Train WiFi: La Guía Completa para Operadores Ferroviarios y Pasajeros
Esta guía autorizada desglosa la arquitectura, los desafíos de implementación y las oportunidades comerciales del WiFi para pasajeros en trenes. Diseñada para líderes sénior de TI y operaciones, cubre la agregación de backhaul, la segmentación de red y cómo convertir una obligación de cumplimiento en análisis de pasajeros accionables.
🎧 Escuchar esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: La Arquitectura de Tres Capas
- Capa 1: Backhaul WAN y Agregación
- Capa 2: La Red a Bordo y Segmentación
- Capa 3: Acceso de Pasajeros y Hardware de Cabina
- Guía de Implementación: Despliegue y Cumplimiento
- ROI e Impacto Comercial: Transformando Datos en Inteligencia
- Escuche el Informe
Resumen Ejecutivo
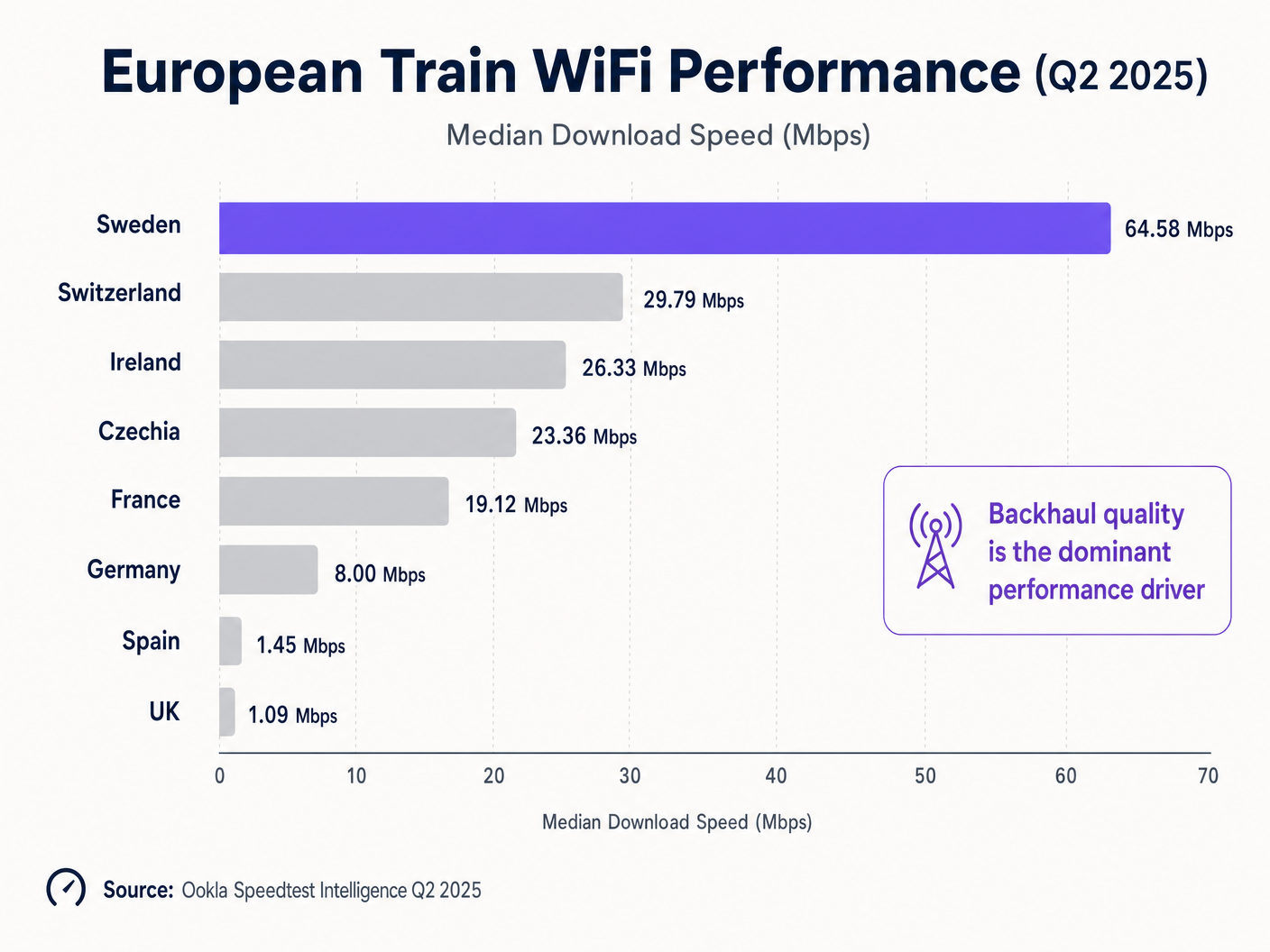
Para los operadores ferroviarios, el Train WiFi de alta calidad ha pasado de ser un beneficio para el pasajero a una infraestructura operativa esencial. La brecha entre las implementaciones de primera clase y las heredadas es evidente: los datos del segundo