¿Cómo funciona el WiFi Marketing?
Esta guía de referencia técnica explica la mecánica del WiFi marketing, desde la solicitud inicial de sondeo del dispositivo y la autenticación del Captive Portal hasta los disparadores de campañas automatizadas y la atribución de ciclo cerrado. Proporciona orientación de implementación práctica para gerentes de TI, arquitectos de red y directores de operaciones de recintos que implementan WiFi para invitados compatible y generador de ingresos en comercios minoristas, hostelería y grandes espacios públicos.
🎧 Escucha esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado
- El Flujo de Autenticación
- Análisis de Presencia vs. Datos Autenticados
- Arquitectura de Automatización
- Guía de Implementación
- Paso 1: Evaluación de la Infraestructura
- Paso 2: Diseño y Configuración de la Página de Bienvenida (Splash Page)
- Paso 3: Cumplimiento y Privacidad
- Paso 4: Integración y Automatización de API
- Mejores Prácticas
- Solución de Problemas y Mitigación de Riesgos
- Modos de Falla Comunes
- ROI e Impacto Comercial
Resumen Ejecutivo
Para los líderes de TI y operaciones empresariales en comercios minoristas, hostelería y grandes espacios públicos, proporcionar WiFi gratuito para invitados ya no es una comodidad opcional, es una expectativa básica. Sin embargo, operar una red inalámbrica segura y de alta densidad representa un centro de costos significativo. El WiFi marketing transforma esta infraestructura en un activo generador de ingresos al establecer un intercambio de valor: conectividad fluida a cambio de datos de clientes autenticados y de primera mano.
Esta guía detalla la mecánica técnica de cómo funciona el WiFi marketing, desde la solicitud inicial de sondeo del dispositivo hasta la ejecución automatizada de campañas de marketing dirigidas. Al implementar un Captive Portal integrado con una plataforma de análisis basada en la nube, los recintos pueden capturar datos demográficos, medir el tráfico peatonal físico y atribuir las visitas en la tienda a los esfuerzos de marketing digital. Ya sea que esté implementando WiFi para invitados en un solo sitio o en una propiedad de múltiples sitios, este documento proporciona la visión general arquitectónica, las mejores prácticas de implementación y las estrategias de mitigación de riesgos necesarias para construir una solución compatible y escalable que impulse un ROI medible.
Análisis Técnico Detallado
Comprender cómo funciona el WiFi marketing requiere examinar el flujo de datos desde el borde de la red hasta la plataforma de automatización de marketing. El proceso se basa en protocolos de red estándar — IEEE 802.11, RADIUS — superpuestos con estándares modernos de autenticación web (OAuth 2.0) e integraciones de API RESTful.
El Flujo de Autenticación

El flujo de cinco etapas anterior mapea el recorrido desde la asociación del dispositivo hasta la atribución. Aquí están los detalles técnicos detrás de cada etapa.
Etapa 1 — Asociación del Dispositivo: Cuando el smartphone o laptop de un invitado entra al recinto, sondea activamente redes conocidas o escucha pasivamente los marcos de baliza que transmiten el Service Set Identifier (SSID) del recinto. La red de invitados se configura típicamente como un SSID abierto — sin clave precompartida — para minimizar la fricción en el punto de entrada.
Etapa 2 — Intercepción del Captive Portal: Al asociarse con el SSID abierto, el dispositivo intenta alcanzar un punto final de internet conocido (por ejemplo, captive.apple.com en iOS, connectivitycheck.gstatic.com en Android). El controlador de red o el Punto de Acceso intercepta esta solicitud HTTP y emite una redirección 302 a la URL del Captive Portal alojada en la plataforma de WiFi marketing.
Etapa 3 — Renderizado de la Página de Bienvenida y Captura de Datos: El Captive Portal renderiza una página de bienvenida de marca. Esta es la interfaz principal de captura de datos.

La página de bienvenida presenta al usuario opciones de autenticación: un formulario estándar de correo electrónico/contraseña, o inicio de sesión social a través de OAuth 2.0 (Google, Facebook, Apple). El inicio de sesión social es particularmente valioso porque devuelve datos demográficos verificados — nombre, dirección de correo electrónico, foto de perfil y, en algunos casos, rango de edad y ubicación — directamente del proveedor de identidad, enriqueciendo el perfil más allá de lo que capturaría un formulario básico.
