How Does WiFi Marketing Work?
This technical reference guide explains the mechanics of WiFi marketing — from the initial device probe request and Captive Portal authentication through to automated campaign triggers and closed-loop attribution. It provides actionable implementation guidance for IT managers, network architects, and venue operations directors deploying compliant, revenue-generating guest WiFi across retail, hospitality, and large public venues.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- The Authentication Flow
- Presence Analytics vs. Authenticated Data
- Automation Architecture
- Implementation Guide
- Step 1: Infrastructure Assessment
- Step 2: Splash Page Design and Configuration
- Step 3: Compliance and Privacy
- Step 4: API Integration and Automation
- Best Practices
- Troubleshooting and Risk Mitigation
- Common Failure Modes
- ROI and Business Impact
Executive Summary
For enterprise IT and operations leaders across retail, hospitality, and large public venues, providing free guest WiFi is no longer an optional amenity — it is a baseline expectation. However, operating a high-density, secure wireless network represents a significant cost centre. WiFi marketing transforms this infrastructure into a revenue-generating asset by establishing a value exchange: seamless connectivity in return for authenticated, first-party customer data.
This guide details the technical mechanics of how WiFi marketing works — from the initial device probe request to the automated execution of targeted marketing campaigns. By implementing a Captive Portal integrated with a cloud-based analytics platform, venues can capture demographic data, measure physical footfall, and attribute in-store visits to digital marketing efforts. Whether you are deploying Guest WiFi across a single site or a multi-site estate, this document provides the architectural overview, deployment best practices, and risk mitigation strategies necessary to build a compliant, scalable solution that drives measurable ROI.
Technical Deep-Dive
Understanding how WiFi marketing works requires examining the data flow from the edge of the network to the marketing automation platform. The process relies on standard networking protocols — IEEE 802.11, RADIUS — layered with modern web authentication standards (OAuth 2.0) and RESTful API integrations.
The Authentication Flow

The five-stage flow above maps the journey from device association to attribution. Here is the technical detail behind each stage.
Stage 1 — Device Association: When a guest's smartphone or laptop enters the venue, it actively probes for known networks or passively listens for beacon frames broadcasting the venue's Service Set Identifier (SSID). The guest network is typically configured as an open SSID — no pre-shared key — to minimise friction at the point of entry.
Stage 2 — Captive Portal Interception: Upon associating with the open SSID, the device attempts to reach a known internet endpoint (e.g., captive.apple.com on iOS, connectivitycheck.gstatic.com on Android). The network controller or Access Point intercepts this HTTP request and issues a 302 redirect to the Captive Portal URL hosted on the WiFi marketing platform.
Stage 3 — Splash Page Rendering and Data Capture: The Captive Portal renders a branded splash page. This is the primary data capture interface.

The splash page presents the user with authentication options: a standard email/password form, or social login via OAuth 2.0 (Google, Facebook, Apple). Social login is particularly valuable because it returns verified demographic data — name, email address, profile picture, and in some cases, age range and location — directly from the identity provider, enriching the profile beyond what a basic form would capture.
Stage 4 — RADIUS Authentication: Once the user submits their credentials, the splash page platform acts as a RADIUS server (Remote Authentication Dial-In User Service). It sends a RADIUS Access-Accept message back to the network controller, containing the user's MAC address and any applicable policy attributes (bandwidth limits, session timeouts). The controller then grants the device internet access.
Stage 5 — Profile Enrichment and Campaign Automation: The captured data is stored in a centralised CRM profile. As the user moves through the venue, the network continues to log their MAC address via probe requests, building a picture of dwell time, zone visits, and return frequency. This data feeds directly into the WiFi Analytics platform, where automated campaign triggers can be configured.
