Como Usar o Microsoft Intune para Distribuir Certificados WiFi para Dispositivos
Uma referência técnica abrangente para líderes de TI sobre a implantação de certificados WiFi 802.1X via Microsoft Intune. Abrange a arquitetura SCEP vs PKCS, etapas de implementação, mapeamento de conformidade e cenários de implantação reais para ambientes corporativos.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Resumo Executivo
- Análise Técnica Aprofundada: Arquitetura e Protocolos
- A Estrutura de Autenticação 802.1X
- EAP-TLS e Autenticação Mútua
- Mecanismos de Implantação de Certificados Intune: SCEP vs PKCS
- Guia de Implementação: Implantação Passo a Passo
- Passo 1: Preparar a Infraestrutura de Chave Pública (PKI)
- Passo 2: Implantar o Certificado Raiz Confiável
- Etapa 3: Implantar o Perfil de Certificado do Cliente
- Etapa 4: Configurar o Perfil de Wi-Fi
- Melhores Práticas e Recomendações Estratégicas
- Certificados de Dispositivo vs. Usuário
- Segmentação de Rede e Acesso de Convidados
- Abordando o Requisito de Mapeamento de Certificados do NPS
- Solução de Problemas e Mitigação de Riscos
- Modos de Falha Comuns
- ROI e Impacto nos Negócios

Resumo Executivo
Para líderes de TI empresariais que gerenciam ambientes em larga escala em Hospitalidade , Varejo ou locais do setor público, o acesso sem fio seguro é um requisito operacional básico. Confiar em PSKs (Pre-Shared Keys) compartilhadas ou autenticação por nome de usuário/senha (PEAP-MSCHAPv2) expõe a rede a roubo de credenciais, phishing e falhas de conformidade. O padrão da indústria para segurança WiFi empresarial robusta é 802.1X com EAP-TLS (Extensible Authentication Protocol com Transport Layer Security), que exige autenticação mútua baseada em certificado entre o dispositivo e a rede.
