Ridurre al minimo le distrazioni degli studenti con il blocco degli annunci a livello di rete
Questa guida tecnica di riferimento autorevole descrive in dettaglio l'architettura, l'implementazione e l'impatto aziendale del blocco degli annunci a livello di rete negli ambienti educativi. Fornisce a responsabili IT e architetti di rete strategie attuabili per recuperare larghezza di banda, rafforzare la conformità ed eliminare i rischi di malvertising.
Ascolta questa guida
Visualizza trascrizione del podcast
- Riepilogo Esecutivo
- Approfondimento Tecnico
- Architettura di Filtraggio a Livello DNS
- Proxy e Ispezione SSL
- Integrazione con il Controllo dell'Accesso alla Rete (NAC)
- Guida all'Implementazione
- Fase 1: Audit del Traffico e Definizione della Baseline
- Fase 2: Implementazione Pilota
- Fase 3: Rollout Completo e Ottimizzazione delle Politiche
- Migliori Pratiche
- Risoluzione dei Problemi e Mitigazione del Rischio
- ROI e Impatto sul Business
Riepilogo Esecutivo
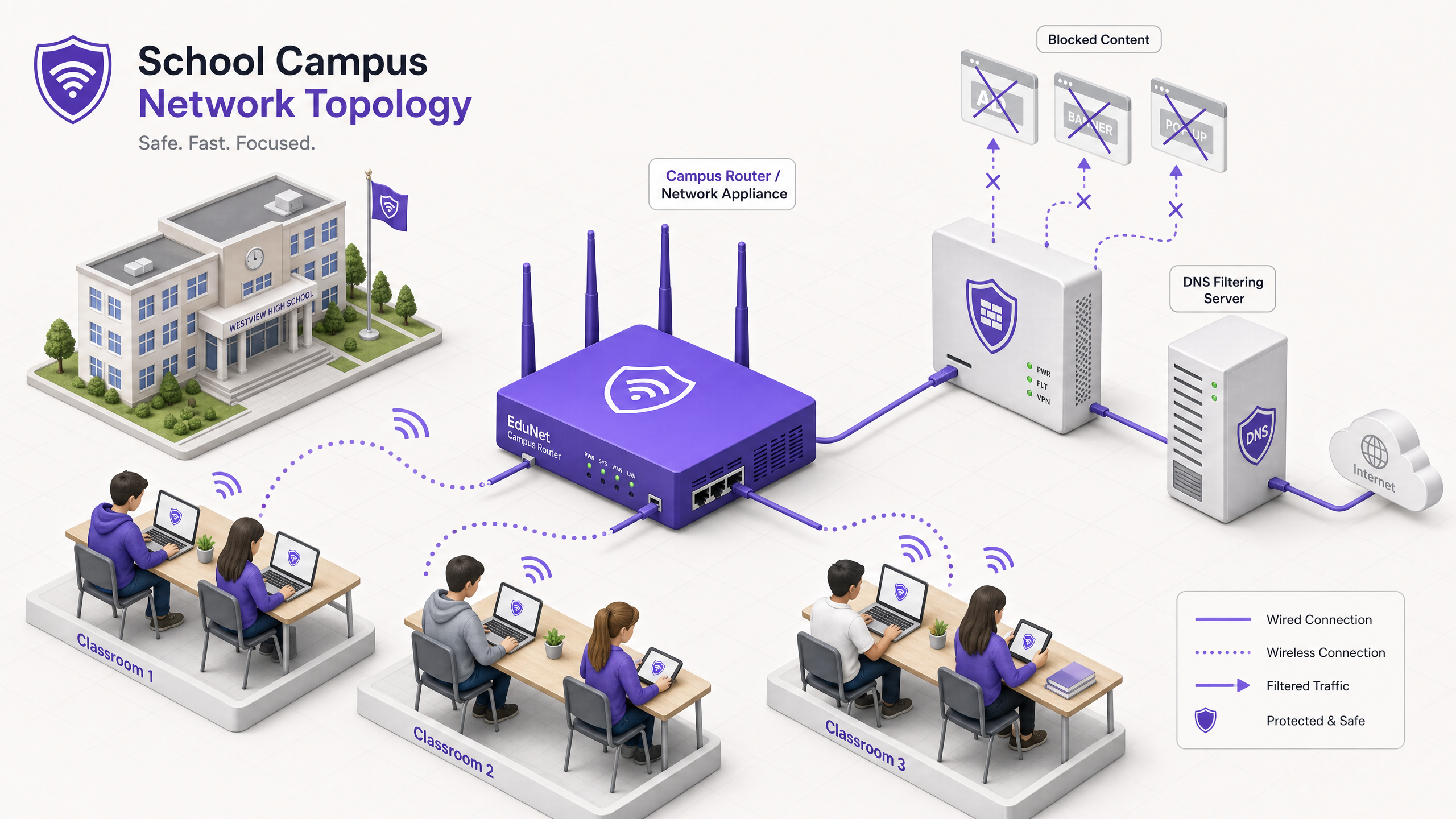
Per i Direttori IT e gli architetti di rete che gestiscono ambienti educativi, la proliferazione dei dispositivi ha creato una tempesta perfetta di consumo di larghezza di banda, rischi per la sicurezza e lacune nella conformità. Con gli studenti che portano in media 2,5 dispositivi nel campus, la gestione del filtraggio basato su endpoint non è più una strategia operativa praticabile.
