eduroam and 802.1X: Secure WiFi Authentication for Higher Education
This authoritative technical reference guide explains the architecture, deployment, and security of eduroam and 802.1X authentication. Designed for IT managers and network architects, it covers practical implementation steps, EAP method selection, and how venue operators can securely support academic roaming.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Executive Summary
- Technical Deep-Dive: 802.1X and the eduroam Architecture
- The 802.1X Triangle
- The eduroam RADIUS Proxy Hierarchy
- EAP Methods: Security vs. Deployability
- Implementation Guide
- 1. Infrastructure Preparation
- 2. Certificate Management
- 3. Client Configuration (The CAT Tool)
- 4. VLAN Assignment and Segmentation
- Best Practices and Vendor-Neutral Recommendations
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For higher education institutions and the venues that host their students and staff, providing secure, seamless wireless connectivity is no longer a luxury—it is an operational mandate. The standard for this connectivity is eduroam, a global roaming service built on the IEEE 802.1X framework.
This guide provides IT managers, network architects, and venue operations directors with a comprehensive, vendor-neutral reference for understanding, deploying, and troubleshooting 802.1X and eduroam. We move beyond basic theoretical models to address the practical realities of enterprise campus WiFi, including certificate management, RADIUS proxy architecture, and integration with broader guest network strategies.
Whether you are upgrading an ageing university network or configuring a conference centre to support academic visitors, implementing 802.1X correctly mitigates significant security risks—particularly credential theft—while drastically reducing support overhead. For venues outside traditional higher education, understanding these standards is critical for evaluating commercial roaming federations like OpenRoaming, which share the same underlying architecture.
Technical Deep-Dive: 802.1X and the eduroam Architecture
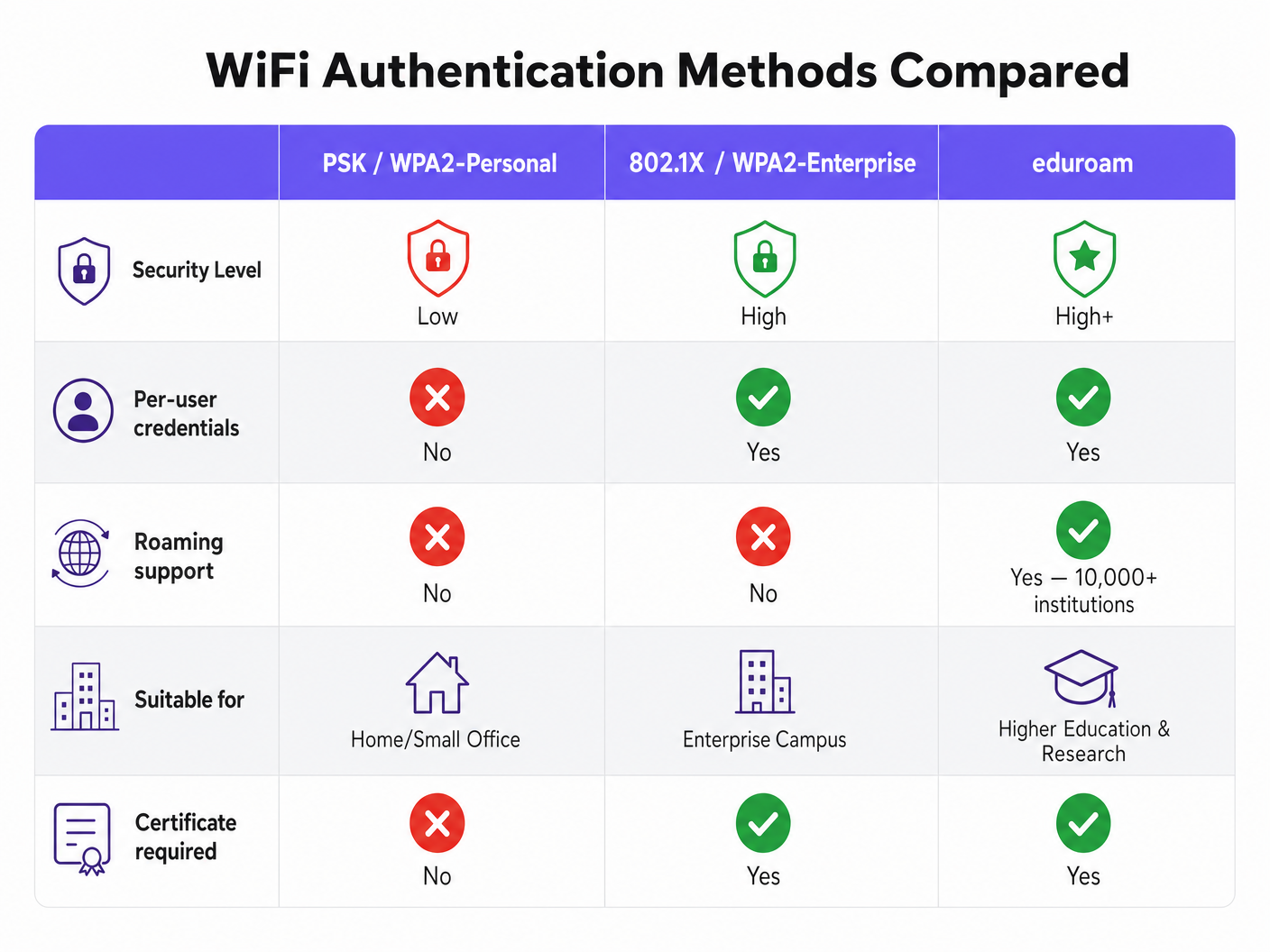
At its core, eduroam is an implementation of IEEE 802.1X, the standard for port-based network access control. While originally designed for wired networks, 802.1X forms the foundation of WPA2-Enterprise and WPA3-Enterprise security.