Etapa 4 — Autenticación RADIUS: Una vez que el usuario envía sus credenciales, la plataforma de la página de bienvenida actúa como un servidor RADIUS (Remote Authentication Dial-In User Service). Envía un mensaje RADIUS Access-Accept de vuelta al controlador de red, que contiene la dirección MAC del usuario y cualquier atributo de política aplicable (límites de ancho de banda, tiempos de espera de sesión). El controlador entonces concede acceso a internet al dispositivo.
Etapa 5 — Enriquecimiento de Perfil y Automatización de Campañas: Los datos capturados se almacenan en un perfil CRM centralizado. A medida que el usuario se mueve por el recinto, la red continúa registrando su dirección MAC a través de solicitudes de sondeo, construyendo una imagen del tiempo de permanencia, visitas a zonas y frecuencia de retorno. Estos datos se alimentan directamente a la plataforma de WiFi Analytics , donde se pueden configurar disparadores de campañas automatizadas.
Análisis de Presencia vs. Datos Autenticados
Es importante distinguir entre dos flujos de datos distintos generados por la red:
| Data Type | Source | Identifiable? | Use Case |
|---|---|---|---|
| Análisis de Presencia | Todas las solicitudes de sondeo (autenticadas y no autenticadas) | No (MAC aleatorizada) | Conteo de tráfico peatonal, tiempo de permanencia, mapas de calor de zonas |
| Datos Autenticados | Inicio de sesión en Captive Portal | Sí (vinculado a perfil de correo electrónico/social) | Perfilado CRM, campañas dirigidas, atribución |
La aleatorización de direcciones MAC — introducida en iOS 14 y Android 10 — significa que los dispositivos no autenticados presentan una dirección MAC diferente, generada aleatoriamente en cada ciclo de sondeo. Esto hace imposible rastrear de forma fiable a los visitantes recurrentes sin autenticación. Sin embargo, una vez que un usuario inicia sesión a través del Captive Portal, su MAC aleatoria actual se vincula a su identidad de perfil persistente (dirección de correo electrónico, ID social), restaurando la capacidad de rastrear el historial de visitas y activar campañas basadas en el comportamiento.
Arquitectura de Automatización
La plataforma de WiFi analytics se integra con el stack de marketing más amplio a través de webhooks y API RESTful. Los eventos en tiempo real — un usuario conectándose, alcanzando un hito de visita, o pasando 45 días sin una visita — envían cargas útiles de webhook a la plataforma de automatización de marketing conectada (por ejemplo, HubSpot, Salesforce Marketing Cloud, Mailchimp). Esto activa flujos de trabajo preconfigurados: un correo electrónico de bienvenida, una recompensa por lealtad o un SMS de recuperación. La red misma se convierte en la capa de activación para el stack de automatización de marketing.
Guía de Implementación
La implementación de una solución robusta de marketing WiFi requiere coordinación entre los equipos de ingeniería de red, marketing y legal. Los siguientes pasos describen una implementación empresarial estándar. Para consideraciones de múltiples sitios, consulte Cómo configurar WiFi en un área grande o una propiedad de múltiples sitios .