No entanto, a principal barreira para a adoção do EAP-TLS tem sido historicamente a sobrecarga operacional do gerenciamento do ciclo de vida dos certificados. O Microsoft Intune resolve isso automatizando a entrega, renovação e revogação de certificados digitais para dispositivos gerenciados em escala.
Esta referência técnica detalha a arquitetura, as metodologias de implantação (SCEP vs PKCS) e as etapas de implementação necessárias para distribuir certificados WiFi via Microsoft Intune. Ele fornece orientação prática para arquitetos de rede e engenheiros de sistemas encarregados de proteger as comunicações corporativas, mantendo uma separação rigorosa das redes de visitantes, como as gerenciadas por uma plataforma Guest WiFi .
Análise Técnica Aprofundada: Arquitetura e Protocolos
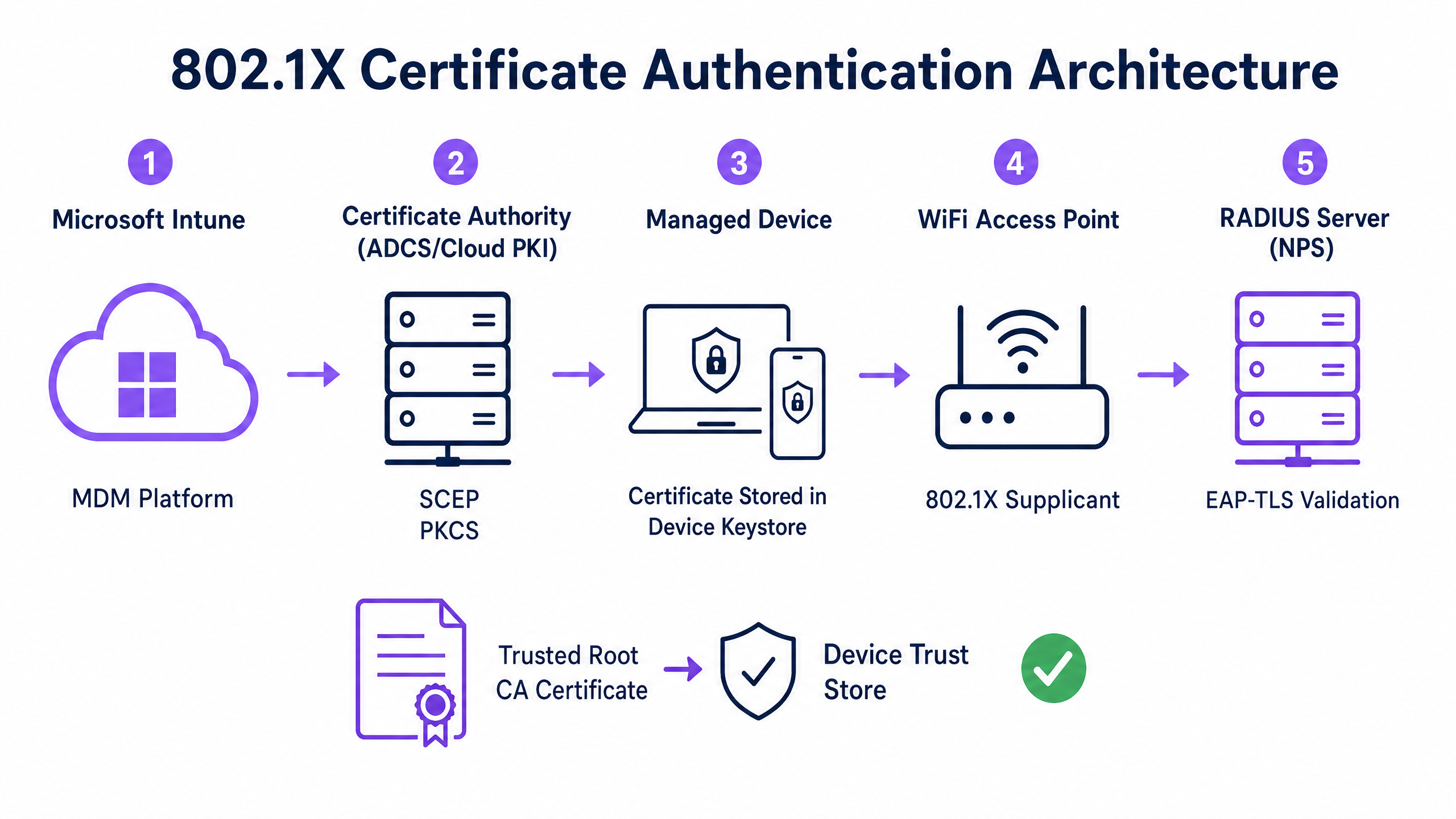
Para implementar a autenticação baseada em certificado de forma eficaz, as equipes de TI devem entender a interação entre a plataforma de Gerenciamento de Dispositivos Móveis (MDM), a Infraestrutura de Chave Pública (PKI) e a camada de controle de acesso à rede.
A Estrutura de Autenticação 802.1X
O padrão IEEE 802.1X define o controle de acesso à rede baseado em porta. Em um contexto sem fio, ele impede que um dispositivo transmita qualquer tráfego (além de quadros de autenticação EAP) até que sua identidade seja verificada. A arquitetura consiste em três componentes:
- Suplicante: O dispositivo cliente (laptop, smartphone, tablet) solicitando acesso à rede.
- Autenticador: O ponto de acesso sem fio ou controlador de LAN sem fio que bloqueia o tráfego até que a autenticação seja bem-sucedida.
- Servidor de Autenticação: O servidor RADIUS (Remote Authentication Dial-In User Service), como Microsoft Network Policy Server (NPS) ou Cisco ISE, que valida as credenciais e autoriza o acesso.
