WiFi in Retail Shops: Building Customer Profiles From Footfall Data
This authoritative guide details how enterprise retail IT teams can transform existing WiFi infrastructure into a robust first-party data collection engine. It covers technical architecture, compliance standards, and actionable deployment strategies for building customer profiles from footfall analytics.
🎧 Listen to this Guide
View Transcript

Executive Summary
For modern retail operations, the physical shop environment remains a critical touchpoint, yet it often lacks the granular analytics native to e-commerce. This guide provides a comprehensive technical framework for transforming standard wireless infrastructure into an enterprise-grade analytics engine. By leveraging authenticated Guest WiFi connections, IT leaders and venue operations directors can passively collect high-fidelity first-party data—including visit frequency, dwell time, and path analysis.
Deploying WiFi Analytics shifts the network from a pure cost centre to a strategic business asset. This document details the necessary technical architecture, the shift from passive MAC detection to authenticated sessions, and the critical compliance standards (GDPR, PCI DSS, WPA3) required for secure implementation across Retail and Hospitality environments.
Technical Deep-Dive
The Mechanics of Data Collection
When a customer's device enters a retail space, it broadcasts probe requests containing a Media Access Control (MAC) address. Historically, this allowed for passive tracking. However, modern operating systems enforce MAC address randomisation to protect user privacy. To overcome this limitation and ensure high data fidelity, enterprise deployments must rely on authenticated connections.
When a user connects via a captive portal, the system captures a verified, consented identity. This identity is mapped to a persistent device identifier, forming the foundation of robust customer profiling.
Core Data Streams
- Visit Frequency: By tracking reconnection events, the system builds a longitudinal profile of customer loyalty.
- Dwell Time: Measuring the duration of active sessions provides insights into customer engagement and correlates strongly with conversion probability.
- Path Analysis: Utilising trilateration across multiple access points (APs) enables the mapping of physical customer journeys through the shop.
- Loyalty Segmentation: Aggregating frequency and dwell time allows for automated segmentation (e.g., new visitors vs. loyal advocates).
Enterprise Architecture
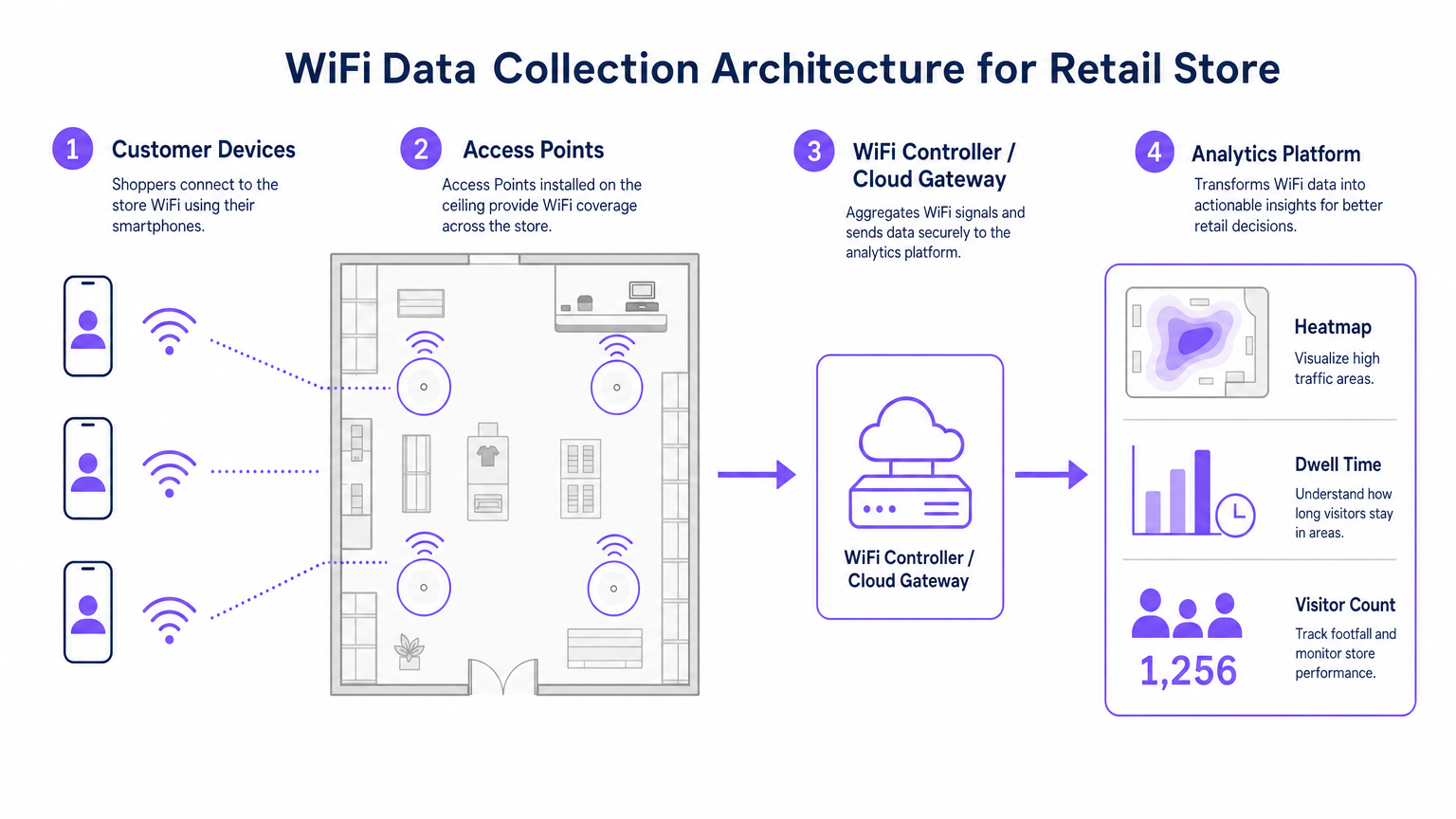
A robust retail WiFi analytics deployment consists of four primary layers:
- Radio Frequency Infrastructure: High-density deployments require 802.11ac Wave 2 or 802.11ax (WiFi 6) access points. The standard recommendation is one AP per 1,500–2,000 square feet, adjusted for high-traffic zones.
