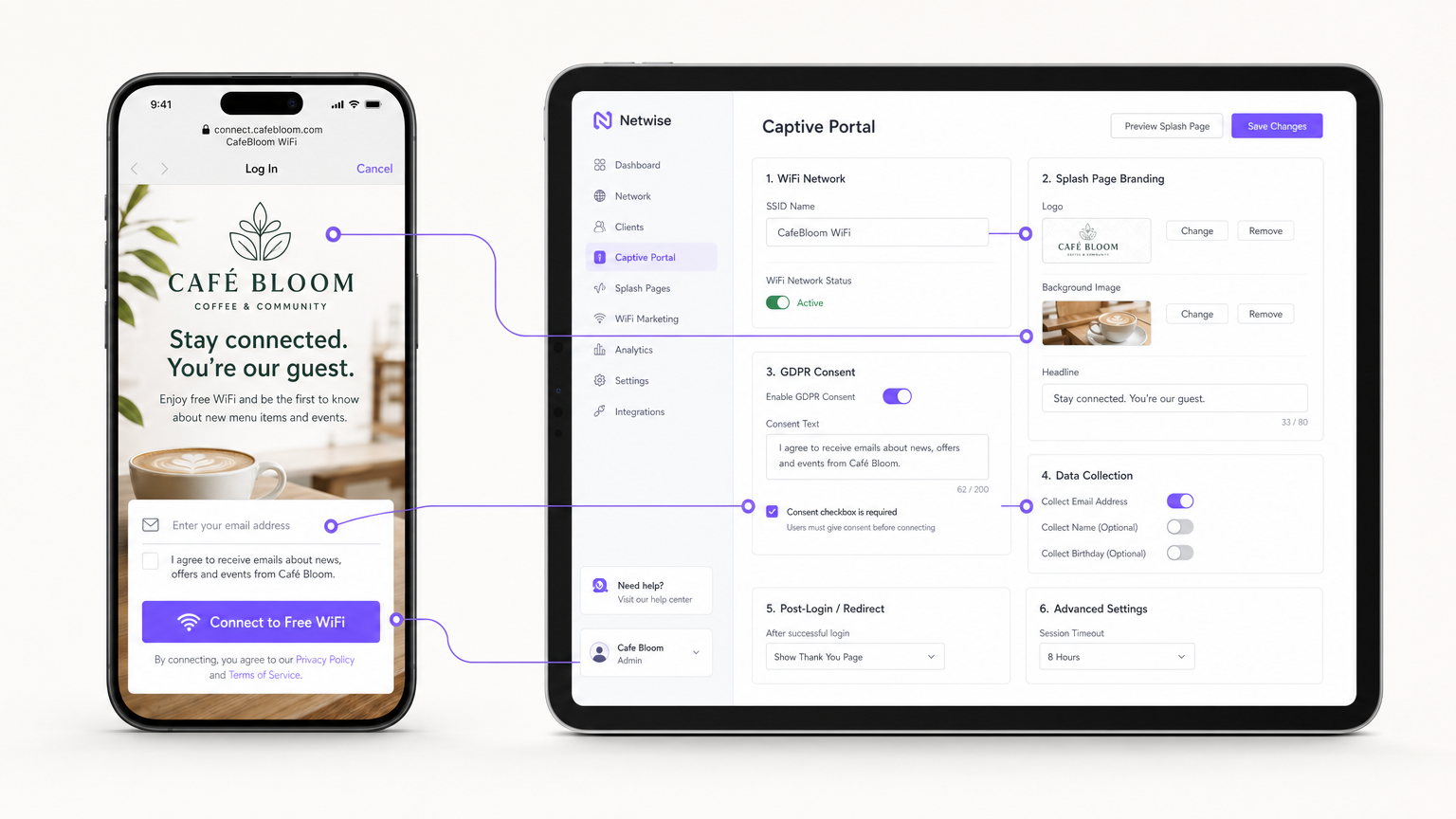
Instead of hosting portal servers on-premises, integrate your APs (via RADIUS or API) with a cloud-based Guest WiFi platform like Purple. Configure the splash page with your venue's branding, and set up the authentication methods (e.g., email, social login, or seamless profile-based authentication like OpenRoaming).
