Automatizando a Revogação de Certificados com OCSP e CRL em um Ambiente NAC
Este guia de referência técnica oferece a gerentes de TI e arquitetos de rede uma análise abrangente da automação da revogação de certificados em um ambiente de Network Access Control (NAC). Ele explora as compensações arquitetônicas entre OCSP e CRL, oferece orientação de implementação neutra em relação ao fornecedor e descreve o impacto nos negócios da aplicação de políticas em tempo real.
Listen to this guide
View podcast transcript
- Resumo Executivo
- Análise Técnica Detalhada
- Arquitetura da Lista de Revogação de Certificados (CRL)
- Arquitetura do Online Certificate Status Protocol (OCSP)
- Integração com Plataformas de Convidados e Análise
- Guia de Implementação
- Passo 1: Definir o Gatilho de Revogação
- Etapa 2: Configurar a Infraestrutura de Revogação
- Etapa 3: Estabelecer a Política de Fallback
- Etapa 4: Definir o Comportamento em Caso de Falha
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios

Resumo Executivo
Para diretores de TI corporativos e arquitetos de rede que gerenciam ambientes de alta densidade — como locais de Hospitalidade , propriedades de Varejo e implantações no setor público — o gerenciamento do ciclo de vida dos certificados é uma fronteira de segurança crítica. Embora o IEEE 802.1X forneça autenticação robusta para dispositivos corporativos e BYOD, o mecanismo pelo qual a confiança é revogada é frequentemente negligenciado até que uma violação ocorra.
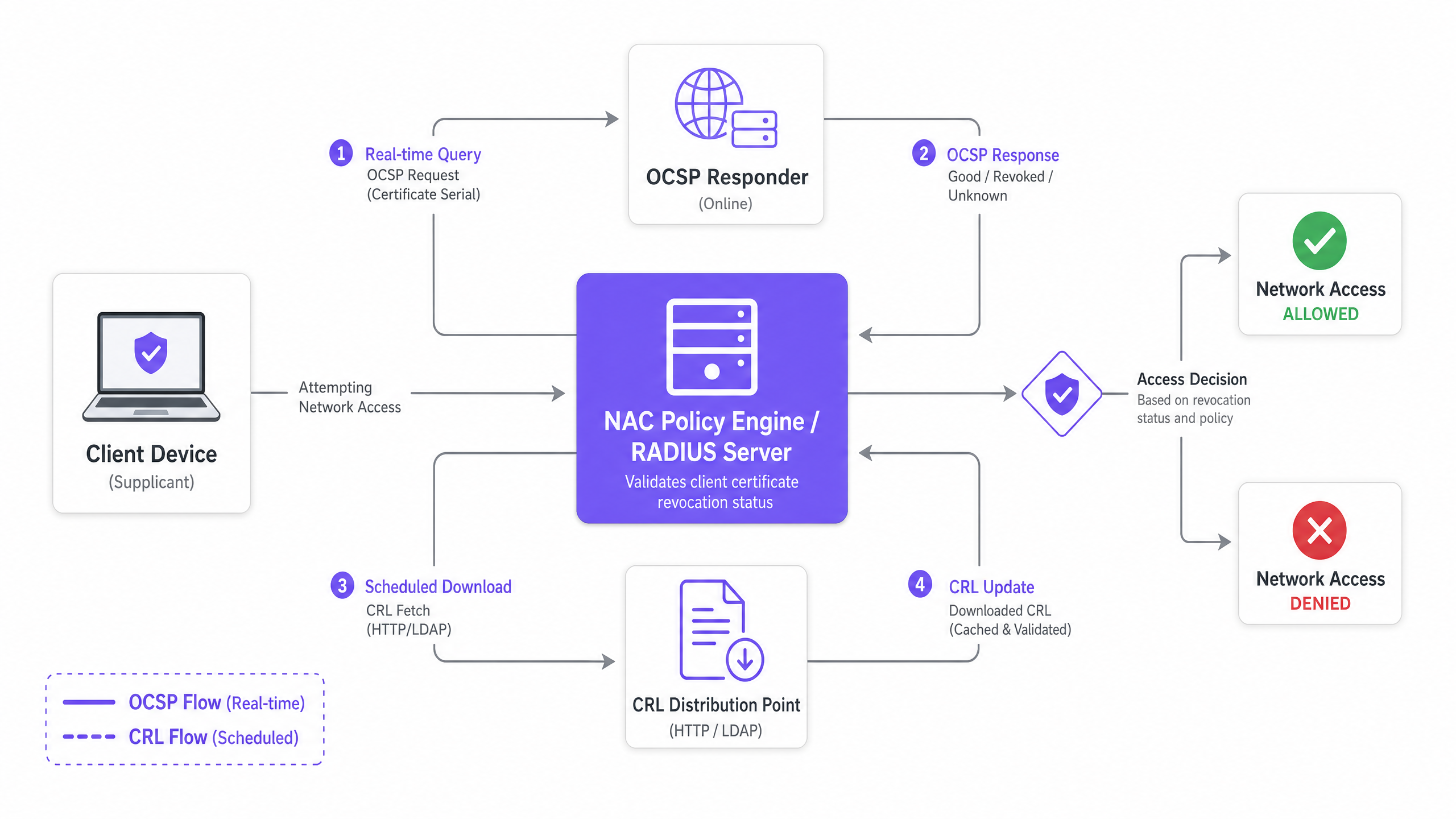
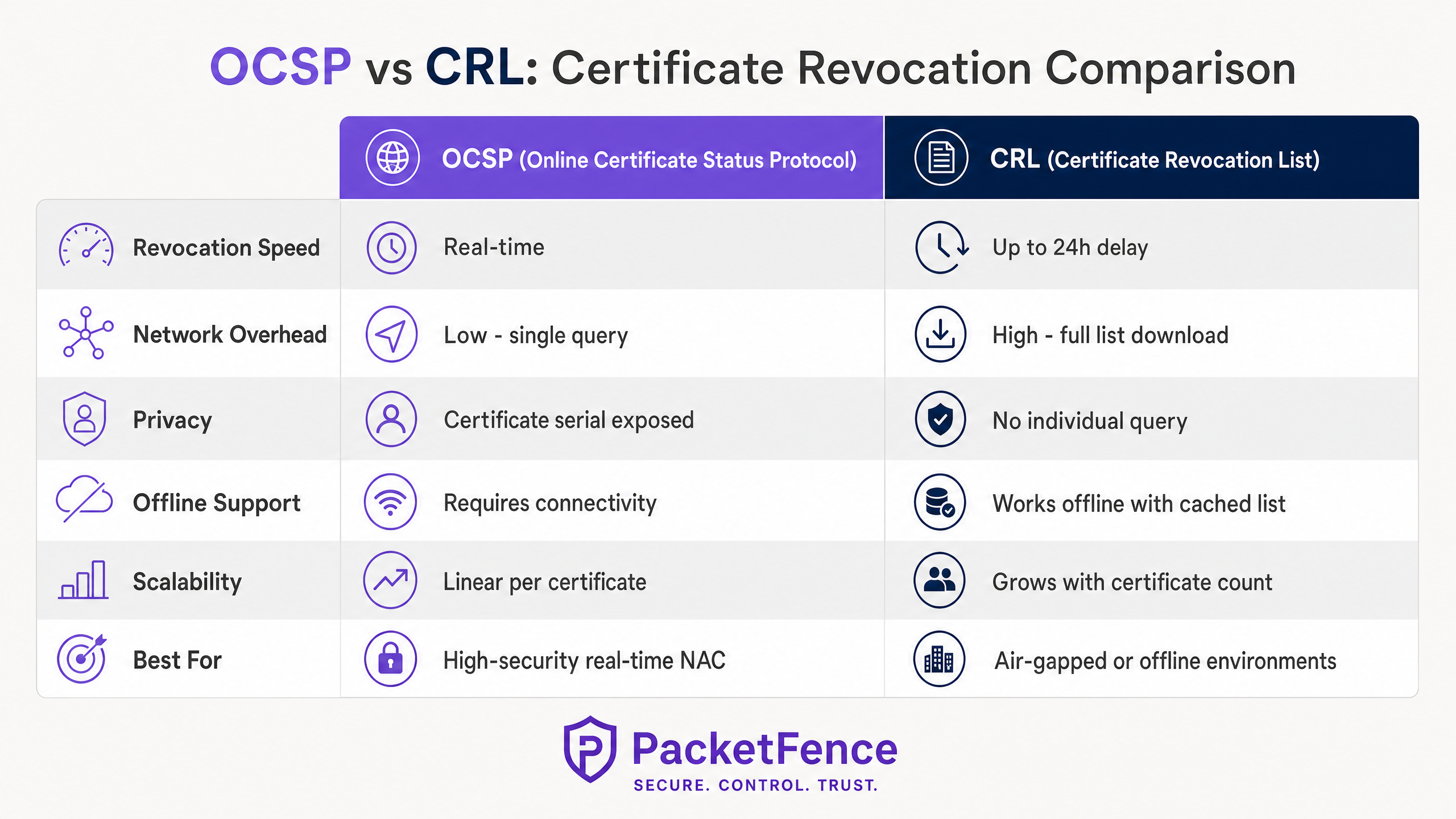
Automatizar a revogação de certificados com o Online Certificate Status Protocol (OCSP) e as Certificate Revocation Lists (CRL) dentro de um ambiente de Network Access Control (NAC) preenche a lacuna entre a desativação de endpoints e a aplicação de políticas de rede. Este guia explora a mecânica arquitetônica da revogação automatizada, comparando as capacidades em tempo real do OCSP com a resiliência offline do CRL.
