Cos'è l'autenticazione 802.1X? Come funziona e perché è importante
Una guida tecnica di riferimento completa per i responsabili IT e gli architetti di rete sull'autenticazione IEEE 802.1X. Questa guida illustra l'architettura sottostante, le strategie di implementazione, i vantaggi di sicurezza rispetto a PSK e come implementare efficacemente il controllo degli accessi di livello enterprise insieme alle soluzioni Guest WiFi.
🎧 Ascolta questa guida
Visualizza trascrizione
- Riepilogo Esecutivo
- Approfondimento Tecnico: Come funziona 802.1X
- L'Architettura a Tre Parti
- Il Flusso di Autenticazione
- Metodi EAP: Scegliere il Protocollo Giusto
- Guida all'Implementazione
- Fase 1: Preparazione dell'Infrastruttura
- Fase 2: Configurazione del Supplicante
- Fase 3: Pilot e Rollout
- Integrazione con l'Accesso Ospiti
- Migliori Pratiche
- Risoluzione dei Problemi e Mitigazione dei Rischi
- ROI e Impatto sul Business
- Briefing Audio

Riepilogo Esecutivo
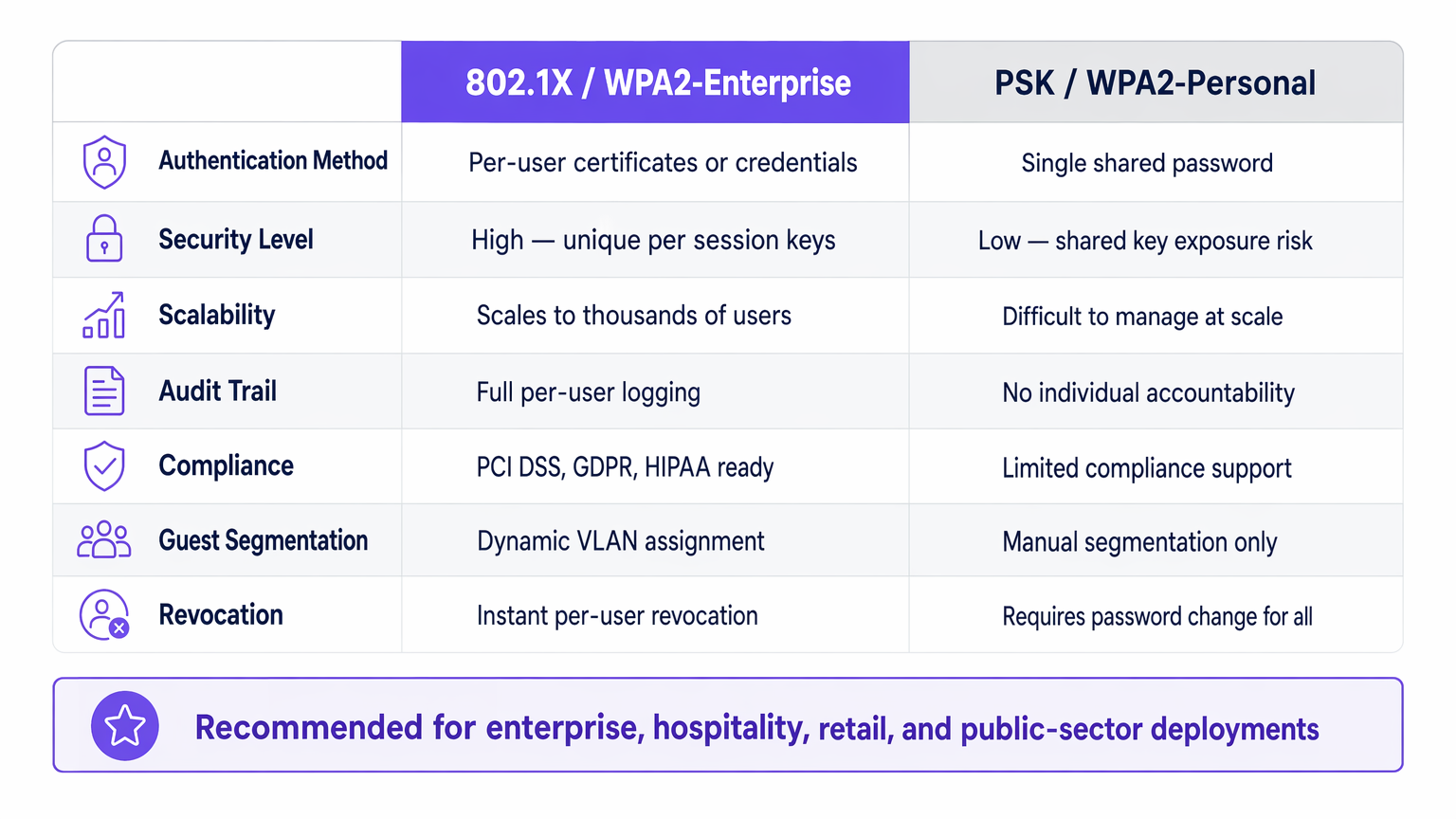
Per i leader IT aziendali che gestiscono reti in sedi Ospitalità , Retail , Sanità o Trasporti , la sicurezza dell'accesso alla rete è un requisito fondamentale. Affidarsi a chiavi pre-condivise (PSK) per l'accesso aziendale introduce rischi inaccettabili: mancanza di responsabilità individuale, processi di revoca complessi e vulnerabilità di crittografia condivise.
