Como a Atualização de Aplicativos em Segundo Plano Mata o Desempenho do WiFi Público
Este guia técnico examina o impacto severo da atualização de aplicativos em segundo plano na capacidade e desempenho do WiFi público. Ele fornece estratégias de mitigação acionáveis, em nível de rede, para que gerentes de TI recuperem tempo de transmissão e melhorem a experiência do convidado.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada
- A Anatomia do Tráfego em Segundo Plano
- O Mito da Mitigação do Wi-Fi 6
- Guia de Implementação
- 1. Classificação e Definição de Linha de Base do Tráfego
- 2. Desenvolvimento da Lista de Bloqueio
- 3. Aplicação de Políticas na Camada do Controlador
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios
Resumo Executivo
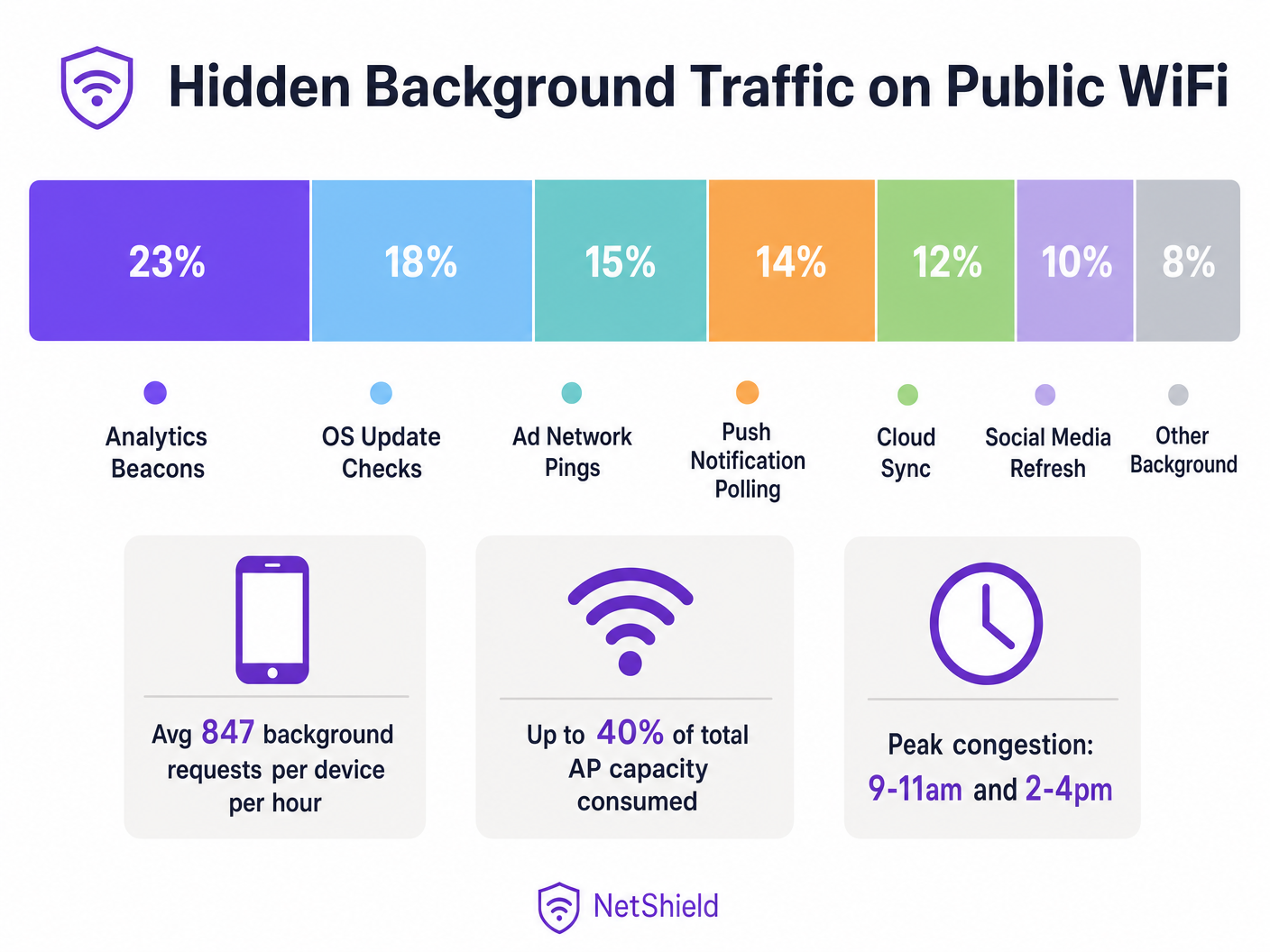
Em ambientes sem fio públicos de alta densidade, até 40% da capacidade do ponto de acesso pode ser silenciosamente consumida pelo tráfego de atualização de aplicativos em segundo plano — beacons de análise, pings de redes de anúncios, verificações de atualização de SO e sondagem de notificações push. Este guia fornece a arquitetos de rede e gerentes de TI um plano neutro em relação a fornecedores para identificar, classificar e mitigar o tráfego em segundo plano na camada de rede. Ao implementar listas de bloqueio direcionadas e políticas de limitação de taxa, os locais podem recuperar um tempo de transmissão significativo, adiar atualizações de hardware caras e melhorar drasticamente a experiência de conectividade para o tráfego de usuários legítimos.
