How Background App Refresh Degrades Public WiFi Performance
This technical guide examines the significant impact of background app refresh on public WiFi capacity and performance. It provides actionable, network-level mitigation strategies for IT managers to reclaim air time and improve the guest experience.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- The Anatomy of Background Traffic
- The Wi-Fi 6 Mitigation Myth
- Implementation Guide
- 1. Traffic Classification and Baselining
- 2. Developing the Block List
- 3. Policy Enforcement at the Controller Layer
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
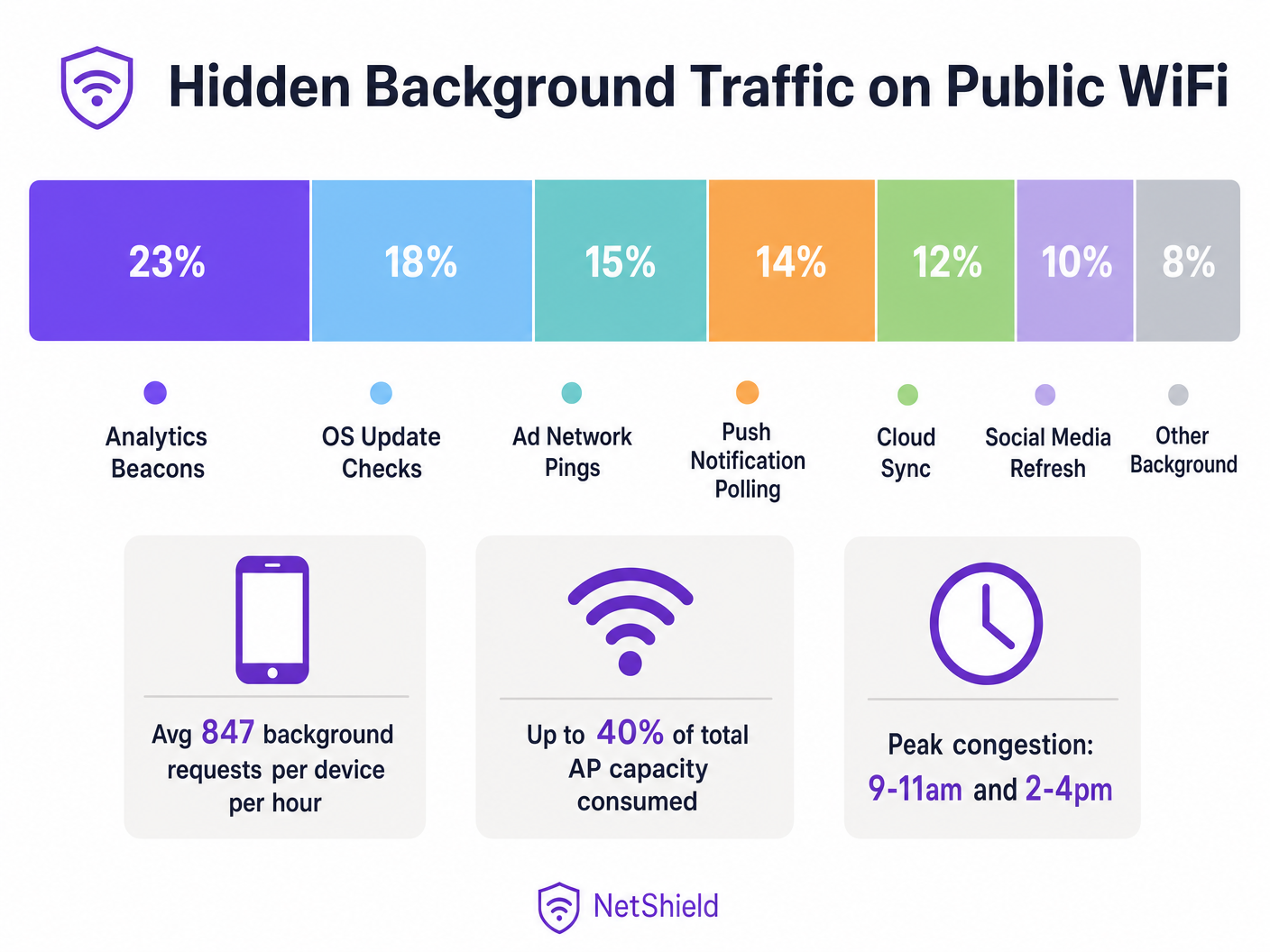
In high-density public wireless environments, up to 40% of access point capacity can be silently consumed by background app refresh traffic—analytics beacons, ad network pings, OS update checks, and push notification polling. This guide provides network architects and IT managers with a vendor-neutral blueprint for identifying, classifying, and mitigating background traffic at the network layer. By implementing targeted block lists and rate-limiting policies, venues can recover significant air time, defer costly hardware upgrades, and dramatically improve the connectivity experience for legitimate user traffic.
Technical Deep-Dive
The Anatomy of Background Traffic
Every smartphone connecting to your Guest WiFi network runs dozens of applications configured to execute background refresh cycles. These processes operate independently of user interaction, initiating connections to telemetry servers, cloud sync endpoints, and ad networks.
