IWF Compliance for Public WiFi Networks in the UK
This authoritative guide details the technical requirements, architecture, and deployment strategies for implementing IWF-compliant public WiFi networks across UK venues. It provides IT leaders with actionable frameworks to mitigate legal risks while maintaining high-performance network access.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: IWF Compliance Architecture
- Layer 1: DNS Filtering
- Layer 2: HTTP/HTTPS Deep Packet Inspection (DPI)
- Integration with Authentication and Analytics
- Implementation Guide: Deploying IWF Filtering
- Best Practices for Public Venues
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
Executive Summary
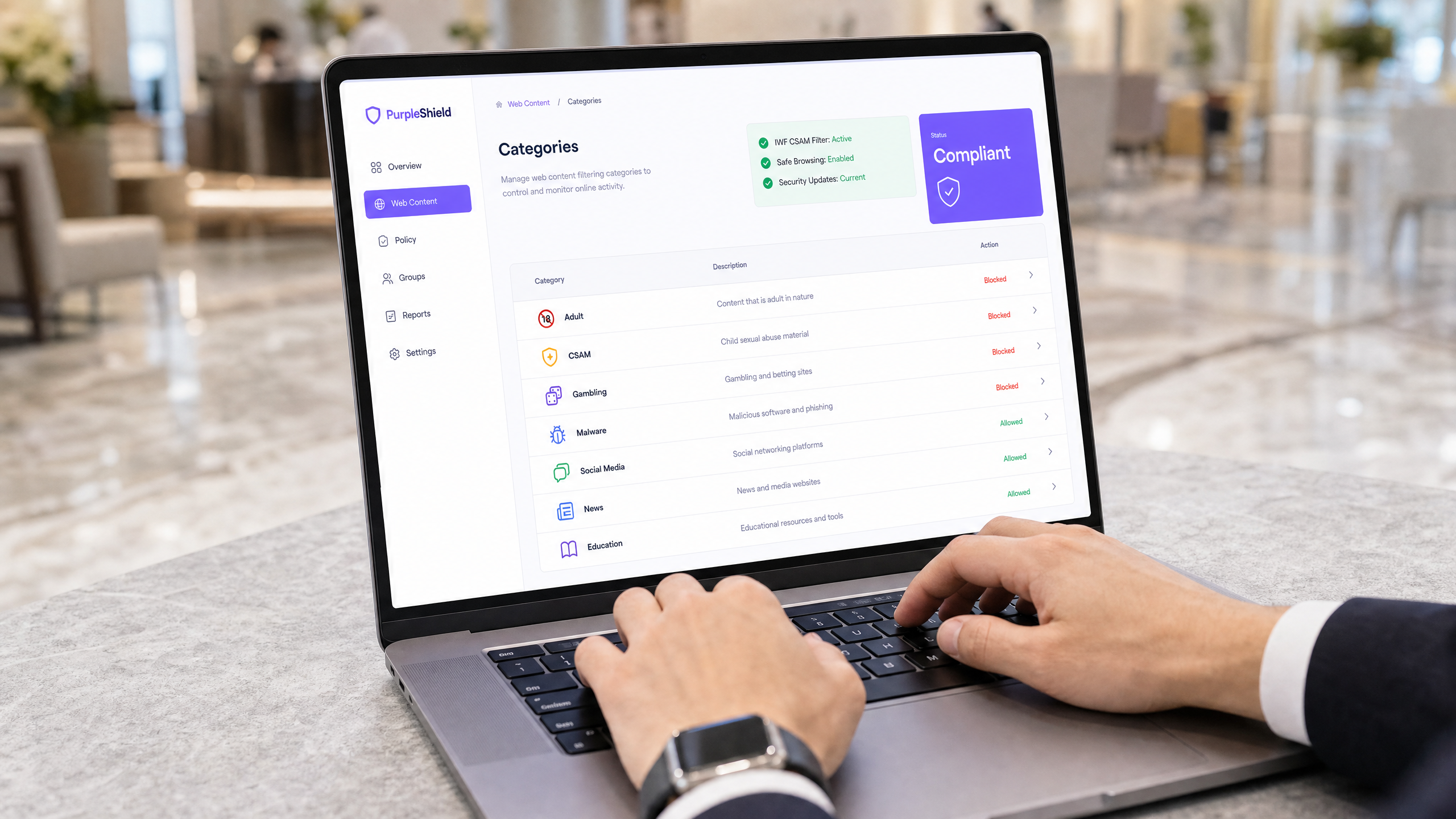
Public WiFi provision in the UK has shifted from a guest amenity to a critical compliance vector. For IT Directors and CTOs managing Retail , Hospitality , and public-sector environments, deploying an open network without robust content filtering exposes the organisation to significant legal and reputational risks. The Internet Watch Foundation (IWF) maintains the definitive blocklist for Child Sexual Abuse Material (CSAM). Integrating this list at the network edge is not merely a best practice; it is a fundamental requirement for responsible venue operation.
