Hotel WiFi Security: How to Protect Your Guests and Your Reputation
This authoritative guide provides IT managers and venue operations directors with a comprehensive framework for securing hotel WiFi networks. It covers essential technical implementations including network segmentation, robust authentication protocols, and compliance-driven Captive Portals to protect guest data and safeguard the venue's reputation.
- Executive Summary
- Technical Deep-Dive: Network Architecture and Segmentation
- VLAN Architecture
- Authentication and Encryption Standards
- Implementation Guide: Securing the Guest Onboarding Flow
- Captive Portal Design and Compliance
- Bandwidth Management and Traffic Shaping
- Best Practices and Industry Standards
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact
Executive Summary

For modern hospitality venues, guest WiFi is no longer merely an amenity—it is a critical operational utility. However, the convenience of ubiquitous connectivity introduces significant attack vectors. Unsecured guest networks are prime targets for threat actors seeking to intercept sensitive data, deploy malware, or leverage the hotel's infrastructure as a staging ground for broader intrusions. This technical reference guide provides a vendor-neutral, architecturally sound framework for securing hotel WiFi. We will explore the mandatory requirements for network segmentation, the transition to robust authentication standards like WPA3 and 802.1X, and the critical role of compliance-driven Captive Portals. Whether you are managing a boutique property or a global chain, implementing these controls is essential to mitigate risk, ensure regulatory compliance (such as PCI DSS and GDPR), and protect your brand's reputation.
Listen to our 10-minute technical briefing podcast for an executive overview:
Technical Deep-Dive: Network Architecture and Segmentation
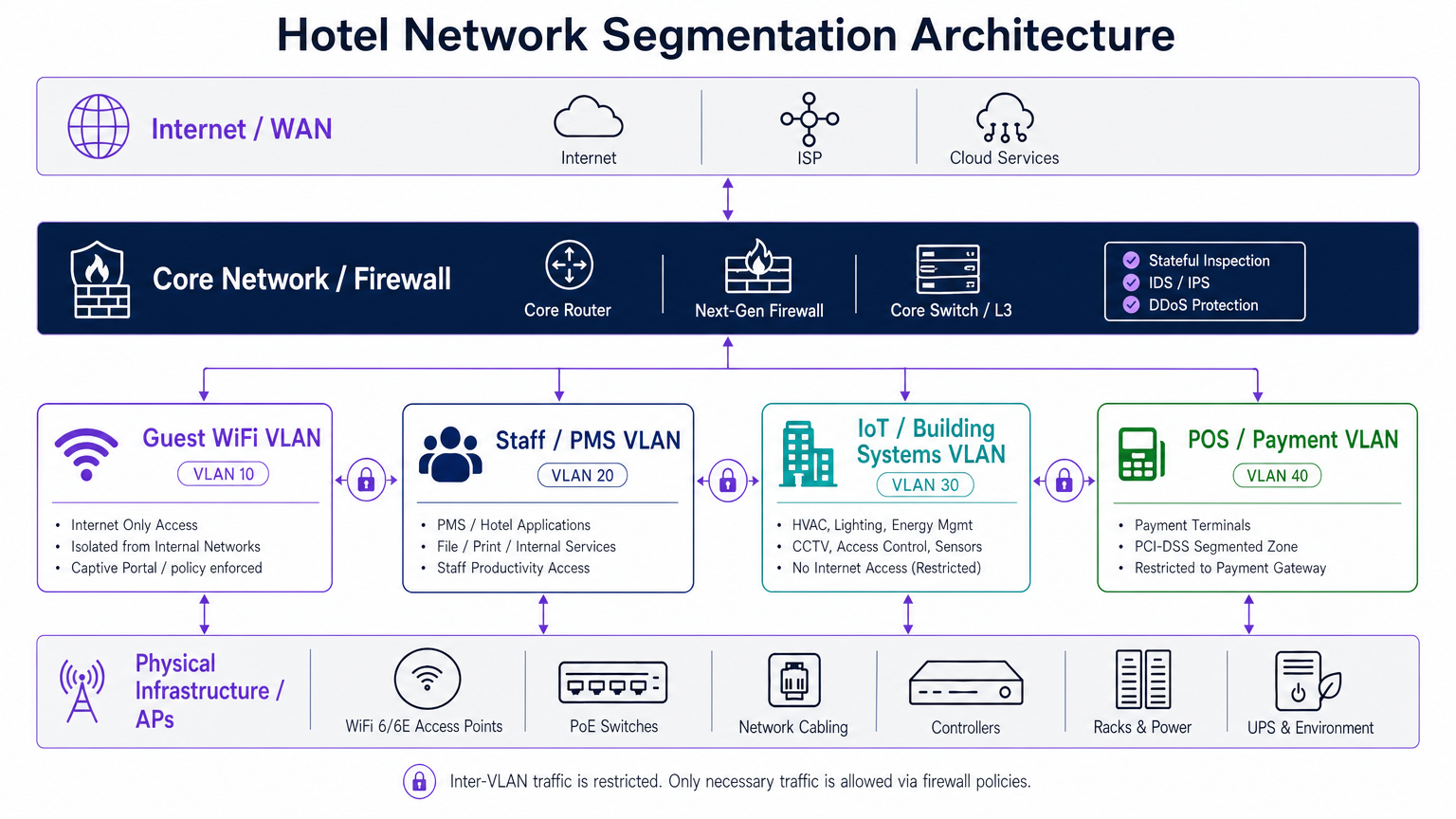
The foundational principle of hotel WiFi security is strict network segmentation. Deploying a flat network where guest traffic, staff applications, and IoT devices coexist is a critical vulnerability. A compromised guest device must never have a line of sight to the Property Management System (PMS) or point-of-sale (POS) terminals.
VLAN Architecture
A robust deployment requires logically isolating traffic into distinct Virtual Local Area Networks (VLANs), enforced by firewall policies with a default-deny stance for inter-VLAN routing.
- Guest WiFi VLAN: This zone must be restricted to internet-only access. It is imperative to enable Client Isolation (also known as AP Isolation) at the wireless controller or access point level. This prevents peer-to-peer communication between guest devices, neutralising lateral movement and man-in-the-middle (MitM) attacks within the guest network.
