Cumplimiento de la normativa PIPEDA para WiFi de invitados en Canadá
This guide provides a definitive technical and operational reference for Canadian venue operators deploying guest WiFi under PIPEDA. It covers the OPC's meaningful consent framework, the accountability principle, enforcement precedents from the Tim Hortons and Google WiFi investigations, and the architectural changes required to meet the incoming Consumer Privacy Protection Act (CPPA) under Bill C-27. IT managers and compliance leads will find actionable captive portal design specifications, data minimisation requirements, and a clear roadmap for future-proofing against GDPR-scale penalties.
🎧 Escuchar esta guía
Ver transcripción
- Resumen ejecutivo
- Análisis técnico en profundidad: PIPEDA y el Captive Portal
- El mandato del consentimiento válido
- El precedente de Tim Hortons: una advertencia para la analítica de ubicación
- Guía de implementación: Creación de un flujo de registro conforme a la normativa
- Paso 1: Minimización de datos en el extremo
- Paso 2: Arquitectura de la interfaz de usuario del Captive Portal por niveles
- Paso 3: Integración de API y residencia de datos
- Paso 4: Cumplimiento bilingüe
- Paso 5: Programa de gestión de la privacidad
- Mejores prácticas y preparación para el Proyecto de Ley C-27 (CPPA)
- Resolución de problemas y mitigación de riesgos
- ROI e impacto empresarial
- Referencias

Resumen ejecutivo
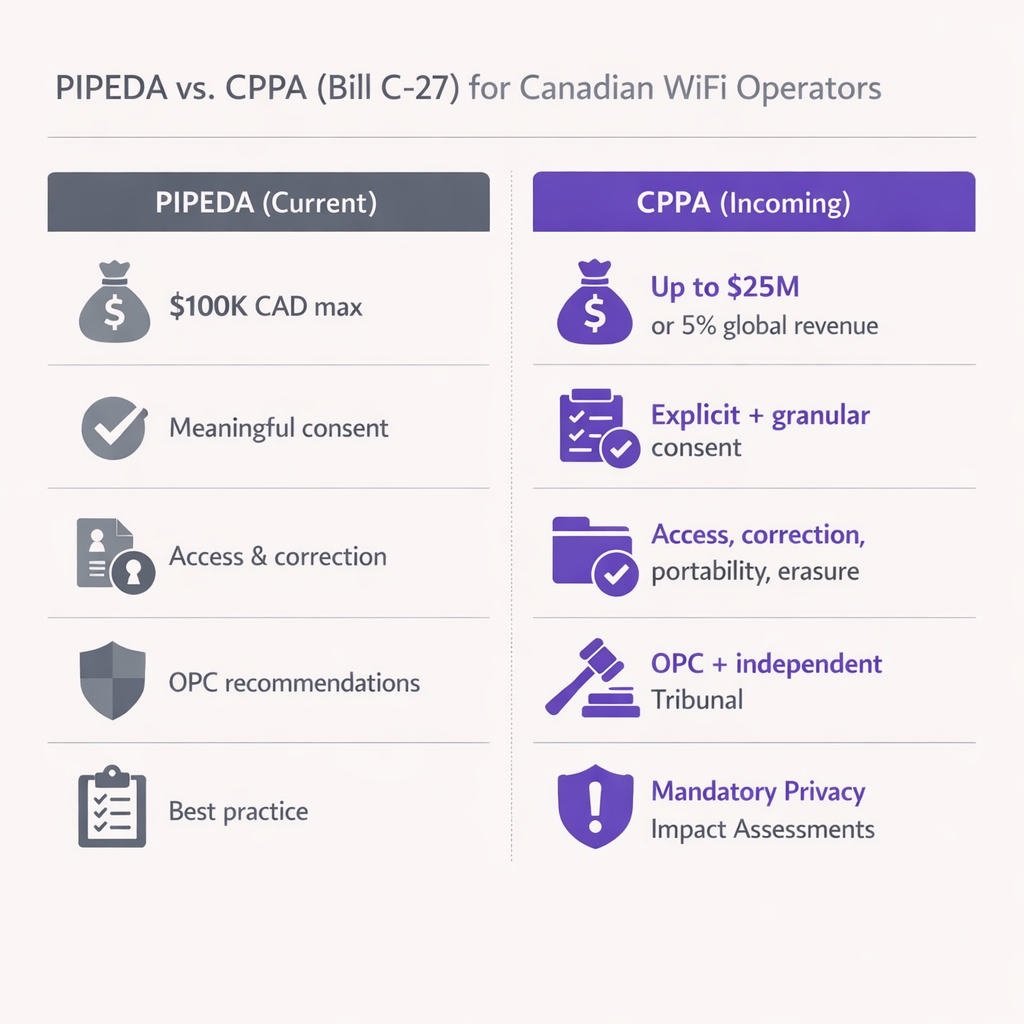
Para los operadores de recintos y líderes de TI canadienses, ofrecer WiFi para invitados ya no es solo una cuestión de conectividad: es un canal fundamental para la adquisición de datos. Sin embargo, el panorama normativo que regula cómo se recopilan y utilizan esos datos es cada vez más estricto. La Ley de Protección de Información Personal y Documentos Electrónicos (PIPEDA) exige requisitos estrictos para obtener un "consentimiento válido" antes de recopilar datos de los usuarios en los Captive Portals. Además, con la inminente Ley de Protección de la Privacidad del Consumidor (CPPA), que introducirá sanciones al estilo del GDPR (hasta 25 millones de dólares canadienses o el 5 % de los ingresos globales), el cumplimiento normativo es ahora una prioridad de gestión de riesgos a nivel directivo.
