Haute disponibilité du serveur RADIUS : Active-Active vs Active-Passive
Un guide de référence technique définitif pour les responsables IT et les architectes réseau évaluant les architectures de haute disponibilité RADIUS. Il compare les déploiements Active-Active et Active-Passive, détaille les exigences de réplication de base de données et explique comment le Cloud RADIUS atténue la latence de basculement pour les sites d'entreprise.
🎧 Écouter ce guide
Voir la transcription
- Résumé analytique
- Analyse technique approfondie : Comprendre l'architecture RADIUS
- Architecture Active-Passive
- Architecture Active-Active
- Le défi de la réplication de base de données
- Guide de mise en œuvre : Cloud vs On-Premise
- Cloud RADIUS PlLes services Cloud RADIUS résolvent les défis de distribution géographique en hébergeant l'infrastructure d'authentification sur plusieurs zones de disponibilité mondiales. Lorsqu'un utilisateur se connecte sur un site distant, la requête est acheminée vers le nœud périphérique cloud le plus proche, minimisant ainsi la latence.
- Considérations sur le déploiement sur site
- Meilleures pratiques pour la haute disponibilité RADIUS
- Dépannage et atténuation des risques
- ROI et impact commercial
Résumé analytique
Pour les réseaux d'entreprise, l'authentification est binaire : soit elle fonctionne parfaitement, soit les opérations commerciales s'arrêtent totalement. Le RADIUS (Remote Authentication Dial-In User Service) sert de gardien critique pour les déploiements IEEE 802.1X, WPA3 enterprise et Guest WiFi sur les sites modernes. Contrairement aux services applicatifs qui se dégradent progressivement sous la charge, une panne RADIUS bloque immédiatement l'accès au réseau des utilisateurs, des terminaux de point de vente et des appareils opérationnels.
Ce guide de référence technique évalue les modèles d'architecture pour le déploiement d'une infrastructure RADIUS hautement disponible. Plus précisément, il compare les configurations Active-Passive traditionnelles aux clusters Active-Active modernes. Pour les responsables IT, les architectes réseau et les directeurs d'exploitation de sites gérant des environnements à haute densité tels que le Retail , l' Hospitality et les stades, il est essentiel de comprendre ces stratégies de basculement, les mécanismes d'équilibrage de charge et les exigences de réplication de base de données.
De plus, ce guide examine comment les plateformes Cloud RADIUS font abstraction de la complexité de la haute disponibilité, offrant un basculement automatique et une évolutivité élastique sans la charge opérationnelle liée à la maintenance d'une infrastructure sur site redondante. En appliquant ces meilleures pratiques neutres vis-à-vis des fournisseurs, les équipes d'ingénierie peuvent concevoir des architectures d'authentification qui éliminent les points de défaillance uniques et respectent des accords de niveau de service (SLA) de disponibilité stricts.
Analyse technique approfondie : Comprendre l'architecture RADIUS
Le RADIUS fonctionne comme un protocole client-serveur sur UDP, utilisant généralement le port 1812 pour l'authentification et le port 1813 pour l'accounting, comme défini dans les RFC 2865 et RFC 2866. La nature sans état (stateless) des requêtes d'authentification UDP est un avantage structurel pour la conception de la haute disponibilité. Comme chaque paquet Access-Request contient tous les identifiants et paramètres nécessaires, n'importe quel serveur RADIUS au sein d'un cluster peut traiter n'importe quelle requête de manière indépendante, sans nécessiter de synchronisation d'état complexe pour la phase d'authentification elle-même.
Architecture Active-Passive
Dans un déploiement Active-Passive (ou primaire-secondaire), un seul serveur RADIUS traite tout le trafic d'authentification et d'accounting entrant. Un serveur secondaire reste en ligne mais inactif, recevant les mises à jour de réplication de la base de données mais ne répondant pas activement aux Network Access Devices (NAD) tels que les points d'accès, les commutateurs ou les passerelles VPN.