Ao integrar sua plataforma de Mobile Device Management (MDM), Certificate Authority (CA) e motor de política NAC, as organizações podem alcançar acesso à rede de confiança zero, onde dispositivos comprometidos ou desativados são instantaneamente impedidos de entrar. Esta referência técnica fornece orientação de implantação acionável, estratégias de mitigação de riscos e explora como essa postura de segurança voltada para a equipe complementa a infraestrutura voltada para o público, como as plataformas Guest WiFi e WiFi Analytics da Purple.
Análise Técnica Detalhada
Em qualquer rede corporativa que utiliza IEEE 802.1X com EAP-TLS, os dispositivos autenticam usando certificados digitais em vez de credenciais compartilhadas. Essa abordagem é fundamental para as arquiteturas de segurança modernas, fornecendo identidade vinculada ao dispositivo que se integra perfeitamente com plataformas MDM via protocolos como SCEP (para leitura adicional, consulte O Papel do SCEP e NAC na Infraestrutura MDM Moderna ). No entanto, os certificados têm um ciclo de vida definido. Quando um dispositivo é perdido, um usuário é desligado ou uma chave privada é comprometida, a infraestrutura de rede deve ser explicitamente instruída a parar de confiar nesse certificado.
Esta instrução de revogação é entregue por meio de dois mecanismos principais: CRL e OCSP.
Arquitetura da Lista de Revogação de Certificados (CRL)
Uma CRL é um arquivo assinado digitalmente publicado pela Certificate Authority contendo os números de série de todos os certificados revogados que ainda não expiraram. O motor de política NAC (atuando como servidor RADIUS) baixa periodicamente esta lista de um CRL Distribution Point (CDP) via HTTP ou LDAP.
Durante o handshake EAP-TLS, o servidor RADIUS verifica o número de série do certificado do cliente recebido em relação à sua CRL armazenada em cache localmente. Se o número de série estiver presente, a autenticação é rejeitada.
Características Arquitetônicas:
- Resiliência Offline: Como o servidor RADIUS armazena em cache a CRL, a verificação de revogação continua mesmo que a CA ou o CDP se tornem inalcançáveis.
- Latência: A principal desvantagem é a latência entre a revogação e a aplicação. Se um certificado for revogado às 09:00 e o intervalo de atualização da CRL for de 24 horas, o dispositivo comprometido mantém o acesso à rede até o próximo download.
- Sobrecarga de Throughput: Em ambientes com dezenas de milhares de certificados, os arquivos CRL podem crescer para vários megabytes, criando tensão na largura de banda durante os ciclos de atualização.
Arquitetura do Online Certificate Status Protocol (OCSP)
OCSP aborda as limitações de latência da CRL, permitindo a verificação de revogação em tempo real. Em vez de baixar uma lista completa, o servidor RADIUS envia uma consulta direcionada contendo o número de série do certificado para um OCSP Responder. O respondedor retorna um status assinado: Bom, Revogado ou Desconhecido.
Características Arquitetônicas:
- Aplicação em Tempo Real: As decisões de revogação se propagam instantaneamente. Assim que a CA atualiza o OCSP Responder, a próxima tentativa de autenticação pelo dispositivo comprometido falhará.
- Dependência de Disponibilidade: O motor de política NAC depende da alta disponibilidade do OCSP Responder. Se o respondedor estiver inalcançável, o administrador de rede deve definir uma política de falha: "fail open" (permitir acesso, comprometendo a segurança) ou "fail closed" (negar acesso, comprometendo a disponibilidade).