trimestre de 2025 de Ookla muestran que Suecia ofrece velocidades de descarga medianas de 64,58 Mbps, mientras que el Reino Unido se estanca en 1,09 Mbps [1]. Esta diferencia de 59 veces no es principalmente un problema tecnológico; es un fallo de arquitectura y estrategia de inversión.
Esta guía proporciona un plan neutral para directores de TI, arquitectos de red y líderes de operaciones de recintos. Diseccionamos la arquitectura de tres capas necesaria para una conectividad a bordo resiliente, exploramos el requisito de seguridad crítico de la segmentación de red y demostramos cómo plataformas como Guest WiFi transforman los datos de conexión brutos en inteligencia comercial accionable. Ya sea que gestione una ruta interurbana de alta velocidad o un servicio de cercanías regional, los principios de agregación de backhaul y captura de datos compatible con GDPR siguen siendo idénticos.
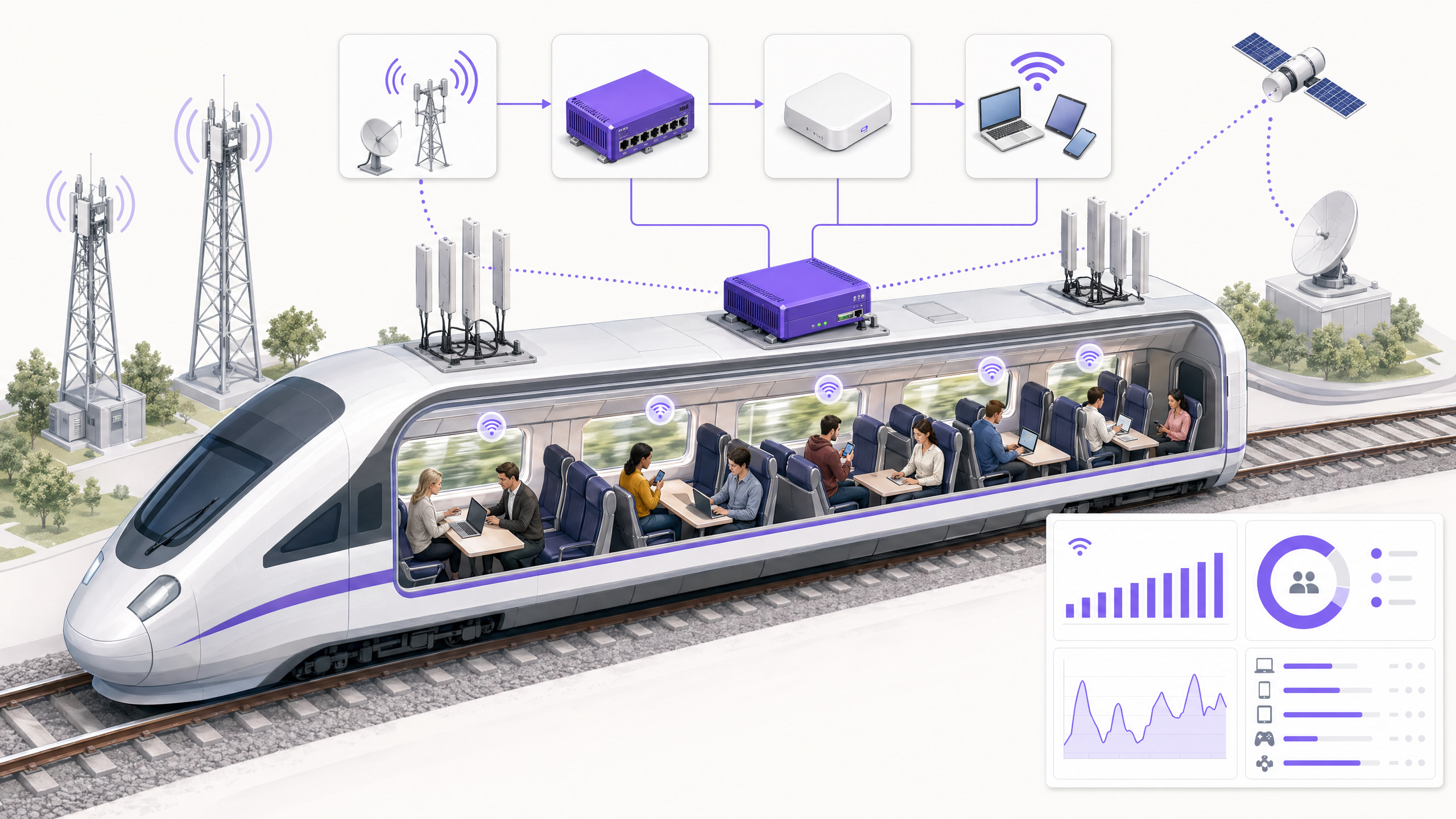
Análisis Técnico Detallado: La Arquitectura de Tres Capas