Esta guía proporciona una hoja de ruta técnica y operativa para arquitectos y directores de TI que implementan soluciones de WiFi para invitados en Canadá. Analizamos la postura de aplicación de la Oficina del Comisionado de Privacidad (OPC), los requisitos técnicos para el consentimiento por niveles y las medidas prácticas para preparar su arquitectura de red ante los próximos cambios legislativos. Tanto si opera en el sector Retail , Hostelería o Transporte , este documento traduce las obligaciones legales en especificaciones técnicas concretas.
Análisis técnico en profundidad: PIPEDA y el Captive Portal
La PIPEDA se aplica a la recopilación, uso y divulgación de información personal en el transcurso de actividades comerciales en Canadá. Para un Captive Portal de WiFi, la "información personal" va más allá de los nombres y las direcciones de correo electrónico; incluye las direcciones MAC de los dispositivos, la analítica de ubicación y el comportamiento de navegación. La Ley se estructura en torno a diez Principios de Información Justa recogidos en el Anexo 1, de los cuales el Principio 3 (Consentimiento), el Principio 2 (Identificación de fines), el Principio 4 (Limitación de la recopilación) y el Principio 1 (Responsabilidad) son los más relevantes para las implementaciones de WiFi para invitados.
El mandato del consentimiento válido
Las Directrices para la obtención de un consentimiento válido de la OPC, publicadas conjuntamente con los comisionados provinciales de Alberta y Columbia Británica en 2018, cambiaron radicalmente la forma en que los recintos deben diseñar sus flujos de registro. Ocultar las prácticas de recopilación de datos en un documento de Términos y Condiciones de 5000 palabras incumple explícitamente la normativa. Las directrices establecen siete principios, tres de los cuales son fundamentales a nivel arquitectónico para el diseño de un Captive Portal.
En primer lugar, énfasis en los elementos clave: la página de inicio debe mostrar de forma destacada qué datos se recopilan, con quién se comparten, los fines de la recopilación y cualquier riesgo residual significativo de daño. El uso de términos ambiguos como "mejora del servicio" es insuficiente; los fines deben ser específicos y distinguir entre los que son esenciales para la prestación del servicio y los que son opcionales.
En segundo lugar, elección granular: los usuarios deben poder aceptar o rechazar usos secundarios (marketing, elaboración de perfiles de comportamiento, analítica) de forma independiente al servicio principal (acceso WiFi). Vincular el consentimiento de marketing como condición para acceder a la red infringe directamente el Principio 3 de la PIPEDA, ya que exige un consentimiento que va más allá de lo necesario para prestar el servicio.
En tercer lugar, transparencia dinámica: el consentimiento no es un evento puntual. Si actualiza su motor de Analítica WiFi para rastrear nuevas métricas o compartir datos con un nuevo tercero, debe notificar a los usuarios existentes y obtener un nuevo consentimiento para el nuevo fin antes de que el cambio entre en vigor.
El precedente de Tim Hortons: una advertencia para la analítica de ubicación
En 2022, la investigación conjunta de la OPC sobre la aplicación móvil de Tim Hortons (Conclusiones de la PIPEDA n.º 2022-001) sentó un precedente histórico en el rastreo de ubicación que todo equipo de TI de un recinto debe comprender. La investigación reveló que la aplicación recopilaba datos GPS granulares incluso cuando estaba cerrada (más de 2700 veces en menos de cinco meses en el caso de un usuario), supuestamente para publicidad dirigida, un fin que en realidad nunca cumplió. La OPC dictaminó que esta recopilación carecía de una "necesidad legítima" y que el consentimiento obtenido era engañoso, ya que se informaba a los usuarios de que los datos solo se recopilaban mientras la aplicación estaba abierta.
Para los equipos de TI de recintos que implementan un Sistema de posicionamiento en interiores: Guía de UWB, BLE y WiFi , la lección es clara: no se pueden recopilar datos de ubicación en exceso "por si acaso". Si sus puntos de acceso sondean direcciones MAC no asociadas para generar mapas de calor de afluencia, debe anonimizar estos datos en el extremo utilizando hashes criptográficos rotativos, u obtener el consentimiento explícito antes de que el usuario se asocie con el SSID. La OPC evaluará si el fin declarado coincide con el uso real y si el volumen de datos recopilados es proporcional al beneficio obtenido.