Step 4: Compliance and Consent Management
Configure the data collection fields. Under GDPR, marketing consent must be explicit, informed, and unambiguous. Ensure your captive portal features an unticked checkbox for marketing opt-ins. The platform must log the timestamp, IP address, MAC address, and the exact consent language displayed to the user to provide a verifiable audit trail.
Step 5: Marketing Automation Integration
Connect the WiFi platform to your CRM or utilise the platform's native WiFi Analytics tools to build automated campaigns. Set up triggers for:
- First-Time Visitors: Welcome email with a loyalty discount.
- Lapsed Visitors: Re-engagement offer after 30 days of absence.
- Frequent Visitors: VIP programme invitation.
Best Practices
- Enable Client Isolation: Always enable Layer 2 client isolation on the guest SSID. This prevents connected devices from seeing or communicating with each other, mitigating the risk of lateral malware movement or packet sniffing.
- Implement Quality of Service (QoS): Configure QoS rules on your router to prioritise operational traffic (POS, VoIP) over guest traffic. Implement per-client bandwidth limits (e.g., capping guests at 5 Mbps down/up) to prevent a single user from saturating the WAN link.
- Shorten DHCP Leases: In high-churn environments like cafés, set DHCP lease times to 1-2 hours rather than the standard 24 hours to prevent IP pool exhaustion.
- Leverage Profile-Based Authentication: For multi-site chains or Retail environments, implement seamless authentication protocols (like Passpoint/OpenRoaming) to allow returning users to connect automatically without re-authenticating at the portal, significantly improving the user experience while maintaining data tracking.
Troubleshooting & Risk Mitigation
| Failure Mode | Root Cause | Mitigation Strategy |
|---|---|---|
| IP Exhaustion | Guests cannot connect because the DHCP server has run out of available IP addresses. | Expand the subnet mask (e.g., from /24 to /23) and reduce DHCP lease times to 1-2 hours. |
| Co-Channel Interference | Multiple APs broadcasting on the same channel, causing high latency and packet loss. | Implement dynamic channel assignment on the wireless controller; avoid 2.4GHz channels other than 1, 6, and 11. |
| Captive Portal Bypass | Devices connect but do not trigger the splash page redirect, leaving users offline. | Ensure the firewall allows DNS and HTTP/HTTPS traffic to the portal's walled garden IP addresses before authentication. |