EAP-TLS e Autenticação Mútua
EAP-TLS é o método EAP mais seguro porque exige autenticação mútua. O servidor RADIUS apresenta seu certificado ao suplicante para provar que é a rede corporativa legítima (prevenindo ataques evil-twin), e o suplicante apresenta seu certificado de cliente ao servidor RADIUS para provar que é um dispositivo ou usuário autorizado.
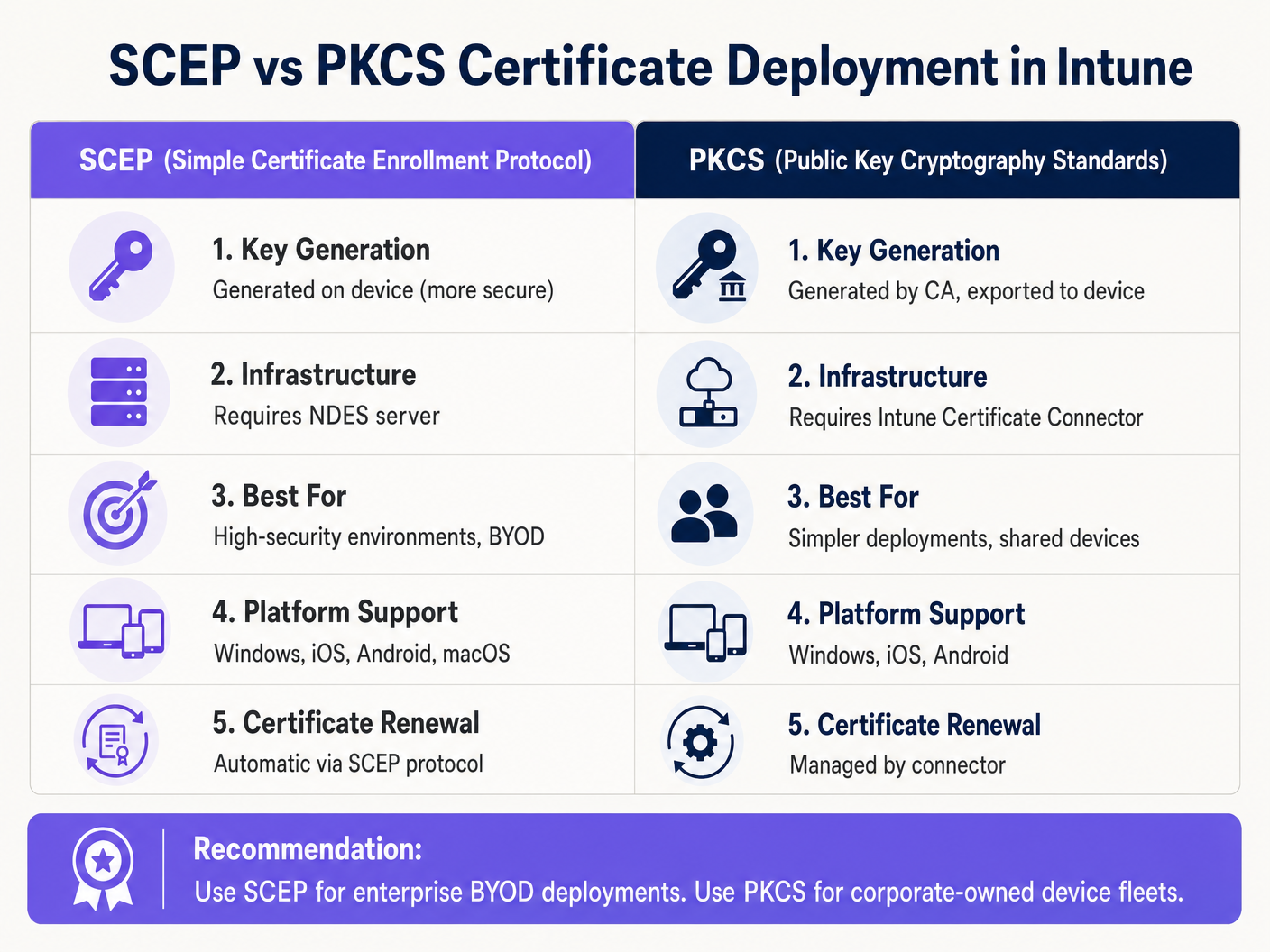
Mecanismos de Implantação de Certificados Intune: SCEP vs PKCS
O Microsoft Intune suporta dois protocolos primários para implantar certificados de cliente em dispositivos. A seleção do mecanismo apropriado é uma decisão arquitetônica crítica.