- Controller/Cloud Management Plane: Aggregates telemetry from the RF layer and manages client roaming.
- Analytics Platform: Ingests raw network telemetry (association events, signal strength) and transforms it into actionable intelligence.
- Engagement Layer: Integrates via APIs or webhooks with CRM systems to trigger automated marketing workflows based on real-time spatial data.
Listen to our full technical briefing on deploying these architectures:
Implementation Guide
Successful deployment requires alignment between network engineering and business operations.
- Optimise the Authentication Flow: Implement a frictionless captive portal. Minimise input fields to maximise opt-in rates while ensuring clear consent mechanisms are in place. Consider integrating existing loyalty programme credentials.
- Design for Triangulation: Standard coverage designs are insufficient for path analysis. Ensure at least three access points provide overlapping coverage in key tracking zones to enable accurate trilateration.
- Define Key Performance Indicators (KPIs): Establish baseline metrics prior to launch. Common KPIs include average dwell time by zone, new vs. returning visitor ratios, and peak footfall hours.

Best Practices
- Standardise Hardware: Ensure consistent AP hardware across sites to maintain uniform signal telemetry, simplifying data normalisation at the analytics layer.
- Isolate Networks: Strictly segregate guest traffic from corporate and Point-of-Sale (POS) networks using dedicated VLANs and SSIDs to maintain PCI DSS compliance.
- Automate Data Retention: Configure the analytics platform to automatically purge raw session data after a defined period (e.g., 12 months) to minimise compliance risk under GDPR.
For broader implementation context across different sectors, see our guides on Hospitality WiFi Solutions: What to Look for in a Provider and Wi Fi in Auto: The Complete 2026 Enterprise Guide .
Troubleshooting & Risk Mitigation
| Failure Mode | Symptom | Mitigation Strategy |
|---|---|---|
| Poor Triangulation Accuracy | Location data jumps erratically across the floor plan. | Conduct a predictive RF site survey; increase AP density in critical zones; ensure APs are mounted at uniform heights. |
| Low Authentication Rates | High passive footfall but low registered user counts. | Simplify the captive portal UI; offer social login options; ensure the splash page is fully responsive. |
| Data Silos | Analytics data is not reaching the CRM. | Verify API endpoint connectivity; check webhook delivery logs; ensure data payload formats match CRM schema requirements. |
ROI & Business Impact
The transition to an analytics-driven WiFi deployment yields measurable business outcomes. Retailers consistently report:
- Increased Conversion Rates: Correlated directly with targeted engagement strategies based on dwell time.