Guía de implementación: Creación de un flujo de registro conforme a la normativa
La implementación de un Captive Portal que cumpla con la PIPEDA requiere coordinación entre los departamentos de ingeniería de redes, legal y marketing. El siguiente plan de acción se aplica a cualquier recinto que implemente WiFi para invitados en Canadá.
Paso 1: Minimización de datos en el extremo
Configure sus controladores WLAN para descartar los datos de carga útil innecesarios. Como se estableció en la investigación de Google Street View de 2011 (Conclusiones de la PIPEDA n.º 2011-001), la captura de datos de carga útil de redes no cifradas infringe la PIPEDA. Asegúrese de que sus servidores RADIUS y puertas de enlace del Captive Portal solo registren los atributos necesarios para la gestión de sesiones y la analítica consentida explícitamente. Para la analítica de presencia basada en direcciones MAC, implemente una función hash rotativa a nivel de AP o controlador para que la dirección MAC sin procesar nunca se escriba en el almacenamiento persistente.
Paso 2: Arquitectura de la interfaz de usuario del Captive Portal por niveles
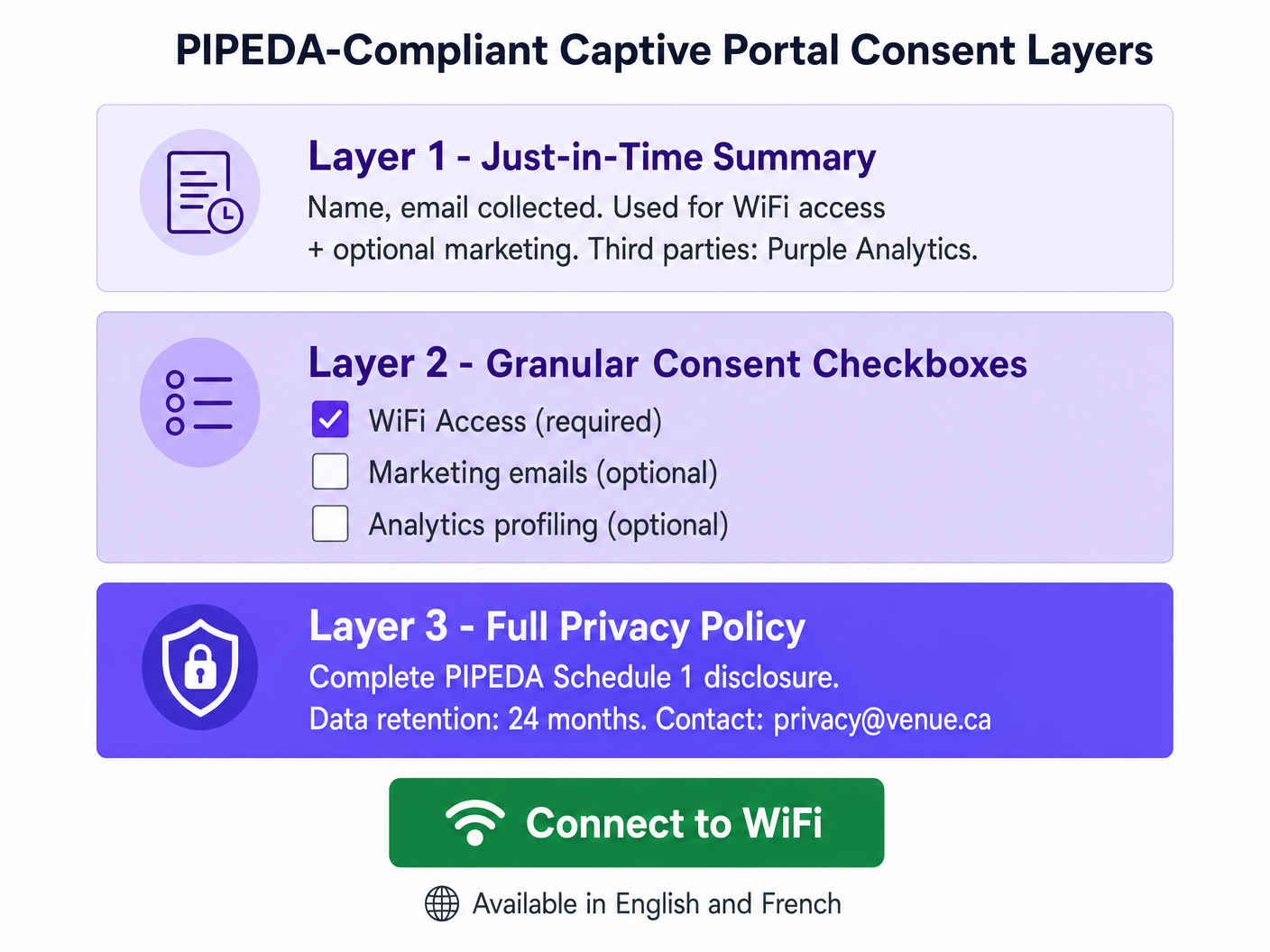
Diseñe la página de inicio utilizando un enfoque de tres niveles alineado con las directrices de avisos por niveles de la OPC. El Nivel 1 (la pantalla de inicio) presenta un resumen claro y en lenguaje sencillo: qué datos se recopilan, quién los procesa y con qué fines. El Nivel 2 presenta casillas de verificación de consentimiento granular (desmarcadas por defecto para todos los fines opcionales) que cubren las comunicaciones de marketing, la analítica de comportamiento y cualquier intercambio de datos con terceros que vaya más allá de lo necesario para la prestación del servicio. El Nivel 3 proporciona un hipervínculo a la política de privacidad completa, alojada en una página segura y adaptativa accesible desde cualquier dispositivo. Si su equipo de marketing necesita ayuda para redactar resúmenes concisos y con validez legal, considere utilizar IA generativa para textos y creatividades de Captive Portal o, para implementaciones en francés, IA générative pour le texte et les créatifs de Captive Portal .