The 802.1X Triangle
The 802.1X framework relies on three distinct components interacting to authorise access:
- Supplicant: The client device (e.g., a student's laptop or smartphone) requesting network access.
- Authenticator: The network access device (e.g., a wireless access point or managed switch). It acts as a gatekeeper, blocking all traffic except authentication messages until the device is authorised.
- Authentication Server: The backend system that validates credentials, almost universally a RADIUS (Remote Authentication Dial-In User Service) server.
When a device connects, the Authenticator establishes a controlled port. It passes Extensible Authentication Protocol (EAP) messages between the Supplicant and the Authentication Server. If the credentials are valid, the server returns a RADIUS Access-Accept message, and the Authenticator opens the port for standard IP traffic.
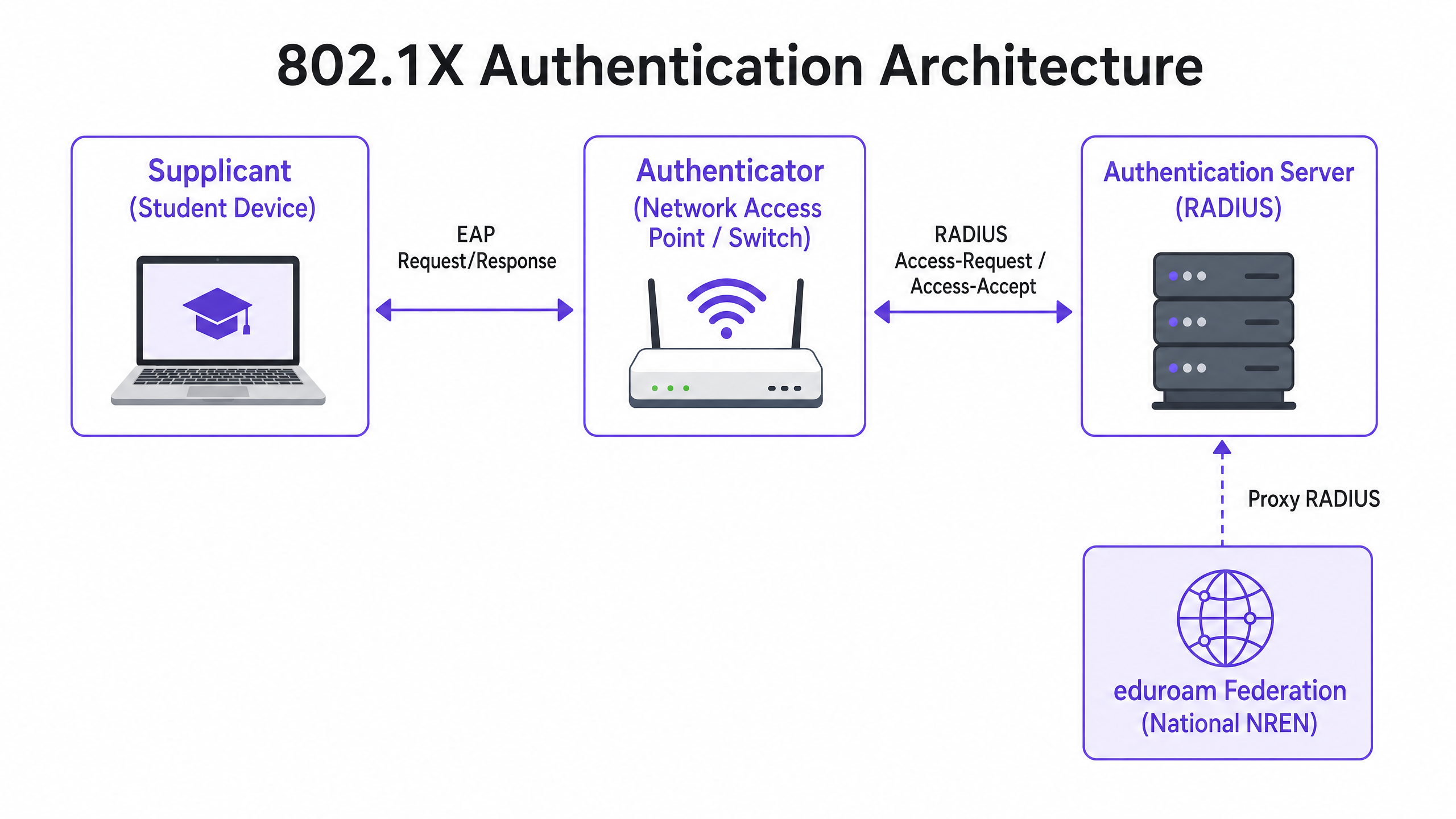
The eduroam RADIUS Proxy Hierarchy
What makes eduroam unique is its federated architecture. It allows users to authenticate at any participating institution using their home credentials, without the host institution needing a copy of those credentials.
This is achieved through a hierarchical RADIUS proxy chain. When a user from username@university.ac.uk connects to the eduroam SSID at a host venue:
- The user's device sends an authentication request in the format
username@university.ac.uk. - The host venue's RADIUS server examines the realm (the portion after the
@). Recognising it as an external domain, it proxies the request to the national top-level RADIUS server (operated by the National Research and Education Network, or NREN). - The national server routes the request to the home institution's RADIUS server (
university.ac.uk). - The home institution validates the credentials and returns an
Access-AcceptorAccess-Rejectmessage down the chain.
This entire process typically completes in under two seconds. Crucially, the user's password is never exposed to the host institution or the intermediate proxies; it is protected within an encrypted EAP tunnel established directly between the supplicant and the home RADIUS server.
EAP Methods: Security vs. Deployability
