Como a Filtragem DNS Reduz o Consumo de Largura de Banda da Rede
Este guia detalha como a implementação de filtragem DNS em redes WiFi corporativas bloqueia tráfego de publicidade, rastreamento e telemetria antes que ele consuma largura de banda. Para gerentes de TI e operadores de locais, isso se traduz em reduções imediatas nos custos de ISP, melhor desempenho da rede e postura de segurança aprimorada.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Aprofundada
- A Mecânica da Resolução DNS e o Desperdício de Largura de Banda
- Como a Filtragem DNS Recupera Largura de Banda
- Arquiteturas de Implantação
- Guia de Implementação
- Passo 1: Estabelecer uma Linha de Base
- Passo 2: Definir Políticas de Filtragem por Segmento de Rede
- Passo 3: Selecione e Teste as Blocklists
- Passo 4: Abordar DNS sobre HTTPS (DoH)
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- Modos de Falha Comuns
- ROI e Impacto nos Negócios

Resumo Executivo
Para gerentes de TI corporativos e arquitetos de rede que supervisionam ambientes de alta densidade — como Hospitalidade , Varejo , Transporte e locais de grande escala — o gerenciamento de largura de banda é um desafio operacional persistente. Apesar das atualizações contínuas nas conexões de ISP e na densidade de pontos de acesso, uma porcentagem significativa da taxa de transferência disponível é frequentemente consumida por tráfego não iniciado pelo usuário. Redes de publicidade, beacons de telemetria, pixels de rastreamento e atualizações de SO em segundo plano degradam silenciosamente o desempenho da rede e inflacionam artificialmente os custos de infraestrutura.
Este guia de referência técnica detalha como a implementação da filtragem DNS na borda da rede aborda diretamente essa ineficiência. Ao interceptar e bloquear solicitações de resolução para domínios conhecidos de publicidade, rastreamento e maliciosos, os operadores de rede podem evitar o estabelecimento de conexões TCP desnecessárias. Essa abordagem reduz o consumo de largura de banda da rede em até 35% em ambientes densos, melhorando a experiência do usuário final e mitigando riscos de segurança. Exploraremos a arquitetura técnica, os modelos de implantação e o ROI mensurável da filtragem DNS, fornecendo orientação acionável para profissionais de TI seniores.
Análise Técnica Aprofundada
A Mecânica da Resolução DNS e o Desperdício de Largura de Banda
O Sistema de Nomes de Domínio (DNS) opera como a camada de roteamento fundamental para todo o tráfego da internet. Quando um dispositivo cliente se conecta a uma rede Guest WiFi , a primeira ação que ele realiza antes de estabelecer qualquer conexão HTTP/HTTPS é uma consulta DNS para resolver um nome de host para um endereço IP.
Em aplicações web e móveis modernas, uma única ação do usuário (por exemplo, carregar um site de notícias ou abrir um aplicativo de mídia social) aciona uma cascata de consultas DNS secundárias e terciárias. Essas consultas são direcionadas a servidores de anúncios, plataformas de análise e endpoints de telemetria.