Presence Analytics vs. Authenticated Data
It is important to distinguish between two distinct data streams generated by the network:
| Data Type | Source | Identifiable? | Use Case |
|---|---|---|---|
| Presence Analytics | All probe requests (authenticated and unauthenticated) | No (MAC randomised) | Footfall counting, dwell time, zone heatmaps |
| Authenticated Data | Captive Portal login | Yes (linked to email/social profile) | CRM profiling, targeted campaigns, attribution |
MAC address randomisation — introduced in iOS 14 and Android 10 — means that unauthenticated devices present a different, randomly generated MAC address on each probe cycle. This makes it impossible to reliably track repeat visitors without authentication. Once a user logs in via the Captive Portal, however, their current randomised MAC is linked to their persistent profile identity (email address, social ID), restoring the ability to track visit history and trigger behaviour-based campaigns.
Automation Architecture
The WiFi analytics platform integrates with the wider marketing stack via webhooks and RESTful APIs. Real-time events — a user connecting, reaching a visit milestone, or going 45 days without a visit — fire webhook payloads to the connected marketing automation platform (e.g., HubSpot, Salesforce Marketing Cloud, Mailchimp). This triggers pre-configured workflows: a welcome email, a loyalty reward, or a win-back SMS. The network itself becomes the trigger layer for the marketing automation stack.
Implementation Guide
Deploying a robust WiFi marketing solution requires coordination between network engineering, marketing, and legal teams. The following steps outline a standard enterprise deployment. For multi-site considerations, refer to How to Set Up WiFi in a Large Area or Multi-Site Estate .
Step 1: Infrastructure Assessment
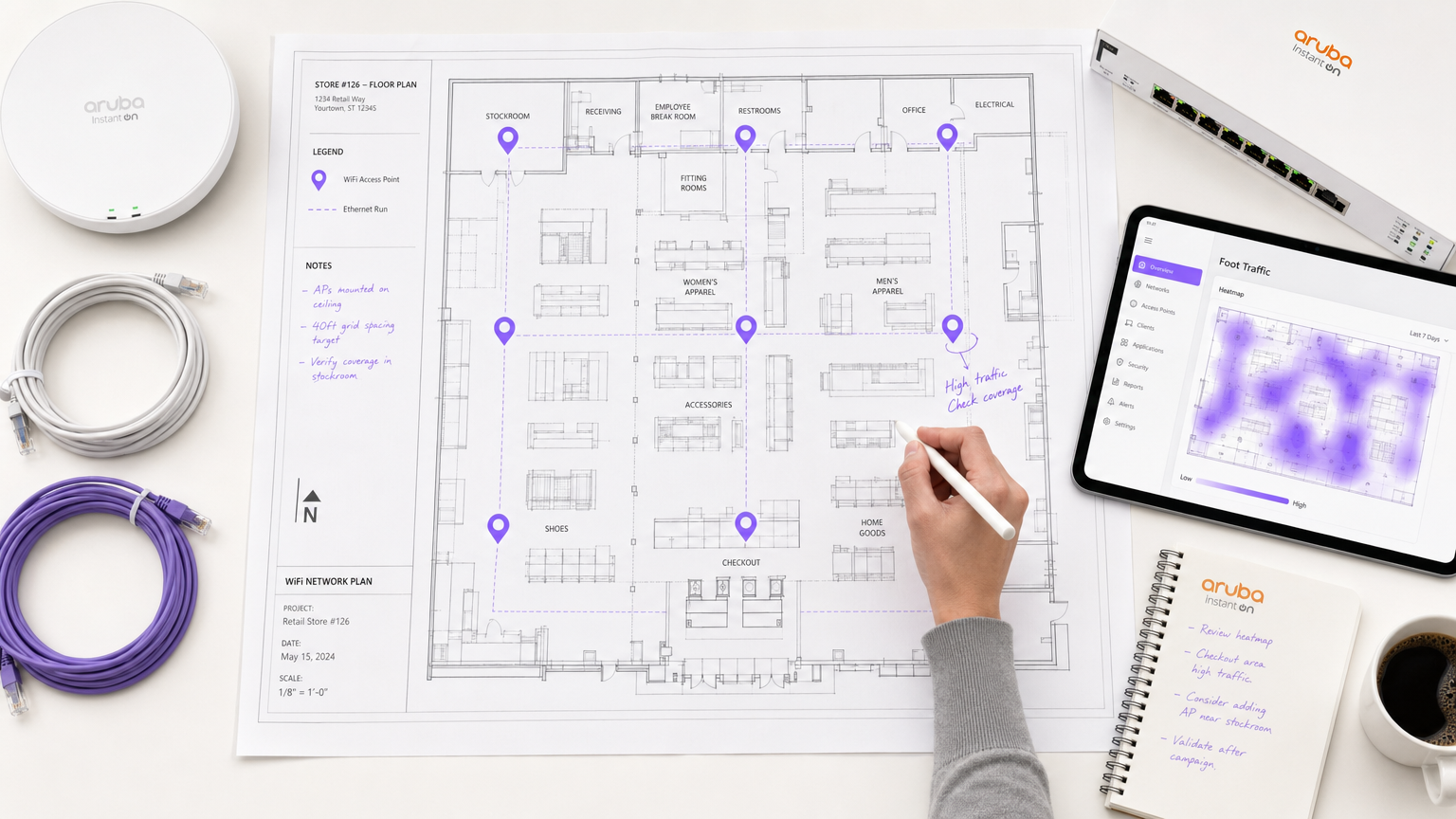
Audit your existing WLAN infrastructure. Confirm that your controllers (Cisco Meraki, Aruba, Ruckus, Ubiquiti, or equivalent) support external captive portal integration and RADIUS authentication. The network must be dimensioned for capacity, not just coverage. In high-density environments — stadiums, conference centres, retail during peak trading — the volume of simultaneous authentication requests can overwhelm an undersized RADIUS server. Plan accordingly.
For venues with complex physical layouts, consider the guidance in Indoor Positioning System: UWB, BLE, & WiFi Guide to understand how zone-level analytics can be layered on top of the WiFi infrastructure.
Step 2: Splash Page Design and Configuration