IEEE 802.1X è il framework standard di settore per il controllo degli accessi di rete basato su porta. Applica un rigoroso processo di autenticazione prima che un dispositivo possa comunicare sulla rete, consentendo la verifica dell'identità per utente, l'applicazione dinamica delle policy e la conformità con framework come PCI DSS e GDPR. Questa guida esplora i meccanismi di 802.1X, le differenze tra i metodi EAP comuni e le strategie di implementazione pratiche per gli ambienti aziendali, incluso come si integra con le soluzioni Guest WiFi per fornire una strategia di accesso olistica.
Approfondimento Tecnico: Come funziona 802.1X
Al suo interno, 802.1X opera su un modello a tre parti progettato per isolare i dispositivi non autenticati dalla rete interna.
L'Architettura a Tre Parti
- Supplicante: Il dispositivo dell'utente finale (laptop, smartphone, sensore IoT) che richiede l'accesso alla rete. Deve eseguire un client software conforme a 802.1X.
- Autenticatore: Il dispositivo di rete (access point wireless o switch gestito) che controlla la porta fisica o logica. Agisce come un guardiano, bloccando tutto il traffico eccetto EAP (Extensible Authentication Protocol) fino a quando l'autenticazione non ha successo.
- Server di Autenticazione: Tipicamente un server RADIUS (Remote Authentication Dial-In User Service). Convalida le credenziali del supplicante rispetto a un archivio di identità backend (come Active Directory) e restituisce una decisione di policy.
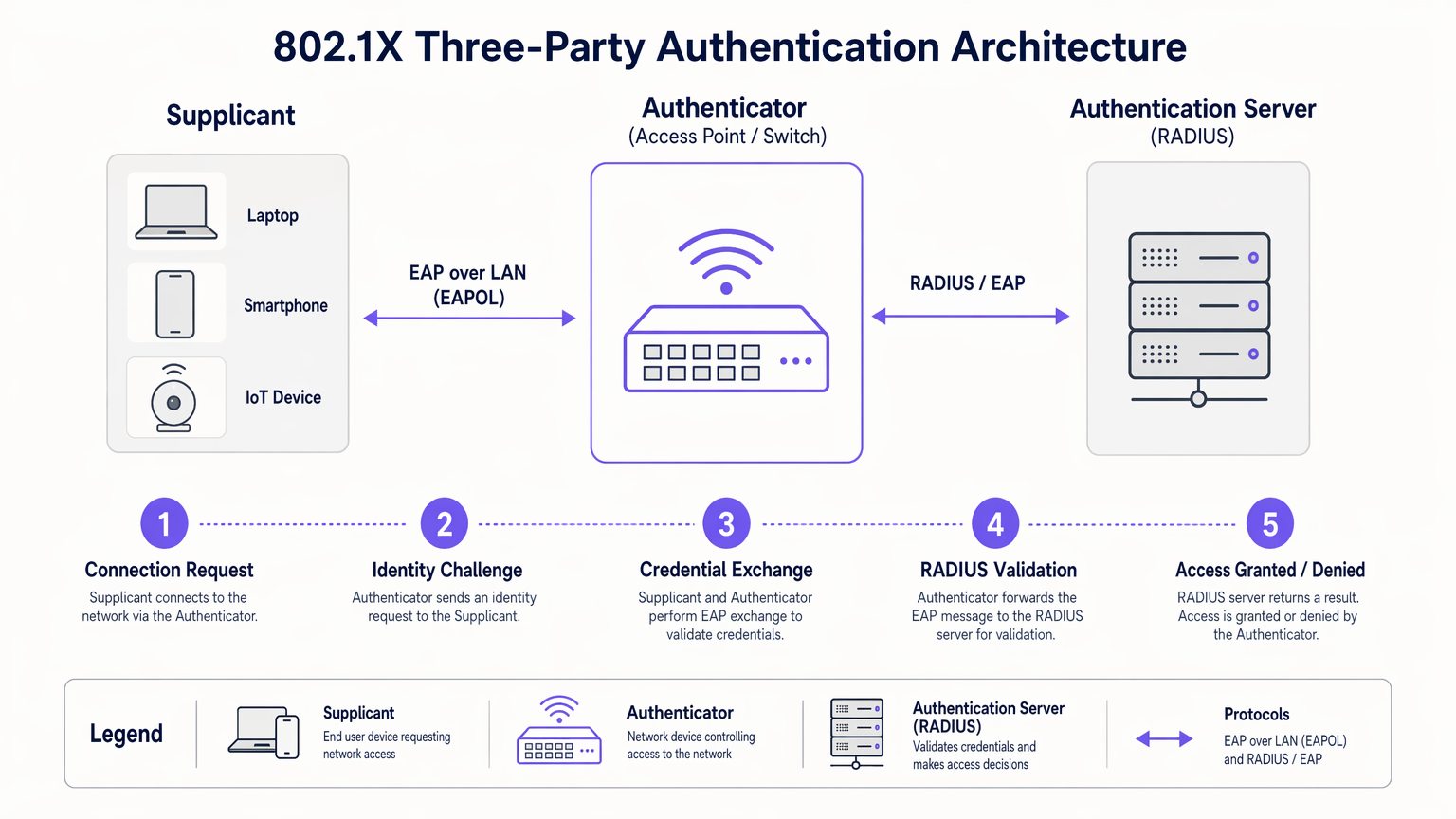
Il Flusso di Autenticazione
Quando un supplicante si connette a una porta o SSID abilitato 802.1X, l'autenticatore pone la porta in uno stato non autorizzato. Il flusso procede come segue:
- EAPOL Start: Il supplicante invia un frame EAP over LAN (EAPOL) Start all'autenticatore.
- Richiesta di Identità: L'autenticatore richiede l'identità del supplicante.
- Risposta di Identità: Il supplicante fornisce la sua identità, che l'autenticatore inoltra al server RADIUS tramite un pacchetto RADIUS Access-Request.