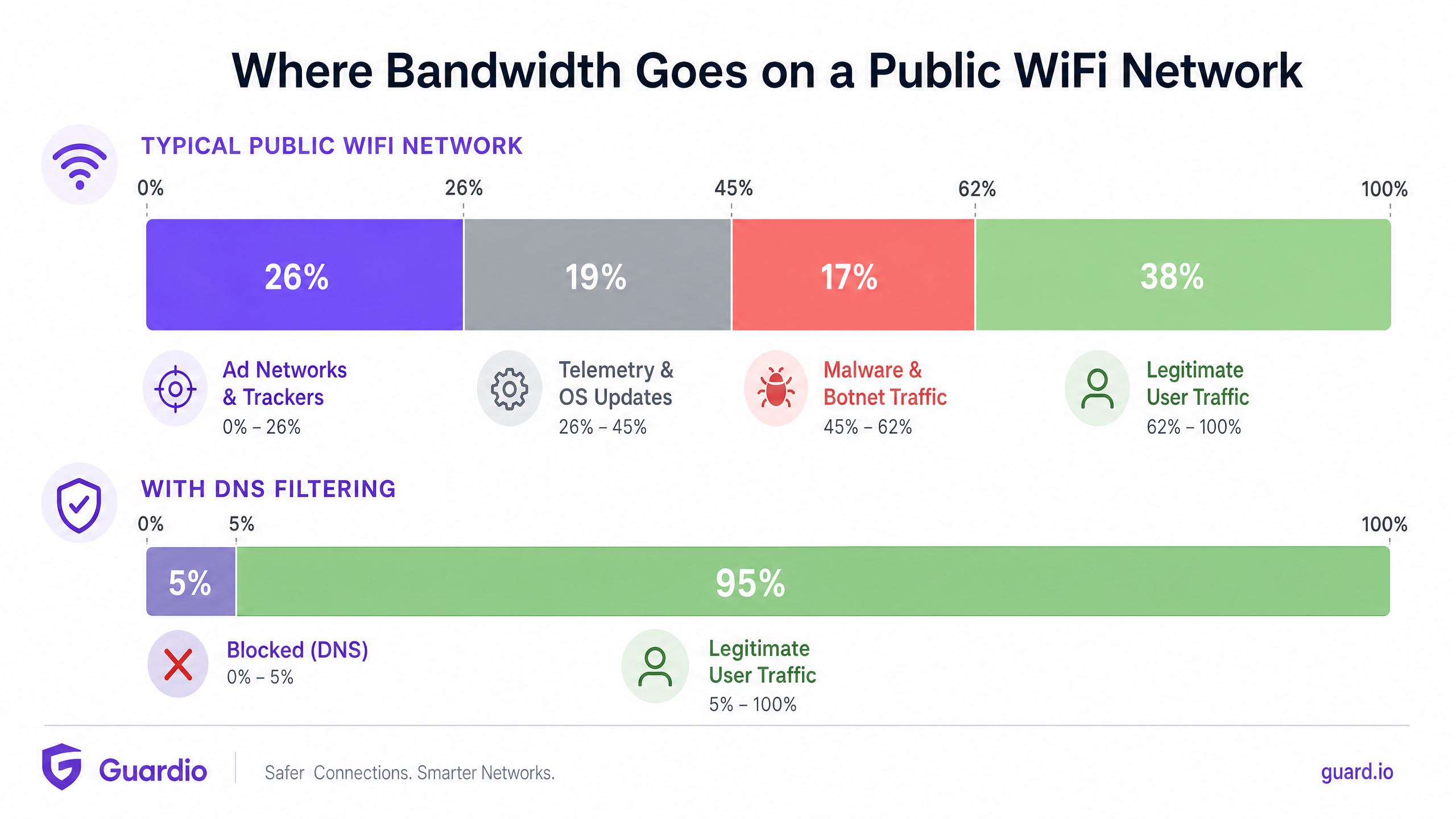
Quando essas consultas são resolvidas com sucesso, o dispositivo estabelece uma conexão e baixa o payload — frequentemente arquivos de mídia pesados para anúncios ou fluxos de dados contínuos para telemetria. Esse tráfego consome largura de banda valiosa, tempo de rádio no Ponto de Acesso (AP) e limites de conexão simultânea no roteador gateway.
Como a Filtragem DNS Recupera Largura de Banda
A filtragem DNS intercepta esse processo na fase de resolução. Quando um dispositivo consulta um domínio, o resolvedor DNS verifica o nome do host em uma lista de bloqueio mantida (ou feed de inteligência de ameaças). Se o domínio for sinalizado como uma rede de anúncios, rastreador ou entidade maliciosa conhecida, o resolvedor retorna uma resposta nula (por exemplo, 0.0.0.0 ou NXDOMAIN) em vez do endereço IP real.