- OCSP Stapling: Para mitigar a carga e as preocupações com a privacidade, o OCSP Stapling permite que o dispositivo cliente obtenha a resposta OCSP assinada e a anexe ao handshake TLS, embora o suporte do suplicante varie.
Integração com Plataformas de Convidados e Análise
Enquanto OCSP e CRL lidam com os rigorosos requisitos de segurança de funcionários e dispositivos corporativos, as redes voltadas para o público exigem arquiteturas diferentes. Para locais públicos, integrar um NAC robusto para funcionários com uma plataforma pública dedicada como a Purple garante cobertura abrangente. A plataforma da Purple lida com a autenticação de captive portal, aceitação de termos de serviço e captura de dados para o segmento público, enquanto a infraestrutura de rede subjacente (muitas vezes os mesmos pontos de acesso físicos e switches) aplica 802.1X e OCSP para SSIDs corporativos. Compreender o ambiente de rádio é crucial para ambos os segmentos; consulte Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 para planejamento de espectro.
Guia de Implementação
A implantação da revogação automatizada de certificados requer coordenação entre os domínios PKI, MDM e NAC. Siga estas etapas de implementação neutras em relação ao fornecedor para estabelecer um pipeline de revogação resiliente.
Passo 1: Definir o Gatilho de Revogação
A automação começa na camada de gerenciamento de endpoints. Configure sua plataforma MDM (por exemplo, Microsoft Intune, Jamf Pro) para acionar uma chamada de API de revogação para sua Autoridade Certificadora quando condições específicas forem atendidas:
- Dispositivo desmatriculado do MDM
- Dispositivo marcado como não-compatível
- Conta de usuário desativada no serviço de diretório
Etapa 2: Configurar a Infraestrutura de Revogação
Para Implantações de CRL:
- Configure a CA para publicar a CRL em um CDP de alta disponibilidade (por exemplo, um servidor web interno com balanceamento de carga).
- Defina o intervalo de publicação da CRL com base na sua tolerância a riscos (por exemplo, a cada 4 horas).
- Configure o servidor RADIUS para buscar a CRL em um intervalo ligeiramente menor que o intervalo de publicação para garantir que o cache esteja sempre atualizado.
Para Implantações de OCSP:
- Implante pelo menos dois OCSP Responders atrás de um balanceador de carga para garantir alta disponibilidade.
- Configure a CA para enviar atualizações de revogação para os OCSP Responders imediatamente.
- Configure o servidor RADIUS para consultar o IP virtual do OCSP com balanceamento de carga durante a autenticação EAP-TLS.
Etapa 3: Estabelecer a Política de Fallback
Não dependa de um único mecanismo. Configure seu servidor RADIUS para usar OCSP como a verificação de revogação primária, com um fallback para uma CRL armazenada em cache localmente se o OCSP Responder estiver inacessível. Isso fornece aplicação em tempo real em condições normais e resiliência offline durante interrupções de infraestrutura.
Etapa 4: Definir o Comportamento em Caso de Falha
Se tanto o OCSP quanto a CRL em cache estiverem indisponíveis, o servidor RADIUS deve decidir como lidar com a solicitação de autenticação.
- Ambientes de Alta Segurança (por exemplo, Saúde ): Configure "fail closed". Negue o acesso para evitar que dispositivos potencialmente comprometidos se conectem.
- Ambientes Padrão (por exemplo, hubs de Transporte ): Configure "fail open" com alerta. Permita o acesso para manter a continuidade operacional, mas gere um alerta de alta prioridade para o SOC.
Melhores Práticas
- Implemente CRLs Delta: Se depender de CRLs em um ambiente grande, implemente CRLs Delta. Esses arquivos contêm apenas as alterações de revogação desde a publicação da última CRL Base completa, reduzindo significativamente o tamanho do download e o consumo de largura de banda.
- Monitore a Latência do OCSP: As consultas OCSP ocorrem em linha durante o handshake EAP-TLS. Se o OCSP Responder demorar 500ms para responder, a autenticação é atrasada em 500ms. Monitore a latência do respondedor e escale horizontalmente se os tempos de resposta se degradarem.
- Certificados de Curta Duração: Considere reduzir os períodos de validade dos certificados (por exemplo, de 1 ano para 7 dias) por meio da renovação automatizada SCEP/EST. Certificados de curta duração expiram naturalmente rápido, reduzindo a dependência de uma infraestrutura de revogação robusta.