At the radio layer, the impact is disproportionate to the payload size. In an 802.11 network using CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance), every transaction requires a full association sequence. A 200-byte analytics beacon requires probe requests, authentication, association, and DHCP negotiation. In environments like Retail or Hospitality , this contention overhead rapidly depletes available air time.
The Wi-Fi 6 Mitigation Myth
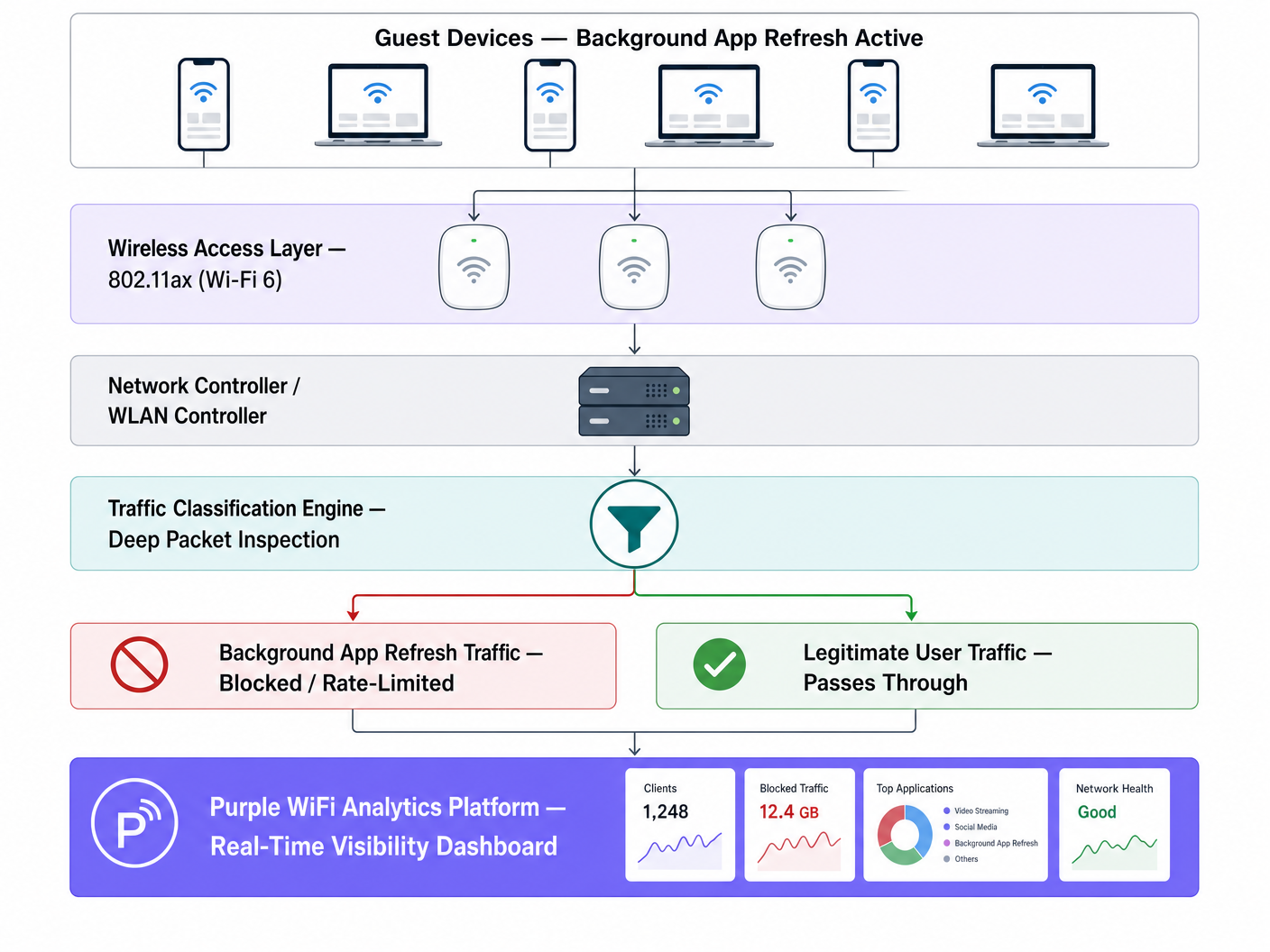
While Wi-Fi 6 (802.11ax) introduces OFDMA and BSS Colouring to manage high-density contention more efficiently, it does not solve the fundamental issue of unwanted payload delivery. The access point cannot distinguish between a user streaming a presentation and an app silently syncing diagnostic data. Network-level intervention via Deep Packet Inspection (DPI) remains essential.
Implementation Guide
1. Traffic Classification and Baselining
Before implementing policy changes, establish a baseline using your WiFi Analytics platform. Monitor traffic for at least five business days to identify peak background activity periods and top destination domains.
2. Developing the Block List
Implement DNS or IP-level blocking for known analytics and ad network endpoints. Start with community-validated lists (like OISD) and supplement with your baselining data.
