How to Track Unique Devices on Enterprise Wireless Networks
This guide provides a comprehensive technical overview of tracking unique devices across enterprise wireless networks. It addresses modern challenges like MAC randomisation and details implementation strategies for venue operators and IT teams to maintain accurate analytics and user identification.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: The Evolution of Device Tracking
- The Legacy Approach: MAC Address Reliance
- The Paradigm Shift: MAC Randomisation
- Modern Architecture: Identity-Centric Tracking
- Implementation Guide: Deployment Strategies
- Step 1: Network Infrastructure Configuration
- Step 2: Captive Portal Design and Deployment
- Step 3: Analytics Platform Integration
- Best Practices for Enterprise Environments
- 1. Prioritise User Experience over Data Collection
- 2. Leverage Passpoint for High-Density Venues
- 3. Ensure Regulatory Compliance
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- ROI & Business Impact

Executive Summary
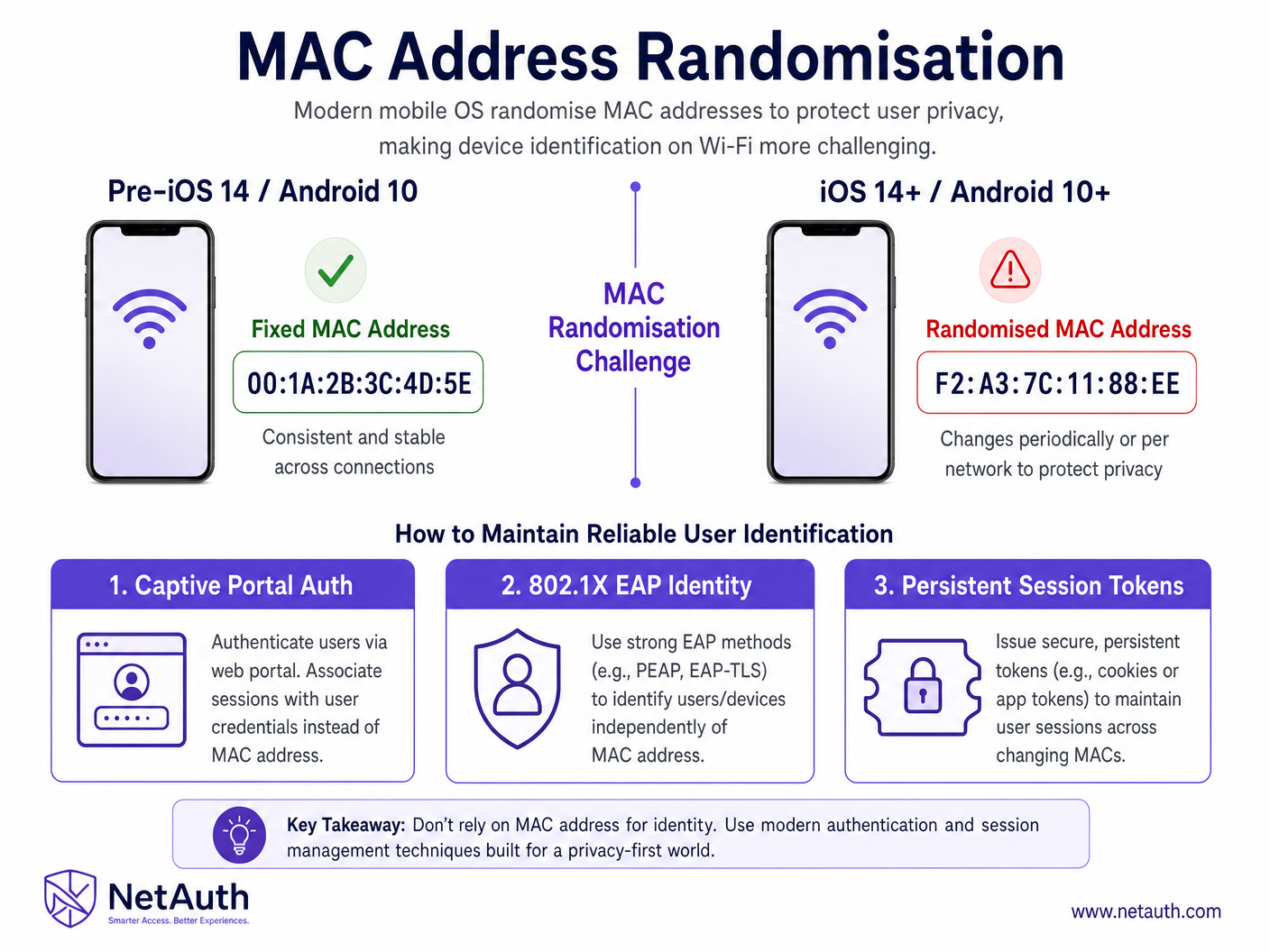
For enterprise IT leaders and venue operators, the ability to accurately track unique devices across a wireless network is foundational to both operational intelligence and marketing ROI. However, the landscape has fundamentally shifted. The widespread adoption of MAC address randomisation by major mobile operating systems (iOS 14+, Android 10+) has deprecated legacy tracking methods, requiring a strategic pivot in how we identify and authenticate users.