Análise Técnica Detalhada
A Anatomia do Tráfego em Segundo Plano
Todo smartphone conectado à sua rede Guest WiFi executa dezenas de aplicativos configurados para realizar ciclos de atualização em segundo plano. Esses processos operam independentemente da interação do usuário, iniciando conexões com servidores de telemetria, endpoints de sincronização na nuvem e redes de anúncios.
Na camada de rádio, o impacto é desproporcional ao tamanho da carga útil. Em uma rede 802.11 usando CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance), cada transação requer uma sequência completa de associação. Um beacon de análise de 200 bytes requer solicitações de sonda, autenticação, associação e negociação DHCP. Em ambientes como Varejo ou Hotelaria , essa sobrecarga de contenção esgota rapidamente o tempo de transmissão disponível.
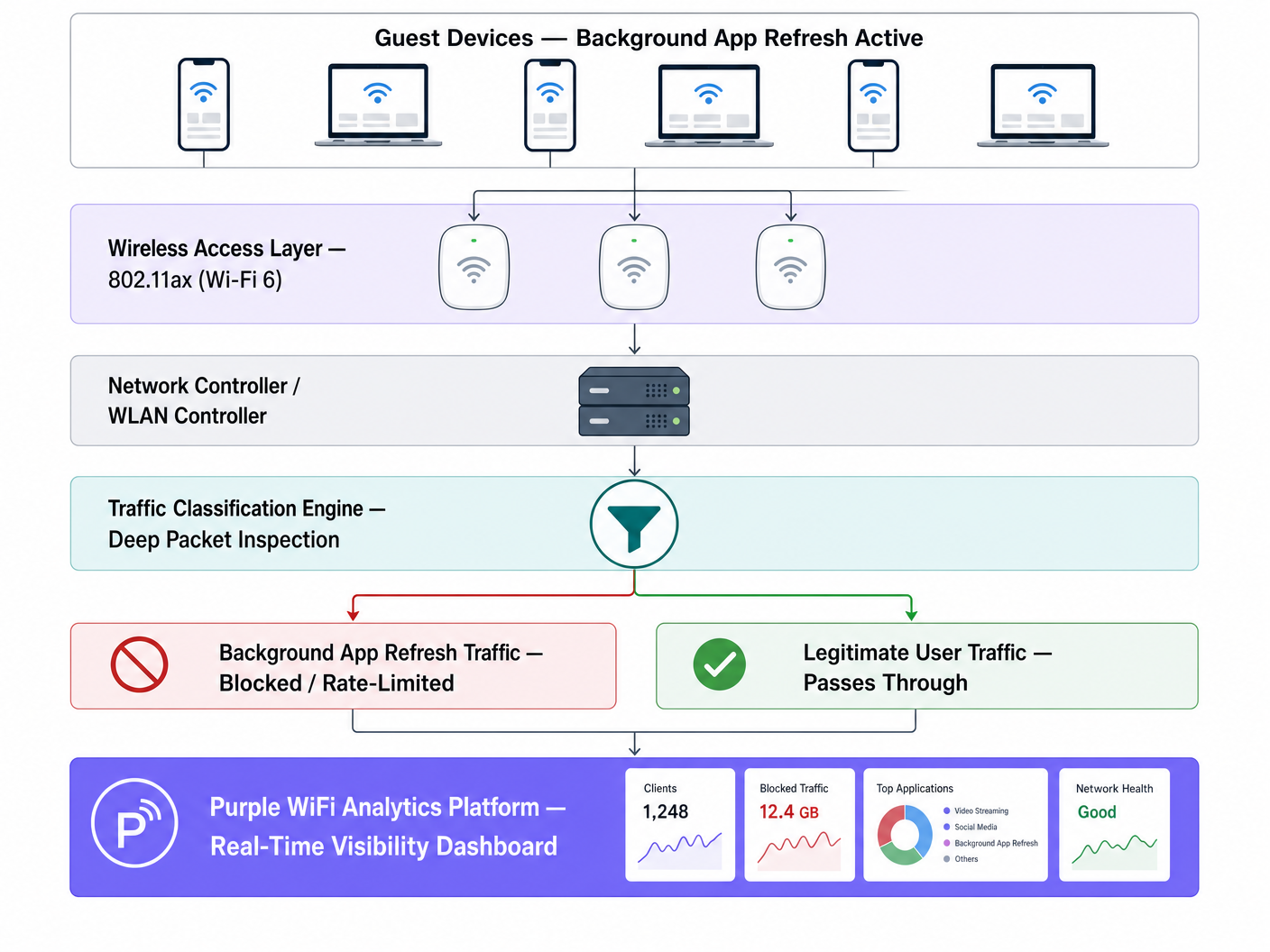
O Mito da Mitigação do Wi-Fi 6
Embora o Wi-Fi 6 (802.11ax) introduza OFDMA e BSS Colouring para gerenciar a contenção de alta densidade de forma mais eficiente, ele não resolve a questão fundamental da entrega de carga útil indesejada. O ponto de acesso não consegue distinguir entre um usuário transmitindo uma apresentação e um aplicativo sincronizando dados de diagnóstico silenciosamente. A intervenção em nível de rede via Deep Packet Inspection (DPI) continua essencial.