Paso 3: Integración de API y residencia de datos
Al integrar su Captive Portal con un CRM o una plataforma de automatización de marketing, asegúrese de que los datos fluyan a través de API seguras y cifradas (TLS 1.2 como mínimo, preferiblemente TLS 1.3). Para las implementaciones en Canadá, priorice a los proveedores que ofrezcan residencia de datos local (por ejemplo, AWS Canada Central, ca-central-1) para mitigar los riesgos de transferencia transfronteriza. Esto es especialmente crítico para los recintos que operan en Quebec bajo la Ley 25, que exige una Evaluación de Impacto en la Privacidad (PIA) antes de transferir información personal fuera de Quebec y estipula que la jurisdicción receptora ofrezca una protección equivalente.
Paso 4: Cumplimiento bilingüe
Todos los avisos de consentimiento, políticas de privacidad e información sobre los derechos de los interesados deben estar disponibles tanto en inglés como en francés para los recintos que operan en Quebec. Este es un requisito tanto de la Ley 25 como de la Carta de la Lengua Francesa de Quebec. Para los recintos federales (aeropuertos, estaciones de tren, edificios federales), la prestación bilingüe es una expectativa básica en virtud de la Ley de Idiomas Oficiales.
Paso 5: Programa de gestión de la privacidad
El Principio de Responsabilidad de la PIPEDA (Principio 1) exige que su organización designe a un Responsable de Privacidad, mantenga políticas y procedimientos documentados, y sea capaz de demostrar el cumplimiento ante la OPC si se le solicita. Para los operadores con múltiples sedes (como una cadena nacional de Retail con más de 50 ubicaciones, cada una con un Captive Portal), esto implica un Programa de Gestión de la Privacidad (PMP) centralizado que cubra todas las sedes de forma coherente, con registros de auditoría para eventos de consentimiento, solicitudes de los interesados y plazos de conservación.
Mejores prácticas y preparación para el Proyecto de Ley C-27 (CPPA)
Aunque el Proyecto de Ley C-27 (la Ley de Protección de la Privacidad del Consumidor) se paralizó debido a la prórroga del Parlamento en enero de 2025, sus principios fundamentales representan el futuro inevitable de la legislación canadiense sobre privacidad. A principios de 2026, se espera que se presente en el Parlamento un nuevo proyecto de ley federal de privacidad que incorpore muchas de las disposiciones de la CPPA. El enfoque más prudente es tratar los controles a nivel de la CPPA como su objetivo de implementación actual.
Los cambios más significativos para los que debe prepararse son los siguientes. El aumento de las sanciones es la preocupación más inmediata: la CPPA introduciría multas de hasta 25 millones de dólares canadienses o el 5 % de los ingresos anuales globales, un cambio radical respecto al máximo actual de 100 000 dólares de la PIPEDA. Las Evaluaciones de Impacto en la Privacidad obligatorias serán necesarias para las actividades de procesamiento de alto riesgo, incluida la analítica de ubicación, la elaboración de perfiles de comportamiento y cualquier procesamiento que implique información personal sensible. Los derechos explícitos de portabilidad y supresión de datos requerirán flujos de trabajo automatizados capaces de eliminar el registro de un usuario de todos los sistemas (base de datos local, controlador en la nube, CRM posteriores) dentro de un plazo de respuesta definido. Los estándares de desidentificación serán más prescriptivos; asegúrese de que su plataforma de analítica aplique funciones hash a las direcciones MAC utilizando salts rotativos y que la reidentificación sea técnicamente inviable.
Para los operadores de recintos sanitarios, la intersección de la analítica WiFi y los datos de los pacientes genera obligaciones adicionales en virtud de la PIPEDA y la legislación provincial sobre privacidad sanitaria. Consulte nuestra guía del sector Sanidad para conocer las consideraciones de implementación específicas del sector.
Resolución de problemas y mitigación de riesgos
Modo de fallo: El portal de "todo o nada". Muchas implementaciones de Captive Portal heredadas presentan un único botón de "Acepto" que agrupa el acceso WiFi, el consentimiento de marketing y la elaboración de perfiles analíticos en un solo clic. Esto supone una infracción directa de la PIPEDA y es el modo de fallo más común que la OPC encuentra en las denuncias. La mitigación es sencilla: desvincule la autenticación de red de las suscripciones de marketing utilizando casillas de verificación separadas y claramente etiquetadas. El acceso a la red debe poder concederse sin ningún consentimiento secundario.