This guide outlines the technical architecture required to achieve IWF compliance, detailing deployment strategies at the DNS and HTTP layers. It cuts through the noise to provide actionable, vendor-neutral advice on implementing certified web filtering without degrading network throughput or user experience.
From securing Guest WiFi to integrating with modern authentication standards like IEEE 802.1X and OpenRoaming, we explore how to build a compliant, high-performance network.
Technical Deep-Dive: IWF Compliance Architecture
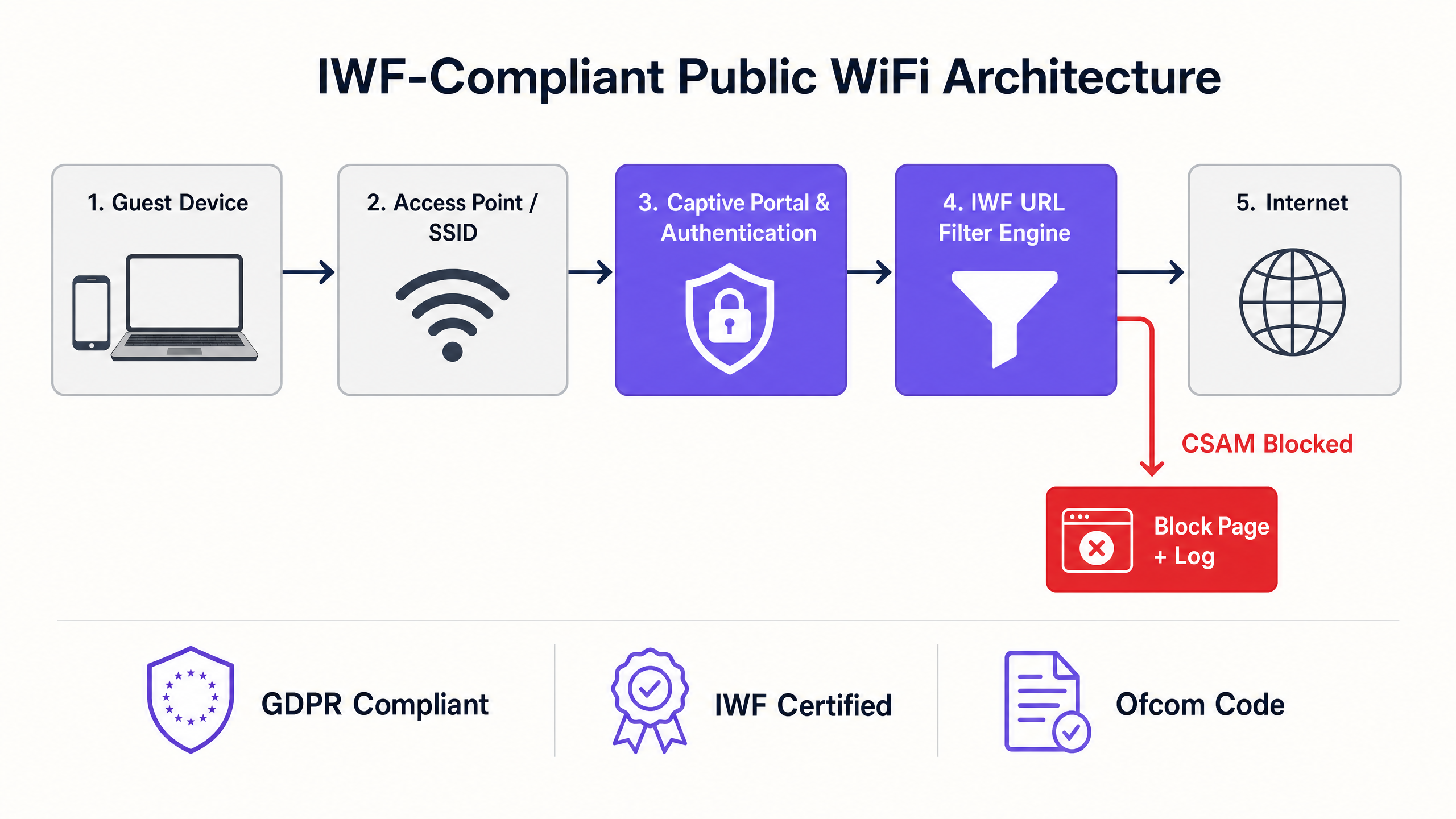
Implementing IWF compliance requires a multi-layered approach to network security. The core requirement is the dynamic integration of the IWF URL list into the venue's web filtering engine. This cannot be a static, manually updated list; it requires real-time or near-real-time synchronisation with the IWF database.