Lorsque le serveur primaire échoue, le NAD détecte le délai d'attente et redirige les requêtes suivantes vers le serveur secondaire. Le temps de détection du basculement dépend entièrement des temporisateurs de configuration du NAD. Un NAD typique envoie une requête RADIUS et attend un délai d'expiration de paquet par défaut (souvent deux secondes). Si aucune réponse n'est reçue, il réessaie. Avec une configuration standard de trois tentatives par serveur, le NAD peut attendre jusqu'à six secondes avant de déclarer le serveur primaire hors service et de basculer vers le secondaire. Dans les environnements avec trois serveurs configurés, cette fenêtre de basculement peut s'étendre jusqu'à dix-huit secondes. Pour un site Hospitality très fréquenté ou un environnement Retail traitant des transactions, ce délai représente une interruption de service notable.
Architecture Active-Active
À l'inverse, une architecture Active-Active répartit la charge d'authentification sur plusieurs serveurs RADIUS opérationnels simultanément. Le trafic est acheminé vers le cluster soit par une configuration round-robin sur les NAD, soit via un équilibreur de charge dédié.
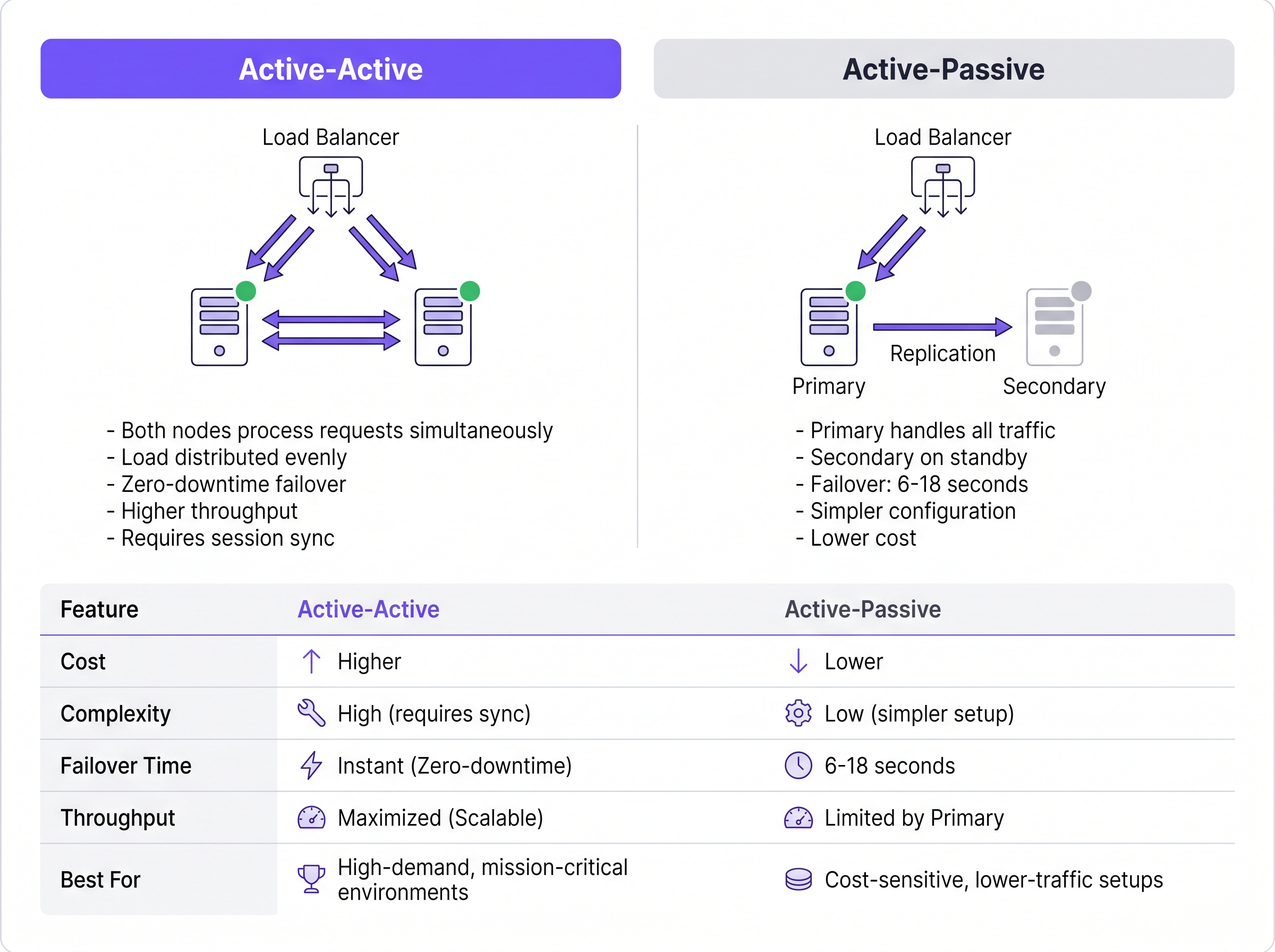
Ce modèle élimine le délai de détection de basculement inhérent aux configurations Active-Passive. Si un nœud échoue, l'équilibreur de charge (ou les NAD utilisant le round-robin) cesse simplement d'acheminer le trafic vers le serveur qui ne répond pas, généralement en une à deux secondes selon les intervalles de vérification de l'état (health-check). Les nœuds actifs restants absorbent instantanément le trafic. De plus, les clusters Active-Active évoluent horizontalement ; l'ajout de capacité pour des événements à haute densité nécessite simplement le provisionnement de nœuds supplémentaires dans le cluster.
Le défi de la réplication de base de données