| Compliance Breach | Collecting emails via an open form without explicit consent logging. | Use a certified captive portal platform that natively handles GDPR consent logging and data retention policies. |
ROI & Business Impact
Transitioning from unmanaged WiFi to an enterprise guest network transforms IT infrastructure from a sunk cost into a measurable marketing asset.
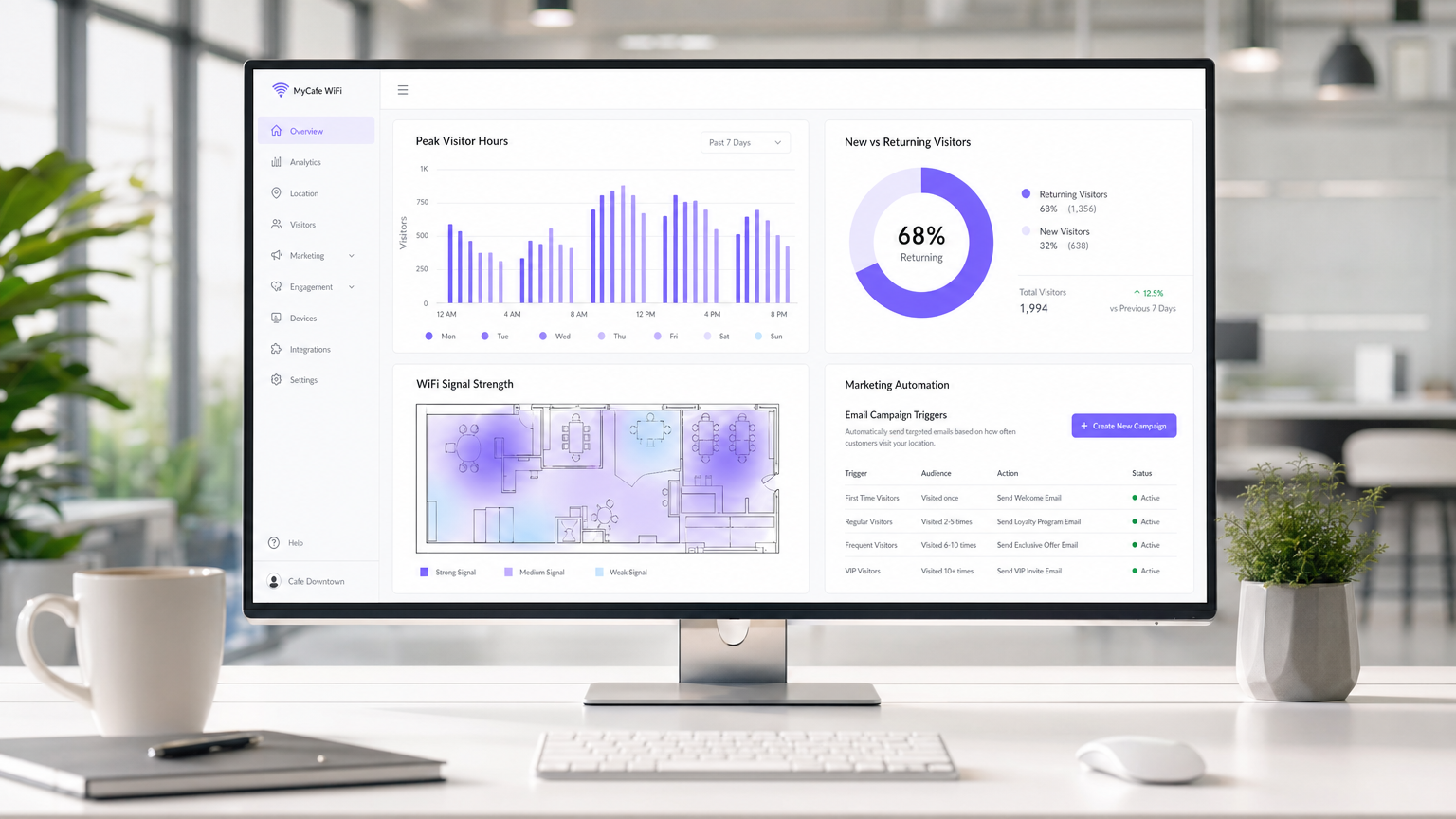
Measuring Success: The ROI of a café WiFi deployment is calculated through three primary metrics:
- Data Capture Rate: The percentage of connected users who opt-in to marketing communications. A well-optimised portal should achieve a 30-40% capture rate.
- Campaign Conversion: The footfall generated by automated email/SMS campaigns triggered by the WiFi platform. For example, tracking how many users return within 7 days of receiving a "we miss you" offer.
- Dwell Time Optimisation: Utilising analytics to correlate visitor dwell time with average transaction value, allowing operations teams to optimise seating and service speed.
By capturing first-party data and driving repeat visits through targeted marketing, a managed guest WiFi solution typically achieves ROI within 3-6 months of deployment, particularly in competitive Hospitality environments.
Key Terms & Definitions
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs. Used to securely separate guest traffic from operational traffic.
Essential for maintaining PCI DSS compliance and preventing guests from accessing back-office systems.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary mechanism for capturing user data, presenting terms of service, and securing GDPR marketing consent.
Client Isolation
A wireless security feature that prevents devices connected to the same AP from communicating with each other.
Crucial for public networks to prevent malicious users from scanning or attacking other guests' devices.
OFDMA (Orthogonal Frequency-Division Multiple Access)
A feature of Wi-Fi 6 that allows an AP to subdivide a channel to communicate with multiple devices simultaneously.
Solves the 'latency' problem in dense café environments where dozens of devices are competing for airtime.
PCI DSS
Payment Card Industry Data Security Standard. A set of security standards designed to ensure that all companies that accept, process, store or transmit credit card information maintain a secure environment.