Layer 1: DNS Filtering
At the most fundamental level, DNS filtering intercepts requests to known CSAM domains and resolves them to a block page or a null route. While highly efficient and low-latency, DNS filtering alone is insufficient because it operates at the domain level, whereas the IWF list often specifies exact URLs. Relying solely on DNS can lead to over-blocking (blocking an entire legitimate domain because of one offending URL) or under-blocking (failing to block IP-based access).
Layer 2: HTTP/HTTPS Deep Packet Inspection (DPI)
To accurately enforce the IWF URL list, the filtering engine must inspect the full HTTP request path. For encrypted HTTPS traffic, this presents a challenge. The modern approach involves Server Name Indication (SNI) inspection combined with targeted SSL decryption for specific, high-risk categories. However, deploying SSL decryption on public networks introduces severe privacy and certificate trust issues. Therefore, the standard deployment model for public venues relies on advanced SNI filtering and dynamic IP categorisation, cross-referenced with the IWF URL database.
Integration with Authentication and Analytics
Compliance extends beyond blocking; it requires accountability. Integrating the filtering engine with the captive portal ensures that users accept an Acceptable Use Policy (AUP) before gaining access. Furthermore, tying network access to robust WiFi Analytics allows IT teams to monitor block events, identify potential security incidents, and demonstrate compliance during audits. Understanding Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 is also vital, as different bands require specific QoS configurations to handle the slight latency introduced by deep packet inspection.
Implementation Guide: Deploying IWF Filtering
Deploying IWF-compliant filtering across distributed environments—such as a national Transport hub or a chain of Healthcare facilities—requires a structured approach.
- Select a Certified Vendor: Ensure your web filtering provider is an official IWF member and consumes their dynamic feed. Do not attempt to build a bespoke integration.
- Network Edge Configuration: Configure the venue routers or access points to force all guest DNS traffic to the compliant filtering service. Block outbound port 53 and 853 (DoT) to prevent users from bypassing the filter using custom DNS servers.
- Captive Portal Alignment: Update the captive portal AUP to explicitly state that content filtering is in place and that access to illegal material is monitored and blocked.
- Testing and Validation: Do not use actual IWF URLs for testing. The IWF provides specific, safe test URLs to validate that the filtering engine is correctly intercepting and blocking restricted content.
- Logging and Retention: Configure the firewall or filtering service to retain logs of blocked access attempts for a minimum of 12 months, aligning with GDPR and local law enforcement requirements.

Best Practices for Public Venues
When designing the network architecture, IT leaders must balance security with user experience.
- Avoid Over-Blocking: Ensure the filtering policy is strictly targeted at illegal content (CSAM) and highly malicious categories (malware, phishing). Overly aggressive filtering (e.g., blocking legitimate social media or streaming) leads to user frustration and increased support tickets.
- Handle Encrypted DNS: With the rise of DNS over HTTPS (DoH), users' browsers may attempt to bypass local DNS filters. Implement network policies to block known DoH resolvers (like 8.8.8.8 or 1.1.1.1) at the firewall level, forcing fallback to the venue's secure DNS.
- Seamless Authentication: Consider transitioning from open networks to secure authentication frameworks. While Passpoint/OpenRoaming is the future, ensuring robust filtering on these networks is paramount. For insights on managing complex enterprise setups, refer to Resolving Roaming Issues in Corporate WLANs .
Troubleshooting & Risk Mitigation
The most common failure mode in public WiFi compliance is the "bypass." Users, either intentionally or inadvertently, circumvent the filtering controls.
- Rogue Access Points: Regular sweeps for rogue APs are essential. A compliant wired network is useless if an employee plugs in an unmanaged, unfiltered consumer router.
- VPN Usage: While blocking all VPN traffic is often impractical in venues like hotels where business travellers need corporate access, IT teams must monitor for excessive, continuous encrypted tunnels that may indicate abuse.
- Latency Spikes: If the filtering engine is cloud-based, ensure regional POPs are utilised. Routing traffic from a London hotel to a US-based filtering server will introduce unacceptable latency. Optimise routing to maintain a seamless experience, similar to how one would Office Wi Fi: Optimize Your Modern Office Wi-Fi Network .