Bien que l'authentification RADIUS soit sans état, l'accounting RADIUS est intrinsèquement avec état (stateful). Il suit l'initiation de la session (Start), l'utilisation en cours (Interim-Update) et la fin de la session (Stop). Pour les sites utilisant le WiFi Analytics ou des systèmes de facturation, ces données d'accounting doivent rester cohérentes sur tous les nœuds.
L'adossement d'un cluster RADIUS à une base de données répliquée (telle que MySQL ou MariaDB intégrée à FreeRADIUS) est obligatoire pour une haute disponibilité robuste. Pour les déploiements Active-Active, une réplication multi-maître synchrone — telle que Galera Cluster ou MySQL NDB Cluster — est requise. La réplication synchrone garantit qu'un enregistrement d'accounting est validé sur tous les nœuds simultanément, évitant ainsi la perte de données si un nœud échoue. La réplication asynchrone traditionnelle, souvent utilisée dans les configurations Active-Passive, introduit un délai de réplication. Si le nœud primaire échoue avant que le secondaire ne reçoive la mise à jour, les données de session active sont définitivement perdues, ce qui peut enfreindre les cadres de conformité comme PCI DSS.
Guide de mise en œuvre : Cloud vs On-Premise
La décision architecturale va au-delà de la manière de regrouper les serveurs ; elle concerne l'endroit où ces serveurs résident. Pour les opérateurs multi-sites, le rapatriement du trafic d'authentification vers un centre de données sur site centralisé introduit une latence WAN et crée un point de défaillance unique au niveau de la liaison WAN.
Cloud RADIUS PlLes services Cloud RADIUS résolvent les défis de distribution géographique en hébergeant l'infrastructure d'authentification sur plusieurs zones de disponibilité mondiales. Lorsqu'un utilisateur se connecte sur un site distant, la requête est acheminée vers le nœud périphérique cloud le plus proche, minimisant ainsi la latence.