Il blocco degli annunci a livello di rete rappresenta un cambiamento fondamentale dalla gestione degli endpoint al controllo a livello di infrastruttura. Intercettando il traffico a livello DNS o proxy prima che raggiunga il dispositivo client, i team IT possono eliminare unilateralmente fino al 30% del consumo di larghezza di banda non educativo, mitigare i rischi di malvertising e imporre la conformità con i framework di protezione dei dati come GDPR e COPPA.
Questa guida tecnica di riferimento delinea l'architettura, la metodologia di implementazione e la misurazione del ROI per l'implementazione del blocco degli annunci a livello di rete nei campus K-12 e universitari, basandosi su implementazioni reali in ambienti ad alta densità.
Ascolta il nostro podcast di accompagnamento per una panoramica strategica:
Approfondimento Tecnico
L'implementazione del blocco degli annunci a livello di rete richiede un approccio architetturale a strati per gestire la diversità del traffico web moderno, in particolare l'ubiquità di HTTPS e i protocolli DNS crittografati emergenti.
Architettura di Filtraggio a Livello DNS
Lo strato fondamentale del blocco degli annunci di rete è il filtraggio DNS. Quando un dispositivo client tenta di risolvere un dominio associato a reti pubblicitarie, telemetria o tracciamento, il resolver DNS della rete intercetta la query e la confronta con una blocklist dinamica.
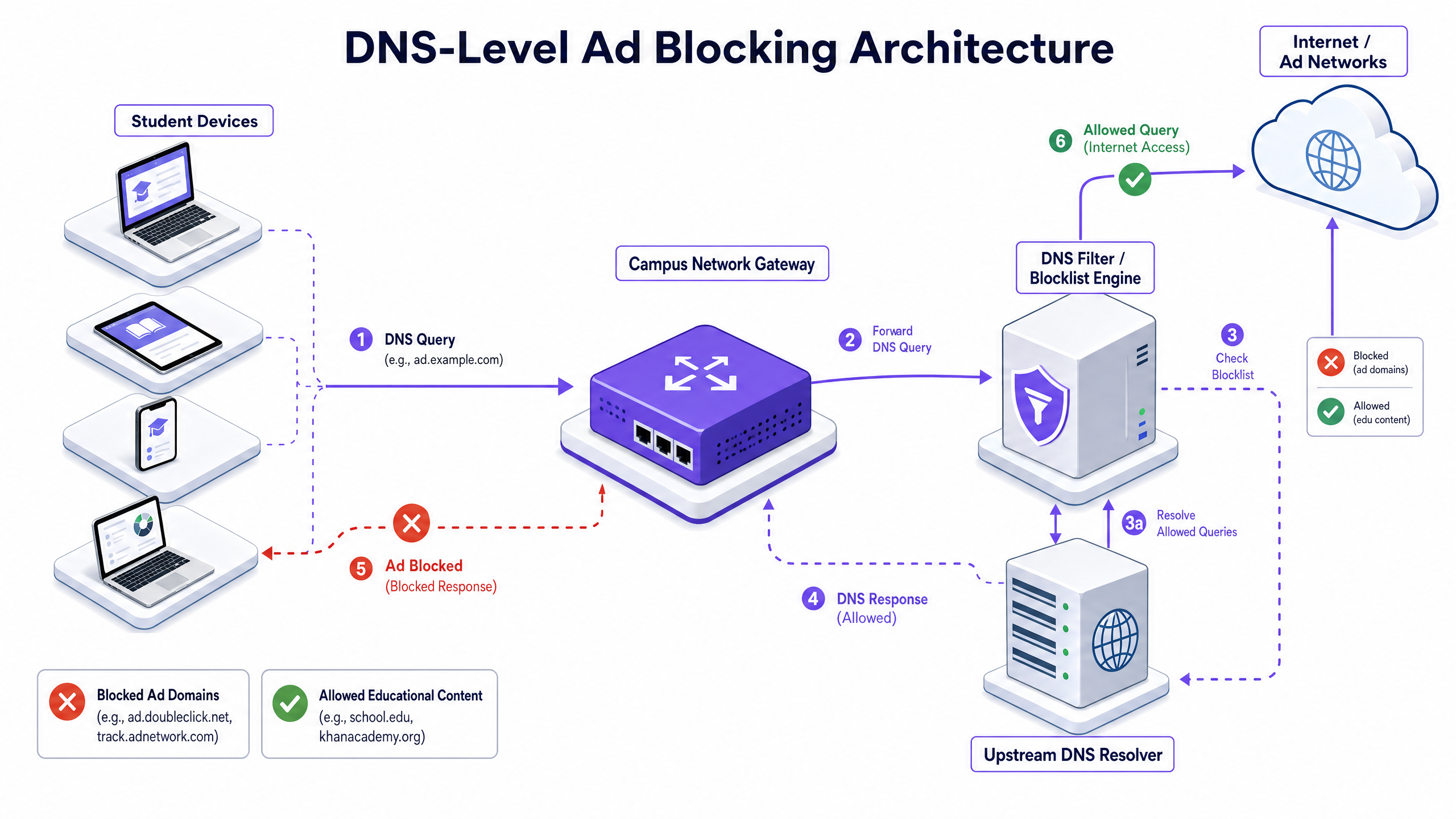
Questo approccio è altamente efficiente perché impedisce che la connessione venga mai stabilita. Il payload dell'annuncio non viene mai scaricato e lo script di tracciamento non viene mai eseguito. Tuttavia, le implementazioni moderne devono tenere conto di DNS-over-HTTPS (DoH) e DNS-over-TLS (DoT). Se i dispositivi client bypassano il resolver locale utilizzando DNS crittografato, lo strato di filtraggio viene aggirato. Gli architetti di rete devono configurare i firewall perimetrali per bloccare gli endpoint DoH/DoT noti (come 8.8.8.8 sulla porta 443) per forzare il fallback al DNS standard (porta 53), o implementare una soluzione gateway che ispeziona nativamente il traffico DoH.