Guia de Implementação
1. Classificação e Definição de Linha de Base do Tráfego
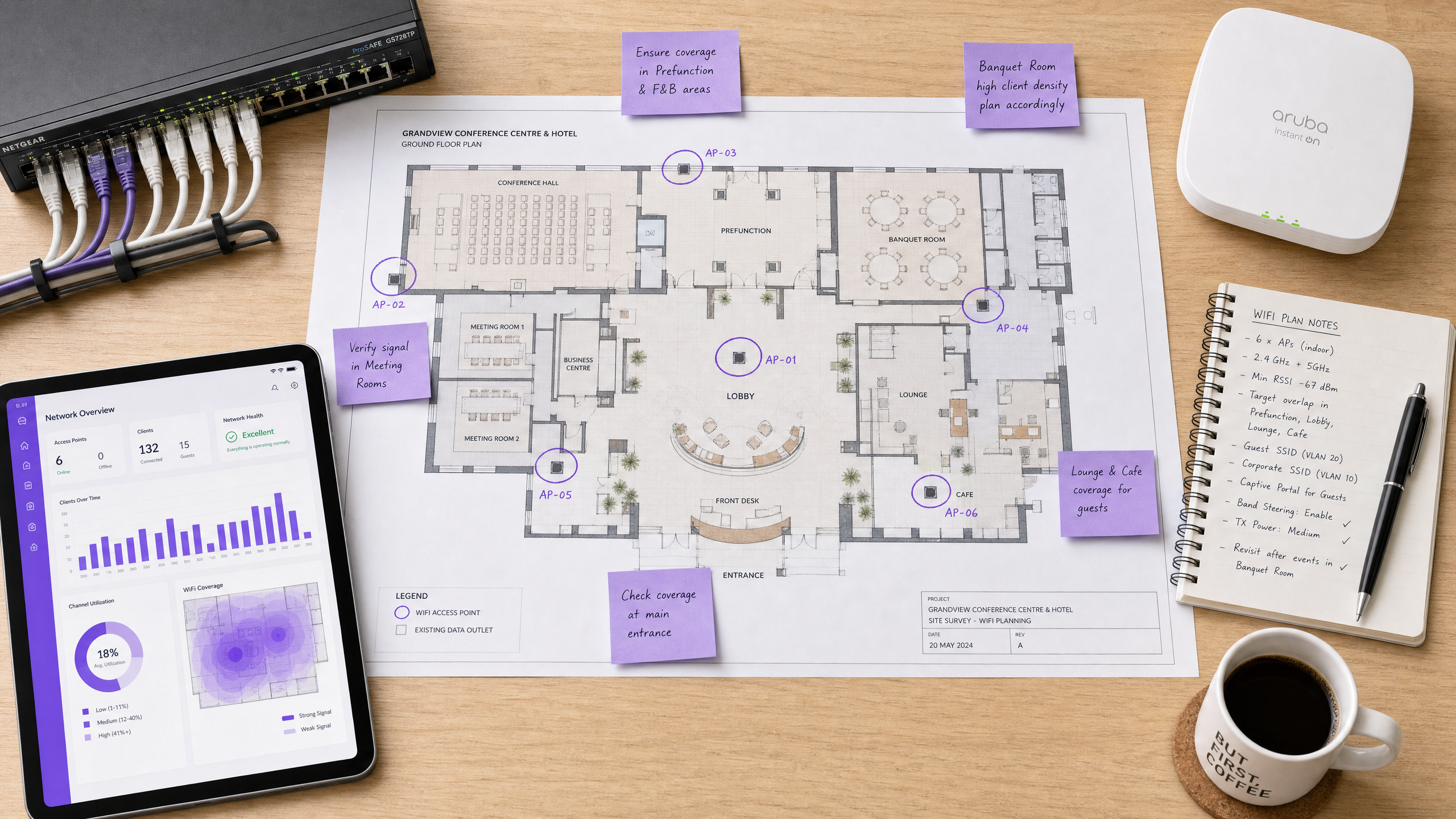
Antes de implementar mudanças de política, estabeleça uma linha de base usando sua plataforma de WiFi Analytics . Monitore o tráfego por pelo menos cinco dias úteis para identificar períodos de pico de atividade em segundo plano e os principais domínios de destino.
2. Desenvolvimento da Lista de Bloqueio
Implemente o bloqueio em nível de DNS ou IP para endpoints conhecidos de análise e redes de anúncios. Comece com listas validadas pela comunidade (como OISD) e complemente com seus dados de linha de base.
Exceção Crítica: Não bloqueie serviços essenciais de notificação push (por exemplo, Apple Push Notification Service na porta TCP 5223 ou Google Firebase Cloud Messaging). O bloqueio desses serviços interromperá a funcionalidade principal do dispositivo e gerará reclamações de usuários.
3. Aplicação de Políticas na Camada do Controlador
Aplique regras de classificação no controlador WLAN em vez de em pontos de acesso individuais para garantir a aplicação consistente da política.
Melhores Práticas
- Limitar Taxa de Atualizações de SO: Em vez de bloquear completamente as atualizações de SO, aplique um limite de taxa rigoroso (por exemplo, 1 Mbps por dispositivo) durante as horas de pico de operação.
- Implementar Marcação QoS: Use marcações DSCP para despriorizar o tráfego em segundo plano para a classe de tráfego mais baixa, permitindo que ele seja transmitido apenas quando o canal estiver livre.
- Monitoramento Contínuo: Os endpoints em segundo plano evoluem. Revise e atualize suas listas de bloqueio trimestralmente.
Solução de Problemas e Mitigação de Riscos
- Bloqueio Excessivo: O bloqueio agressivo sem testes pode quebrar a funcionalidade legítima de aplicativos. Sempre teste as políticas em um único grupo de AP antes da implantação em toda a propriedade.
- Ignorando a Divisão 5GHz/6GHz: O tráfego em segundo plano frequentemente se concentra em 2.4GHz devido a padrões de dispositivos legados. Garanta que a análise de tráfego cubra todas as bandas. Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 fornece contexto adicional sobre o gerenciamento de bandas.