The splash page is the primary conversion point. Its performance directly determines the quality of your data capture. Key design principles:
- Minimise load time: Keep the page under 200KB. Avoid large images or heavy JavaScript frameworks. The page must load quickly on a 3G mobile connection.
- Walled garden configuration: Whitelist all domains required by the splash page — social login scripts (accounts.google.com, connect.facebook.net), CDN-hosted assets, and your privacy policy URL — so they are accessible before authentication.
- Progressive profiling: Capture the minimum viable data on the first visit (email address, consent). Enrich the profile on subsequent visits with additional optional fields (phone number, date of birth, preferences).
- Mobile-first design: The majority of users will authenticate on a smartphone. Design for a 375px viewport as the primary target.
Step 3: Compliance and Privacy
GDPR (in the UK and EU), CCPA (in California), and equivalent data protection regulations require that marketing consent be active and explicit. The splash page must present an unticked checkbox for marketing opt-in, alongside a clear link to the Privacy Policy. Pre-ticked boxes, implied consent, or consent buried in the Terms of Service are non-compliant and expose the organisation to regulatory risk.
For Healthcare deployments, additional considerations apply around the sensitivity of location data. Consult WiFi in Hospitals: A Guide to Secure Clinical Networks for sector-specific guidance.
Step 4: API Integration and Automation
Integrate the WiFi analytics platform with your CRM and marketing automation stack via RESTful APIs or webhooks. Configure the following baseline automation triggers:
| Trigger | Condition | Recommended Action |
|---|---|---|
| First Visit | User connects for the first time | Send welcome email with venue information |
| Loyalty Milestone | User reaches 5th visit | Send loyalty reward or discount code |
| Win-Back | User not seen for 45 days | Send re-engagement SMS or email |
| Post-Visit Survey | User disconnects after 30+ min session | Send NPS survey email |
Best Practices
Profile-Based Authentication: Where possible, implement Passpoint (Hotspot 2.0) or profile-based authentication for returning users. This allows authenticated repeat visitors to connect automatically and securely (WPA2/WPA3 Enterprise) without seeing the splash page again, whilst still logging their visit and triggering automation. This is particularly valuable in Hospitality and Retail environments where repeat footfall is high.