Proxy e Ispezione SSL
Mentre il filtraggio DNS gestisce la maggior parte del traffico pubblicitario, il proxying HTTP/HTTPS trasparente fornisce un controllo granulare su URL specifici piuttosto che su interi domini. Poiché la stragrande maggioranza del traffico web è crittografata, l'implementazione dell'ispezione SSL (decrittografia Man-in-the-Middle) è necessaria per l'ispezione approfondita dei pacchetti.
Ciò richiede l'implementazione di un certificato radice attendibile su tutti i dispositivi gestiti. Sebbene sia una pratica standard negli ambienti aziendali, l'ispezione SSL in contesti educativi richiede un'attenta definizione dell'ambito per evitare di decrittografare traffico sensibile (ad esempio, portali bancari o sanitari) e deve essere allineata con la politica di utilizzo accettabile dell'organizzazione.
Integrazione con il Controllo dell'Accesso alla Rete (NAC)
Un filtraggio efficace richiede politiche sensibili all'identità. L'integrazione con IEEE 802.1X consente alla rete di applicare politiche di filtraggio differenziate basate sull'utente autenticato o sul profilo del dispositivo. Uno studente che accede alla rete tramite WPA3-Enterprise riceve una politica restrittiva, mentre un membro del personale riceve una politica diversa e un visitatore sulla rete Guest WiFi riceve una politica di conformità di base.
Guida all'Implementazione
L'implementazione del blocco degli annunci a livello di rete richiede un approccio graduale per evitare di interrompere le legittime attività educative.
Fase 1: Audit del Traffico e Definizione della Baseline
Prima di implementare qualsiasi regola di blocco, implementare la soluzione di filtraggio in modalità di monitoraggio passivo (solo logging) per 14-21 giorni. Ciò stabilisce una baseline dei volumi e della categorizzazione delle query DNS attuali. Utilizzare questi dati per identificare le principali reti pubblicitarie e i domini di tracciamento che attualmente consumano larghezza di banda. Questa baseline è fondamentale per il calcolo successivo del ROI e per il reporting di WiFi Analytics .