Protocolo de Registro de Certificado Simples (SCEP)
Com o SCEP, a chave privada é gerada diretamente no dispositivo cliente. O dispositivo cria uma Solicitação de Assinatura de Certificado (CSR) e a envia via Intune para o servidor Network Device Enrollment Service (NDES), que atua como um proxy para a infraestrutura Active Directory Certificate Services (ADCS). A CA emite o certificado, que é retornado ao dispositivo.
Como a chave privada nunca sai do dispositivo, o SCEP é considerado altamente seguro e é a abordagem recomendada para implantações BYOD (Bring Your Own Device) e arquiteturas de confiança zero.
Padrões de Criptografia de Chave Pública (PKCS)
Com o PKCS, o Intune Certificate Connector solicita o certificado da CA em nome do dispositivo. A CA gera tanto o certificado público quanto a chave privada, que o conector então entrega com segurança ao dispositivo via Intune.
Embora o PKCS simplifique os requisitos de infraestrutura (nenhum servidor NDES é necessário), a chave privada é transmitida pela rede. Este modelo é geralmente aceitável para frotas de dispositivos corporativos e totalmente gerenciados, onde a plataforma MDM já é um componente altamente confiável.
Guia de Implementação: Implantação Passo a Passo
A implantação de certificados WiFi via Intune requer sequenciamento preciso. A implantação de perfis fora de ordem é a causa mais comum de falha na implementação.
Passo 1: Preparar a Infraestrutura de Chave Pública (PKI)
Seja utilizando ADCS no local ou uma solução nativa da nuvem como Microsoft Cloud PKI, a Autoridade Certificadora deve ser configurada com os modelos apropriados.
- Uso da Chave: O modelo deve incluir o OID
Client Authentication(1.3.6.1.5.5.7.3.2). - Tamanho da Chave: Configure um tamanho mínimo de chave de 2048 bits (RSA) para alinhar com os padrões criptográficos modernos.
- Nome do Assunto: Para certificados de usuário, o Subject Alternative Name (SAN) deve ser configurado para usar o User Principal Name (UPN). Para certificados de dispositivo, use o Azure AD Device ID.
Passo 2: Implantar o Certificado Raiz Confiável
Antes que um dispositivo possa autenticar, ele deve confiar na CA que emitiu o certificado do servidor RADIUS.
- Exporte o certificado da CA Raiz (e quaisquer certificados de CA intermediários) em
.cer"formato. - No centro de administração do Intune, navegue até Dispositivos > Perfis de configuração > Criar perfil.
- Selecione a plataforma e escolha o tipo de perfil Certificado confiável.
- Carregue o arquivo
.cere atribua o perfil ao dispositivo de destino ou grupos de usuários.
Nota: Este perfil deve ser aplicado com sucesso aos dispositivos antes de prosseguir para as próximas etapas.
Etapa 3: Implantar o Perfil de Certificado do Cliente
Crie um perfil de certificado SCEP ou PKCS para entregar o certificado de identidade ao solicitante.
- Navegue até Dispositivos > Perfis de configuração > Criar perfil.
- Selecione a plataforma e escolha Certificado SCEP ou Certificado PKCS.
- Configure o formato do Nome do Assunto e SAN de acordo com seus requisitos de identidade (Usuário vs. Dispositivo).