The choice of EAP method dictates how the encrypted tunnel is formed and how credentials are exchanged. The eduroam Policy Service Definition strongly restricts permissible methods to ensure security.
- PEAP (Protected EAP): The most common deployment. It establishes a TLS tunnel using a server-side certificate on the RADIUS server. The client then authenticates inside this tunnel, typically using MSCHAPv2 (username and password). It is relatively easy to deploy but vulnerable to rogue access point attacks if clients are not configured to strictly validate the server certificate.
- EAP-TLS: The gold standard for security. It requires mutual authentication, meaning both the RADIUS server and the client device must present valid certificates. While immune to credential phishing, it requires a robust Public Key Infrastructure (PKI) to issue and manage client certificates, making it more complex to deploy at scale.
Implementation Guide
Deploying 802.1X and eduroam requires careful coordination between network infrastructure, identity management, and client configuration.
1. Infrastructure Preparation
Ensure your wireless access points and controllers support WPA2-Enterprise/WPA3-Enterprise and 802.1X. Any modern enterprise-grade hardware (Cisco, Aruba, Juniper, etc.) will meet this requirement. You must also deploy a robust RADIUS infrastructure (e.g., FreeRADIUS, Cisco ISE, Aruba ClearPass) capable of handling the expected authentication load and proxying requests.
2. Certificate Management
For PEAP deployments, your RADIUS server requires a TLS certificate issued by a Certificate Authority (CA) trusted by your clients. Do not use self-signed certificates for production eduroam deployments. The certificate must be regularly renewed to prevent authentication outages.
3. Client Configuration (The CAT Tool)
The most common point of failure in eduroam deployments is client misconfiguration. Users manually connecting often fail to configure certificate validation, leaving them vulnerable to credential harvesting.
To mitigate this, institutions must use the eduroam Configuration Assistant Tool (CAT) or an MDM solution to distribute pre-configured profiles. These profiles automatically configure the correct EAP method, pin the expected RADIUS server certificate, and set the appropriate inner authentication protocols.