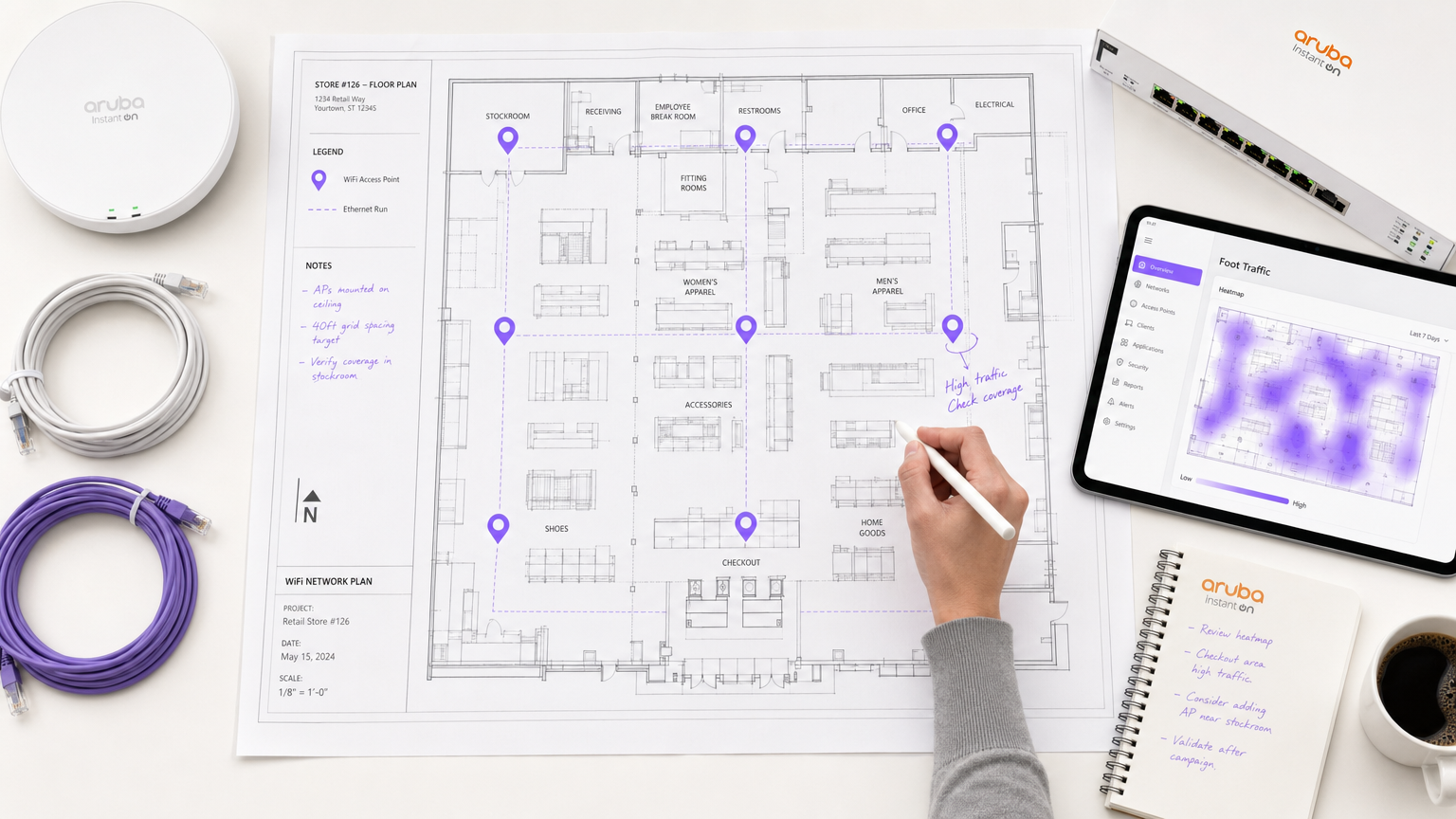
Paso 1: Evaluación de la Infraestructura
Audite su infraestructura WLAN existente. Confirme que sus controladores (Cisco Meraki, Aruba, Ruckus, Ubiquiti o equivalente) admiten la integración de Captive Portal externo y la autenticación RADIUS. La red debe estar dimensionada para capacidad, no solo para cobertura. En entornos de alta densidad —estadios, centros de conferencias, comercios durante las horas pico— el volumen de solicitudes de autenticación simultáneas puede saturar un servidor RADIUS subdimensionado. Planifique en consecuencia.
Para recintos con diseños físicos complejos, considere la guía en Sistema de Posicionamiento Interior: Guía UWB, BLE y WiFi para comprender cómo se pueden superponer los análisis a nivel de zona sobre la infraestructura WiFi.