Modo de fallo: Rastreo silencioso de MAC. Algunas implementaciones registran las direcciones MAC de los dispositivos que pasan por el recinto pero que nunca se conectan al SSID, utilizando estos datos para generar analítica de afluencia. Según la PIPEDA, esto constituye una recopilación de información personal sin conocimiento ni consentimiento. La mitigación consiste en implementar compatibilidad con la aleatorización de MAC a nivel de AP y garantizar que todos los paneles de analítica de presencia agreguen y anonimicen los datos antes de su almacenamiento. Las direcciones MAC sin procesar de dispositivos no asociados nunca deben escribirse en el almacenamiento persistente.
Modo de fallo: Consentimiento obsoleto. Un recinto implementa un Captive Portal conforme a la normativa y, seis meses después, añade una nueva integración analítica que envía datos de sesión a una plataforma publicitaria de terceros. Los usuarios existentes que dieron su consentimiento a los términos originales no han dado su consentimiento a esta nueva divulgación. Esto infringe el requisito de la PIPEDA de obtener el consentimiento antes de cualquier nuevo fin. La mitigación consiste en implementar un sistema de control de versiones de consentimiento que active una solicitud de nuevo consentimiento para los usuarios existentes cuando se realicen cambios sustanciales en las actividades de procesamiento de datos.
Modo de fallo: Contratos inadecuados con terceros. Como se destacó en la investigación de Tim Hortons, un lenguaje contractual ambiguo con proveedores de servicios externos (que les permita utilizar los datos para sus propios fines) no constituye una protección adecuada. Asegúrese de que todos los acuerdos de procesamiento de datos con proveedores de analítica, proveedores de CRM y plataformas de marketing incluyan restricciones explícitas sobre el uso secundario, límites de retención de datos y controles de subencargados del tratamiento.
ROI e impacto empresarial
El cumplimiento normativo no es un centro de costes: es un multiplicador de confianza con resultados comerciales cuantificables. Los recintos que implementan flujos de consentimiento transparentes y centrados en el usuario informan sistemáticamente de mayores tasas de aceptación en los programas de marketing porque los usuarios sienten que tienen el control de sus datos. Un Captive Portal bien diseñado y conforme a la PIPEDA que explique claramente el intercambio de valor (WiFi gratis a cambio de una dirección de correo electrónico y un consentimiento de marketing opcional) genera conversiones a tasas significativamente más altas que un portal que oculta el consentimiento en jerga legal.
Desde el punto de vista de la mitigación de riesgos, el cálculo financiero es sencillo. Una sola medida de aplicación de la OPC, incluso bajo el máximo actual de 100 000 dólares de la PIPEDA, genera importantes daños a la reputación y costes legales que superan con creces la inversión en una implementación conforme a la normativa. Bajo el nuevo régimen de la CPPA, la exposición financiera aumenta a niveles que amenazan la viabilidad de la empresa. La estandarización en una plataforma de nivel empresarial como Purple, que proporciona gestión centralizada del consentimiento, registros de auditoría y flujos de trabajo automatizados para las solicitudes de los interesados, reduce la carga operativa de gestionar el cumplimiento de la privacidad en un entorno con múltiples sedes y proporciona el rastro de pruebas documentadas que la OPC espera ver.
Para los operadores de transporte que estén considerando implementaciones de vehículos conectados y WiFi en tránsito, se aplican los mismos principios de la PIPEDA. Consulte nuestra guía sobre Su guía de soluciones empresariales de Wi-Fi en el coche para conocer las consideraciones específicas de implementación.
Referencias
[1] Oficina del Comisionado de Privacidad de Canadá. "Ley de Protección de Información Personal y Documentos Electrónicos (PIPEDA)". priv.gc.ca.
[2] Oficina del Comisionado de Privacidad de Canadá. "Directrices para la obtención de un consentimiento válido". priv.gc.ca, mayo de 2018.
[3] Oficina del Comisionado de Privacidad de Canadá. "Principios de Información Justa de la PIPEDA — Anexo 1". priv.gc.ca.
[4] Oficina del Comisionado de Privacidad de Canadá. "Investigación conjunta sobre el rastreo de ubicación por parte de la aplicación de Tim Hortons (Conclusiones de la PIPEDA n.º 2022-001)". priv.gc.ca, junio de 2022.
[5] Oficina del Comisionado de Privacidad de Canadá. "Informe de conclusiones: Recopilación de datos WiFi de Google Inc. (Conclusiones de la PIPEDA n.º 2011-001)". priv.gc.ca, 2011.
[6] Commission d'accès à l'information du Québec. "Ley 25: Ley para modernizar las disposiciones legislativas en materia de protección de la información personal". cai.gouv.qc.ca.