4. VLAN Assignment and Segmentation
A mature deployment utilises RADIUS attributes to dynamically assign VLANs based on the user's identity.
- Home Users: Assigned to internal VLANs with appropriate access to campus resources.
- Visiting Users: Assigned to a restricted guest VLAN with internet-only access.
This segmentation is vital for security and compliance, ensuring visiting devices cannot access sensitive internal networks.
Best Practices and Vendor-Neutral Recommendations
- Prioritise WPA3: For new deployments, enable WPA3-Enterprise to benefit from mandatory 192-bit encryption and improved protection against offline dictionary attacks.
- Enforce Certificate Validation: Mandate the use of configuration profiles (via CAT or MDM) to ensure supplicants strictly validate the RADIUS server certificate before transmitting credentials.
- Use RadSec: When configuring RADIUS proxy connections to the national federation, use RadSec (RADIUS over TLS) rather than plain UDP. This encrypts the proxy traffic and improves reliability over WAN links.
- Integrate with Guest Solutions: eduroam only serves users with academic credentials. You must maintain a separate, secure Guest WiFi solution for contractors, public visitors, and event attendees.
- Review Related Infrastructure: Ensure your underlying network is secure. Read our guide to Protect Your Network with Strong DNS and Security for more details. If deploying temporary infrastructure for university events, consult Event WiFi: Planning and Deploying Temporary Wireless Networks or the Portuguese version Event WiFi: Planeamento e Implementação de Redes Sem Fios Temporárias .
Troubleshooting & Risk Mitigation
When authentication fails, systematic troubleshooting is essential.
- Isolate the Failure Domain: Determine if the failure is local (affecting your own users on your own network), remote (affecting your users elsewhere), or inbound (affecting visitors on your network).
- Check the RADIUS Logs: The RADIUS server logs are the definitive source of truth. Look for
Access-Rejectmessages (indicating bad credentials or policy violations) or timeouts (indicating proxy connectivity issues). - Verify Certificate Validity: Ensure the RADIUS server certificate has not expired and that the full certificate chain is being presented to the client.
- Monitor Upstream Latency: High latency on the connection to the national RADIUS proxy can cause client timeouts, resulting in failed connections even with correct credentials.
ROI & Business Impact
For higher education institutions, the ROI of a proper eduroam deployment is measured in drastically reduced support tickets. By eliminating captive portals and manual password entry, IT helpdesks see a significant drop in connectivity-related calls. (Purple's commitment to this sector is evident; see Purple Signals Higher Education Ambitions with Appointment of VP Education Tim Peers ).
For commercial venues—such as those in Hospitality , Retail , Healthcare , or Transport —supporting eduroam Visitor Access (eVA) or similar federations like OpenRoaming provides a frictionless experience for high-value demographics. It ensures academic visitors can connect automatically and securely, improving satisfaction while allowing the venue to maintain strict network segmentation. If your venue requires dedicated bandwidth to support this, consider reading What Is a Leased Line? Dedicated Business Internet .
When planning network upgrades, integrating 802.1X capabilities ensures the infrastructure is ready for modern identity-driven networking, laying the groundwork for advanced WiFi Analytics and location-based services.
GuidesSlugPage.keyDefinitionsTitle
802.1X
An IEEE standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enterprise-grade WiFi security, replacing shared passwords (PSKs) with individualised authentication.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend server in an 802.1X deployment that actually checks the user's credentials against a directory (like Active Directory).
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections. It provides for the transport and usage of various authentication mechanisms.
The language spoken between the client device and the RADIUS server during the 802.1X handshake.
Supplicant
The client device (e.g., laptop, smartphone) or the software on that device attempting to authenticate to a network using 802.1X.
The entity requesting access. Its configuration (especially regarding certificate validation) is critical for security.
Authenticator
The network device (e.g., wireless access point, Ethernet switch) that facilitates the 802.1X authentication process by passing messages between the Supplicant and the Authentication Server.
The gatekeeper that blocks network traffic until the RADIUS server gives the green light.
PEAP (Protected Extensible Authentication Protocol)
An EAP method that encapsulates the EAP transaction within a TLS tunnel established using a server-side certificate, protecting the inner authentication (usually a password).
The most common authentication method for eduroam, balancing security with ease of deployment.
RadSec
A protocol for transmitting RADIUS data over TCP and TLS, rather than the traditional UDP.
Recommended for securing the proxy connections between institutions and the national eduroam federation, preventing interception of authentication traffic.