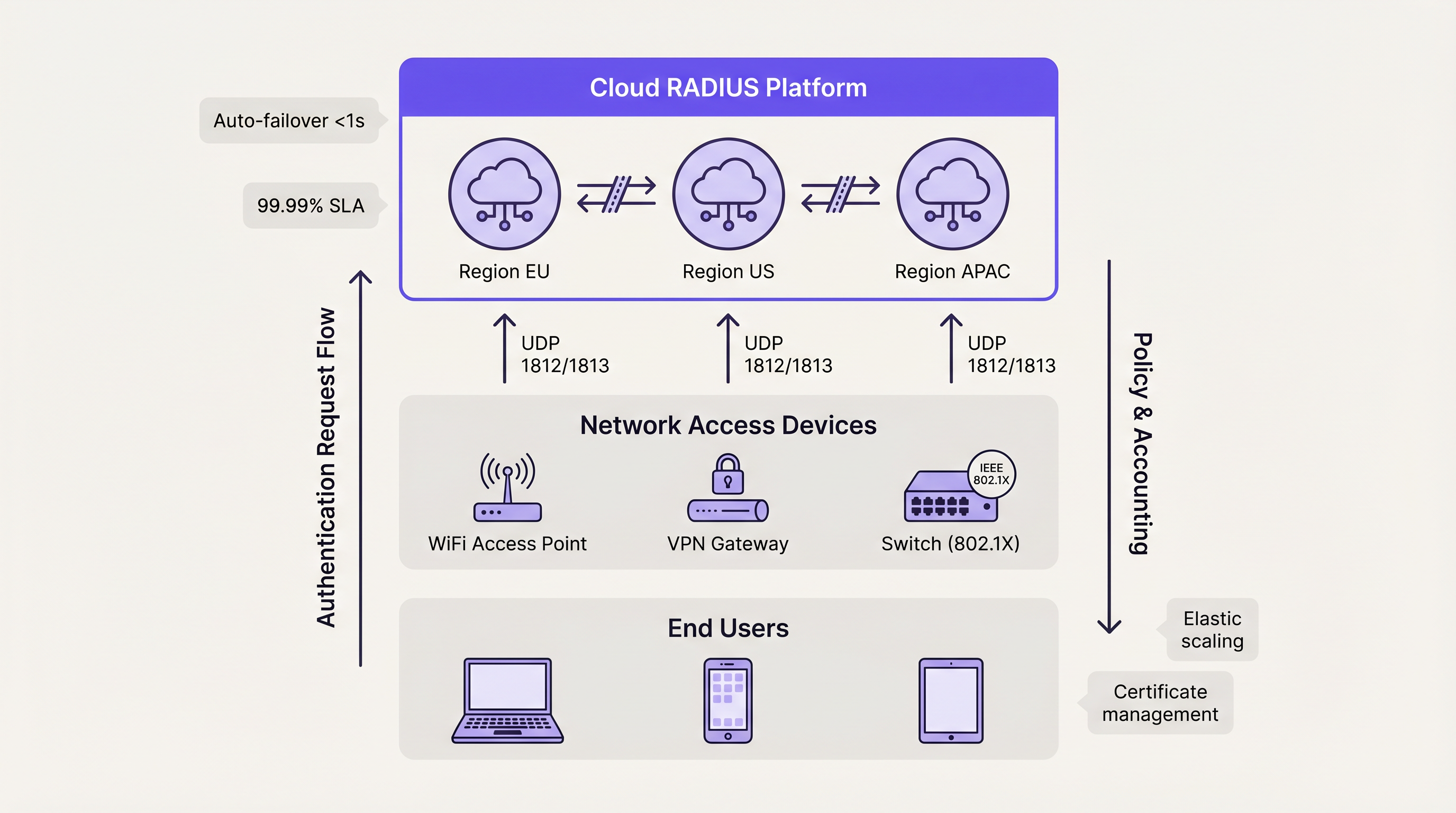
Les plateformes cloud utilisent intrinsèquement des architectures Actif-Actif. Le basculement entre les zones de disponibilité est géré automatiquement par l'équilibrage de charge interne du fournisseur, masquant entièrement la complexité pour l'équipe d'ingénierie du client. Ce modèle offre généralement des SLA de disponibilité de 99,99 % et élimine le besoin de gestion manuelle des certificats, de correctifs du système d'exploitation et d'ajustement de la réplication de la base de données. Pour les organisations déployant Wayfinding ou Sensors sur des campus distribués, l'authentification hébergée dans le cloud garantit une application cohérente des politiques sans dépendances matérielles locales.