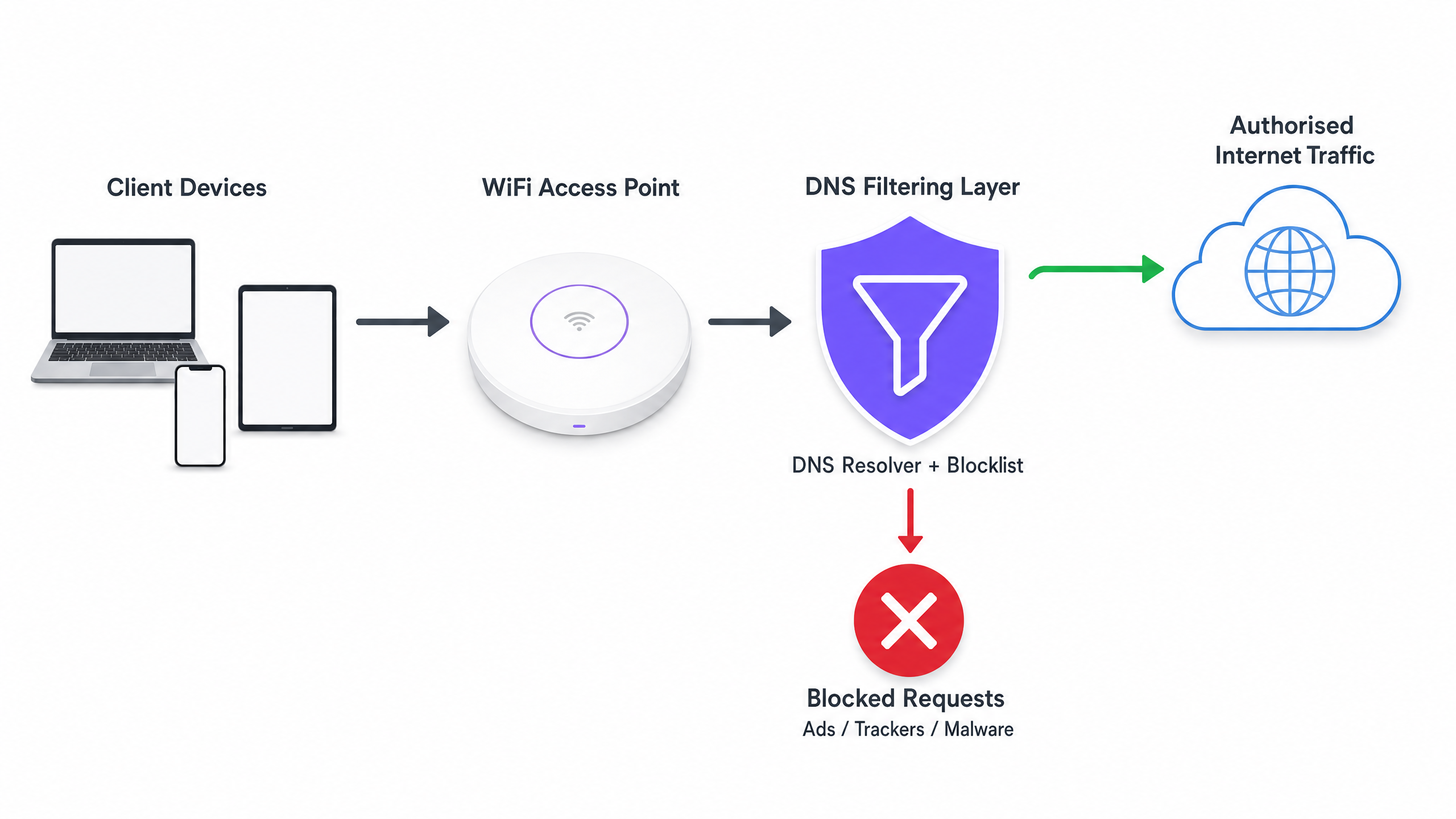
O ganho crítico de eficiência aqui é que a transação é encerrada antes que um handshake TCP possa ocorrer. Nenhuma negociação TLS acontece, e nenhum payload é baixado. A largura de banda que teria sido consumida pelo anúncio ou script de rastreamento é totalmente preservada.
Arquiteturas de Implantação
Existem três modelos arquitetônicos primários para implantar a filtragem DNS em um ambiente corporativo:
- Resolvedores Baseados em Nuvem: O servidor DHCP local é configurado para atribuir os endereços IP de um serviço de filtragem DNS baseado em nuvem (por exemplo, Cisco Umbrella, Cloudflare Gateway) aos dispositivos clientes. Esta é a implantação de menor atrito, não exigindo alterações de hardware no local. No entanto, depende inteiramente da latência do provedor de nuvem.