ROI e Impacto nos Negócios
Recuperar 30-40% do tempo de transmissão desperdiçado é funcionalmente equivalente a aumentar sua densidade física de AP na mesma proporção. Para locais que enfrentam restrições de capacidade, o gerenciamento de tráfego em nível de rede pode adiar gastos de capital significativos em atualizações de hardware, ao mesmo tempo em que melhora imediatamente os índices de satisfação dos convidados.
Ouça o briefing técnico completo:
Definições principais
Background App Refresh
A mobile OS feature allowing apps to check for updates, sync data, and send telemetry without active user interaction.
The primary source of hidden air time consumption on high-density public networks.
CSMA/CA
Carrier Sense Multiple Access with Collision Avoidance; the protocol WiFi uses to manage access to the shared radio medium.
Explains why even small background payloads cause significant network overhead due to contention.
Air Time
The finite amount of time available for devices to transmit data over a specific radio frequency.
The critical resource depleted by background traffic, more important than raw bandwidth in high-density deployments.
Deep Packet Inspection (DPI)
Advanced network packet filtering that examines the data part of a packet to classify traffic types.
Required to distinguish between legitimate user traffic and background telemetry.
DSCP Marking
Differentiated Services Code Point; a mechanism for classifying and managing network traffic for Quality of Service (QoS).
Used to deprioritise background traffic so it only transmits when the network is idle.
BSS Colouring
A Wi-Fi 6 feature that identifies overlapping basic service sets to improve spatial reuse.
Improves efficiency but does not eliminate the need to block unwanted background payloads.
OFDMA
Orthogonal Frequency-Division Multiple Access; allows a single AP to communicate with multiple devices simultaneously.
A Wi-Fi 6 enhancement that mitigates but does not solve background traffic contention.
Rate Limiting
Controlling the rate of traffic sent or received on a network interface.
The recommended approach for managing essential but heavy background traffic, like OS updates.
Exemplos práticos
A 340-room four-star hotel is experiencing poor WiFi performance during peak check-in (3 PM - 6 PM) despite a recent Wi-Fi 6 hardware upgrade.
- Deploy traffic analysis via Purple WiFi Analytics.
- Identify that 38% of air time is consumed by background app refresh.
- Implement a targeted DNS block list for 847 known analytics and ad domains.
- Apply a 1 Mbps rate limit to identified OS update traffic during peak hours.
A regional retail chain with 60 stores reports that digital signage buffering occurs simultaneously with high guest WiFi usage.
- Baseline traffic across the estate.
- Discover iOS update checks on the guest SSID are saturating the WAN link.
- Deploy centralised policy via the WLAN controller to rate-limit Apple update servers to 512 Kbps per guest device.
- Prioritise digital signage MAC addresses via QoS.
Questões práticas
Q1. A stadium IT director wants to block all traffic to Apple and Google servers during a major sporting event to preserve bandwidth. What is the risk?
Dica: Consider essential device services that rely on persistent connections.
Ver resposta modelo
Blocking all traffic to Apple and Google will break essential push notification services (APNS on TCP 5223 and Firebase Cloud Messaging). This will cause legitimate apps (like digital ticketing or emergency alerts) to fail. Instead, block specific analytics subdomains and rate-limit OS updates.
Q2. After deploying a Wi-Fi 6 upgrade, a conference centre still experiences severe latency during the morning keynote when 2,000 attendees arrive. Why didn't the hardware upgrade solve the issue?
Dica: Think about what Wi-Fi 6 handles well versus what it cannot control.
Ver resposta modelo
Wi-Fi 6 improves efficiency (via OFDMA and BSS Colouring) but cannot distinguish between a user checking email and 2,000 devices simultaneously executing background app refreshes. The sheer volume of contention overhead still depletes air time. Network-level traffic classification is required.
Q3. When configuring QoS for a guest network, how should background traffic like cloud photo sync be handled?
Dica: It's not malicious, but it's not urgent.
Ver resposta modelo
It should be classified and marked with a low DSCP value (e.g., Background/Scavenger class). This deprioritises the traffic, ensuring it only transmits when the network is idle, protecting real-time traffic like VoIP or point-of-sale transactions.