Una implementación moderna de Train WiFi es fundamentalmente diferente de las implementaciones estáticas de recintos que se encuentran en Retail o Hospitality . La red debe mantener la persistencia de la sesión mientras se mueve a 300 km/h, realizando traspasos entre celdas junto a la vía y penetrando en material rodante fuertemente aislado.
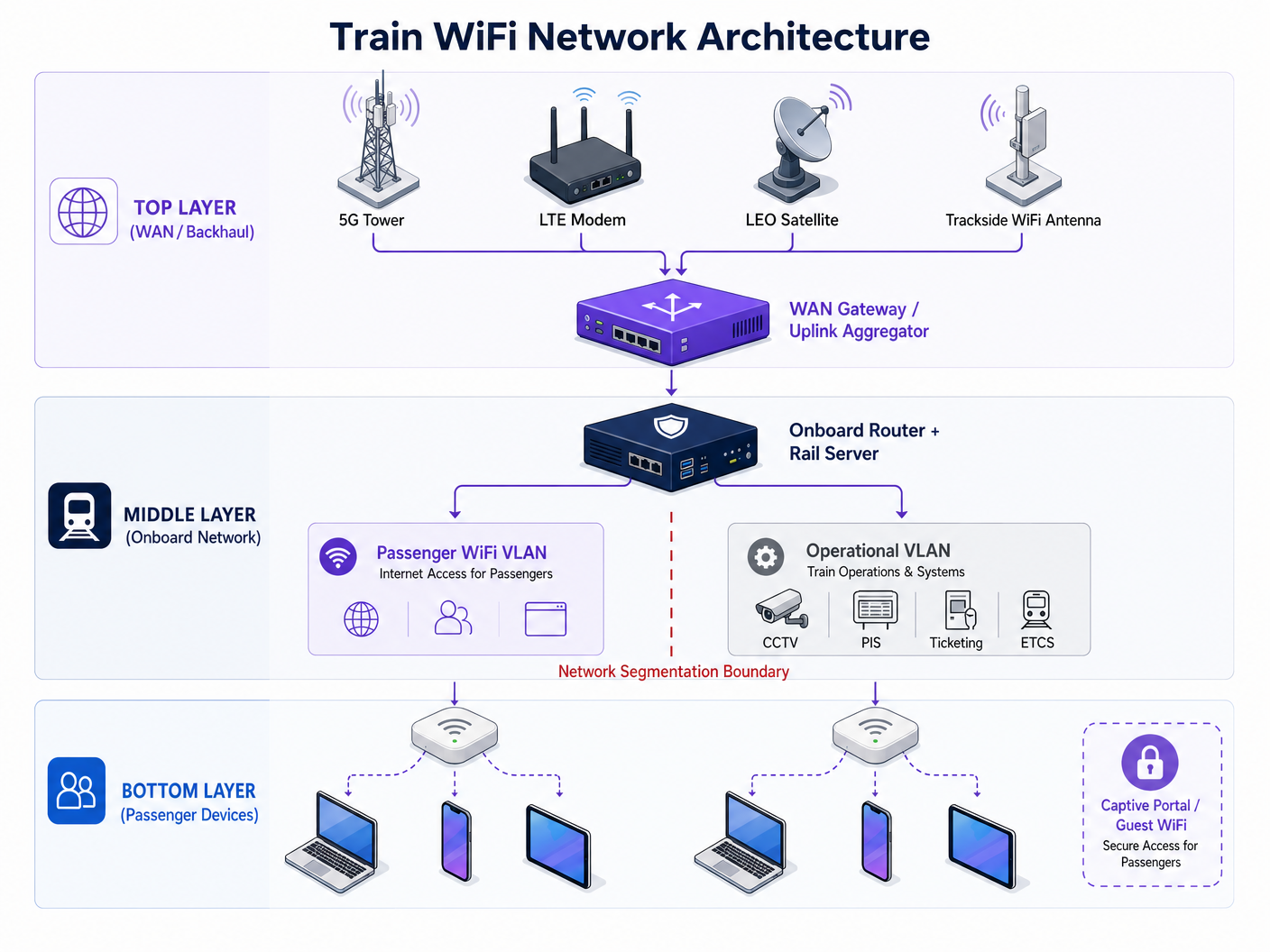
Capa 1: Backhaul WAN y Agregación
El límite de su experiencia de pasajero está dictado completamente por su capacidad de backhaul. Un solo módem LTE con una antena montada en el techo ya no es viable. Las arquitecturas modernas utilizan un WAN Gateway para agregar múltiples enlaces ascendentes:
- Cellular Bonding: Combinación de conexiones 4G/5G de múltiples Operadores de Red Móvil (MNOs) para mitigar puntos ciegos de cobertura de red única.
- Infraestructura en Vía: Redes inalámbricas dedicadas de 5 GHz o 60 GHz desplegadas a lo largo del corredor ferroviario.
- Satélite LEO: Constelaciones de órbita terrestre baja (p. ej., Starlink) que proporcionan un rendimiento de 100-200 Mbps en secciones rurales o transfronterizas donde la telefonía móvil terrestre falla [2].
Capa 2: La Red a Bordo y Segmentación
El WAN Gateway alimenta un router a bordo y un servidor ferroviario. Esta capa gestiona la tarea crítica de la Segmentación de Red.
> "El WiFi para pasajeros debe ejecutarse en una VLAN completamente aislada, sin ruta de enrutamiento a la red operativa que transporta las transmisiones de CCTV, los Sistemas de Información al Pasajero (PIS) o los datos de señalización del Sistema Europeo de Control de Trenes (ETCS)."
Un ciberataque en 2024 a una red WiFi para pasajeros del Reino Unido demostró los graves riesgos de una segmentación inadecuada, donde las vulnerabilidades de cara al público comprometieron la infraestructura terminal más amplia [3]. La implementación de la autenticación basada en puertos IEEE 802.1X y reglas estrictas de firewall entre VLAN es un requisito de seguridad no negociable. Además, el servidor ferroviario proporciona alojamiento de aplicaciones en contenedores, lo que permite que el almacenamiento en caché de contenido local y los servicios de Captive Portal funcionen incluso cuando la conectividad de backhaul se interrumpe.