Paso 2: Diseño y Configuración de la Página de Bienvenida (Splash Page)
La página de bienvenida es el punto principal de conversión. Su rendimiento determina directamente la calidad de su captura de datos. Principios clave de diseño:
- Minimizar el tiempo de carga: Mantenga la página por debajo de 200KB. Evite imágenes grandes o frameworks JavaScript pesados. La página debe cargarse rápidamente en una conexión móvil 3G.
- Configuración de "walled garden": Incluya en la lista blanca todos los dominios requeridos por la página de bienvenida — scripts de inicio de sesión social (accounts.google.com, connect.facebook.net), activos alojados en CDN y la URL de su política de privacidad — para que sean accesibles antes de la autenticación.
- Perfilado progresivo: Capture los datos mínimos viables en la primera visita (dirección de correo electrónico, consentimiento). Enriquezca el perfil en visitas posteriores con campos opcionales adicionales (número de teléfono, fecha de nacimiento, preferencias).
- Diseño "mobile-first": La mayoría de los usuarios se autenticarán en un smartphone. Diseñe para una ventana gráfica de 375px como objetivo principal.
Paso 3: Cumplimiento y Privacidad
GDPR (en el Reino Unido y la UE), CCPA (en California) y las regulaciones equivalentes de protección de datos requieren que el consentimiento de marketing sea activo y explícito. La página de bienvenida debe presentar una casilla de verificación sin marcar para la opción de marketing, junto con un enlace claro a la Política de Privacidad. Las casillas premarcadas, el consentimiento implícito o el consentimiento oculto en los Términos de Servicio no cumplen con la normativa y exponen a la organización a riesgos regulatorios.
Para implementaciones en Salud , se aplican consideraciones adicionales sobre la sensibilidad de los datos de ubicación. Consulte WiFi en Hospitales: Una Guía para Redes Clínicas Seguras para obtener orientación específica del sector.
Paso 4: Integración y Automatización de API
Integre la plataforma de análisis WiFi con su CRM y su pila de automatización de marketing a través de API RESTful o webhooks. Configure los siguientes disparadores de automatización de referencia:
| Disparador | Condición | Acción Recomendada |
|---|---|---|
| Primera Visita | El usuario se conecta por primera vez | Enviar correo electrónico de bienvenida con información del lugar |
| Hito de Lealtad | El usuario alcanza la 5ª visita | Enviar recompensa de lealtad o código de descuento |
| Recuperación | Usuario no visto durante 45 días | Enviar SMS o correo electrónico de re-engagement |
| Encuesta Post-Visita | El usuario se desconecta después de una sesión de más de 30 minutos | Enviar correo electrónico de encuesta NPS |
Mejores Prácticas
Autenticación Basada en Perfil: Siempre que sea posible, implemente Passpoint (Hotspot 2.0) o autenticación basada en perfil para usuarios recurrentes. Esto permite que los visitantes recurrentes autenticados se conecten de forma automática y segura (WPA2/WPA3 Enterprise) sin volver a ver la página de bienvenida, mientras se registra su visita y se activan las automatizaciones. Esto es particularmente valioso en entornos de Hostelería y Comercio Minorista donde la afluencia de visitantes recurrentes es alta.
Segmentación de Audiencia: Evite las campañas de difusión genéricas. Utilice los datos de comportamiento capturados por la red para segmentar su audiencia — visitantes frecuentes, clientes inactivos, primerizos, visitantes con alto tiempo de permanencia — y adapte los mensajes a cada segmento. Un visitante primerizo a una cafetería necesita una comunicación diferente a la de un cliente que visita tres veces por semana.
Atribución de Ciclo Cerrado: Configure sus análisis para rastrear el recorrido desde el envío de la campaña digital hasta la visita al lugar físico. Cuando un usuario que recibió un correo electrónico promocional se autentica posteriormente en el WiFi del lugar, esa visita se atribuye a la campaña. Esta es la métrica de ROI más convincente para justificar la inversión en la plataforma ante los interesados financieros.
Consistencia Multi-Sitio: Para centros de Transporte y cadenas minoristas que operan en múltiples sitios, asegure que la marca de la página de bienvenida y el flujo de autenticación sean consistentes en todas las ubicaciones. La inconsistencia erosiona la confianza y reduce las tasas de conversión.