- Scambio EAP: Il server RADIUS e il supplicante negoziano un metodo EAP e scambiano le credenziali in modo sicuro tramite l'autenticatore.
- Decisione di Accesso: In caso di convalida riuscita, il server RADIUS invia un pacchetto RADIUS Access-Accept all'autenticatore. Questo pacchetto spesso include attributi specifici del fornitore (VSA) per l'assegnazione dinamica di VLAN o policy QoS.
- Porta Autorizzata: L'autenticatore porta la porta a uno stato autorizzato, consentendo il normale traffico di rete.
Metodi EAP: Scegliere il Protocollo Giusto
Il framework EAP è estensibile. La scelta del metodo EAP determina come le credenziali vengono scambiate e verificate:
- EAP-TLS (Transport Layer Security): Lo standard d'oro per la sicurezza. Richiede l'autenticazione reciproca utilizzando certificati digitali sia sul client che sul server. Sebbene altamente sicuro, richiede una robusta infrastruttura a chiave pubblica (PKI).
- PEAP-MSCHAPv2 (Protected EAP): La distribuzione più comune negli ambienti aziendali. Utilizza un certificato lato server per stabilire un tunnel TLS sicuro, all'interno del quale il client si autentica utilizzando un nome utente e una password standard (MSCHAPv2). Bilancia la sicurezza con la semplicità di implementazione.
- EAP-TTLS (Tunneled TLS): Simile a PEAP ma supporta una gamma più ampia di protocolli di autenticazione interni, inclusi PAP o CHAP legacy, spesso utilizzati in ambienti non Windows.
Guida all'Implementazione
La distribuzione di 802.1X richiede un'attenta pianificazione per evitare interruzioni agli utenti. Un approccio a fasi è fondamentale per il successo.
Fase 1: Preparazione dell'Infrastruttura
Prima di abilitare 802.1X sul perimetro, assicurati che la tua infrastruttura core sia preparata. Implementa un server RADIUS (come Microsoft NPS o FreeRADIUS) e integralo con il tuo provider di identità. Configura l'alta disponibilità per l'infrastruttura RADIUS; se il server di autenticazione fallisce, l'accesso alla rete si interrompe.