- Especifique o Provedor de Armazenamento de Chaves (KSP) — tipicamente o Trusted Platform Module (TPM) para segurança baseada em hardware.
- Atribua o perfil aos mesmos grupos segmentados na Etapa 2.
Etapa 4: Configurar o Perfil de Wi-Fi
O componente final vincula os certificados às configurações da rede sem fio.
- Navegue até Dispositivos > Perfis de configuração > Criar perfil.
- Selecione a plataforma e escolha o tipo de perfil Wi-Fi.
- Defina o tipo de Wi-Fi como Enterprise e insira o SSID exato.
- Defina o tipo de EAP como EAP-TLS.
- Em Confiança do Servidor, especifique o nome exato do certificado do servidor RADIUS e selecione o perfil de certificado Raiz Confiável implantado na Etapa 2.
- Em Autenticação do Cliente, selecione o perfil de certificado SCEP ou PKCS implantado na Etapa 3.
- Atribua o perfil aos grupos de destino.
Melhores Práticas e Recomendações Estratégicas
Certificados de Dispositivo vs. Usuário
Os arquitetos de rede devem decidir se emitem certificados para o dispositivo (autenticação de máquina) ou para o usuário (autenticação de usuário).
- Certificados de Dispositivo: Permitem que a máquina se conecte à rede WiFi antes que um usuário faça login. Isso é crítico para o provisionamento inicial do dispositivo, processamento de Política de Grupo e redefinições de senha na tela de login. Recomendado para dispositivos corporativos.
- Certificados de Usuário: Vinculam o acesso à rede à identidade do indivíduo. Isso fornece auditoria granular e controle de acesso baseado em função. Recomendado para cenários BYOD.
Segmentação de Rede e Acesso de Convidados
Um princípio de segurança fundamental é a estrita separação lógica da rede corporativa 802.1X das redes de acesso de visitantes ou públicas. A infraestrutura gerenciada pelo Intune deve ser dedicada exclusivamente a dispositivos corporativos e funcionários autenticados.
Para acesso de visitantes, as organizações devem implantar um SSID Guest WiFi dedicado, apoiado por um Captive Portal. Isso garante que dispositivos não gerenciados sejam isolados, ao mesmo tempo em que permite que a empresa capture análises de visitantes por meio de uma plataforma WiFi Analytics . Para saber mais sobre como proteger a infraestrutura DNS em ambos os segmentos, consulte nosso guia sobre como Proteger Sua Rede com DNS e Segurança Fortes .
Abordando o Requisito de Mapeamento de Certificados do NPS
Para organizações que utilizam o Microsoft Network Policy Server (NPS) com dispositivos unidos ao Azure AD, uma mudança crítica de configuração foi introduzida pela Microsoft. O NPS agora exige um mapeamento forte de certificados.
Ao usar certificados de dispositivo, o objeto do computador no Active Directory local deve ter seu atributo altSecurityIdentities preenchido com os detalhes do certificado (tipicamente o X509IssuerSerialNumber). As equipes de TI devem implementar um script agendado ou um fluxo de trabalho orientado por eventos para atualizar este atributo quando o Intune emitir um novo certificado, caso contrário, a autenticação falhará.
Solução de Problemas e Mitigação de Riscos
Quando uma implantação 802.1X falha, o problema quase sempre reside na cadeia de certificados ou no sequenciamento do perfil do Intune.
Modos de Falha Comuns
- Falha Silenciosa do Perfil de WiFi: Se o perfil de WiFi do Intune for aplicado a um dispositivo antes que o certificado do cliente tenha sido provisionado com sucesso, o perfil de WiFi frequentemente falhará na instalação ou falhará silenciosamente. Sempre verifique a presença do certificado no armazenamento Pessoal do dispositivo (
certmgr.mscno Windows) antes de solucionar problemas da configuração de WiFi. - Erros de Validação de Confiança do Servidor: Se o dispositivo rejeitar o servidor RADIUS, verifique se o nome do servidor especificado no perfil de WiFi do Intune corresponde exatamente ao Nome do Assunto ou SAN no certificado do servidor RADIUS. Além disso, garanta que toda a cadeia de certificados (Raiz e Intermediário) esteja presente no armazenamento de Autoridades de Certificação Raiz Confiáveis do dispositivo.
