EAP-TLS vs. PEAP: Qual Protocolo de Autenticação é o Certo para Sua Rede?
Uma comparação técnica abrangente dos protocolos de autenticação EAP-TLS e PEAP, cobrindo arquitetura de segurança, complexidade de implantação e implicações de conformidade. Este guia oferece estruturas de decisão acionáveis para líderes de TI em ambientes de hospitalidade, varejo, eventos e setor público que precisam selecionar o método de autenticação 802.1X correto para sua infraestrutura de WiFi empresarial.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Aprofundada: Arquitetura do Protocolo
- EAP-TLS: Autenticação Mútua por Certificado
- PEAP: Autenticação de Senha Tunelada
- Guia de Implementação: Estratégias de Implantação
- Implantando EAP-TLS
- Implantando PEAP
- Melhores Práticas e Padrões da Indústria
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios

Resumo Executivo
A seleção do protocolo de autenticação correto é uma decisão arquitetônica crítica que impacta tanto a postura de segurança quanto a sobrecarga operacional. Para gerentes de TI, arquitetos de rede e CTOs que operam em ambientes complexos — como Hospitalidade , Varejo , estádios e organizações do setor público — a escolha entre EAP-TLS e PEAP frequentemente dita o equilíbrio entre segurança robusta e viabilidade de implantação.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security) é amplamente considerado o padrão ouro para segurança de WiFi empresarial, contando com autenticação mútua baseada em certificado. PEAP (Protected Extensible Authentication Protocol), por outro lado, encapsula a autenticação padrão baseada em senha dentro de um túnel TLS criptografado, reduzindo significativamente a complexidade de implantação.
Este guia de referência técnica oferece uma análise arquitetônica aprofundada e neutra em relação a fornecedores de ambos os protocolos. Exploramos suas mecânicas operacionais, avaliamos as complexidades de implantação e fornecemos recomendações acionáveis para garantir que sua infraestrutura de rede atenda aos padrões de segurança modernos — incluindo conformidade com PCI DSS e GDPR — enquanto mantém conectividade perfeita para seus usuários.
Análise Técnica Aprofundada: Arquitetura do Protocolo
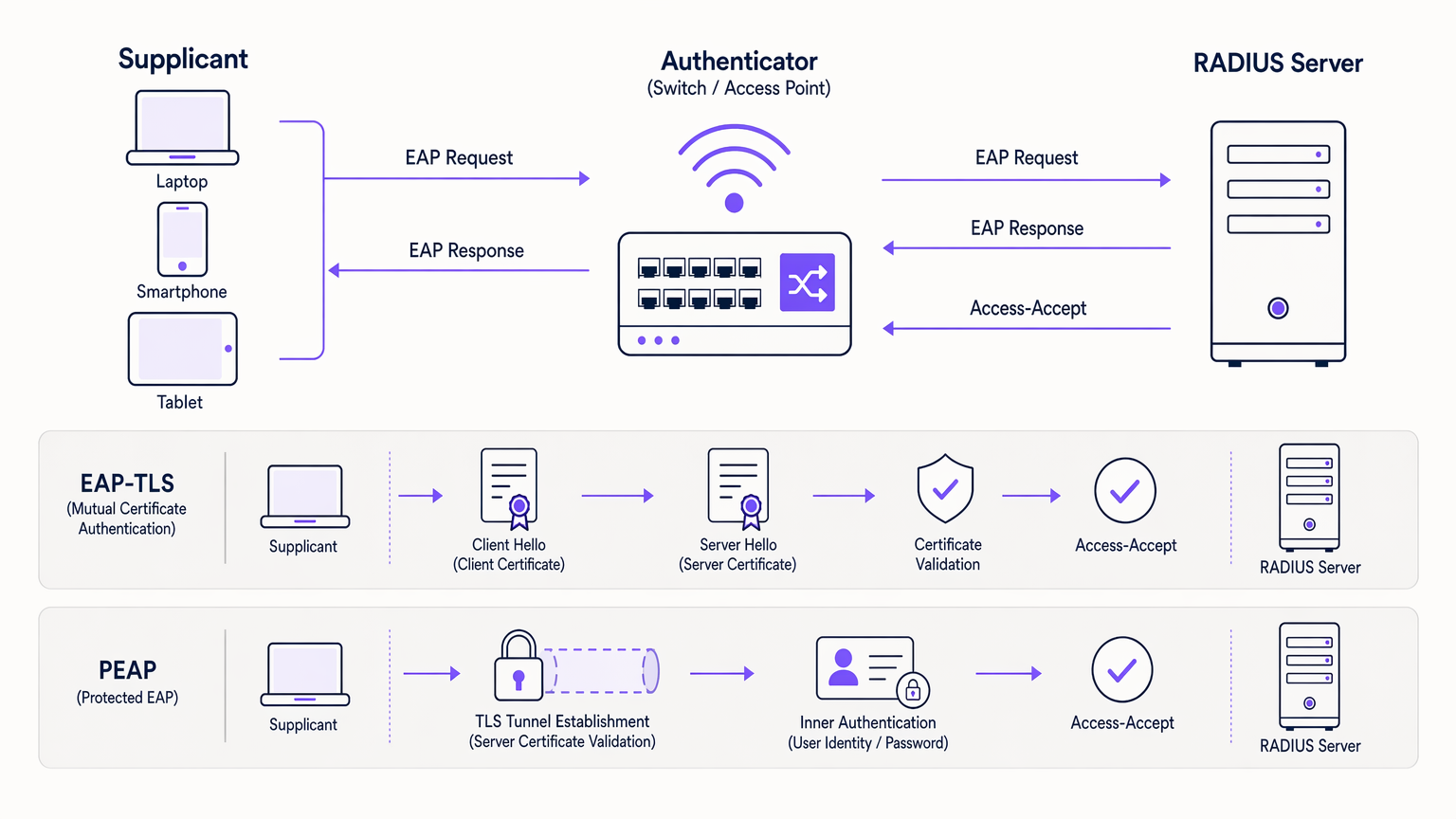