Capa 3: Acceso de Pasajeros y Hardware de Cabina
La capa final consiste en los puntos de acceso (APs) distribuidos por todos los vagones. El hardware heredado es un lastre significativo para el rendimiento. En Alemania, la actualización de WiFi 4 (802.11n) a WiFi 5 (802.11ac) produjo una mejora de velocidad del 241%, mientras que el cambio de tráfico de la banda de 2.4 GHz a 5 GHz supuso un aumento del 328% [1]. Sin embargo, casi el 40% de las conexiones ferroviarias europeas todavía dependen de WiFi 4.
Guía de Implementación: Despliegue y Cumplimiento
Desplegar Train WiFi es un proyecto complejo de integración de sistemas. Los siguientes pasos describen una estrategia de despliegue robusta:
- Realice una Auditoría de Backhaul: Antes de especificar los APs de cabina, audite su ruta en busca de lagunas de cobertura celular. Diseñe su estrategia de agregación de enlaces ascendentes en torno a estos puntos ciegos.
- Especifique Ventanas Permeables a RF: Las ventanas modernas de los trenes utilizan recubrimientos metálicos para la eficiencia térmica, lo que puede atenuar las señales celulares en 20-30 dB. Las antenas montadas en el techo que alimentan los APs internos son obligatorias para superar esto.
- Implemente un Captive Portal Robusto: El Captive Portal es la interfaz principal entre el pasajero y el operador. Debe capturar de forma segura credenciales verificadas (correo electrónico o inicio de sesión social) mientras presenta los términos de servicio.
- Asegure el Cumplimiento del GDPR: Los operadores deben establecer una base legal para el procesamiento de datos de pasajeros. El consentimiento debe ser libremente otorgado y registrado de manera inequívoca. Proteja su Red con un DNS y Seguridad Robustos es una consideración crítica aquí.
ROI e Impacto Comercial: Transformando Datos en Inteligencia
Proporcionar WiFi gratuito representa un gasto operativo significativo. Para generar ROI, los operadores deben aprovechar la capa de conexión para recopilar datos de primera parte.
Cuando los pasajeros se autentican a través de un Captive Portal compatible, los operadores pueden construir perfiles ricos del comportamiento del viaje. Aquí es donde WiFi Analytics se vuelve transformador. Al analizar las frecuencias de conexión, los tiempos de permanencia en estaciones específicas y los patrones de ocupación de los vagones, los operadores obtienen inteligencia operativa que rivaliza con los conocimientos recopilados en centros de Transport y aeropuertos.
Por ejemplo, comprender que un grupo específico de viajeros de negocios se conecta constantemente en el servicio de las 07:30 permite comunicaciones de marketing dirigidas y de alto valor o la integración de programas de fidelización. Este enfoque basado en datos transforma la red WiFi en fde un centro de costes a un activo generador de ingresos.
Escuche el Informe
Para una inmersión más profunda en la arquitectura y la estrategia comercial, escuche nuestro informe técnico completo:
Referencias: [1] Ookla Speedtest Intelligence, "Trenes rápidos, Wi-Fi lento: La realidad de la conectividad a bordo en Europa y Asia", Q2 2025. [2] Pruebas de la industria, Integración de satélites LEO para la movilidad, 2024-2025. [3] Railway Technology, "Red wifi de pasajeros del Reino Unido hackeada", septiembre de 2024.
Términos clave y definiciones
WAN Aggregation
The process of combining multiple Wide Area Network connections (e.g., two 5G connections and a satellite link) into a single logical connection to increase throughput and resilience.
Critical for trains moving through varying cellular coverage areas to prevent dropped connections.
Network Segmentation (VLAN)
Dividing a computer network into smaller, isolated sub-networks. Virtual Local Area Networks (VLANs) keep traffic separated logically even if it shares the same physical switches.