Solución de Problemas y Mitigación de Riesgos
Modos de Falla Comunes
Captive Portal No Aparece: La causa más común es una falla en la resolución de DNS en la VLAN de invitados, o reglas de firewall que bloquean la intercepción HTTP. Asegúrese de que la VLAN de invitados tenga un servidor DNS configurado, que el controlador de red esté configurado para interceptar el tráfico HTTP en el puerto 80, y que el "walled garden" permita el acceso al dominio del Captive Portal antes de la autenticación.
Altas Tasas de Abandono: Si los usuarios llegan a la página de bienvenida pero no completan la autenticación, las causas más comunes son: tiempo de carga lento de la página (audite el "walled garden" en busca de dominios CDN faltantes), demasiados campos de formulario obligatorios (reduzca a correo electrónico + consentimiento en la primera visita), o una propuesta de valor poco clara (haga que el beneficio del WiFi sea prominente en la página).
Silos de Datos: Si la plataforma WiFi no está integrada con el CRM, los datos capturados no tienen valor comercial. Establezca una verificación regular del estado de la integración — confirme que los nuevos perfiles aparecen en el CRM dentro del SLA esperado y configure alertas para fallas de webhook.
Casos Extremos de Aleatorización de MAC: EIncluso con autenticación, la aleatorización de MAC puede hacer que un solo usuario aparezca como múltiples perfiles si inicia sesión desde diferentes dispositivos o si su MAC aleatorizada cambia entre sesiones en el mismo dispositivo. Implemente la deduplicación basada en correo electrónico en el CRM para fusionar perfiles duplicados.
ROI e Impacto Comercial
El caso de negocio para el marketing WiFi se basa en tres resultados medibles:
1. Activo de Datos de Primera Parte: En un mundo post-cookies, los datos de primera parte son un activo estratégico. Cada conexión WiFi autenticada añade un contacto verificado y con consentimiento al CRM. Para un lugar con 500 visitantes diarios y una tasa de autenticación del 40%, esto representa 200 perfiles nuevos o reactivados por día.
2. Ingresos Impulsados por Campañas: Las campañas automatizadas activadas por eventos de red generan ingresos directamente atribuibles a la plataforma WiFi. Una campaña de recuperación con una tasa de canje del 10% en una oferta de £5, enviada a 1,000 clientes inactivos, genera £500 en ingresos incrementales por campaña ejecutada, con un costo laboral marginal cero una vez configurada.
3. Inteligencia Operacional: El análisis de presencia y los mapas de calor de zonas proporcionan a los equipos de operaciones del lugar datos para optimizar la dotación de personal, la ubicación de productos y la distribución. Para implementaciones a gran escala, esta inteligencia operacional por sí sola puede justificar el costo de la plataforma.
Para un desglose detallado de cómo estas métricas se aplican a su tipo de lugar específico, la plataforma WiFi Analytics proporciona paneles de control de ROI preconfigurados segmentados por vertical de industria.
Términos clave y definiciones
Captive Portal
A web-based authentication mechanism that intercepts a user's initial HTTP request when they connect to a network and redirects them to a specific page before granting full internet access.
The fundamental technical mechanism underpinning WiFi marketing. Every WiFi marketing deployment relies on a captive portal to intercept the user and present the splash page.
Splash Page
The specific branded web page displayed within the captive portal where the user authenticates (via email form or social login) and provides consent for marketing communications.
The primary user interface for WiFi marketing. Its design — load time, number of form fields, clarity of consent language — directly determines the authentication conversion rate.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorisation, and Accounting (AAA) management. In WiFi marketing, the cloud platform acts as a RADIUS server, issuing Access-Accept or Access-Reject messages to the network controller based on whether the user has successfully authenticated.
The protocol that bridges the WiFi marketing platform and the physical network infrastructure. Understanding RADIUS is essential for troubleshooting authentication failures.
MAC Address (Media Access Control Address)
A unique hardware identifier assigned to a network interface controller (NIC), used as a network address within a local network segment.
The primary identifier used by the network to track a device's presence. Subject to randomisation in modern operating systems, which limits its utility for tracking unauthenticated devices.