Fase 2: Implementazione Pilota
Selezionare un segmento di rete rappresentativo, come una singola VLAN studentesca o un edificio specifico, per la fase pilota. Applicare le politiche iniziali della blocklist che mirano a reti pubblicitarie e tracker noti.
Passo Cruciale: Stabilire un processo di richiesta di whitelist a risposta rapida. Gli insegnanti incontreranno inevitabilmente falsi positivi in cui contenuti educativi legittimi sono ospitati su domini categorizzati come pubblicitari o di tracciamento. L'helpdesk IT deve essere preparato a valutare e whitelisting i domini rapidamente per mantenere la fiducia degli stakeholder.
Fase 3: Rollout Completo e Ottimizzazione delle Politiche
Estendere l'implementazione a tutti i segmenti di rete pertinenti, applicando politiche differenziate tramite l'integrazione 802.1X. Monitorare i log continuamente per le prime 48 ore per identificare eventuali problemi sistemici.
Assicurarsi che l'implementazione sia allineata con politiche di sicurezza più ampie, come il mantenimento di un Explain what is audit trail for IT Security in 2026 per dimostrare la conformità ai requisiti di salvaguardia.
Migliori Pratiche
- Difesa a Strati: Non fare affidamento esclusivamente sul filtraggio DNS. Combinarlo con la gestione degli endpoint per i dispositivi di proprietà della scuola e robuste regole firewall per bloccare i tentativi di bypass (ad esempio, protocolli VPN, DoH).
- Sicurezza Standardizzata: Assicurarsi che tutte le nuove implementazioni wireless utilizzino WPA3 per proteggere contro il furto di credenziali, che è una comune vvettore per gli studenti che tentano di accedere alle reti del personale per aggirare il filtraggio.
- Allineamento alla Conformità: Nel Regno Unito, assicurati che le tue politiche di filtraggio soddisfino i requisiti di base delineati nella IWF Compliance for Public WiFi Networks in the UK (o Cumplimiento IWF para redes WiFi públicas en el Reino Unido per le operazioni di lingua spagnola).
- Revisione Regolare: Le reti pubblicitarie cambiano costantemente i domini per eludere le blocklist. Assicurati che la tua soluzione di filtraggio utilizzi feed di intelligence sulle minacce aggiornati dinamicamente anziché elenchi statici.
Risoluzione dei Problemi e Mitigazione del Rischio
| Modalità di Fallimento | Causa Radice | Strategia di Mitigazione |
|---|---|---|
| Bypass tramite DNS Crittografato | Studenti che configurano i browser per utilizzare DoH/DoT (es. Cloudflare, Google DNS). | Blocca gli indirizzi IP noti dei provider DoH sul firewall; imposta la risoluzione DNS locale tramite DHCP. |
| Bypass tramite VPN | Utilizzo di client VPN commerciali o estensioni del browser. | Blocca i protocolli VPN comuni (IPsec, OpenVPN, WireGuard) e i domini noti dei provider VPN sulle VLAN degli studenti. |
| Sovra-blocco (Falsi Positivi) | Filtraggio euristico aggressivo che blocca contenuti educativi. | Implementa un processo semplificato di richiesta di whitelist, supportato da SLA, per il personale docente; testa le politiche a fondo prima del dispiegamento completo. |
| Fuga IPv6 | Filtraggio applicato solo a IPv4, consentendo il bypass tramite risoluzione DNS IPv6. | Assicurati che la soluzione di filtraggio e l'infrastruttura di rete supportino e applichino pienamente le politiche attraverso lo stack IPv6. |
ROI e Impatto sul Business
Il business case per il blocco degli annunci a livello di rete va oltre la salvaguardia; offre efficienze operative misurabili.