Critical Exception: Do not block essential push notification services (e.g., Apple Push Notification Service on TCP 5223 or Google Firebase Cloud Messaging). Blocking these will disrupt core device functionality and generate user complaints.
3. Policy Enforcement at the Controller Layer
Apply classification rules at the WLAN controller rather than individual access points to ensure consistent policy enforcement.
Best Practices
- Rate-Limit OS Updates: Rather than blocking OS updates entirely, apply a strict rate limit (e.g., 1 Mbps per device) during peak operational hours.
- Implement QoS Marking: Use DSCP markings to deprioritise background traffic to the lowest traffic class, allowing it to transmit only when the channel is clear.
- Continuous Monitoring: Background endpoints evolve. Review and update your block lists quarterly.
Troubleshooting & Risk Mitigation
- Over-Blocking: Aggressive blocking without testing can break legitimate app functionality. Always test policies on a single AP group before estate-wide deployment.
- Ignoring the 5GHz/6GHz Split: Background traffic often clusters on 2.4GHz due to legacy device defaults. Ensure traffic analysis covers all bands. Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 provides further context on band management.
ROI & Business Impact
Reclaiming 30-40% of wasted air time is functionally equivalent to increasing your physical AP density by the same margin. For venues facing capacity constraints, network-level traffic management can defer significant capital expenditure on hardware refreshes while immediately improving guest satisfaction scores.
Listen to the full technical briefing:
Key Definitions
Background App Refresh
A mobile OS feature allowing apps to check for updates, sync data, and send telemetry without active user interaction.
The primary source of hidden air time consumption on high-density public networks.
CSMA/CA
Carrier Sense Multiple Access with Collision Avoidance; the protocol WiFi uses to manage access to the shared radio medium.
Explains why even small background payloads cause significant network overhead due to contention.
Air Time
The finite amount of time available for devices to transmit data over a specific radio frequency.
The critical resource depleted by background traffic, more important than raw bandwidth in high-density deployments.
Deep Packet Inspection (DPI)
Advanced network packet filtering that examines the data part of a packet to classify traffic types.
Required to distinguish between legitimate user traffic and background telemetry.
DSCP Marking
Differentiated Services Code Point; a mechanism for classifying and managing network traffic for Quality of Service (QoS).
Used to deprioritise background traffic so it only transmits when the network is idle.
BSS Colouring
A Wi-Fi 6 feature that identifies overlapping basic service sets to improve spatial reuse.
Improves efficiency but does not eliminate the need to block unwanted background payloads.
OFDMA
Orthogonal Frequency-Division Multiple Access; allows a single AP to communicate with multiple devices simultaneously.
A Wi-Fi 6 enhancement that mitigates but does not solve background traffic contention.
Rate Limiting
Controlling the rate of traffic sent or received on a network interface.
The recommended approach for managing essential but heavy background traffic, like OS updates.
Worked Examples
A 340-room four-star hotel is experiencing poor WiFi performance during peak check-in (3 PM - 6 PM) despite a recent Wi-Fi 6 hardware upgrade.
- Deploy traffic analysis via Purple WiFi Analytics.
- Identify that 38% of air time is consumed by background app refresh.
- Implement a targeted DNS block list for 847 known analytics and ad domains.
- Apply a 1 Mbps rate limit to identified OS update traffic during peak hours.
A regional retail chain with 60 stores reports that digital signage buffering occurs simultaneously with high guest WiFi usage.
- Baseline traffic across the estate.
- Discover iOS update checks on the guest SSID are saturating the WAN link.
- Deploy centralised policy via the WLAN controller to rate-limit Apple update servers to 512 Kbps per guest device.
- Prioritise digital signage MAC addresses via QoS.
Practice Questions
Q1. A stadium IT director wants to block all traffic to Apple and Google servers during a major sporting event to preserve bandwidth. What is the risk?
Hint: Consider essential device services that rely on persistent connections.
View model answer
Blocking all traffic to Apple and Google will break essential push notification services (APNS on TCP 5223 and Firebase Cloud Messaging). This will cause legitimate apps (like digital ticketing or emergency alerts) to fail. Instead, block specific analytics subdomains and rate-limit OS updates.
Q2. After deploying a Wi-Fi 6 upgrade, a conference centre still experiences severe latency during the morning keynote when 2,000 attendees arrive. Why didn't the hardware upgrade solve the issue?
Hint: Think about what Wi-Fi 6 handles well versus what it cannot control.
View model answer
Wi-Fi 6 improves efficiency (via OFDMA and BSS Colouring) but cannot distinguish between a user checking email and 2,000 devices simultaneously executing background app refreshes. The sheer volume of contention overhead still depletes air time. Network-level traffic classification is required.
Q3. When configuring QoS for a guest network, how should background traffic like cloud photo sync be handled?
Hint: It's not malicious, but it's not urgent.
View model answer
It should be classified and marked with a low DSCP value (e.g., Background/Scavenger class). This deprioritises the traffic, ensuring it only transmits when the network is idle, protecting real-time traffic like VoIP or point-of-sale transactions.