Considérations sur le déploiement sur site
Les organisations opérant dans des secteurs hautement réglementés — tels que certains environnements de Santé ou gouvernementaux — peuvent nécessiter des déploiements sur site en raison de mandats stricts de souveraineté des données. Dans ces scénarios, le déploiement d'un cluster FreeRADIUS Actif-Actif avec réplication synchrone Galera offre le plus haut niveau de résilience.
Cependant, les équipes d'ingénierie doivent tenir compte de la surcharge opérationnelle. La gestion des certificats TLS sur plusieurs nœuds, la garantie de la cohérence de la configuration et la surveillance active de la santé de la réplication de la base de données nécessitent des ressources administratives dédiées. Les équilibreurs de charge matériels doivent être spécifiquement configurés pour prendre en charge le trafic UDP avec des contrôles de santé RADIUS appropriés, car de nombreux équilibreurs de charge standard sont optimisés uniquement pour le trafic TCP HTTP/HTTPS.
Meilleures pratiques pour la haute disponibilité RADIUS
- Distribuer plutôt que dupliquer : Pour les déploiements dépassant 500 utilisateurs simultanés, privilégiez les architectures Actif-Actif aux configurations Actif-Passif pour maximiser le débit et minimiser la latence de basculement.
- Implémenter la réplication synchrone : Protégez les données de comptabilité (accounting) avec état en utilisant la réplication de base de données multi-maître synchrone (ex: Galera Cluster) plutôt que des modèles primaire-réplique asynchrones.
- Standardiser la confiance des certificats : Dans un cluster Actif-Actif, assurez-vous que tous les nœuds présentent le même certificat de serveur ou des certificats provenant exactement de la même chaîne d'autorité de certification (CA). Les divergences entraîneront l'échec des handshakes EAP-TLS et PEAP lors de la rotation des nœuds.
- Ajuster les minuteurs NAD : Optimisez les minuteurs de tentative et de délai d'expiration RADIUS sur vos périphériques d'accès réseau (NAD). Un délai d'expiration de deux secondes avec deux tentatives offre un équilibre entre la détection rapide du basculement et la prévention d'un basculement prématuré lors d'une congestion mineure du réseau.
- Tester les scénarios de défaillance : Traitez les nœuds secondaires comme des systèmes de production. Simulez régulièrement des pannes de nœuds, des désynchronisations de base de données et des coupures de liaison WAN pour valider que les mécanismes de basculement automatisés fonctionnent comme prévu.
Dépannage et atténuation des risques
Le mode de défaillance le plus courant dans la haute disponibilité RADIUS est la dérive de configuration. Dans les configurations Actif-Passif, les administrateurs mettent fréquemment à jour les politiques ou renouvellent les certificats sur le nœud principal mais négligent le secondaire. Lorsqu'un événement de basculement se produit, le nœud secondaire rejette le trafic légitime en raison d'identifiants expirés ou de politiques obsolètes.
Pour atténuer ce risque, implémentez des outils de gestion de configuration (tels qu'Ansible ou Terraform) pour déployer les modifications de manière symétrique sur tous les nœuds. Pour la gestion des certificats, utilisez des protocoles de renouvellement automatisés (comme ACME) configurés pour distribuer le certificat mis à jour simultanément à l'ensemble du cluster.