Fase 2: Configurazione del Supplicante
Non fare affidamento sugli utenti per configurare manualmente i propri dispositivi. Per i dispositivi aziendali gestiti, utilizza oggetti Criteri di gruppo (GPO) o piattaforme di Mobile Device Management (MDM) per distribuire il profilo 802.1X corretto, inclusi il metodo EAP richiesto e il certificato radice attendibile per il server RADIUS.
Fase 3: Pilot e Rollout
Inizia con un piccolo gruppo pilota utilizzando un SSID di test dedicato o uno stack di switch specifico. Monitora i log RADIUS per eventuali errori di autenticazione, in particolare quelli relativi a problemi di fiducia dei certificati o credenziali errate. Una volta che il pilot è stabile, procedi con un rollout a fasi in tutta l'organizzazione.
Integrazione con l'Accesso Ospiti
802.1X è progettato per utenti aziendali con credenziali note. Per visitatori, appaltatori e clienti, è necessaria una strategia parallela. Qui una piattaforma Guest WiFi dedicata diventa essenziale. Mentre i dispositivi aziendali si autenticano senza problemi tramite 802.1X su VLAN sicure, gli ospiti si autenticano tramite un captive portal, fornendo preziosi dati di prima parte per WiFi Analytics pur rimanendo isolati dalle risorse interne.
La piattaforma di Purple può anche fungere da provider di identità per servizi come OpenRoaming con licenza Connect, colmando il divario tra accesso pubblico senza interruzioni e autenticazione sicura.
Migliori Pratiche
- **Applica il Server Validazione del Certificato: Quando si utilizzano PEAP o EAP-TTLS, è necessario configurare i supplicanti per convalidare il certificato del server RADIUS. La mancata esecuzione di questa operazione rende la rete vulnerabile agli attacchi di punti di accesso non autorizzati (Evil Twin).
- Implementare l'Assegnazione Dinamica di VLAN: Sfruttare gli attributi RADIUS per assegnare gli utenti a VLAN specifiche in base alla loro appartenenza a gruppi di Active Directory. Ciò riduce il numero di SSID richiesti e semplifica la segmentazione della rete.
- Gestire i Dispositivi IoT con MAB: Molti dispositivi IoT (stampanti, smart TV) non supportano i supplicanti 802.1X. Utilizzare il MAC Authentication Bypass (MAB) come soluzione di ripiego. L'autenticatore utilizza l'indirizzo MAC del dispositivo come nome utente e password. Poiché gli indirizzi MAC possono essere contraffatti, limitare rigorosamente i privilegi di accesso dei dispositivi autenticati tramite MAB.
Risoluzione dei Problemi e Mitigazione dei Rischi
Quando l'802.1X fallisce, i log del server RADIUS sono il vostro principale strumento diagnostico.
- Errore: EAP Timeout: L'autenticatore non riceve una risposta dal supplicante. Ciò spesso indica che il software del supplicante non è in esecuzione o che il dispositivo non è configurato per l'802.1X.
- Errore: Utente Sconosciuto o Password Errata: L'utente ha inserito credenziali errate o il server RADIUS non può comunicare con l'archivio di identità backend.
- Errore: Fallimento della Fiducia del Certificato: Il supplicante ha rifiutato il certificato del server RADIUS. Assicurarsi che il certificato della CA radice che ha emesso il certificato del server RADIUS sia installato nell'archivio radice attendibile del supplicante.
Per una prospettiva più ampia sull'ottimizzazione dell'architettura di rete, considerate come l'autenticazione si integri con le moderne strategie WAN, come discusso in I Vantaggi Chiave dell'SD WAN per le Aziende Moderne .
ROI e Impatto sul Business
L'implementazione dell'802.1X offre un valore aziendale misurabile che va oltre la semplice sicurezza:
- Costi Operativi Ridotti: Elimina la necessità di ruotare manualmente le PSK quando i dipendenti lasciano l'azienda o i collaboratori terminano i loro incarichi. L'accesso viene revocato istantaneamente disabilitando l'account utente nella directory.
- Conformità Semplificata: Fornisce i percorsi di audit per utente e i robusti controlli di accesso richiesti da PCI DSS, HIPAA e GDPR.
- Visibilità di Rete Migliorata: Integra l'identità con l'attività di rete, consentendo ai team IT di tracciare eventi di sicurezza o problemi di prestazioni a utenti specifici anziché a indirizzi IP generici.