Para tomar uma decisão informada, é essencial entender a mecânica subjacente de como esses protocolos protegem a estrutura de autenticação 802.1X. Ambos os protocolos utilizam um servidor RADIUS para lidar com as solicitações de autenticação, mas seus métodos de validação de identidade diferem fundamentalmente. Para uma compreensão fundamental da infraestrutura RADIUS, consulte nosso guia sobre O Que É RADIUS? Como os Servidores RADIUS Protegem Redes WiFi .
EAP-TLS: Autenticação Mútua por Certificado
EAP-TLS opera no princípio da autenticação mútua. Tanto o dispositivo cliente (suplicante) quanto o servidor de autenticação (RADIUS) devem apresentar certificados digitais válidos para estabelecer uma conexão.
O Handshake: Quando um dispositivo tenta se conectar, o servidor RADIUS apresenta seu certificado ao cliente. O cliente valida este certificado contra suas Autoridades Certificadoras Raiz (CAs) confiáveis. Uma vez que o servidor é verificado, o cliente apresenta seu próprio certificado exclusivo de volta ao servidor. Se ambos os certificados forem válidos e não tiverem sido revogados — verificados via CRL ou OCSP — uma sessão TLS segura é estabelecida e o acesso à rede é concedido.
Esta verificação mútua torna o EAP-TLS altamente resistente a roubo de credenciais, ataques de dicionário e ataques Man-in-the-Middle (MitM). Como nenhuma senha é transmitida, credenciais de usuário comprometidas não podem ser usadas para violar a rede.
PEAP: Autenticação de Senha Tunelada
O PEAP foi desenvolvido como uma alternativa mais fácil de implantar ao EAP-TLS, eliminando a necessidade de certificados do lado do cliente, ao mesmo tempo em que oferece segurança robusta.
Estabelecimento do Túnel: O servidor RADIUS apresenta seu certificado ao cliente. O cliente valida o servidor, estabelecendo um túnel TLS criptografado. Dentro deste túnel seguro, o cliente realiza a autenticação padrão baseada em senha — tipicamente MSCHAPv2 — contra um provedor de identidade como o Active Directory. O servidor RADIUS valida as credenciais e concede acesso.
Embora o PEAP seja altamente seguro quando configurado corretamente, ele depende de os usuários manterem senhas fortes. Criticamente, se o dispositivo de um usuário não estiver configurado para validar o certificado do servidor, um ponto de acesso malicioso pode interceptar credenciais. Este não é um risco teórico; é um vetor de ataque bem documentado usado em testes de penetração no mundo real.