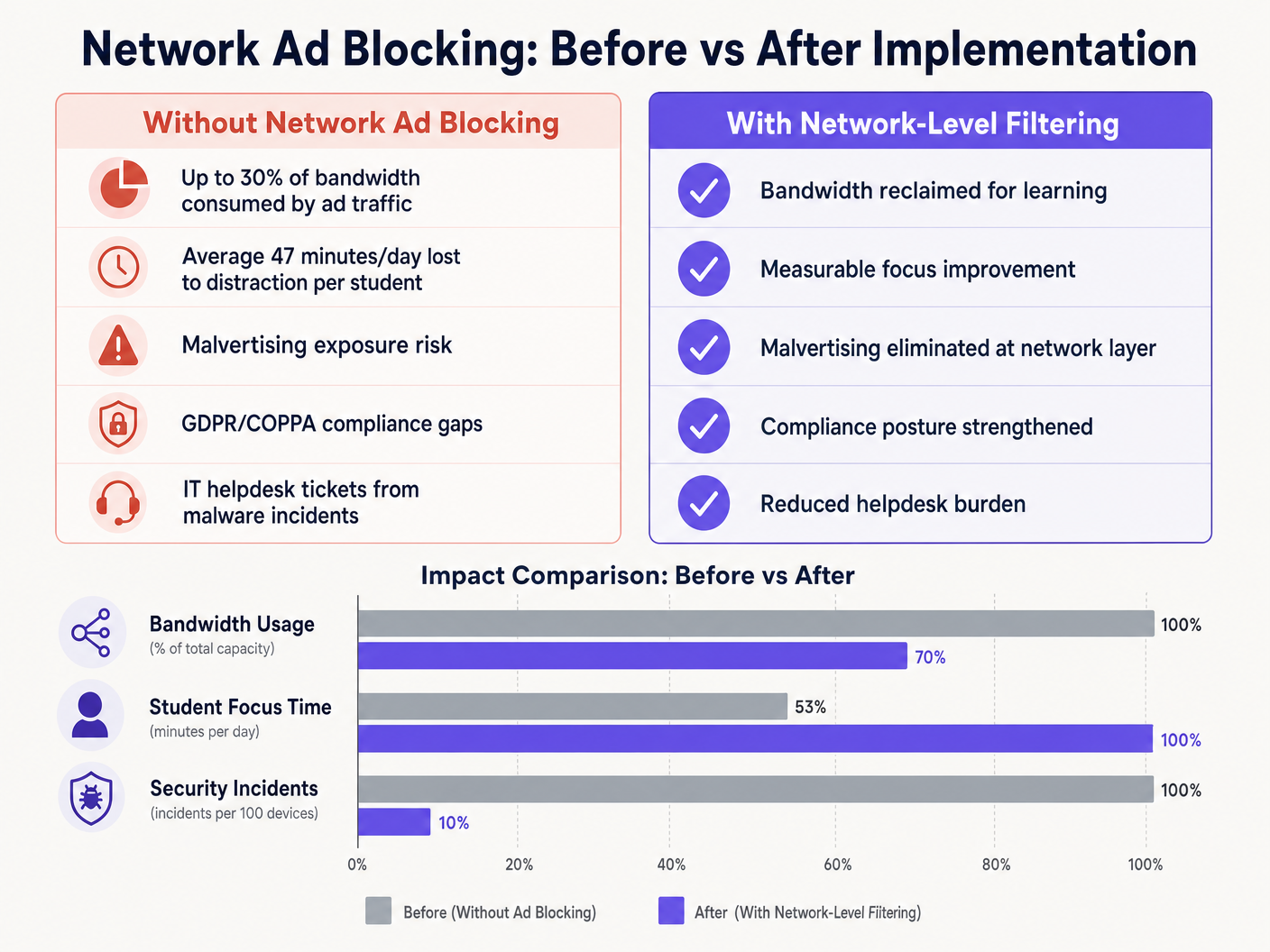
Eliminando i payload pubblicitari e gli script di tracciamento al bordo della rete, le sedi tipicamente recuperano dal 15% al 30% della loro larghezza di banda totale. Questa capacità recuperata posticipa la necessità di costosi aggiornamenti dei circuiti e migliora le prestazioni delle applicazioni cloud critiche. Inoltre, il blocco dei domini di malvertising a livello DNS riduce significativamente il volume degli incidenti malware, abbassando direttamente i volumi dei ticket dell'helpdesk IT e i costi di bonifica.
Sia che si tratti di implementare in una scuola, ottimizzare Wi-Fi per l'Ufficio: Ottimizza la Tua Rete Wi-Fi Moderna , o gestire ambienti ad alta densità in Vendita al Dettaglio , Sanità , Ospitalità , o Trasporti , comprendere il livello fisico, come Frequenze Wi-Fi: Una Guida alle Frequenze Wi-Fi nel 2026 , e proteggere il livello logico tramite il filtraggio DNS sono componenti essenziali dell'architettura di rete moderna.