- Indisponibilidade da Lista de Revogação de Certificados (CRL): Se o servidor RADIUS não conseguir alcançar o ponto de distribuição de CRL da CA para verificar o status do certificado do cliente, a autenticação será negada. Garanta que a URL da CRL esteja altamente disponível e acessível a partir do servidor RADIUS.
ROI e Impacto nos Negócios
A transição para a autenticação WiFi baseada em certificados via Intune oferece retornos operacionais e de segurança significativos.
- Mitigação de Riscos: Elimina o risco de coleta de credenciais, ataques pass-the-hash e acesso não autorizado à rede via PSKs compartilhadas.
- Eficiência Operacional: Reduz os tickets de suporte de TI relacionados a expirações de senha e problemas de conectividade WiFi. O gerenciamento automatizado do ciclo de vida significa que os certificados são renovados de forma transparente, sem intervenção do usuário.
- Habilitação de Conformidade: Satisfaz requisitos regulatórios rigorosos. Para ambientes de varejo, aborda diretamente os requisitos do PCI DSS para criptografia e autenticação sem fio robustas. Para o setor público e saúde, alinha-se com os princípios de acesso à rede de confiança zero (ZTNA).
Ao aproveitar o Microsoft Intune para implantação de certificados, as equipes de TI podem alcançar uma experiência sem fio sem atritos e altamente segura que opera silenciosamente em segundo plano, permitindo que a empresa se concentre nas operações principais.
GuidesSlugPage.keyDefinitionsTitle
802.1X
An IEEE standard for port-based network access control that prevents unauthorized devices from accessing a LAN or WLAN until they successfully authenticate.
The foundational security protocol that replaces shared WiFi passwords with enterprise-grade authentication in corporate environments.
EAP-TLS
Extensible Authentication Protocol with Transport Layer Security. An authentication framework that requires both the client and the server to prove their identities using digital certificates.
The specific protocol configured in the Intune WiFi profile to enforce mutual certificate authentication, eliminating the risk of credential theft.
SCEP
Simple Certificate Enrollment Protocol. A mechanism where the client device generates its own private key and requests a certificate from the CA via an intermediary server.
The preferred deployment method for BYOD environments because the private key is never transmitted across the network.
PKCS
Public Key Cryptography Standards. In the context of Intune, a deployment method where the CA generates the private key and the Intune Connector securely delivers it to the device.
A simpler deployment architecture often used for corporate-owned device fleets, as it removes the need for an NDES server.
NDES
Network Device Enrollment Service. A Microsoft server role that acts as a proxy, allowing devices running without domain credentials to obtain certificates from an Active Directory Certificate Authority.
A mandatory infrastructure component when deploying certificates via SCEP in an on-premises ADCS environment.
RADIUS
Remote Authentication Dial-In User Service. A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The server (like Microsoft NPS or Cisco ISE) that receives the authentication request from the WiFi access point and validates the device's certificate.
Supplicant
The software client on the end-user device (laptop, smartphone) that initiates the 802.1X authentication process.
The Intune WiFi profile configures the native OS supplicant (e.g., Windows WLAN AutoConfig) to use the correct certificates and EAP methods.
Certificate Revocation List (CRL)
A digitally signed list published by the Certificate Authority containing the serial numbers of certificates that have been revoked and should no longer be trusted.
Crucial for security compliance; the RADIUS server must check the CRL to ensure a connecting device hasn't been reported lost or stolen.