This technical reference guide outlines the modern architecture required to reliably track devices across enterprise environments—from expansive retail spaces to high-density stadiums. We will explore the technical mechanics of device identification, evaluate the impact of privacy-centric OS updates, and provide actionable deployment strategies. By transitioning from hardware-centric tracking to identity-centric authentication—leveraging captive portals, 802.1X, and persistent session tokens—organisations can maintain robust WiFi Analytics while ensuring compliance with stringent data protection regulations.
Technical Deep-Dive: The Evolution of Device Tracking
The Legacy Approach: MAC Address Reliance
Historically, enterprise networks relied heavily on the Media Access Control (MAC) address—a unique, hardware-encoded identifier assigned to every network interface controller (NIC). When a device probed for networks or connected to an access point, the network infrastructure logged this MAC address. This provided a persistent identifier that analytics platforms used to calculate dwell time, visit frequency, and cross-venue movement.
The Paradigm Shift: MAC Randomisation
To enhance user privacy and prevent passive tracking, Apple and Google introduced MAC randomisation. When a modern device scans for networks, it broadcasts a randomised, temporary MAC address. More critically, when connecting to a network, the device may use a different randomised MAC address per SSID, and in some configurations, rotate this address periodically (e.g., every 24 hours).
This fundamentally breaks analytics models that rely on the MAC address as a primary key. A single returning visitor might appear as multiple unique devices over a week, severely skewing metrics like footfall and loyalty.
Modern Architecture: Identity-Centric Tracking
To overcome MAC randomisation, the industry has shifted towards identity-centric tracking. This involves moving the primary identifier from the hardware layer (Layer 2) to the application layer (Layer 7).
1. Captive Portal Authentication
The most prevalent solution in public venues is the Guest WiFi captive portal. Instead of tracking the device, the network authenticates the user. When a user connects, they are redirected to a portal where they authenticate via email, social login, or SMS. The analytics platform (such as Purple) then associates the current session (and its temporary MAC address) with the authenticated user profile.
2. Persistent Session Tokens and Cookies
Once a user authenticates through the captive portal, the system drops a persistent cookie or session token on the device's browser. When the user returns to the venue, even if their MAC address has changed, the network can silently re-authenticate them via the token, linking the new MAC address to the existing user profile.
3. 802.1X EAP and Passpoint (Hotspot 2.0)
For seamless, secure connectivity, technologies like 802.1X and Passpoint (Hotspot 2.0) offer a robust solution. Devices are provisioned with a certificate or profile that automatically authenticates them to the network. The identity is tied to the certificate, completely bypassing the need for MAC address tracking. This is the foundation of modern initiatives like OpenRoaming.
![]()
Implementation Guide: Deployment Strategies
Deploying a resilient device tracking architecture requires careful coordination between the network infrastructure and the analytics platform.
Step 1: Network Infrastructure Configuration
Ensure your Wireless LAN Controllers (WLCs) or cloud-managed access points are configured to support advanced authentication methods.