[7] IAPP. "Lo que puede deparar 2026 para los esfuerzos de reforma de la privacidad en Canadá". iapp.org, febrero de 2026.
Términos clave y definiciones
PIPEDA (Personal Information Protection and Electronic Documents Act)
Canada's federal private-sector privacy law governing the collection, use, and disclosure of personal information in commercial activities. Structured around ten Fair Information Principles in Schedule 1. Applies to all provinces except Alberta, British Columbia, and Quebec, which have substantially similar provincial legislation.
The primary compliance framework for any Canadian venue offering guest WiFi. IT teams encounter PIPEDA when designing captive portals, configuring analytics platforms, and responding to data subject requests.
Meaningful Consent
The OPC's standard for valid consent under PIPEDA, requiring that individuals genuinely understand what they are consenting to — specifically: what data is collected, who receives it, the purposes of collection, and any meaningful risks of harm. Consent buried in lengthy T&Cs, or obtained through a single bundled 'I Accept' button, does not meet this standard.
The central compliance requirement for captive portal design. Every element of the splash page UI must be evaluated against this standard.
Captive Portal
A network gateway that intercepts HTTP/HTTPS traffic from newly associated WiFi clients and redirects them to a web page for authentication, consent collection, and/or payment before granting internet access. Technically implemented via WLAN controller redirect rules, DNS spoofing, or a dedicated gateway appliance.
The primary point of consent collection for guest WiFi deployments. The design of the captive portal UI directly determines PIPEDA compliance status.
MAC Address (Media Access Control Address)
A 48-bit hardware identifier assigned to a network interface controller, used to uniquely identify a device at the data link layer (Layer 2). Under PIPEDA, MAC addresses are personal information because they can be used to identify an individual's device and, by extension, their movements and behaviour.
Encountered in WiFi analytics deployments, probe-based footfall counting, and session logging. Must be anonymised or handled with explicit consent.
OPC (Office of the Privacy Commissioner of Canada)
The independent federal authority responsible for overseeing compliance with PIPEDA and the Privacy Act. The OPC investigates complaints, conducts audits, publishes guidance, and can apply to the Federal Court to enforce its recommendations. Current maximum fine under PIPEDA is $100,000 CAD per violation.
The primary regulatory body IT teams must satisfy. OPC findings are publicly published and serve as binding precedents for compliance interpretation.
CPPA (Consumer Privacy Protection Act)
The proposed replacement for PIPEDA, introduced as part of Bill C-27 in 2022. Would introduce GDPR-scale penalties (up to $25M CAD or 5% of global revenue), mandatory Privacy Impact Assessments, explicit data portability and erasure rights, and a new independent enforcement tribunal. Bill C-27 stalled due to parliamentary prorogation in January 2025; a successor bill is anticipated in 2026.
The future compliance target for Canadian venue operators. IT teams should begin implementing CPPA-level controls now to avoid costly remediation when the legislation passes.
Law 25 (Quebec Act to Modernize Legislative Provisions as Regards the Protection of Personal Information)
Quebec's provincial privacy legislation, which imposes requirements that exceed PIPEDA. Key provisions include mandatory Privacy Impact Assessments before new projects involving personal information, explicit consent for cross-border data transfers, French-language consent notices, and fines up to $25M CAD or 10% of worldwide turnover. Fully in force as of September 2023.
Applies to all venues operating in Quebec. IT teams must implement enhanced consent flows, bilingual notices, and PIAs for any Quebec deployment.
Privacy Impact Assessment (PIA)
A structured risk assessment process that evaluates the privacy implications of a new project, system, or data processing activity before deployment. Identifies data flows, assesses risks to individuals, and documents mitigation measures. Currently a best practice under PIPEDA; mandatory under Quebec's Law 25 for new projects involving personal information; expected to become mandatory federally under the CPPA.
Required before deploying new analytics features, location tracking systems, or third-party data integrations. Provides the documented evidence trail the OPC expects to see in an enforcement scenario.
Layered Notice
A consent architecture that presents privacy information at multiple levels of detail: a brief, prominent summary for the average user; granular options for those who want more control; and a full privacy policy for those who want complete information. Recommended by the OPC as the preferred method for obtaining meaningful consent in digital environments.
The architectural pattern that all PIPEDA-compliant captive portals should implement. Directly addresses the OPC's concern that information buried in lengthy T&Cs is functionally invisible to users.
Accountability Principle (PIPEDA Schedule 1, Principle 1)
The requirement that an organisation is responsible for personal information under its control and must designate an individual (a Privacy Officer) accountable for compliance. Includes implementing policies and practices, training staff, and being able to demonstrate compliance to the OPC on request.
The organisational governance requirement that underpins all other PIPEDA compliance activities. Multi-site venue operators must have a documented Privacy Management Programme covering all locations.
Casos de éxito
A 300-room hotel in Toronto wants to offer free guest WiFi and use sign-up data to drive repeat bookings and promotional email campaigns. The hotel's current captive portal uses a single 'I Accept' button that links to a 4,000-word Terms and Conditions document. The IT director has been asked to assess compliance risk and redesign the flow before the next OPC audit cycle.