GuidesSlugPage.workedExamplesTitle
A 400-location retail chain is deploying corporate-owned tablets for inventory management. The devices are fully managed via Intune and joined to Azure AD. They need immediate network access upon boot to sync inventory databases, before any specific user logs in. The network infrastructure uses Cisco ISE as the RADIUS server. What is the optimal certificate deployment strategy?
The IT team should implement PKCS device certificates.
- Configure a device certificate template on the CA.
- Deploy the Root CA certificate to the tablets via Intune.
- Create a PKCS certificate profile in Intune, setting the Subject Name format to the Azure AD Device ID ({{AAD_Device_ID}}).
- Create an Enterprise WiFi profile specifying EAP-TLS, referencing the ISE server's certificate name and the deployed PKCS profile.
- Assign all profiles to the device group containing the tablets.
A large teaching hospital allows medical staff to use their personal smartphones (BYOD) to access clinical scheduling applications. The devices are enrolled in Intune via a Work Profile. Security policy mandates that no corporate credentials be stored on personal devices, and network access must be revoked immediately if a device is compromised. How should the WiFi authentication be designed?
The hospital must implement SCEP user certificates combined with Intune Compliance Policies.
- Deploy an NDES server to proxy requests to the CA.
- Create a SCEP user certificate profile in Intune, with the SAN configured to the User Principal Name ({{UserPrincipalName}}).
- Create an Intune Compliance Policy requiring a minimum OS version, an active screen lock, and no jailbreak/root access.
- Configure the CA to publish a highly available Certificate Revocation List (CRL).
- Configure the RADIUS server to strictly enforce CRL checking on every authentication attempt.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your organisation is migrating from PEAP-MSCHAPv2 (username/password) to EAP-TLS for the corporate WiFi. During the pilot phase, several Windows 11 laptops receive the Intune configuration profiles successfully but fail to connect to the network. Reviewing the Windows Event Logs shows Event ID 20271 indicating the RADIUS server certificate was rejected. What is the most likely cause?
GuidesSlugPage.hintPrefixConsider the chain of trust required for mutual authentication.
GuidesSlugPage.viewModelAnswer
The devices lack the Trusted Root CA certificate that issued the RADIUS server's certificate. In EAP-TLS, the device must validate the RADIUS server's identity. The IT team must ensure the 'Trusted certificate' profile containing the Root CA (and any Intermediate CAs) is deployed to the devices via Intune and successfully installed before the WiFi profile attempts to connect.
Q2. A public sector venue is deploying 802.1X for staff devices using Intune and PKCS certificates. They also operate a separate visitor network managed by a Guest WiFi platform. An auditor notes that if a staff laptop is stolen, the certificate remains valid for 12 months. How should the network architect address this risk?
GuidesSlugPage.hintPrefixHow does the authentication server know a certificate is no longer valid before it expires?
GuidesSlugPage.viewModelAnswer
The architect must implement a robust Certificate Revocation workflow. First, ensure the CA publishes a Certificate Revocation List (CRL) to a highly available distribution point. Second, configure the RADIUS server (e.g., NPS) to mandate CRL checking during every authentication attempt. Finally, establish an Intune operational procedure to explicitly revoke the certificate of any device marked as lost or stolen, which updates the CRL and blocks network access.
Q3. You are designing the Intune deployment for a fleet of shared kiosk devices in a retail environment. These devices reboot daily and must immediately connect to the corporate network to download updates before any user interacts with them. Should you deploy User certificates or Device certificates, and what Subject Alternative Name (SAN) format should be used?
GuidesSlugPage.hintPrefixConsider the state of the device immediately after a reboot.
GuidesSlugPage.viewModelAnswer
You must deploy Device certificates. Because the kiosks need network access before a user logs in, a User certificate would be unavailable at boot time. The Subject Alternative Name (SAN) in the Intune certificate profile should be configured to use the Azure AD Device ID ({{AAD_Device_ID}}) or the device's fully qualified domain name, allowing the RADIUS server to authenticate the specific hardware asset.