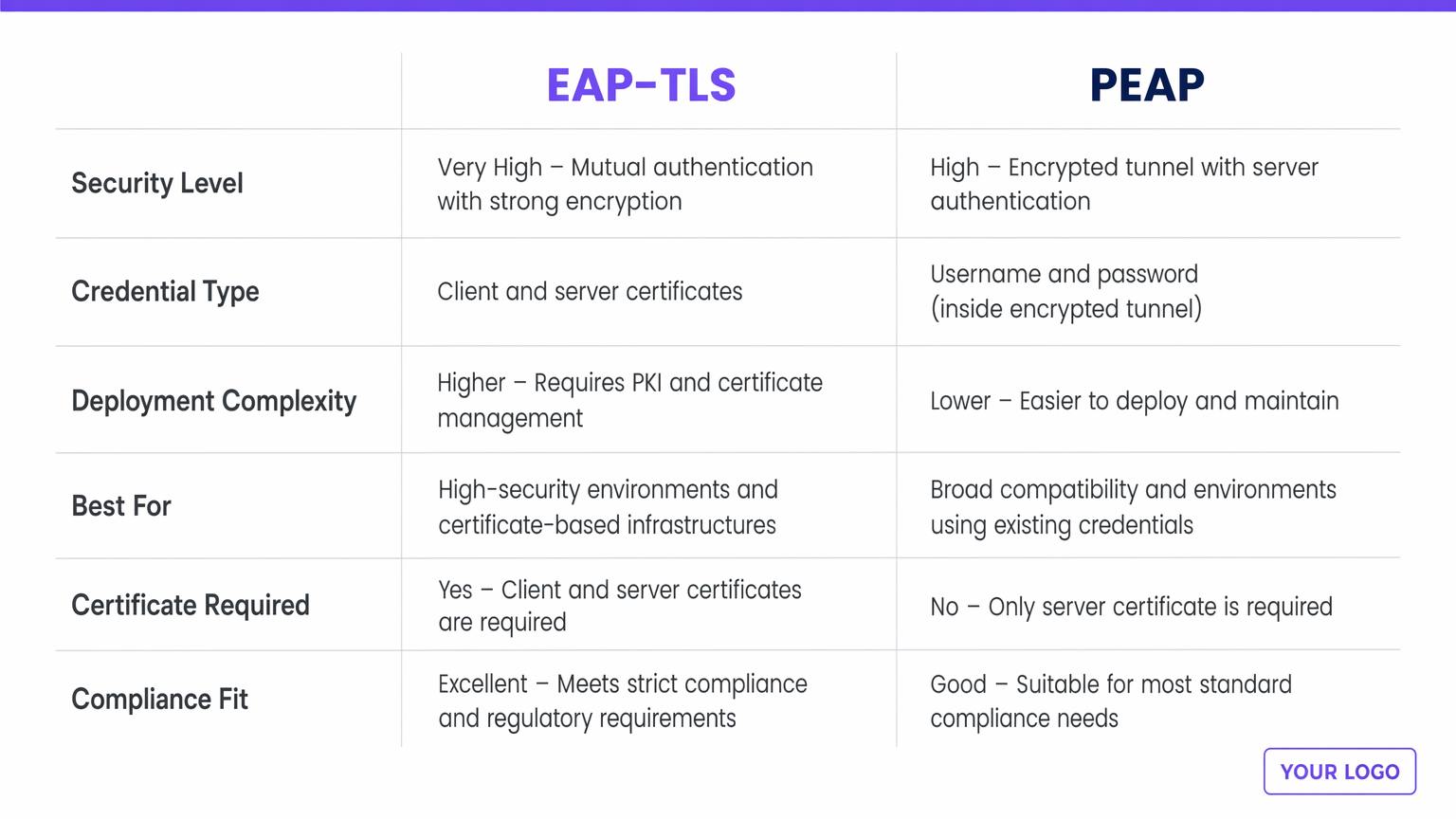
| Dimensão | EAP-TLS | PEAP |
|---|---|---|
| Nível de Segurança | Muito Alto — autenticação mútua por certificado | Alto — túnel criptografado, apenas certificado do servidor |
| Tipo de Credencial | Certificados digitais de cliente e servidor | Nome de usuário e senha (dentro do túnel TLS) |
| Complexidade de Implantação | Maior — requer PKI e MDM | Menor — integra-se com serviços de diretório existentes |
| Melhor Para | Frotas de dispositivos corporativos, indústrias regulamentadas | Ambientes BYOD, organizações sem PKI |
| Certificado de Cliente Necessário | Sim | Não |
| Adequação PCI DSS / GDPR | Excelente — preferencial para ambientes de alta conformidade | Bom — em conformidade quando a validação do servidor é imposta |
Guia de Implementação: Estratégias de Implantação
A principal divergência entre EAP-TLS e PEAP reside na complexidade de sua implantação e no gerenciamento do ciclo de vida.
Implantando EAP-TLS
A implementação de EAP-TLS requer uma robusta Infraestrutura de Chave Pública (PKI) para emitir, gerenciar e revogar certificados para cada dispositivo na rede. Soluções de Gerenciamento de Dispositivos Móveis (MDM) ou Gerenciamento de Mobilidade Empresarial (EMM) são praticamente obrigatórias para automatizar o provisionamento de certificados para endpoints em escala. As equipes de TI devem gerenciar os ciclos de vida dos certificados, lidando com renovações antes do vencimento e garantindo a revogação imediata para dispositivos perdidos ou funcionários que saem. EAP-TLS é mais adequado para redes corporativas com dispositivos de propriedade da empresa, ambientes altamente regulamentados como Saúde ou finanças, e arquiteturas de confiança zero.