The regulatory reason why network segmentation between POS and guest WiFi is legally required.
First-Party Data
Information a company collects directly from its customers and owns entirely.
The core asset generated by a guest WiFi platform, insulating venues from the deprecation of third-party cookies.
QoS (Quality of Service)
Technologies that manage data traffic to reduce packet loss, latency and jitter on the network.
Used to prioritize critical business traffic (like payment processing) over guest Netflix streaming.
Walled Garden
A restricted environment that controls user access to web content and services.
Required configuration on the firewall to allow unauthenticated users to access the captive portal and its associated resources (like social login APIs) before granting full internet access.
Case Studies
A growing independent café chain with 3 locations is experiencing network dropouts during peak hours. Their POS terminals frequently disconnect, and guests complain about slow speeds. They are currently using consumer-grade routers provided by their ISP, broadcasting a single SSID for both staff and guests.
- Replace consumer routers with a cloud-managed business gateway and Wi-Fi 6 access points at each location.
- Implement VLAN tagging: VLAN 10 for POS/Staff, VLAN 20 for Guests.
- Configure firewall rules to block inter-VLAN routing, securing the POS network.
- Set up QoS to prioritize VLAN 10 traffic over VLAN 20, and implement a 5 Mbps per-client bandwidth cap on the guest network.
- Deploy a centralized captive portal to manage guest access and collect GDPR-compliant marketing data.
A large conference centre café needs to provide seamless WiFi for returning delegates without forcing them to log in via the captive portal every day, while still tracking their presence for analytics.
Deploy a profile-based authentication system utilizing Passpoint (Hotspot 2.0) or OpenRoaming. Guests authenticate via the captive portal on their first visit, downloading a secure profile to their device. On subsequent visits, their device authenticates automatically via WPA2/3-Enterprise using EAP-TTLS, bypassing the splash page while still registering their MAC address and presence in the analytics dashboard.
Scenario Analysis
Q1. A retail café chain wants to implement a guest WiFi network. The marketing director insists on making email collection mandatory for access to maximize database growth. The IT director is concerned about compliance. What is the correct architectural approach?
💡 Hint:Consider the specific requirements of GDPR regarding 'freely given' consent.
Show Recommended Approach
Under GDPR, consent for marketing cannot be a precondition for service. The captive portal must allow users to access the WiFi without opting into marketing emails. The correct approach is to offer a clear, unticked checkbox for marketing consent, while allowing users to connect simply by accepting the terms and conditions. The marketing team should instead incentivize opt-ins by offering a clear value exchange (e.g., 'Sign up for 10% off your next coffee').
Q2. During peak hours (12:00 PM - 2:00 PM), guests at a busy city-centre café report that they can see the WiFi network with strong signal, but cannot connect or obtain an IP address. The network works perfectly in the morning and evening. What is the most likely cause and solution?
💡 Hint:Think about the lifecycle of a connection in a high-turnover environment.
Show Recommended Approach
The most likely cause is DHCP IP pool exhaustion. Because the café has high footfall but short dwell times, the default 24-hour DHCP leases are tying up IP addresses long after the guests have left. The solution is to reduce the DHCP lease time for the guest VLAN to 1 or 2 hours, and potentially expand the subnet from a /24 (254 addresses) to a /23 (510 addresses).
Q3. A venue operator wants to deploy a single unified network for both their EPOS systems and guest WiFi to save on hardware costs, using a standard consumer broadband router. What are the specific technical and business risks of this approach?
💡 Hint:Evaluate the scenario against PCI DSS requirements and wireless performance standards.
Show Recommended Approach
- Compliance Failure: A flat network violates PCI DSS requirements for isolating the Cardholder Data Environment, risking heavy fines and loss of card processing abilities. 2. Security Risk: Without client isolation and VLANs, guests can potentially access or attack the EPOS systems. 3. Performance Degradation: Consumer routers lack QoS to prioritize EPOS traffic, meaning guest streaming could cause payment processing to time out. 4. Device Limitations: Consumer routers cannot handle the concurrent connections typical in a café, leading to network crashes.