- Staff and PMS VLAN: Dedicated to internal operations, this VLAN hosts the PMS, back-office applications, and staff communication tools. Access should require strong authentication, preferably 802.1X.
- IoT and Building Systems VLAN: Modern hotels are heavily reliant on IoT—smart thermostats, IP cameras, and electronic door locks. These devices often lack robust native security and have long patch cycles. They must reside on a dedicated VLAN with strictly defined, outbound-only internet access (if required at all) and zero inbound access from other internal zones.
- POS and Payment VLAN: To comply with PCI DSS, payment terminals must be isolated in a dedicated VLAN, restricted exclusively to communicating with the payment gateway.
Authentication and Encryption Standards
The era of open, unencrypted guest networks is ending. While open networks maximise ease of use, they expose guests to eavesdropping.
- WPA3-SAE (Simultaneous Authentication of Equals): For guest networks, transitioning to WPA3 is highly recommended. WPA3-SAE provides individualised data encryption even on networks using a shared passphrase, mitigating offline dictionary attacks.
- 802.1X / RADIUS: For staff networks and corporate devices, 802.1X provides robust, identity-based authentication. This ensures that only authorised personnel and managed devices can access the internal network.
- Passpoint (Hotspot 2.0): For a seamless and secure guest experience, Passpoint allows compatible devices to automatically authenticate and connect to the network using enterprise-grade WPA2/WPA3-Enterprise security, without requiring a Captive Portal interaction every time. Purple's platform acts as a free identity provider for services like OpenRoaming under the Connect license, facilitating this secure, frictionless onboarding.
Implementation Guide: Securing the Guest Onboarding Flow
The Captive Portal is your first line of defence and the primary mechanism for enforcing compliance. It is not merely a branding exercise; it is a critical security control.
Captive Portal Design and Compliance
When deploying a Captive Portal, IT teams must ensure it meets several operational and legal requirements:
- Terms of Use (ToU) Acceptance: The portal must present clear Terms of Use that guests must explicitly accept before gaining network access. This limits the venue's liability for malicious actions performed by users on the network.
- GDPR and Privacy Compliance: If the portal collects user data (e.g., email addresses for marketing), it must comply with data protection regulations like GDPR. This requires explicit, opt-in consent mechanisms and clear privacy policies. Utilising a comprehensive Guest WiFi platform ensures these compliance requirements are met automatically.