ROI & Business Impact
While compliance is often viewed as a cost centre, robust IWF filtering protects the brand. The reputational damage of a venue being associated with illegal downloads or CSAM distribution far outweighs the deployment costs. Furthermore, a secure, compliant network is a prerequisite for leveraging advanced technologies like BLE Low Energy Explained for Enterprise for location-based services, as users must trust the underlying infrastructure before opting into tracking and analytics. Success is measured by zero compliance breaches, minimal false-positive support tickets, and seamless network performance.
Key Definitions
Internet Watch Foundation (IWF)
A UK-based organization that compiles a dynamic list of URLs containing Child Sexual Abuse Material (CSAM).
Integration with the IWF list is the baseline standard for public WiFi compliance in the UK.
Server Name Indication (SNI)
An extension to the TLS protocol that indicates which hostname the client is attempting to connect to at the start of the handshaking process.
SNI inspection allows IT teams to block specific malicious websites on HTTPS connections without needing to decrypt the entire traffic stream.
DNS over HTTPS (DoH)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the DNS queries.
DoH can bypass traditional DNS-based web filters, requiring network administrators to block known DoH endpoints to enforce compliance.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
Crucial for enforcing the Acceptable Use Policy (AUP) and establishing the legal framework for network usage.
Acceptable Use Policy (AUP)
A document stipulating constraints and practices that a user must agree to for access to a corporate network or the internet.
Provides the legal cover for venue operators to block content and terminate sessions for non-compliant users.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks.
Essential for separating untrusted guest traffic (which requires IWF filtering) from trusted corporate or POS traffic.
Deep Packet Inspection (DPI)
A form of computer network packet filtering that examines the data part of a packet as it passes an inspection point.
Used to identify and block specific applications or protocols (like BitTorrent or VPNs) that might be used to bypass standard filters.
False Positive
When a legitimate website is incorrectly categorized and blocked by the filtering engine.
High false-positive rates lead to user complaints and IT support overhead; selecting a highly accurate, IWF-certified vendor minimizes this.
Worked Examples
A 200-room hotel needs to implement IWF filtering but has noticed a high volume of guests using DNS over HTTPS (DoH) via modern browsers, bypassing the current DNS-based filter.
The IT team must implement a dual-layer approach. First, configure the edge firewall to block outbound traffic to known DoH providers (e.g., blocking IPs for Cloudflare, Google, and Quad9 DoH endpoints). Second, utilize SNI (Server Name Indication) inspection on the firewall to intercept the initial TLS handshake and block IWF-listed URLs before the encrypted session is established.
A large retail chain is rolling out free guest WiFi across 500 stores and needs to ensure compliance while minimizing latency at the Point of Sale (POS).
The network architect segments the VLANs. The Guest VLAN is routed through a cloud-based IWF-certified web filter using redundant regional POPs to minimize latency. The POS VLAN is strictly isolated, utilizing an explicit allow-list (whitelisting) for payment gateways and inventory systems, completely bypassing the web filter to ensure zero latency impact on transactions.
Practice Questions
Q1. You are deploying guest WiFi at a major conference centre. The marketing team wants to use a generic, open SSID with no captive portal to reduce 'friction'. How do you respond from a compliance perspective?
Hint: Consider the legal requirement for user consent and accountability.
View model answer
I would advise against an open, frictionless SSID. Without a captive portal, users cannot agree to the Acceptable Use Policy (AUP). This leaves the venue legally exposed if illegal activity occurs on the network. A captive portal is a mandatory control gate for enforcing terms of service and logging MAC addresses against accepted sessions, which is critical for incident response.
Q2. During a network audit, you discover that 15% of guest traffic is successfully bypassing the web filter using custom DNS servers configured on their devices. What is the immediate technical remediation?
Hint: Look at edge firewall port configurations.
View model answer
The immediate remediation is to configure the edge firewall to block outbound traffic on UDP/TCP port 53 and TCP port 853 (DNS over TLS) from the Guest VLAN to any external IP address. All DNS requests must be forced (or transparently proxied) to the venue's secure, IWF-integrated DNS servers.
Q3. A hotel IT manager suggests using full SSL decryption (SSL Inspection/Termination) on the guest network to ensure 100% visibility into HTTPS traffic for IWF compliance. Why is this a flawed approach for public WiFi?
Hint: Consider device trust and user privacy.
View model answer
Full SSL decryption requires installing a custom root certificate on every guest device. In a public WiFi scenario, this is impossible to enforce, will cause severe browser certificate errors for all users, and represents a massive privacy violation. The correct approach is to rely on DNS filtering combined with SNI (Server Name Indication) inspection, which allows categorization of encrypted traffic without breaking the TLS tunnel.