MAC Randomisation
A privacy feature in iOS 14+, Android 10+, and Windows 10+ where the device presents a randomly generated MAC address when probing for networks, rather than its true hardware MAC address.
A significant challenge for unauthenticated presence analytics. Overcome by linking the randomised MAC to a persistent profile identity at the point of captive portal authentication.
Walled Garden
A restricted network environment that allows a user to access a limited set of pre-approved IP addresses or domains before completing authentication on the captive portal.
Critical for ensuring the splash page loads correctly. All resources required by the splash page (social login scripts, CDN assets, privacy policy) must be whitelisted in the walled garden.
Presence Analytics
The measurement of physical footfall, dwell time, and movement patterns within a venue by passively monitoring the probe requests emitted by all WiFi-enabled devices in range, regardless of whether they connect to the network.
Provides baseline operational metrics (total footfall, peak times, zone occupancy) but lacks demographic depth. Affected by MAC randomisation for repeat-visitor tracking.
Closed-Loop Attribution
The ability to track a customer's complete journey from receiving a digital marketing message (email, SMS) to physically visiting a venue and authenticating on the WiFi network, proving that the digital campaign drove the physical visit.
The most commercially compelling metric for WiFi marketing ROI. Enables marketing teams to prove the physical impact of digital spend to finance stakeholders.
Webhook
An HTTP callback that fires automatically when a specific event occurs in a system, sending a data payload to a pre-configured URL in another system.
The mechanism by which real-time network events (user connects, visit milestone reached, user churns) trigger automated workflows in the connected marketing automation platform.
Progressive Profiling
A data capture strategy where additional profile attributes are requested incrementally across multiple interactions, rather than all at once on the first visit.
Reduces friction on the first visit (improving conversion rates) while building a richer profile over time. Typically implemented by configuring different splash page forms for first-time vs. returning visitors.
Casos de éxito
A 200-room hotel in a major city wants to increase direct bookings and reduce reliance on Online Travel Agencies (OTAs), which are charging 15-18% commission on every reservation. They currently offer an open guest WiFi network secured with a simple WPA2 pre-shared key. How should they architect a WiFi marketing solution to address this objective?
Replace the WPA2 pre-shared key with an open SSID that redirects to a captive portal hosted on the Purple platform. The splash page requires guests to authenticate via email or social login and explicitly opt-in to marketing communications. The platform is integrated via API with the hotel's Property Management System (PMS) and email marketing platform. When a guest authenticates, their profile is enriched with their stay dates (pulled from the PMS via API). The hotel configures two automated triggers: (1) A 'During Stay' trigger — when a guest connects for the first time, send a welcome message with the hotel's dining and spa offers. (2) A 'Post-Checkout' trigger — 24 hours after the guest's device disconnects from the network (indicating checkout), send an email offering a 15% discount on their next stay booked directly through the hotel's website. The discount code is unique per guest and tracked in the PMS, allowing direct attribution of bookings to the WiFi campaign.
A pub group operating 50 sites across the UK wants to understand which venues are underperforming on customer retention and implement an automated strategy to win back lapsed customers, without requiring manual intervention from the marketing team at each site.
Deploy a unified guest WiFi solution across all 50 sites, with a consistent splash page and authentication flow. Configure the analytics dashboard to surface 'Return Rate' (percentage of customers who visit more than once in a 90-day window) and 'Average Visit Frequency' per venue. After 60 days of data collection, identify the three sites with the lowest return rates relative to the group average. Configure a group-wide automated win-back campaign: if a customer who has previously authenticated at any of the three underperforming sites has not been seen on the network for 45 days, a webhook triggers an SMS via the connected SMS gateway, offering a complimentary drink on their next visit. The campaign runs continuously and automatically, requiring no manual intervention. Monthly reporting tracks the return rate at the three target sites against the group baseline.
Análisis de escenarios
Q1. Your marketing team wants to launch a campaign targeting customers who have visited your flagship retail store more than five times in the last month but have not returned in the last two weeks. They report that the data in the CRM is incomplete — many customers appear only once despite being regular visitors. You discover the network is configured with a WPA2 pre-shared key. What is the fundamental architectural problem, and what is the correct solution?