- Walled Garden Configuration: Before authentication, users should only be able to access the Captive Portal itself and essential services (like DNS). Ensure the walled garden is strictly defined to prevent unauthorised internet access via DNS tunnelling or other bypass techniques.
Bandwidth Management and Traffic Shaping
Security also encompasses availability. A single compromised or malicious guest device can consume all available bandwidth, causing a denial-of-service (DoS) for other users and potentially impacting staff operations.
- Per-User Rate Limiting: Implement strict upload and download bandwidth limits per MAC address or authenticated session.
- Application Control: Utilise Layer 7 firewall rules to block or throttle high-bandwidth, non-essential applications (e.g., peer-to-peer file sharing) on the guest network.
Best Practices and Industry Standards

To maintain a secure posture, IT teams should adhere to the following vendor-neutral best practices:
- Continuous Rogue AP Detection: Implement Wireless Intrusion Prevention Systems (WIPS) to continuously monitor the RF environment for unauthorized access points (Rogue APs) and 'Evil Twin' networks designed to steal guest credentials. The system should automatically suppress these threats.
- Regular Firmware Updates: Establish a rigorous patch management schedule for all network infrastructure, including access points, switches, and firewalls. Vulnerabilities in network hardware are frequently exploited.
- DNS Filtering: Implement DNS-based content filtering on the guest network to block access to known malicious domains, command-and-control (C2) servers, and illegal content. This provides a crucial layer of defence against malware and phishing.
Troubleshooting & Risk Mitigation
Even with a robust architecture, incidents will occur. A proactive approach to monitoring and response is essential.
Common Failure Modes
- VLAN Bleed: Misconfigured switch ports or firewall rules can inadvertently allow traffic to route between isolated VLANs. Mitigation: Conduct regular configuration audits and penetration testing to verify network segmentation.
- Captive Portal Bypass: Attackers may attempt to bypass the captive portal using MAC spoofing or DNS tunnelling. Mitigation: Implement robust MAC authentication bypass (MAB) controls and monitor DNS traffic for anomalies.
- IoT Device Compromise: An unpatched smart TV or thermostat is compromised and used to scan the internal network. Mitigation: Strict isolation of the IoT VLAN and network behaviour anomaly detection.
ROI & Business Impact
Investing in robust WiFi security is not just a cost centre; it is a critical risk mitigation strategy with tangible business benefits.
- Brand Protection: A significant data breach originating from a hotel's WiFi network can cause irreparable damage to the brand's reputation, leading to lost bookings and decreased customer trust.
- Regulatory Compliance: Failure to comply with PCI DSS or GDPR can result in substantial fines and legal liabilities. A secure architecture simplifies compliance audits and reduces exposure.
- Operational Continuity: Preventing malware infections and DoS attacks ensures that critical hotel operations, such as the PMS and POS systems, remain available and performant.
- Data Monetisation: A secure, compliant captive portal enables the safe collection of first-party guest data. This data, when analysed through a robust WiFi Analytics platform, drives targeted marketing campaigns and improves the overall guest experience, directly impacting revenue.
By prioritising security in the WiFi deployment lifecycle, IT leaders in Hospitality and Retail can transform a potential vulnerability into a secure, value-generating asset.
Key Terms & Definitions
Client Isolation (AP Isolation)
A wireless network security feature that prevents devices connected to the same Access Point from communicating directly with each other.
Crucial for guest networks to prevent peer-to-peer attacks like ARP spoofing or unauthorized file sharing.
VLAN (Virtual Local Area Network)
A logical grouping of network devices that behave as if they are on a single, isolated LAN, regardless of their physical location.
The foundation of network segmentation, separating guest traffic from internal hotel systems.
Captive Portal
A web page that a user is prompted to view and interact with before access is granted to a public network.
Used to enforce Terms of Use, capture consent, and authenticate users.
WPA3-SAE
The latest WiFi security standard providing individualized encryption for users on a network with a shared password.
Protects guest data from eavesdropping even on 'open' networks.
802.1X
An IEEE standard for port-based network access control, requiring users to authenticate against a central server (like RADIUS) before gaining access.