Audience Segmentation: Avoid generic broadcast campaigns. Use the behavioural data captured by the network to segment your audience — frequent visitors, lapsed customers, first-timers, high-dwell-time visitors — and tailor messaging to each segment. A first-time visitor to a coffee shop needs different communication than a customer who visits three times a week.
Closed-Loop Attribution: Configure your analytics to track the journey from digital campaign send to physical venue visit. When a user who received a promotional email subsequently authenticates on the venue WiFi, that visit is attributed to the campaign. This is the most compelling ROI metric for justifying the platform investment to finance stakeholders.
Multi-Site Consistency: For Transport hubs and retail chains operating across multiple sites, ensure the splash page branding and authentication flow is consistent across all locations. Inconsistency erodes trust and reduces conversion rates.
Troubleshooting and Risk Mitigation
Common Failure Modes
Captive Portal Not Appearing: The most common cause is DNS resolution failure on the guest VLAN, or firewall rules blocking the HTTP interception. Ensure the guest VLAN has a DNS server configured, that the network controller is set to intercept HTTP traffic on port 80, and that the walled garden allows access to the captive portal domain before authentication.
High Abandonment Rates: If users reach the splash page but do not complete authentication, the most common causes are: slow page load time (audit the walled garden for missing CDN domains), too many required form fields (reduce to email + consent on first visit), or an unclear value proposition (make the WiFi benefit prominent on the page).
Data Silos: If the WiFi platform is not integrated with the CRM, captured data has no commercial value. Establish a regular integration health check — confirm that new profiles are appearing in the CRM within the expected SLA, and set up alerting for webhook failures.
MAC Randomisation Edge Cases: Even with authentication, MAC randomisation can cause a single user to appear as multiple profiles if they log in from different devices or if their randomised MAC changes between sessions on the same device. Implement email-based deduplication in the CRM to merge duplicate profiles.
ROI and Business Impact
The business case for WiFi marketing rests on three measurable outcomes:
1. First-Party Data Asset: In a post-cookie world, first-party data is a strategic asset. Every authenticated WiFi connection adds a verified, opted-in contact to the CRM. For a venue with 500 daily visitors and a 40% authentication rate, that is 200 new or re-engaged profiles per day.
2. Campaign-Driven Revenue: Automated campaigns triggered by network events generate revenue that is directly attributable to the WiFi platform. A win-back campaign with a 10% redemption rate on a £5 offer, sent to 1,000 lapsed customers, generates £500 in incremental revenue per campaign run — with zero marginal labour cost once configured.
3. Operational Intelligence: Presence analytics and zone heatmaps provide venue operations teams with data to optimise staffing, product placement, and layout. For large-scale deployments, this operational intelligence alone can justify the platform cost.
For a detailed breakdown of how these metrics apply to your specific venue type, the WiFi Analytics platform provides pre-built ROI dashboards segmented by industry vertical.
Key Terms & Definitions
Captive Portal
A web-based authentication mechanism that intercepts a user's initial HTTP request when they connect to a network and redirects them to a specific page before granting full internet access.
The fundamental technical mechanism underpinning WiFi marketing. Every WiFi marketing deployment relies on a captive portal to intercept the user and present the splash page.
Splash Page
The specific branded web page displayed within the captive portal where the user authenticates (via email form or social login) and provides consent for marketing communications.
The primary user interface for WiFi marketing. Its design — load time, number of form fields, clarity of consent language — directly determines the authentication conversion rate.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorisation, and Accounting (AAA) management. In WiFi marketing, the cloud platform acts as a RADIUS server, issuing Access-Accept or Access-Reject messages to the network controller based on whether the user has successfully authenticated.
The protocol that bridges the WiFi marketing platform and the physical network infrastructure. Understanding RADIUS is essential for troubleshooting authentication failures.
MAC Address (Media Access Control Address)
A unique hardware identifier assigned to a network interface controller (NIC), used as a network address within a local network segment.
The primary identifier used by the network to track a device's presence. Subject to randomisation in modern operating systems, which limits its utility for tracking unauthenticated devices.
MAC Randomisation
A privacy feature in iOS 14+, Android 10+, and Windows 10+ where the device presents a randomly generated MAC address when probing for networks, rather than its true hardware MAC address.