💡 Sugerencia:Consider how devices are identified on the network and how MAC randomisation affects repeat-visitor tracking without authentication.
Mostrar enfoque recomendado
The fundamental problem is that a WPA2 pre-shared key network provides no authentication layer. Devices are tracked only by their MAC address, and due to MAC randomisation in modern iOS and Android devices, each visit may present a different MAC address, making it impossible to link multiple visits to the same individual. The solution is to deploy a captive portal with a splash page. By requiring users to authenticate via email or social login to access the internet, the platform links their current randomised MAC address to a persistent profile identity in the CRM. This enables accurate visit frequency tracking and allows the marketing team to build the audience segment they need for their campaign.
Q2. During a stadium event with 40,000 attendees, the IT team reports that the captive portal splash page is taking 15-20 seconds to load at halftime, causing widespread abandonment and complaints. Network monitoring confirms the APs are not overloaded and internet backhaul is performing normally. What is the most likely cause, and how do you diagnose and resolve it?
💡 Sugerencia:Think about what resources the splash page needs to load before the user has full internet access, and what the walled garden configuration controls.
Mostrar enfoque recomendado
The most likely cause is an incomplete walled garden configuration. The splash page relies on external resources — social login scripts from Google or Facebook, CDN-hosted CSS or JavaScript files, or images — that are not whitelisted in the walled garden. Before authentication, the device can only access domains explicitly permitted in the walled garden. If the splash page attempts to load a resource from a non-whitelisted domain, the request times out, causing the page to load slowly or partially. To diagnose: open the splash page URL in a browser with developer tools open and observe which network requests are failing or timing out. To resolve: add the failing domains to the walled garden whitelist on the network controller. Additionally, consider hosting all splash page assets on the captive portal platform itself to eliminate external dependencies.
Q3. You are deploying guest WiFi across a chain of 20 healthcare clinics. The legal team is concerned about GDPR compliance for data captured via the WiFi network. The marketing team wants every user who connects to be automatically added to the monthly newsletter. How do you design the authentication flow to satisfy both requirements?
💡 Sugerencia:GDPR requires active, explicit consent for marketing communications. Consider how the splash page UI must be structured to meet this requirement while still enabling the marketing team's goal.
Mostrar enfoque recomendado
The splash page must implement an active opt-in mechanism for the newsletter — specifically, an unticked checkbox with clear language such as 'I would like to receive the monthly newsletter from [Clinic Name]', alongside a link to the Privacy Policy. The user must actively tick this box to opt in. Pre-ticked boxes, implied consent, or consent embedded in the Terms of Service are non-compliant under GDPR. The marketing team's goal of growing the newsletter database is achievable, but it requires optimising the 'Give to Get' value proposition on the splash page: make the WiFi benefit prominent, keep the form simple (email + checkbox), and consider offering a tangible incentive for opting in (e.g., 'Opt in for health tips and clinic updates'). Only users who actively tick the checkbox should be added to the newsletter list. This approach is compliant and, if the value proposition is compelling, will still generate significant database growth over time.
Q4. A conference centre wants to use WiFi analytics to prove to exhibitors that their stands generated measurable footfall during a three-day trade show. The venue has deployed WiFi across the entire exhibition floor. What data does the platform need to capture, and how would you structure the reporting to demonstrate ROI to exhibitors?
💡 Sugerencia:Consider the difference between presence analytics (unauthenticated) and authenticated data, and which is more appropriate for this specific use case.
Mostrar enfoque recomendado
For this use case, presence analytics (unauthenticated) is the most appropriate data source, because the goal is to measure total footfall past exhibitor stands — not to capture personal data from attendees. The network monitors probe requests from all WiFi-enabled devices in range of each AP. By mapping APs to specific zones (each exhibitor stand area), the platform can report on: total unique device count per zone per day, average dwell time per zone, peak traffic times per zone, and conversion rate from the main hall to specific stand areas. This data is presented to exhibitors in a per-stand report. The key configuration requirement is accurate zone mapping — each AP must be assigned to the correct exhibitor zone in the analytics platform. No personal data is captured or processed in this scenario, which simplifies the compliance position significantly.