- Alinhe com a Estratégia de Rede Mais Ampla: Garanta que sua implantação NAC esteja alinhada com sua arquitetura de rede de longa distância. Para insights sobre design WAN moderno, consulte SD WAN vs MPLS: The 2026 Enterprise Network Guide .
Solução de Problemas e Mitigação de Riscos
O modo de falha mais comum na revogação automatizada é um pipeline CA-para-NAC quebrado, resultando em um evento de "fail closed" que bloqueia usuários legítimos.
Risco: Interrupção do OCSP Responder Mitigação: Implante respondedores em um cluster ativo-ativo em múltiplos domínios de falha. Implemente verificações de saúde abrangentes no balanceador de carga que verifiquem a capacidade do respondedor de consultar o banco de dados da CA, não apenas a disponibilidade da porta TCP 80.
Risco: Cache de CRL Desatualizado Mitigação: Servidores RADIUS podem falhar ao baixar a CRL mais recente devido a partições de rede ou interrupções de CDP. Implemente monitoramento que alerte se a CRL armazenada em cache localmente for mais antiga que o intervalo de publicação definido.
Risco: Revogação de MDM Incompleta Mitigação: Se o MDM falhar ao acionar a chamada de revogação para a CA, o certificado permanece válido. Implemente um script de reconciliação que compare periodicamente a lista de dispositivos ativos do MDM com a lista de certificados válidos da CA, revogando automaticamente quaisquer discrepâncias.
ROI e Impacto nos Negócios
A automação da revogação de certificados transforma a segurança de um processo reativo e manual em um mecanismo de defesa proativo e automatizado.
- Redução de Riscos: Ao eliminar a janela de exposição entre o comprometimento do dispositivo e o isolamento da rede, as organizações reduzem significativamente o risco de movimento lateral e exfiltração de dados. Isso é crucial para manter a conformidade com frameworks como PCI DSS e GDPR.
- Eficiência Operacional: A automação do pipeline de revogação elimina a necessidade de a equipe de suporte técnico atualizar manualmente as configurações do RADIUS ou os bancos de dados da CA quando um funcionário sai, economizando centenas de horas anualmente em grandes empresas.
- Estratégia de Acesso Unificado: Um ambiente NAC robusto para dispositivos corporativos permite que as equipes de TI implantem com confiança serviços paralelos, como o WiFi de convidado baseado em análise da Purple ou serviços baseados em localização (consulte BLE Low Energy Explained for Enterprise ), sabendo que a infraestrutura central é segura.
Ouça nosso briefing técnico sobre este tópico abaixo:
Key Definitions
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
The most secure standard for 802.1X network authentication, requiring both the client and the server to present digital certificates to prove their identity.
IT teams deploy EAP-TLS to eliminate the risks associated with password-based authentication, ensuring only managed, certificate-bearing devices can connect to the corporate network.
OCSP (Online Certificate Status Protocol)
An internet protocol used for obtaining the revocation status of an X.509 digital certificate in real-time.
Crucial for environments requiring immediate enforcement of access policies, such as when an employee is terminated and their device must be instantly disconnected.
CRL (Certificate Revocation List)
A periodically published, digitally signed list of certificate serial numbers that have been revoked by the issuing Certificate Authority.
Used as a primary revocation mechanism in offline or air-gapped networks, or as a highly resilient fallback mechanism for OCSP.
OCSP Stapling
A mechanism where the client device fetches its own OCSP response and 'staples' it to the TLS handshake, presenting it to the RADIUS server.
Reduces the load on the RADIUS server and OCSP Responder, and improves privacy by preventing the CA from seeing exactly when and where a device is authenticating.
Delta CRL
A smaller revocation list containing only the certificates revoked since the last full Base CRL was published.
Essential for large deployments to prevent network congestion, as full CRLs can become massive and consume significant bandwidth during refresh cycles.
CDP (CRL Distribution Point)
The location, typically an HTTP or LDAP URL, where the Certificate Authority publishes the CRL for clients and RADIUS servers to download.
IT teams must ensure the CDP is highly available and reachable from all NAC policy engines; if the CDP goes down, the RADIUS servers cannot update their caches.
Fail Open / Fail Closed
The policy decision dictating what happens when the revocation infrastructure (OCSP or CDP) is unreachable. Fail Open allows access; Fail Closed denies access.