- Dispositivos On-Premises: Um resolvedor DNS dedicado (dispositivo físico ou virtual) é implantado dentro da infraestrutura de rede local. Isso proporciona a menor latência para a resolução DNS e garante que todos os logs de consulta DNS permaneçam no local, o que pode simplificar a conformidade com as regulamentações de soberania de dados.
- Plataformas Integradas de Gerenciamento WiFi: O modelo mais eficiente para operadores de múltiplos locais é integrar a filtragem DNS diretamente na camada de gerenciamento de rede ou captive portal. Plataformas que oferecem WiFi Analytics abrangente frequentemente incluem filtragem DNS baseada em políticas que pode ser aplicada por SSID, por local ou por grupo de usuários.
Guia de Implementação
A implantação da filtragem DNS requer uma abordagem estruturada para evitar a interrupção do tráfego legítimo do usuário ou a quebra de serviços essenciais.
Passo 1: Estabelecer uma Linha de Base
Antes de implementar quaisquer regras de bloqueio, configure seus resolvedores DNS atuais para registrar todas as consultas. Execute isso em modo de auditoria por pelo menos 14 dias para capturar uma amostra representativa do tráfego em todos os locais. Analise esses logs para identificar os domínios mais consultados e calcular a porcentagem de consultas direcionadas a redes de anúncios e rastreadores conhecidos. Esta linha de base é essencial para medir o ROI pós-implantação.
Passo 2: Definir Políticas de Filtragem por Segmento de Rede
Uma política de filtragem monolítica raramente é eficaz em um ambiente corporativo. Você deve segmentar suas políticas com base na finalidade da rede:
- Guest WiFi: Implemente bloqueio agressivo de redes de anúncios, rastreadores, conteúdo adulto e domínios de malware conhecidos para maximizar a economia de largura de banda e proteger a reputação do local.
- Redes de Funcionários/Corporativas: Aplique filtragem moderada. Embora domínios de malware e phishing devam ser bloqueados, o bloqueio excessivamente agressivo de anúncios pode interferir nas equipes de marketing ou em aplicativos SaaS específicos. Revise Políticas BYOD Seguras para Redes WiFi de Funcionários para obter orientação sobre o balançosegurança e acesso.
- Redes IoT/Operacionais: Implemente uma lista de permissões rigorosa (negação padrão). Dispositivos IoT (por exemplo, termostatos inteligentes, terminais de ponto de venda) devem ser capazes de resolver apenas os domínios específicos necessários para sua operação.
Passo 3: Selecione e Teste as Blocklists
A eficácia da sua filtragem DNS depende inteiramente da qualidade das suas Blocklists. Confiar em uma única fonte é arriscado. Combine feeds de inteligência de ameaças comerciais com listas confiáveis mantidas pela comunidade (por exemplo, OISD).
Crucialmente, execute as Blocklists selecionadas em modo de 'simulação' ou monitoramento primeiro. Analise os logs para identificar quaisquer falsos positivos — domínios legítimos que seriam bloqueados. Por exemplo, bloquear uma CDN principal pode inadvertidamente interromper a renderização de aplicações de negócios críticas.
Passo 4: Abordar DNS sobre HTTPS (DoH)
Navegadores modernos (Chrome, Firefox, Edge) estão cada vez mais usando DNS sobre HTTPS (DoH) por padrão, o que criptografa as consultas DNS e as envia diretamente para resolvedores em nuvem (como Google ou Cloudflare), ignorando os servidores DNS atribuídos por DHCP da sua rede local. Se o DoH estiver ativo, sua filtragem DNS é ignorada.
Para mitigar isso, você deve configurar seus firewalls de borda para bloquear o tráfego de saída para provedores DoH conhecidos na porta 443, forçando os navegadores a retornar ao resolvedor DNS local e não criptografado onde suas políticas de filtragem são aplicadas.
Melhores Práticas
- Automatizar Atualizações de Blocklist: Os cenários de ameaças e os domínios de veiculação de anúncios mudam diariamente. Garanta que sua solução de filtragem DNS puxe automaticamente as atualizações dos feeds de inteligência de ameaças escolhidos a cada 24 horas, no mínimo.