- Optimised Store Layouts: Data-driven decisions on product placement derived from path analysis.
- Enhanced Customer Retention: Automated re-engagement campaigns triggered by lapsed visitor thresholds.
By bridging the gap between physical operations and digital intelligence, enterprise WiFi analytics provides a definitive competitive advantage in the modern retail landscape.
Key Terms & Definitions
MAC Address Randomisation
A privacy feature in modern operating systems that broadcasts a fake MAC address during network probing, preventing passive tracking.
Forces IT teams to rely on authenticated connections rather than passive listening for accurate footfall analytics.
Trilateration
The process of determining absolute or relative locations of points by measurement of distances, using the geometry of circles, spheres or triangles.
Used by the analytics platform to calculate a device's physical location based on signal strength received by multiple APs.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary mechanism for capturing user consent and identity to build first-party data profiles.
Dwell Time
The total duration a customer's device remains continuously associated with the WiFi network during a single visit.
A critical metric for marketing teams to gauge customer engagement and intent.
802.11ax (WiFi 6)
The latest standard for wireless networks, offering higher throughput, better performance in dense environments, and improved power efficiency.
The recommended hardware standard for enterprise retail environments requiring high-density analytics.
PCI DSS
Payment Card Industry Data Security Standard; a set of security standards designed to ensure that all companies that accept, process, store or transmit credit card information maintain a secure environment.
Mandates strict network segregation between guest WiFi and point-of-sale systems.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
Used to securely isolate guest WiFi traffic from internal corporate networks.
First-Party Data
Information a company collects directly from its customers and owns entirely.
The ultimate output of a successful retail WiFi analytics deployment, highly valuable for targeted marketing.
Case Studies
A 50-store retail chain needs to implement footfall tracking to optimize staffing, but their current network only provides passive MAC detection, resulting in highly inaccurate data due to MAC randomization.
Deploy a captive portal authentication system integrated with the existing WiFi controllers. Configure the portal to require a simple email or social login in exchange for free WiFi access. Map the authenticated identity to the device's persistent identifier, bypassing the randomized MAC issue. Integrate this data feed via API into the central workforce management system to align staffing levels with verified peak footfall hours.
A large conference centre wants to track attendee flow between different exhibition halls to justify premium pricing for certain vendor booths.
Redesign the RF layout specifically for location analytics rather than just coverage. Deploy additional 802.11ax access points to ensure at least three APs overlap in key transition corridors, enabling accurate trilateration. Feed the signal strength telemetry into the analytics platform to generate real-time heatmaps and path analysis reports for the events team.
Scenario Analysis
Q1. Your marketing team wants to implement path analysis to track customer movement around a new product display. The store currently has two access points providing adequate signal coverage for connectivity. What is the necessary technical recommendation?
💡 Hint:Consider the requirements for spatial calculation.
Show Recommended Approach
You must advise the marketing team that path analysis requires trilateration. Therefore, you need to deploy at least one additional access point to ensure the target area is covered by overlapping signals from a minimum of three APs.
Q2. During a security audit, it is discovered that the guest WiFi network and the POS terminals are operating on the same physical switch without logical separation. What is the immediate compliance risk and remediation?
💡 Hint:Think about payment security standards.
Show Recommended Approach
This configuration violates PCI DSS requirements. The immediate remediation is to configure separate VLANs on the switch to logically isolate the guest traffic from the POS network, ensuring no lateral movement is possible.
Q3. The operations director notes that while the system reports 1,000 visitors per day based on passive MAC detection, the authenticated user count is only 150. How do you explain this discrepancy?
💡 Hint:Consider modern mobile OS features.
Show Recommended Approach
Explain that modern smartphones use MAC address randomisation when probing for networks, which artificially inflates passive counts as a single device may broadcast multiple fake MACs. The authenticated count of 150 represents the true, high-fidelity data of users who actively engaged with the captive portal.