Essential for preventing a compromised passenger device from accessing critical train control systems.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
Used to enforce terms of service, collect user data, and secure GDPR consent.
RF Attenuation
The reduction in signal strength as radio waves pass through a medium.
Modern train windows with metallic thermal coatings cause massive RF attenuation, requiring roof-mounted antennas.
LEO Satellite
Low Earth Orbit satellites that operate much closer to Earth than traditional geostationary satellites, offering lower latency and higher bandwidth.
Increasingly used as a backhaul solution for trains in rural or cross-border areas.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Used to secure the operational network interfaces on the train from unauthorized access.
Rail Server
A ruggedized onboard computer designed to host containerized applications locally on the train.
Used to host local entertainment, caching, and captive portal services to reduce reliance on the WAN link.
First-Party Data
Information a company collects directly from its customers and owns.
The primary commercial output of a properly configured Guest WiFi network.
Casos de éxito
A regional rail operator running 4-carriage commuter trains through a mix of dense urban areas and deep rural valleys is experiencing severe passenger complaints regarding WiFi dropouts. Their current setup uses a single 4G LTE modem per train. How should they redesign their architecture?
- Upgrade the WAN Backhaul: Replace the single LTE modem with a WAN Gateway capable of uplink aggregation. Install dual-SIM routers using two different Mobile Network Operators (MNOs) to provide failover in urban areas.
- Address Rural Gaps: For the deep valleys where cellular coverage is non-existent, integrate a LEO satellite terminal (e.g., Starlink Mobility) into the WAN Gateway as a secondary aggregated link.
- Local Caching: Deploy an onboard rail server to cache the captive portal and key journey information locally, ensuring the passenger UI remains responsive even during brief total connection losses in tunnels.
An intercity rail franchise is upgrading its fleet and wants to use the new onboard WiFi to gather passenger analytics for marketing, similar to how [Retail](/industries/retail) venues operate. What compliance and technical steps must they take?
- Captive Portal Deployment: Implement a robust captive portal that requires users to authenticate via email or social login before accessing the internet.
- GDPR Compliance: Ensure the portal explicitly asks for opt-in consent for marketing communications. Pre-ticked boxes must not be used. The system must log the timestamp and version of the privacy policy consented to.
- Analytics Integration: Route the authenticated session data into a centralized WiFi Analytics platform to track journey frequency, dwell time, and cross-reference with ticketing data where permissible.
Análisis de escenarios
Q1. Your CTO wants to upgrade all carriage access points to WiFi 6 to solve passenger complaints about slow internet speeds. Your current backhaul is a single 4G connection. What is the correct architectural response?
💡 Sugerencia:Consider where the actual bottleneck in the data flow is occurring.
Mostrar enfoque recomendado
Advise the CTO to halt the AP upgrade and invest the budget in a WAN Gateway capable of uplink aggregation. Upgrading to WiFi 6 will improve local device-to-AP speeds within the carriage, but the total throughput to the internet remains choked by the single 4G connection. Fix the backhaul bottleneck first.
Q2. During a network design review, an engineer suggests routing the train's CCTV data through the same router interfaces as the passenger WiFi to save on cabling costs. How do you respond?
💡 Sugerencia:Consider the security implications of mixing public and operational traffic.
Mostrar enfoque recomendado
Reject the proposal immediately. Passenger WiFi and operational systems like CCTV must be strictly segmented into isolated VLANs with deny-all firewall rules between them. Mixing this traffic creates a critical security vulnerability, potentially allowing a malicious actor on the public WiFi to access or disrupt train operations.
Q3. The marketing team wants to automatically subscribe all passengers who use the free WiFi to a weekly newsletter to boost engagement. What must you configure on the captive portal to ensure this is legal?
💡 Sugerencia:Review the requirements for lawful data processing under GDPR.
Mostrar enfoque recomendado
You must configure the captive portal to include an explicit, unticked opt-in checkbox for marketing communications. Automatic subscription or pre-ticked boxes violate GDPR requirements for freely given, unambiguous consent. The system must also log the timestamp of this consent for audit purposes.