Definizioni chiave
DNS Filtering
The process of using the Domain Name System to block malicious websites and filter out harmful or unwanted content by returning a null IP address for blocked domains.
The primary mechanism for network-level ad blocking, operating upstream of client devices.
DNS-over-HTTPS (DoH)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
A common method used to bypass local network DNS filtering policies.
Malvertising
The use of online advertising to spread malware, often through legitimate advertising networks without the publisher's knowledge.
A key security risk mitigated by network-level ad blocking.
SSL Inspection
The process of intercepting, decrypting, and inspecting HTTPS traffic for malicious content or policy violations before re-encrypting and forwarding it.
Required for deep packet inspection of encrypted web traffic, though complex to deploy in BYOD environments.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Used to identify users and devices to apply differentiated filtering policies.
WPA3-Enterprise
The latest generation of Wi-Fi security, providing enhanced cryptographic strength and protecting against dictionary attacks.
Essential for securing campus networks and ensuring users cannot easily spoof identities to bypass filtering.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
Used to segment student, staff, and guest traffic to apply different security and filtering policies.
Transparent Proxy
An intermediary system that sits between a user and a content provider, intercepting requests without requiring client-side configuration.
Used to enforce URL-level filtering policies without deploying endpoint agents.
Esempi pratici
A large multi-academy trust with 15,000 students across 12 campuses needs to implement ad blocking. They currently use a mix of school-issued Chromebooks and a BYOD policy for sixth-form students. The network is struggling with bandwidth congestion during peak hours.
- Deploy a cloud-managed DNS filtering solution across all 12 campuses, pointing all DHCP-assigned DNS settings to the cloud resolvers.
- Configure the firewall to block outbound port 53 traffic to any external IP other than the approved cloud resolvers to prevent manual DNS overrides.
- Block known DoH provider IPs at the firewall.
- Integrate the DNS filtering solution with the trust's Active Directory via 802.1X to apply different filtering policies: a strict policy for the Chromebook VLAN and a slightly more permissive policy for the BYOD VLAN, while maintaining core ad and malvertising blocking across both.
A university campus IT team receives complaints from the Computer Science faculty that the new network ad blocking solution is preventing access to legitimate development tools and APIs used in coursework.
- Review the DNS query logs for the Computer Science VLAN to identify the specific domains being blocked.
- Create a dedicated policy group for the Computer Science faculty and student VLANs.
- Implement a scoped whitelist for the required development domains, applying it only to the Computer Science policy group to maintain security across the rest of the campus.
- Establish a fast-track IT ticketing category specifically for 'Educational Content Blocking' to handle future requests with a 2-hour SLA.
Domande di esercitazione
Q1. You have deployed DNS filtering across the campus network, but monitoring shows that a significant number of student BYOD devices are still loading ads and accessing restricted content. What is the most likely cause, and how should you address it?
Suggerimento: Consider how modern browsers handle DNS queries independently of the operating system's network settings.
Visualizza risposta modello
The most likely cause is that modern browsers on the BYOD devices are using DNS-over-HTTPS (DoH) to bypass the local network's DNS resolver. To address this, configure the perimeter firewall to block known DoH provider IP addresses and drop outbound traffic on port 53 that does not originate from the approved campus DNS resolvers. This forces the devices to fall back to the local, filtered DNS infrastructure.
Q2. The school's leadership team wants to block all social media and advertising networks globally across the entire campus to ensure maximum compliance. As the IT Director, why might you advise against a single global policy, and what architecture would you propose instead?
Suggerimento: Consider the different user groups on campus and their specific needs.
Visualizza risposta modello
A single global policy will inevitably cause operational friction. Staff may need access to social media for communications or marketing, and certain ad networks may be required for legitimate educational tools. Instead, propose a segmented architecture using 802.1X integration to apply identity-aware policies. Create distinct VLANs and policy groups for Students, Staff, and Guests, applying strict blocking to students while allowing necessary access for staff.
Q3. Before switching the new DNS filtering solution into active enforcement mode, what critical operational process must be established with the IT helpdesk?
Suggerimento: Think about the impact of false positives on teaching staff.
Visualizza risposta modello
A rapid-response whitelist request process must be established. Heuristic filtering will inevitably block some legitimate educational resources (false positives). Without a fast, SLA-backed process for teachers to request domains be unblocked, the deployment will disrupt learning and cause stakeholder resistance.