Realm
The portion of a user's identity following the '@' symbol (e.g., 'university.ac.uk' in 'user@university.ac.uk').
Used by RADIUS proxy servers to determine where to route the authentication request in a federated environment like eduroam.
GuidesSlugPage.workedExamplesTitle
A 400-room conference hotel adjacent to a major university frequently hosts academic symposiums. The IT Director wants to allow visiting academics to connect automatically without using the hotel's standard captive portal, but must ensure these visitors cannot access the hotel's corporate network or the standard guest network VLAN.
The hotel should implement eduroam Visitor Access (eVA) or join a commercial federation like OpenRoaming.
- The hotel configures a new SSID ('eduroam' or 'OpenRoaming') on their enterprise access points.
- The APs are configured to use WPA2-Enterprise/802.1X.
- The hotel deploys a local RADIUS server configured to proxy authentication requests for external realms to the national federation (for eduroam) or the OpenRoaming hub.
- Crucially, the local RADIUS server is configured to return a specific VLAN ID attribute in the
Access-Acceptmessage for all proxied authentications. - The access points place these authenticated users onto an isolated, internet-only VLAN, completely segmented from the hotel's corporate and standard guest traffic.
A university IT team notices a spike in compromised student accounts. Investigation reveals that students are connecting to a rogue access point broadcasting the 'eduroam' SSID at a local coffee shop. The rogue AP is using a self-signed certificate to harvest credentials via PEAP.
The IT team must immediately enforce strict certificate validation on all client devices.
- They must stop advising students to manually connect to the SSID and 'accept the certificate warning'.
- They deploy the eduroam Configuration Assistant Tool (CAT) for BYOD devices and update MDM profiles for managed devices.
- These profiles configure the supplicant to only trust the specific Certificate Authority (CA) that issued the university's RADIUS server certificate, and to verify the server's Common Name (CN).
- Once configured, if a student's device encounters the rogue AP, the EAP tunnel establishment will fail because the rogue certificate does not match the pinned CA/CN, preventing the transmission of credentials.
A retail chain wants to offer OpenRoaming across 50 locations using their existing guest WiFi infrastructure, which currently relies on an open SSID with a captive portal.
The retail chain must upgrade their network to support 802.1X and RADIUS proxying.
- The network team enables a new SSID broadcasting the OpenRoaming Consortium OI (Organization Identifier).
- They configure the access points to authenticate via 802.1X.
- They configure their central RADIUS server to proxy requests to the OpenRoaming federation hub.
- They ensure their internet backhaul can support the expected increase in automated connections, potentially upgrading to dedicated leased lines if necessary.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your university is deploying a new wireless network. The CISO mandates that credential phishing via rogue access points must be mathematically impossible. Which EAP method must you select?
GuidesSlugPage.hintPrefixConsider which method relies on passwords versus which relies entirely on cryptographic keys.
GuidesSlugPage.viewModelAnswer
You must select EAP-TLS. Unlike PEAP, which relies on a password inside a TLS tunnel, EAP-TLS requires mutual certificate authentication. Because the client device authenticates using a cryptographic certificate rather than a password, there are no credentials for a rogue access point to phish.
Q2. A visiting researcher from another university complains they cannot connect to your eduroam network. Your local users are connecting fine. You check your local RADIUS server logs and see the request arriving, but it times out before an Access-Accept is received. What is the most likely cause?
GuidesSlugPage.hintPrefixThink about the path the authentication request takes for a visiting user versus a local user.
GuidesSlugPage.viewModelAnswer
The most likely cause is a connectivity or latency issue between your local RADIUS server and the national NREN RADIUS proxy. Because local users authenticate directly against your server, they are unaffected. The visiting user's request must be proxied upstream, and a timeout indicates the response from the home institution is not returning in time.
Q3. You are a network architect for a retail chain located near a large university. You want to offer seamless WiFi to students using eduroam Visitor Access (eVA), but you must comply with PCI DSS for your point-of-sale terminals. How do you securely integrate eVA?
GuidesSlugPage.hintPrefixHow does 802.1X allow the network access point to differentiate traffic after authentication?
GuidesSlugPage.viewModelAnswer
You integrate eVA by configuring your RADIUS server to assign all successful eVA authentications to a dedicated, internet-only guest VLAN. The Access-Accept message from the RADIUS server must include the specific VLAN ID. This ensures student devices are completely segmented from the PCI-compliant VLAN used by the point-of-sale terminals, satisfying compliance requirements.