- RADIUS Integration: Configure the infrastructure to forward RADIUS accounting data to your analytics platform. This data includes session start/stop times, data usage, and the current MAC address.
- Walled Garden Configuration: Ensure the captive portal domains and necessary authentication servers (e.g., social login APIs) are allowed in the pre-authentication walled garden.
Step 2: Captive Portal Design and Deployment
The captive portal is the critical juncture for identity capture.
- Frictionless Onboarding: Minimise the steps required to connect. How a wi fi assistant Enables Passwordless Access in 2026 highlights the importance of seamless authentication.
- Progressive Profiling: Don't ask for all data upfront. Collect basic contact info on the first visit, and request additional details (e.g., demographics, preferences) on subsequent visits.
Step 3: Analytics Platform Integration
Integrate the network data with a robust analytics platform like Purple.
- Identity Resolution Logic: The platform must be capable of resolving multiple MAC addresses to a single user profile based on authentication events and session tokens.
- Data Lake Synchronisation: Ensure the analytics data flows seamlessly into your CRM or data lake for broader business intelligence applications.
Best Practices for Enterprise Environments
1. Prioritise User Experience over Data Collection
A cumbersome authentication process will deter users, reducing your overall data capture rate. Strive for a balance. As discussed in How To Improve Guest Satisfaction: The Ultimate Playbook , a seamless WiFi experience is a critical component of overall guest satisfaction.
2. Leverage Passpoint for High-Density Venues
In environments like stadiums or large conference centres, captive portals can cause bottlenecks. Passpoint enables secure, automatic connection, providing a frictionless experience while ensuring reliable user identification.
3. Ensure Regulatory Compliance
Device tracking inherently involves personal data.
- GDPR / CCPA: Ensure explicit consent is obtained during the captive portal onboarding process. Provide clear mechanisms for users to opt-out or request data deletion.
- Data Minimisation: Only collect data that serves a specific business purpose.
Troubleshooting & Risk Mitigation
Common Failure Modes
- Inflated Unique Visitor Counts: If your analytics platform is not properly resolving randomised MAC addresses, your unique visitor metrics will be artificially high.
- Mitigation: Ensure your identity resolution logic is functioning correctly and that session tokens are being successfully deployed and read.
- Captive Portal Drop-off: High drop-off rates at the captive portal indicate friction in the onboarding process.
- Mitigation: Simplify the login options, optimise the portal for mobile devices, and review the walled garden configuration to ensure necessary resources are loading quickly.
- Inconsistent Tracking Across Venues: If a user visits multiple locations within a chain (e.g., a Retail brand), they should be recognised seamlessly.
- Mitigation: Implement a centralised authentication database and ensure consistent SSID naming and security configurations across all venues.
ROI & Business Impact
Accurate device tracking is not merely an IT metric; it is a fundamental business driver.
- Marketing Attribution: By accurately tracking users, marketing teams can attribute physical visits to digital campaigns. If a user receives an email offer and subsequently connects to the venue WiFi, the platform can close the attribution loop.
- Operational Efficiency: Understanding dwell times and foot traffic patterns allows venue operators to optimise staffing, layout, and resource allocation. This is particularly crucial in Hospitality and Healthcare environments.
- Enhanced Guest Experience: Recognising returning visitors allows for personalised engagement, driving loyalty and increasing lifetime value.
Key Definitions
MAC Randomisation
A privacy feature in modern operating systems where a device generates a temporary, random MAC address instead of its true hardware address when scanning for or connecting to networks.
IT teams must understand this as it fundamentally breaks legacy analytics systems that rely on MAC addresses for persistent device tracking.
Captive Portal
A web page that a user must view and interact with before access is granted to a public network. Often used for authentication, payment, or accepting terms of service.
This is the primary mechanism for shifting from hardware-centric tracking to identity-centric tracking in enterprise guest WiFi deployments.
802.1X
An IEEE standard for port-based network access control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Essential for secure, seamless authentication (like Passpoint) that bypasses the need for captive portals and is immune to MAC randomisation issues.