- Implementar um Cache Local: Para minimizar a latência, garanta que seu resolvedor DNS local armazene em cache as consultas frequentes. Mesmo que você use um serviço de filtragem baseado em nuvem, um encaminhador de cache local reduz o tempo de ida e volta para solicitações comuns.
- Manter uma Allow-List Acessível: Falsos positivos acontecerão. Estabeleça um processo claro e rápido para as equipes de suporte de TI adicionarem domínios específicos a uma allow-list quando um serviço legítimo for bloqueado inadvertidamente.
- Garantir Conformidade: Os logs de consulta DNS contêm informações sobre o comportamento de navegação do usuário, que podem estar sujeitas a regulamentações como GDPR ou CCPA. Garanta que suas práticas de registro estejam alinhadas com as políticas de privacidade da sua organização. Para mais informações sobre como manter registros seguros, consulte Explique o que é trilha de auditoria para segurança de TI em 2026 .
Solução de Problemas e Mitigação de Riscos
Modos de Falha Comuns
- Falha no Captive Portal: A filtragem DNS agressiva pode, às vezes, bloquear os domínios necessários para a detecção de Captive Portal do sistema operacional do dispositivo (por exemplo,
captive.apple.com). Garanta que esses domínios essenciais estejam explicitamente na allow-list. - Mau Funcionamento da Aplicação: Algumas aplicações móveis falharão ao carregar ou travarão se seus domínios de telemetria ou veiculação de anúncios estiverem inacessíveis. Se um aplicativo crítico usado por sua equipe ou convidados estiver falhando, revise os logs DNS para consultas bloqueadas originadas desses dispositivos e ajuste a allow-list de acordo.
- Gargalos de Desempenho: Ao implantar um appliance on-premises, garanta que ele esteja adequadamente provisionado para lidar com o pico de consultas por segundo (QPS) da sua rede. Um resolvedor DNS com recursos insuficientes introduzirá latência significativa, degradando a experiência do usuário muito mais do que os anúncios teriam.
ROI e Impacto nos Negócios
A implementação da filtragem DNS proporciona retornos mensuráveis em três áreas principais:
- Redução de Custos de Largura de Banda: Ao eliminar de 15% a 35% do tráfego não essencial, as organizações podem frequentemente atrasar atualizações caras de circuitos de ISP. Em ambientes com conexões medidas ou backhaul via satélite, a economia de custos é imediata e substancial.
- Melhora no Desempenho da Rede: Reduzir o volume de conexões simultâneas e o tempo de rádio consumido pelo tráfego de fundo melhora diretamente a taxa de transferência e a latência para atividades legítimas do usuário. Isso se traduz em menos tickets de helpdesk sobre 'WiFi lento' e maiores pontuações de satisfação do usuário.
- Postura de Segurança Aprimorada: Bloquear domínios de comando e controle (C2) de malware e sites de phishing na camada DNS reduz significativamente o risco de uma violação bem-sucedida originada de um dispositivo comprometido na rede de convidados ou da equipe.
À medida que as iniciativas do setor público e de cidades inteligentes se expandem — como as defendidas em nosso recente anúncio, Purple nomeia Iain Fox como VP de Crescimento – Setor Público para Impulsionar a Inclusão Digital e a Inovação em Cidades Inteligentes — a utilização eficiente da largura de banda torna-se crítica para fornecer conectividade equitativa e de alto desempenho em escala. Além disso, recursos como Purple Lança Modo de Mapas Offline para Navegação Contínua e Segura para Hotspots WiFi demonstram como a otimização dos recursos de rede pode aprimorar a jornada geral do usuário.
Definições principais
DNS Resolution
The process of translating a human-readable domain name (e.g., example.com) into a machine-readable IP address.
This is the prerequisite step for almost all network traffic; intercepting it here is the most efficient way to block unwanted connections.
DNS over HTTPS (DoH)
A protocol for performing remote DNS resolution via the HTTPS protocol, encrypting the query.
DoH prevents local network administrators from seeing or filtering DNS requests, requiring specific firewall rules to mitigate.
Telemetry Traffic
Automated communications sent by operating systems or applications to their vendors, reporting usage data, diagnostics, or status.