Abbandonando le chiavi condivise e adottando il controllo degli accessi basato su porta, le reti aziendali raggiungono la sicurezza granulare richiesta dalle moderne esigenze operative. Per un confronto dettagliato degli standard di sicurezza wireless, consultate la nostra guida su WPA, WPA2 e WPA3: Qual è la Differenza e Quale Dovreste Usare? .
Briefing Audio
Ascoltate il nostro briefing tecnico di 10 minuti sull'autenticazione 802.1X:
Termini chiave e definizioni
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational standard replacing shared passwords with per-user authentication in enterprise networks.
Supplicant
The software client on an end-user device that requests network access and handles the EAP exchange.
Required on all laptops, phones, and tablets connecting to an 802.1X network.
Authenticator
The network edge device (switch or access point) that controls the physical or logical port, blocking traffic until authentication is complete.
The enforcement point in the network architecture.
RADIUS Server
Remote Authentication Dial-In User Service. The central server that validates credentials against a directory and returns policy decisions.
The brain of the 802.1X deployment, often implemented via Microsoft NPS or Cisco ISE.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections, providing transport for various authentication methods.
The language spoken between the supplicant and the RADIUS server.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the authenticator to place a user into a specific VLAN based on their identity or group membership.
Crucial for network segmentation and compliance without broadcasting dozens of SSIDs.
EAP-TLS
An EAP method requiring mutual certificate-based authentication between the client and the server.
The most secure method, ideal for highly regulated environments like healthcare or finance.
PEAP (Protected EAP)
An EAP method that establishes a secure TLS tunnel using a server certificate, protecting the inner credential exchange (usually a username/password).
The most common deployment method due to its balance of security and operational simplicity.
Casi di studio
A 200-room hotel needs to secure its back-of-house operational network (staff tablets, VoIP phones, management laptops) while maintaining a separate, open guest network. They currently use a single PSK for staff.
- Deploy Microsoft NPS (RADIUS) integrated with the hotel's Active Directory.
- Configure the wireless controller to broadcast a new 'Staff_Secure' SSID using WPA2-Enterprise (802.1X).
- Push a PEAP-MSCHAPv2 profile to all managed staff laptops and tablets via MDM.
- For VoIP phones lacking 802.1X support, configure MAC Authentication Bypass (MAB) on the RADIUS server, assigning them to an isolated Voice VLAN.
- Retain the open guest network, securing it with Purple's captive portal for guest isolation and analytics.
A large retail chain is failing PCI DSS compliance because their Point of Sale (PoS) terminals are on the same logical network segment as store manager laptops, using a shared WPA2-Personal key.
- Implement 802.1X across all corporate access points.
- Configure dynamic VLAN assignment on the RADIUS server.
- Create a policy: If the authenticating device is a PoS terminal (authenticated via machine certificate using EAP-TLS), assign it to the highly restricted PCI-VLAN.
- Create a second policy: If the user is a Store Manager (authenticated via PEAP), assign them to the Corp-VLAN with standard internet and intranet access.
Analisi degli scenari
Q1. Your organization is migrating from WPA2-Personal to WPA2-Enterprise. You have a mix of corporate-owned Windows laptops and employee-owned BYOD smartphones. You do not have a PKI infrastructure. Which EAP method should you deploy?
💡 Suggerimento:Consider the requirement for client certificates versus server-only certificates.
Mostra l'approccio consigliato
PEAP-MSCHAPv2. Since you lack a PKI infrastructure, deploying client certificates for EAP-TLS is not feasible. PEAP only requires a server-side certificate on the RADIUS server, allowing users to authenticate with their standard Active Directory username and password.
Q2. After deploying 802.1X using PEAP, several users report they are prompted with a security warning asking them to 'Trust' a certificate when connecting to the network. What configuration step was missed?
💡 Suggerimento:Think about how the supplicant validates the identity of the RADIUS server.
Mostra l'approccio consigliato
The supplicant profile pushed to the devices was not configured to explicitly trust the Root CA that issued the RADIUS server's certificate. Without this configuration, the OS prompts the user to manually verify the server's identity, which is a security risk and poor user experience.
Q3. You need to connect 50 smart TVs in hotel conference rooms to the network. These devices do not support 802.1X supplicants. How can you provide them access while maintaining security?
💡 Suggerimento:Consider alternative authentication methods for headless devices and how to restrict their access.
Mostra l'approccio consigliato
Implement MAC Authentication Bypass (MAB). The authenticator will use the smart TV's MAC address to authenticate against the RADIUS server. Crucially, the RADIUS server must be configured to assign these devices to a heavily restricted VLAN (e.g., internet-only, no internal access) to mitigate the risk of MAC address spoofing.