A critical business decision balancing security posture against operational uptime. Requires sign-off from both IT operations and the CISO.
SCEP (Simple Certificate Enrollment Protocol)
A protocol used by MDM platforms to automate the issuance of digital certificates to managed devices without user intervention.
The starting point of the automated lifecycle. SCEP issues the certificate, and the MDM later triggers the CA to revoke it when the device is retired.
Worked Examples
A 500-bed hospital network is migrating from credential-based 802.1X to certificate-based EAP-TLS for all medical IoT devices and staff laptops. The CISO mandates that if a device is reported stolen, its network access must be terminated within 5 minutes. The network team is concerned about the RADIUS server load if it has to constantly query external services. How should the revocation architecture be designed?
The hospital must deploy OCSP to meet the 5-minute revocation SLA, as CRL refresh intervals cannot reliably meet this target without causing severe network overhead. To address the network team's load concerns, the architecture should implement OCSP Responders locally within the hospital's data centre, positioned close to the RADIUS servers to minimise latency. The RADIUS servers should be configured to query the local OCSP VIP. To ensure resilience, the RADIUS servers must be configured with a fallback to a locally cached CRL, updated hourly. The failure policy must be set to 'fail closed' due to the healthcare environment's strict compliance requirements.
A global retail chain with 1,200 stores uses SCEP to provision certificates to point-of-sale (POS) tablets. The stores have limited WAN bandwidth. The IT director wants to implement certificate revocation but is concerned that downloading large CRL files across 1,200 branch RADIUS servers will saturate the WAN links. What is the optimal deployment strategy?
The retail chain should implement a hybrid approach utilising Delta CRLs and OCSP Stapling. First, the CA should be configured to publish a Base CRL weekly and a Delta CRL (containing only recent revocations) every 4 hours. The branch RADIUS servers will only download the small Delta CRLs during the day, minimising WAN impact. Alternatively, if the POS tablets' EAP supplicants support it, OCSP Stapling should be enabled. This shifts the burden of fetching the OCSP response from the branch RADIUS server to the tablet itself, which can fetch the response directly from the central CA over standard HTTPS, bypassing the RADIUS server's processing overhead entirely.
Practice Questions
Q1. Your organisation is deploying 802.1X across 50 remote branch offices. The WAN links to the central data centre are highly congested and frequently drop packets. You need to implement certificate revocation for the branch corporate laptops. Which architecture should you choose?
Hint: Consider the impact of packet loss on real-time protocols versus the resilience of cached data.
View model answer
You should implement a CRL-based architecture, specifically using Base and Delta CRLs. Because the WAN links are congested and unreliable, real-time OCSP queries will frequently time out, causing authentication delays or failures. By configuring the branch RADIUS servers to download and cache Delta CRLs during off-peak hours, the local RADIUS server can perform revocation checks instantly against its cache, even if the WAN link drops entirely during the authentication attempt.
Q2. A security audit reveals that when your primary OCSP Responder goes offline for maintenance, all corporate users are completely locked out of the WiFi network. The business demands that maintenance should not impact user connectivity, but the CISO refuses to change the policy to 'Fail Open'. How do you resolve this?
Hint: If you cannot change the failure policy, you must change the availability of the service.
View model answer
You must implement high availability for the OCSP service. Deploy at least one additional OCSP Responder and place both behind a load balancer. Configure the RADIUS server to query the load balancer's Virtual IP (VIP). During maintenance, you can drain connections from the primary responder, take it offline, and the load balancer will seamlessly route all OCSP queries to the secondary responder, satisfying both the business uptime requirement and the CISO's 'Fail Closed' mandate.
Q3. You have configured your MDM to automatically revoke certificates when a device is marked as 'lost'. You test the system by marking a test iPad as lost. The MDM confirms the revocation, but 10 minutes later, the iPad successfully connects to the corporate WiFi. The RADIUS server is configured to use a CRL published every 24 hours. What is the root cause and how do you fix it?
Hint: Trace the timeline of the revocation data from the CA to the RADIUS server's enforcement engine.
View model answer
The root cause is latency in the CRL publication and refresh cycle. While the MDM successfully told the CA to revoke the certificate, the CA will not publish that updated status to the CRL Distribution Point until the next 24-hour cycle, and the RADIUS server will not download it until its own cache expires. To fix this, you must either migrate to OCSP for real-time checking, or drastically reduce the CRL publication and download intervals (e.g., to 1 hour) to meet your required enforcement timeline.