Passpoint (Hotspot 2.0)
A standard that enables mobile devices to automatically discover and connect to Wi-Fi networks without user intervention, using secure 802.1X authentication.
Crucial for high-density venues where frictionless onboarding is required, allowing for reliable tracking without captive portal bottlenecks.
Session Token
A unique identifier generated and sent from a server to a client to identify the current interaction session. Often stored as a cookie.
Used to maintain user identity across network reconnections, even if the device's MAC address has rotated.
Identity Resolution
The process of matching multiple identifiers (like various randomised MAC addresses) to a single, comprehensive user profile.
The core function of modern analytics platforms like Purple to ensure accurate visitor metrics.
Walled Garden
A limited environment that controls the user's access to web content and services before they have fully authenticated to the network.
Must be correctly configured to allow captive portals and third-party authentication services (like social logins) to function prior to granting full internet access.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The protocol used to pass authentication and session data (including MAC addresses and data usage) from the wireless controller to the analytics platform.
Worked Examples
A national retail chain with 500 locations is reporting a 300% increase in 'new' visitors over the past six months, while sales have remained flat. The IT Director suspects the WiFi analytics data is flawed.
- Audit the current tracking methodology: Determine if the analytics platform is relying solely on MAC addresses. 2. Implement Identity-Centric Tracking: Deploy a captive portal requiring user authentication (email or SMS) to access the Guest WiFi. 3. Enable Session Persistence: Configure the captive portal to drop a persistent cookie on the user's device. 4. Update Analytics Logic: Configure the analytics platform to merge profiles based on the authenticated identity, overriding the temporary MAC addresses. 5. Baseline New Metrics: Establish a new baseline for unique visitors based on authenticated users rather than device MACs.
A large stadium needs to track VIP attendees across different hospitality suites to optimise staffing and F&B services, but captive portals cause unacceptable delays during peak ingress.
- Deploy Passpoint (Hotspot 2.0): Implement Passpoint across the stadium network. 2. Pre-provision VIPs: Distribute Passpoint profiles to VIP ticket holders via the stadium app or email prior to the event. 3. Automatic Authentication: When VIPs arrive, their devices automatically and securely connect to the network using 802.1X EAP, without requiring a captive portal interaction. 4. Track via Identity: The network infrastructure logs the movement of these authenticated identities across the access points serving the hospitality suites.
Practice Questions
Q1. Your organisation is deploying a new Guest WiFi network across 50 retail locations. The marketing team requires accurate data on repeat visitor frequency. Which authentication strategy should you prioritize?
Hint: Consider the impact of MAC randomisation on tracking returning devices without explicit user identification.
View model answer
You should prioritize an identity-centric authentication strategy using a Captive Portal. By requiring users to authenticate (e.g., via email or social login) and deploying persistent session tokens, you can reliably identify returning visitors regardless of whether their device has rotated its MAC address. Relying on MAC addresses alone will result in inflated 'new visitor' metrics and inaccurate repeat frequency data.
Q2. A hospital IT director wants to track the movement of medical carts equipped with WiFi modules to optimize asset utilization. These modules do not support captive portal interaction. How can they ensure reliable tracking?
Hint: These are headless IoT devices, not user-facing smartphones.
View model answer
For headless devices like medical carts, the IT team should utilize 802.1X EAP-TLS authentication. By provisioning each cart's WiFi module with a unique digital certificate, the network can securely authenticate and identify the specific asset. The tracking is tied to the certificate identity, bypassing any potential issues with MAC randomisation (though enterprise IoT modules typically allow MAC randomisation to be disabled via MDM profiles).
Q3. During a busy conference, attendees are complaining that they have to log in to the captive portal every time their device wakes from sleep. What is the likely configuration issue?
Hint: Think about how the network recognizes a returning device that has already authenticated.
View model answer
The likely issue is a failure in session persistence. Either the captive portal is not configured to drop a persistent session token (cookie) on the device, or the session timeout value on the wireless controller/RADIUS server is set too aggressively. When the device wakes up, it may present a new MAC address; without a valid session token, the network treats it as a new device and forces re-authentication.