Un autre risque important est la mauvaise configuration de l'équilibreur de charge. Si un équilibreur de charge n'effectue pas de contrôles de santé au niveau de la couche application (en vérifiant spécifiquement la réactivité du port UDP 1812), il peut continuer à acheminer le trafic vers un nœud où le système d'exploitation fonctionne mais où le démon RADIUS s'est arrêté. Assurez-vous que les contrôles de santé valident explicitement la disponibilité du service RADIUS.
ROI et impact commercial
Le retour sur investissement d'une haute disponibilité RADIUS robuste se mesure principalement par l'atténuation des risques et l'efficacité opérationnelle. Les pannes d'authentification entraînent des pertes de productivité immédiates pour les employés et de graves dommages à la réputation des lieux accueillant du public.
En passant de déploiements manuels sur serveur unique à des architectures Actif-Actif automatisées (particulièrement via Cloud RADIUS), les organisations récupèrent des heures d'ingénierie significatives auparavant dédiées à la maintenance de routine. Cette efficacité opérationnelle permet aux équipes réseau de se concentrer sur des initiatives stratégiques, telles que le déploiement de The Core SD WAN Benefits for Modern Businesses ou l'optimisation de la couverture haute densité, plutôt que de gérer les échecs d'authentification. En fin de compte, une authentification fiable est la couche fondamentale sur laquelle dépendent tous les services réseau ultérieurs.
Termes clés et définitions
Active-Active Architecture
A high availability design where multiple RADIUS servers process authentication requests simultaneously, distributing the load and providing instant failover without detection delays.
Essential for high-density venues (stadiums, large retail) where a single server cannot handle peak authentication surges.
Active-Passive Architecture
A redundancy model where a primary server handles all traffic, and a secondary server remains idle on standby until the primary fails.
Suitable for smaller, cost-sensitive deployments, but introduces a 6-18 second failover delay while the network access device detects the failure.
Synchronous Replication
A database replication method where data is written to all nodes in a cluster simultaneously before the transaction is considered complete.
Mandatory for Active-Active RADIUS accounting databases (like Galera Cluster) to prevent data loss and ensure compliance.
Asynchronous Replication
A database replication method where the primary node records the data and later copies it to secondary nodes, introducing a slight delay (lag).
Often used in Active-Passive setups but carries the risk of losing recent accounting records if the primary node fails abruptly.
Network Access Device (NAD)
The hardware component (such as a WiFi access point, switch, or VPN gateway) that requests authentication from the RADIUS server on behalf of the user.
The NAD's internal retry and timeout timers dictate how quickly an Active-Passive failover occurs.
Stateless Protocol
A communications protocol that treats each request as an independent transaction, unrelated to any previous request.
RADIUS authentication over UDP is stateless, allowing load balancers to route any request to any active server seamlessly.
Configuration Drift
The phenomenon where secondary or backup servers become out of sync with the primary server regarding policies, updates, or certificates over time.
The leading cause of failure in Active-Passive RADIUS deployments when the secondary node is forced to take over.
Cloud RADIUS
A managed authentication service hosted across globally distributed cloud infrastructure, providing built-in Active-Active redundancy and automatic scaling.
Replaces the need for IT teams to manually build, patch, and monitor redundant on-premise RADIUS servers.
Études de cas
A European hotel group manages 45 properties across six countries. They currently run independent FreeRADIUS virtual machines at each property. A recent expired TLS certificate at one location caused a complete guest WiFi outage during a major conference. How should they redesign their authentication architecture to prevent localized outages and reduce maintenance overhead?
The hotel group should migrate from localized, single-node FreeRADIUS instances to a centralized Cloud RADIUS platform utilizing an Active-Active architecture. By leveraging a cloud provider with geographically distributed edge nodes, authentication requests from each property are routed to the nearest regional node, minimizing latency. Centralized policy management allows the IT team to define authentication rules once and apply them globally. The cloud provider automatically handles TLS certificate rotation, operating system patching, and database replication.