A significant challenge for unauthenticated presence analytics. Overcome by linking the randomised MAC to a persistent profile identity at the point of captive portal authentication.
Walled Garden
A restricted network environment that allows a user to access a limited set of pre-approved IP addresses or domains before completing authentication on the captive portal.
Critical for ensuring the splash page loads correctly. All resources required by the splash page (social login scripts, CDN assets, privacy policy) must be whitelisted in the walled garden.
Presence Analytics
The measurement of physical footfall, dwell time, and movement patterns within a venue by passively monitoring the probe requests emitted by all WiFi-enabled devices in range, regardless of whether they connect to the network.
Provides baseline operational metrics (total footfall, peak times, zone occupancy) but lacks demographic depth. Affected by MAC randomisation for repeat-visitor tracking.
Closed-Loop Attribution
The ability to track a customer's complete journey from receiving a digital marketing message (email, SMS) to physically visiting a venue and authenticating on the WiFi network, proving that the digital campaign drove the physical visit.
The most commercially compelling metric for WiFi marketing ROI. Enables marketing teams to prove the physical impact of digital spend to finance stakeholders.
Webhook
An HTTP callback that fires automatically when a specific event occurs in a system, sending a data payload to a pre-configured URL in another system.
The mechanism by which real-time network events (user connects, visit milestone reached, user churns) trigger automated workflows in the connected marketing automation platform.
Progressive Profiling
A data capture strategy where additional profile attributes are requested incrementally across multiple interactions, rather than all at once on the first visit.
Reduces friction on the first visit (improving conversion rates) while building a richer profile over time. Typically implemented by configuring different splash page forms for first-time vs. returning visitors.
Case Studies
A 200-room hotel in a major city wants to increase direct bookings and reduce reliance on Online Travel Agencies (OTAs), which are charging 15-18% commission on every reservation. They currently offer an open guest WiFi network secured with a simple WPA2 pre-shared key. How should they architect a WiFi marketing solution to address this objective?
Replace the WPA2 pre-shared key with an open SSID that redirects to a captive portal hosted on the Purple platform. The splash page requires guests to authenticate via email or social login and explicitly opt-in to marketing communications. The platform is integrated via API with the hotel's Property Management System (PMS) and email marketing platform. When a guest authenticates, their profile is enriched with their stay dates (pulled from the PMS via API). The hotel configures two automated triggers: (1) A 'During Stay' trigger — when a guest connects for the first time, send a welcome message with the hotel's dining and spa offers. (2) A 'Post-Checkout' trigger — 24 hours after the guest's device disconnects from the network (indicating checkout), send an email offering a 15% discount on their next stay booked directly through the hotel's website. The discount code is unique per guest and tracked in the PMS, allowing direct attribution of bookings to the WiFi campaign.
A pub group operating 50 sites across the UK wants to understand which venues are underperforming on customer retention and implement an automated strategy to win back lapsed customers, without requiring manual intervention from the marketing team at each site.
Deploy a unified guest WiFi solution across all 50 sites, with a consistent splash page and authentication flow. Configure the analytics dashboard to surface 'Return Rate' (percentage of customers who visit more than once in a 90-day window) and 'Average Visit Frequency' per venue. After 60 days of data collection, identify the three sites with the lowest return rates relative to the group average. Configure a group-wide automated win-back campaign: if a customer who has previously authenticated at any of the three underperforming sites has not been seen on the network for 45 days, a webhook triggers an SMS via the connected SMS gateway, offering a complimentary drink on their next visit. The campaign runs continuously and automatically, requiring no manual intervention. Monthly reporting tracks the return rate at the three target sites against the group baseline.
Scenario Analysis
Q1. Your marketing team wants to launch a campaign targeting customers who have visited your flagship retail store more than five times in the last month but have not returned in the last two weeks. They report that the data in the CRM is incomplete — many customers appear only once despite being regular visitors. You discover the network is configured with a WPA2 pre-shared key. What is the fundamental architectural problem, and what is the correct solution?