The existing single-button flow is non-compliant and must be replaced with a three-layer architecture. On the WLAN controller (e.g., Cisco Catalyst Centre or Aruba Central), configure the captive portal redirect to the new splash page hosted over HTTPS. Layer 1 of the splash page presents a plain-language summary panel: 'We collect your name, email address, and device identifier to provide WiFi access. We share this data with Purple (our WiFi analytics provider). You can optionally receive promotional emails from us.' Layer 2 presents two checkboxes: Checkbox A (pre-checked, mandatory): 'I agree to the WiFi Terms of Use and Privacy Policy.' Checkbox B (unchecked, optional): 'I would like to receive promotional offers and news from [Hotel Name].' Layer 3 provides a hyperlink 'Full Privacy Policy' opening the complete PIPEDA-compliant policy in a new tab. The policy must specify: data categories collected (name, email, MAC address, session timestamps), purposes (WiFi access delivery; marketing if opted-in), third parties (Purple, email marketing platform), retention period (12 months for marketing, 90 days for session logs), and a privacy contact email. The hotel must also configure its CRM integration to tag records with consent status, so that only users who checked Checkbox B receive marketing communications. Implement a consent versioning system so that if the hotel adds a new analytics partner in future, existing users are prompted to re-consent.
A large shopping centre operator in Montreal wants to deploy a WiFi analytics system to generate zone-level footfall heatmaps across 120,000 square feet of retail space. The proposed system uses WiFi probe requests from unassociated devices (i.e., phones that have not connected to the network) to estimate visitor counts and dwell times. The CTO wants to understand the PIPEDA and Law 25 compliance requirements before procurement.
This deployment involves processing personal information (MAC addresses are personal information under PIPEDA) without the knowledge or consent of the individuals whose devices are being probed. Under both PIPEDA and Quebec's Law 25, this requires careful architectural controls. The compliant approach is as follows: First, conduct a Privacy Impact Assessment (PIA) before procurement, as required by Law 25 for any new project involving personal information. The PIA must assess the necessity and proportionality of the data collection. Second, implement MAC address anonymisation at the access point or controller level using a rotating cryptographic hash (e.g., HMAC-SHA256 with a key that rotates every 24 hours). This ensures that the same device cannot be tracked across days, and that the raw MAC address is never written to persistent storage. Third, configure the analytics platform to store and display only aggregate, zone-level counts — not individual device trajectories. The dashboard should show 'Zone A: 450 visitors, avg dwell 8 minutes' rather than individual movement paths. Fourth, post clear, visible signage at all venue entrances disclosing that WiFi-based analytics are in use for footfall measurement, with a QR code linking to the full privacy notice. This satisfies the 'openness' principle and provides constructive notice. Fifth, for the connected WiFi network (the SSID guests can join), implement a standard three-layer captive portal as described in the hotel scenario above. The Law 25 requirement for French-language consent notices applies to all captive portal text.
A national retail chain with 85 stores across Canada is preparing for the incoming CPPA regime. Their current PIPEDA compliance is adequate, but the CTO wants to understand what architectural changes are needed to meet CPPA-level requirements, particularly around data subject rights, de-identification, and the increased penalty exposure.
The transition from PIPEDA to CPPA compliance requires three primary architectural investments. First, implement automated data subject rights workflows. The CPPA introduces explicit rights to data portability and erasure. The chain's WiFi platform must expose an API endpoint that, when triggered by a verified data subject request, can: (a) export all personal data associated with a given email address or device identifier in a machine-readable format (JSON or CSV); and (b) purge that record from the local captive portal database, the cloud analytics platform, and all downstream CRM and marketing automation systems simultaneously. This must be achievable within a defined SLA — 30 days is the CPPA's proposed response window. Second, upgrade de-identification protocols. Current PIPEDA guidance on de-identified data is relatively permissive. The CPPA will introduce a higher bar: de-identified data must be processed in a manner that makes re-identification 'not reasonably foreseeable.' For MAC-based analytics, this means implementing rotating hash keys (as described above) and ensuring that the analytics platform cannot be used to re-identify individuals even by the operator. Third, conduct mandatory Privacy Impact Assessments for all high-risk processing activities. For a retail chain, this includes any deployment involving location analytics, behavioural profiling for targeted advertising, or data sharing with advertising technology platforms. PIAs should be documented and retained as evidence of accountability. The chain should also review all third-party data processing agreements and update them to include CPPA-compliant clauses covering data retention, sub-processor restrictions, and breach notification timelines.
Análisis de escenarios
Q1. Your venue's current captive portal collects name, email, and device MAC address. The splash page has a single 'Connect to WiFi' button that, when clicked, is deemed acceptance of the Terms and Conditions (which include consent to receive marketing emails). A user complains to the OPC. What specific PIPEDA violations has your venue committed, and what is the minimum remediation required?
💡 Sugerencia:Consider PIPEDA Principles 1, 2, 3, and 4. Focus on the bundling of consent and the adequacy of the notice provided.