A national sports stadium is preparing for a 60,000-attendee event. Their current RADIUS setup is an Active-Passive configuration. During load testing, the primary server became saturated processing 8,000 authentication requests per minute when the gates opened, causing severe connection delays, while the secondary server remained completely idle. How can they optimize this deployment?
The network engineering team must convert the deployment from Active-Passive to Active-Active. First, they should reconfigure the stadium's Network Access Devices (NADs) to utilize round-robin load balancing across both RADIUS servers, instantly doubling their authentication throughput. Second, they should provision a third RADIUS node to provide necessary headroom for peak surges. Finally, to ensure accounting data remains consistent across all three active nodes, they must implement a synchronous multi-master database replication solution, such as Galera Cluster.
Analyse de scénario
Q1. Your enterprise retail client requires a highly available RADIUS solution for their point-of-sale terminals. They have strict PCI DSS compliance requirements dictating that absolutely no accounting session data can be lost during a server failover. Which database replication strategy must you implement for the RADIUS backend?
💡 Astuce :Consider the difference between data being written simultaneously versus data being copied after the fact.
Afficher l'approche recommandée
You must implement Synchronous Replication (such as a Galera Cluster or MySQL NDB Cluster). Synchronous replication ensures that the accounting record is committed to all nodes simultaneously before acknowledging the transaction. If you used Asynchronous replication, a node failure could result in the loss of recent transactions that had not yet been copied to the secondary database, violating the strict compliance requirement.
Q2. A university campus network uses an Active-Passive RADIUS setup. Students complain that when the primary server undergoes maintenance, it takes nearly 20 seconds for their laptops to connect to the WiFi. The access points are configured with a 3-second RADIUS timeout and 5 retries. How can you reduce the failover delay without changing the server architecture?
💡 Astuce :Calculate the maximum wait time based on the NAD timers before it attempts the secondary server.
Afficher l'approche recommandée
You should tune the timers on the Network Access Devices (access points). Currently, the AP waits 3 seconds and retries 5 times, resulting in an 18-second delay (3 seconds × 6 total attempts) before failing over to the passive server. By reducing the configuration to a 2-second timeout and 2 retries, the failover detection time drops to 6 seconds, significantly improving the user experience during maintenance windows.
Q3. You are migrating a multi-site corporate network from an Active-Passive on-premise RADIUS server to an Active-Active Cloud RADIUS platform. During the pilot phase, devices successfully authenticate against Cloud Node A, but when the load balancer routes them to Cloud Node B, the EAP-TLS handshakes fail. What is the most likely configuration error?
💡 Astuce :Consider what the client device verifies when establishing a secure EAP tunnel with a new server.
Afficher l'approche recommandée
The most likely issue is a Certificate Trust mismatch. In an Active-Active cluster, all RADIUS nodes must present the exact same server certificate (or certificates issued by the exact same trusted CA chain). If Cloud Node B is presenting a different certificate that the client devices do not trust, the EAP-TLS handshake will be rejected by the client, causing authentication to fail despite the server functioning correctly.
Points clés à retenir
- ✓RADIUS high availability is critical because authentication failures immediately block all network access for users and devices.
- ✓Active-Passive setups are simpler but introduce a 6-18 second failover delay dictated by the Network Access Device's retry timers.
- ✓Active-Active architectures process requests simultaneously, providing instant failover and horizontal scalability for high-density environments.
- ✓While RADIUS authentication is stateless, accounting is stateful and requires synchronous database replication (like Galera) to prevent data loss.
- ✓Cloud RADIUS platforms abstract HA complexity by providing globally distributed, automatically scaling Active-Active infrastructure.
- ✓Configuration drift and mismatched TLS certificates are the most common causes of failure during RADIUS failover events.