💡 Hint:Consider how devices are identified on the network and how MAC randomisation affects repeat-visitor tracking without authentication.
Show Recommended Approach
The fundamental problem is that a WPA2 pre-shared key network provides no authentication layer. Devices are tracked only by their MAC address, and due to MAC randomisation in modern iOS and Android devices, each visit may present a different MAC address, making it impossible to link multiple visits to the same individual. The solution is to deploy a captive portal with a splash page. By requiring users to authenticate via email or social login to access the internet, the platform links their current randomised MAC address to a persistent profile identity in the CRM. This enables accurate visit frequency tracking and allows the marketing team to build the audience segment they need for their campaign.
Q2. During a stadium event with 40,000 attendees, the IT team reports that the captive portal splash page is taking 15-20 seconds to load at halftime, causing widespread abandonment and complaints. Network monitoring confirms the APs are not overloaded and internet backhaul is performing normally. What is the most likely cause, and how do you diagnose and resolve it?
💡 Hint:Think about what resources the splash page needs to load before the user has full internet access, and what the walled garden configuration controls.
Show Recommended Approach
The most likely cause is an incomplete walled garden configuration. The splash page relies on external resources — social login scripts from Google or Facebook, CDN-hosted CSS or JavaScript files, or images — that are not whitelisted in the walled garden. Before authentication, the device can only access domains explicitly permitted in the walled garden. If the splash page attempts to load a resource from a non-whitelisted domain, the request times out, causing the page to load slowly or partially. To diagnose: open the splash page URL in a browser with developer tools open and observe which network requests are failing or timing out. To resolve: add the failing domains to the walled garden whitelist on the network controller. Additionally, consider hosting all splash page assets on the captive portal platform itself to eliminate external dependencies.
Q3. You are deploying guest WiFi across a chain of 20 healthcare clinics. The legal team is concerned about GDPR compliance for data captured via the WiFi network. The marketing team wants every user who connects to be automatically added to the monthly newsletter. How do you design the authentication flow to satisfy both requirements?
💡 Hint:GDPR requires active, explicit consent for marketing communications. Consider how the splash page UI must be structured to meet this requirement while still enabling the marketing team's goal.
Show Recommended Approach
The splash page must implement an active opt-in mechanism for the newsletter — specifically, an unticked checkbox with clear language such as 'I would like to receive the monthly newsletter from [Clinic Name]', alongside a link to the Privacy Policy. The user must actively tick this box to opt in. Pre-ticked boxes, implied consent, or consent embedded in the Terms of Service are non-compliant under GDPR. The marketing team's goal of growing the newsletter database is achievable, but it requires optimising the 'Give to Get' value proposition on the splash page: make the WiFi benefit prominent, keep the form simple (email + checkbox), and consider offering a tangible incentive for opting in (e.g., 'Opt in for health tips and clinic updates'). Only users who actively tick the checkbox should be added to the newsletter list. This approach is compliant and, if the value proposition is compelling, will still generate significant database growth over time.
Q4. A conference centre wants to use WiFi analytics to prove to exhibitors that their stands generated measurable footfall during a three-day trade show. The venue has deployed WiFi across the entire exhibition floor. What data does the platform need to capture, and how would you structure the reporting to demonstrate ROI to exhibitors?
💡 Hint:Consider the difference between presence analytics (unauthenticated) and authenticated data, and which is more appropriate for this specific use case.
Show Recommended Approach
For this use case, presence analytics (unauthenticated) is the most appropriate data source, because the goal is to measure total footfall past exhibitor stands — not to capture personal data from attendees. The network monitors probe requests from all WiFi-enabled devices in range of each AP. By mapping APs to specific zones (each exhibitor stand area), the platform can report on: total unique device count per zone per day, average dwell time per zone, peak traffic times per zone, and conversion rate from the main hall to specific stand areas. This data is presented to exhibitors in a per-stand report. The key configuration requirement is accurate zone mapping — each AP must be assigned to the correct exhibitor zone in the analytics platform. No personal data is captured or processed in this scenario, which simplifies the compliance position significantly.