Mostrar enfoque recomendado
The venue has committed at least three violations. First, under Principle 3 (Consent), the bundling of marketing consent with WiFi access is non-compliant — users cannot be required to consent to marketing as a condition of receiving the service. Second, under Principle 2 (Identifying Purposes), the purposes are not clearly identified at the point of collection; the user must read the full T&Cs to discover the marketing purpose. Third, the consent is not 'meaningful' under the OPC's 2018 guidelines because key elements (what data, why, who gets it) are not prominently displayed. Minimum remediation: redesign the portal with a three-layer architecture, decouple marketing consent into a separate unchecked checkbox, and add a plain-language summary to the splash page. The venue must also implement a consent versioning system and update its Privacy Management Programme documentation.
Q2. You are the IT director of a conference centre in Vancouver. A vendor proposes deploying a WiFi analytics system that tracks the MAC addresses of all devices in the venue — including those that never connect to the WiFi network — to generate session-level movement analytics for exhibitors. The vendor says the data is 'de-identified' because they hash the MAC addresses. Is this deployment compliant with PIPEDA? What additional controls, if any, are required?
💡 Sugerencia:Consider whether hashing alone constitutes de-identification under PIPEDA. Think about the difference between a static hash and a rotating hash, and the concept of re-identification risk.
Mostrar enfoque recomendado
The deployment is potentially compliant but requires additional controls. A static hash of a MAC address is not true de-identification under PIPEDA because the same device will always produce the same hash, allowing cross-session tracking and, potentially, re-identification if the hash table is compromised or if the MAC address is known. To achieve genuine de-identification, the hash key must rotate at regular intervals (e.g., every 24 hours), ensuring that the same device cannot be tracked across sessions. Additionally, the venue must post clear, visible signage at all entrances disclosing that WiFi-based analytics are in use, satisfying the Openness principle. The analytics platform must store and display only aggregate, zone-level data — not individual device trajectories. If the vendor intends to share session-level data with exhibitors (third parties), this constitutes a disclosure of personal information and requires explicit consent from users who have connected to the network, or robust anonymisation that makes re-identification 'not reasonably foreseeable.' A Privacy Impact Assessment is strongly recommended before deployment.
Q3. A hotel chain with properties in Ontario, Alberta, and Quebec is standardising its guest WiFi platform. The CTO wants a single consent flow that works across all provinces. The legal team has flagged that Quebec's Law 25 imposes additional requirements. Design the minimum viable consent architecture that satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is forward-compatible with the incoming CPPA.
💡 Sugerencia:Identify the highest common denominator across all three regimes. Consider language, PIA requirements, consent granularity, and data subject rights.
Mostrar enfoque recomendado
The minimum viable architecture should be designed to the highest standard across all applicable regimes, which means treating Law 25 as the baseline. The consent flow must: (1) Present a bilingual (English and French) splash page with a plain-language just-in-time summary; (2) Provide separate, unchecked-by-default checkboxes for WiFi access terms, marketing consent, and analytics profiling; (3) Link to a full privacy policy available in both languages, specifying data categories, purposes, third parties, retention periods, and data subject rights contact; (4) Support data subject rights for access, correction, and deletion — with automated workflows capable of purging records across all systems within 30 days; (5) Implement rotating-hash MAC anonymisation at the edge. Before deploying the system in Quebec, conduct a Privacy Impact Assessment as required by Law 25. For CPPA forward-compatibility, ensure the platform supports data portability export in machine-readable format and can generate audit trails of all consent events. This single architecture satisfies PIPEDA in Ontario and Alberta, Law 25 in Quebec, and is well-positioned for CPPA compliance when the legislation passes.
Q4. Six months after deploying a compliant captive portal, your marketing team wants to add a new integration that sends guest session data (email, visit frequency, dwell time) to a third-party programmatic advertising platform for retargeting campaigns. Existing users consented to the original terms, which did not mention this platform. What are your obligations under PIPEDA before activating this integration?
💡 Sugerencia:Focus on the 'new purpose' requirement under PIPEDA and the OPC's guidance on dynamic consent. Consider what constitutes a 'significant change' to privacy practices.
Mostrar enfoque recomendado
Under PIPEDA, sharing personal information with a third-party advertising platform for retargeting constitutes a new purpose that was not anticipated in the original consent. Before activating the integration, you must: (1) Update your privacy policy to disclose the new third party and the retargeting purpose; (2) Notify all existing users of the material change to your privacy practices — this can be done via email to those who provided their address during WiFi sign-up; (3) Obtain fresh consent from existing users for the new purpose before their data is shared with the advertising platform — this means presenting them with a new opt-in opportunity, not assuming their original consent covers the new use; (4) Ensure that users who do not consent to the new purpose continue to receive WiFi access without interruption; (5) Review the data processing agreement with the advertising platform to ensure it includes adequate protections against secondary use by the platform. Failing to obtain fresh consent before activating the integration would constitute a disclosure of personal information for a purpose beyond what was originally consented to — a direct violation of PIPEDA Principle 3.