The gold standard for securing staff and corporate networks.
Rogue AP
An unauthorized wireless access point connected to a secure network, often installed by an attacker to bypass security controls.
Requires continuous monitoring (WIPS) to detect and mitigate.
Evil Twin
A fraudulent WiFi access point that appears to be legitimate (e.g., using the hotel's SSID) to eavesdrop on wireless communications.
A common attack vector in public spaces, mitigated by strong authentication and WIPS.
PCI DSS
Payment Card Industry Data Security Standard; a set of security standards designed to ensure that all companies that accept, process, store or transmit credit card information maintain a secure environment.
Requires strict isolation of POS terminals from all other network traffic.
Case Studies
A 300-room resort is upgrading its network infrastructure. The current setup uses a single, flat network for guest WiFi, back-office staff, and the newly installed smart room thermostats. The IT Director needs to design a secure architecture that prevents guest devices from communicating with each other and isolates the thermostats from the internet.
- Implement VLAN Segmentation: Create three distinct VLANs: Guest (VLAN 10), Staff (VLAN 20), and IoT (VLAN 30).
- Configure Firewall Rules: Set a default-deny policy between all VLANs. Allow Staff VLAN access to the internet and specific internal servers. Allow Guest VLAN access only to the internet.
- Isolate IoT: Deny the IoT VLAN access to the internet and all other internal VLANs. Only allow specific, required traffic from the management server to the IoT VLAN.
- Enable Client Isolation: On the wireless controller, enable Client Isolation (AP Isolation) on the Guest SSID to prevent guest devices from communicating with each other.
A hotel chain wants to implement a new captive portal to collect guest email addresses for marketing purposes. They operate in the UK and must comply with GDPR. What are the critical technical and legal requirements for the portal configuration?
- Explicit Consent: The portal must include an unchecked checkbox for marketing opt-in. Pre-ticked boxes are not GDPR compliant.
- Clear Privacy Policy: A link to a clear, easily understandable privacy policy must be provided on the portal before the user submits any data.
- Separation of Terms: Acceptance of the Terms of Use (ToU) for network access must be separate from the marketing consent. Guests cannot be forced to accept marketing to use the WiFi.
- Secure Data Handling: All data submitted through the portal must be transmitted over HTTPS and stored securely in a compliant database.
Scenario Analysis
Q1. A VIP guest complains they cannot cast a video from their phone to the smart TV in their room. Both devices are connected to the 'Hotel_Guest' WiFi network. What is the most likely cause, and how should IT resolve it securely?
💡 Hint:Consider the security controls implemented on the guest network to prevent peer-to-peer communication.
Show Recommended Approach
The issue is caused by Client Isolation (AP Isolation) being enabled on the guest network, which correctly prevents devices from communicating directly. Disabling Client Isolation globally is a massive security risk. The secure resolution is to implement a dedicated casting solution (like Google Chromecast for Hospitality or similar enterprise gateways) that uses a secure, managed proxy to allow casting between specific devices in a single room without exposing the entire network.
Q2. During a network audit, you discover that the hotel's IP security cameras are on the same VLAN as the back-office staff computers. What are the risks, and what immediate action should be taken?
💡 Hint:Think about the patch frequency and inherent security of IoT devices compared to managed corporate laptops.
Show Recommended Approach
The risk is that if a vulnerability in an IP camera is exploited, the attacker gains direct access to the staff network, potentially compromising the PMS or sensitive files. The immediate action is to migrate the IP cameras to a dedicated IoT VLAN with strict access control lists (ACLs) that deny access to the staff VLAN and restrict internet access.
Q3. The marketing team wants to replace the current captive portal with a simple 'Click to Connect' button to reduce friction, removing the Terms of Use and Privacy Policy links. As the IT Director, how do you respond?
💡 Hint:Consider the legal and regulatory implications of providing public network access without terms or consent.
Show Recommended Approach
The request must be denied. Removing the Terms of Use exposes the hotel to legal liability for illegal activities conducted on the network (e.g., copyright infringement). Removing the Privacy Policy violates data protection regulations like GDPR if any data (even MAC addresses) is logged. A frictionless experience can be achieved securely using technologies like Passpoint/OpenRoaming, but initial consent and ToU acceptance are legally mandatory.