While individually small, the aggregate telemetry traffic from hundreds of devices on a public WiFi network consumes significant bandwidth.
NXDOMAIN
A DNS response indicating that the requested domain name does not exist.
DNS filters often return an NXDOMAIN response for blocked domains, immediately terminating the client's connection attempt.
Threat Intelligence Feed
A continuously updated stream of data providing information on known malicious domains, IPs, and URLs.
Used to dynamically update DNS blocklists to protect networks from newly identified malware and phishing infrastructure.
False Positive
In DNS filtering, when a legitimate, necessary domain is incorrectly categorized and blocked.
False positives cause application breakage and require a rapid allow-listing process to resolve user complaints.
Allow-List (Default Deny)
A security posture where all traffic is blocked by default, and only explicitly approved domains are permitted to resolve.
Best practice for highly secure or operational networks (like IoT or POS systems) where the required domains are known and finite.
Captive Portal Detection
The mechanism by which an OS determines if it is behind a captive portal, usually by attempting to reach a specific vendor domain.
If DNS filtering blocks these specific domains, devices will fail to display the WiFi login page, preventing users from connecting.
Exemplos práticos
A 400-room hotel is experiencing severe network congestion during the evening peak (7 PM - 10 PM). The 1Gbps ISP connection is saturated, and guests are complaining about slow video streaming. Upgrading the circuit to 2Gbps will cost an additional £1,500 per month. How can the IT Director use DNS filtering to address this?
- Deploy a cloud-based DNS filtering solution and configure the core router's DHCP scope to assign the new resolvers to the Guest VLAN.
- Enable a comprehensive blocklist targeting ad networks, tracking pixels, and known bandwidth-heavy telemetry endpoints.
- Configure the edge firewall to block outbound DoH (DNS over HTTPS) traffic to ensure all guest devices use the filtered resolvers.
- Monitor the bandwidth utilization during the next evening peak.
A large retail chain offers free Guest WiFi across 50 locations. They have noticed a high volume of background traffic originating from Android devices, primarily Google Play Services telemetry, which is degrading the performance of the in-store point-of-sale (POS) tablets sharing the same WAN link.
- Implement policy-based DNS filtering via the central WiFi management platform.
- Create two distinct policies: one for the Guest SSID and one for the POS SSID.
- On the Guest SSID policy, apply standard ad and malware blocking, plus specific rules to rate-limit or block non-essential OS telemetry domains.
- On the POS SSID policy, implement a strict allow-list, only permitting DNS resolution for the payment gateway, inventory management system, and essential MDM (Mobile Device Management) endpoints.
Questões práticas
Q1. You are deploying DNS filtering across a university campus network. During the pilot phase, students report that they cannot access the login page for the campus WiFi. What is the most likely cause, and how do you resolve it?
Dica: Think about how operating systems determine if they need to display a login screen.
Ver resposta modelo
The DNS filter is likely blocking the specific domains used by Apple, Android, and Windows for Captive Portal Detection (e.g., captive.apple.com, connectivitycheck.gstatic.com). The resolution is to immediately add these vendor-specific captive portal domains to the global allow-list.
Q2. A stadium IT director wants to implement DNS filtering to save bandwidth during game days. However, they are concerned about the latency introduced by routing all DNS queries to a cloud provider. What architectural approach should you recommend?
Dica: Consider where the DNS resolution process physically takes place.
Ver resposta modelo
Recommend deploying an On-Premises DNS Appliance or a local caching forwarder. This keeps the initial DNS resolution local to the stadium infrastructure, providing sub-millisecond response times, while still utilizing cloud-based threat intelligence feeds to update the local blocklists asynchronously.
Q3. After implementing DNS filtering, the dashboard shows a 25% reduction in DNS queries, but the overall WAN bandwidth utilization has only dropped by 5%. What is the most likely reason for this discrepancy?
Dica: What protocol bypasses local DNS resolvers entirely?
Ver resposta modelo
Client devices (specifically modern browsers) are likely using DNS over HTTPS (DoH) to bypass the local DNS resolvers. While some background OS traffic is being caught by the local filter (the 25% query reduction), the heavy browser traffic is encrypted and bypassing the filter. The firewall must be configured to block outbound DoH traffic to force browsers to fall back to the local resolver.