Implantando PEAP
O PEAP é significativamente mais fácil de implantar porque aproveita os armazenamentos de identidade existentes — Active Directory, LDAP ou diretórios em nuvem — sem exigir certificados de cliente. Um servidor RADIUS com um certificado de servidor válido (idealmente fde uma CA pública) e a integração com seu serviço de diretório existente são suficientes para começar. A sobrecarga operacional é mínima: os usuários se autenticam com suas credenciais corporativas padrão. As políticas de rotação de senha se aplicam, o que pode causar uma pequena sobrecarga no helpdesk quando os usuários esquecem de atualizar seus perfis de WiFi após uma alteração de senha. O PEAP é mais adequado para ambientes BYOD, setores de educação e organizações sem uma infraestrutura PKI ou MDM estabelecida.
Melhores Práticas e Padrões da Indústria
Independentemente do protocolo escolhido, a adesão aos padrões da indústria é inegociável para mitigar riscos.
Impor Validação de Certificado do Servidor: A vulnerabilidade mais comum em implantações PEAP são dispositivos cliente mal configurados que não validam o certificado do servidor RADIUS. Isso permite que invasores configurem pontos de acesso não autorizados e coletem credenciais. A TI deve usar políticas de grupo ou perfis MDM para impor uma validação rigorosa do servidor em cada endpoint.
Implementar Redundância RADIUS: A autenticação é um caminho crítico. Garanta que sua infraestrutura RADIUS seja altamente disponível. Soluções RADIUS baseadas em nuvem podem aliviar pontos únicos de falha no local. As considerações arquitetônicas para resiliência de rede distribuída são discutidas mais detalhadamente em Os Principais Benefícios do SD WAN para Empresas Modernas .
Integrar com Provedores de Identidade Modernos: Para locais públicos, aproveitar uma plataforma robusta de Guest WiFi que atua como um provedor de identidade seguro pode otimizar o acesso, mantendo a segurança. A licença Connect da Purple, por exemplo, oferece um provedor de identidade gratuito para serviços como OpenRoaming, preenchendo a lacuna entre a segurança de nível empresarial e o onboarding de convidados sem interrupções.
Segmentação de Rede Pós-Autenticação: Uma autenticação 802.1X bem-sucedida não deve conceder acesso irrestrito a toda a sub-rede corporativa. Use políticas de atribuição dinâmica de VLAN para colocar os usuários em segmentos de rede apropriados com ACLs restritas.
Solução de Problemas e Mitigação de Riscos
Ao gerenciar redes 802.1X, as equipes de TI devem estar preparadas para modos de falha comuns.
Expiração de Certificado (EAP-TLS): Se o certificado da CA ou o certificado do servidor RADIUS expirar, todas as autenticações falharão simultaneamente. Implemente monitoramento e alertas agressivos para períodos de validade de certificados — defina alertas 90, 30 e 7 dias antes da expiração.
Má Configuração do Suplicante (PEAP): A falha na validação do certificado do servidor é um risco crítico. Audite regularmente as configurações dos endpoints para garantir que a "Validação do certificado do servidor" seja estritamente aplicada. Inclua isso como um item padrão em sua lista de verificação de auditoria de segurança.
Problemas de Timeout do RADIUS: Alta latência entre o controlador sem fio e o servidor RADIUS, ou entre o servidor RADIUS e o Active Directory, pode causar timeouts de EAP e falhas de autenticação. Garanta conectividade robusta e considere proxies RADIUS locais para sites distribuídos. Isso é particularmente relevante para implantações multi-site de Transporte e varejo.
Ataques de Pontos de Acesso Maliciosos: Conduza avaliações periódicas de segurança sem fio para detectar APs maliciosos. Sistemas de detecção de intrusão sem fio (WIDS) integrados à sua infraestrutura de ponto de acesso podem fornecer monitoramento contínuo.
ROI e Impacto nos Negócios
A decisão entre EAP-TLS e PEAP acarreta implicações comerciais significativas além da arquitetura técnica.
O EAP-TLS exige um CapEx inicial mais alto para soluções PKI e MDM, juntamente com um OpEx contínuo para gerenciamento de certificados. No entanto, ele oferece o mais alto nível de mitigação de riscos contra violações baseadas em credenciais, que podem resultar em danos financeiros e de reputação devastadores. Para locais que lidam com dados sensíveis ou operam sob estrita conformidade regulatória, o ROI do EAP-TLS é realizado através de custos de violação evitados e auditorias de conformidade simplificadas. Uma única violação baseada em credenciais em um ambiente de varejo ou hospitalidade pode custar milhões em remediação, multas regulatórias e danos à marca.
O PEAP oferece um tempo de valorização mais rápido e custos de implementação mais baixos. É altamente eficaz para ambientes onde o objetivo principal é o acesso seguro e criptografado, sem a sobrecarga do gerenciamento de dispositivos. Ao integrar o PEAP com uma solução abrangente de WiFi Analytics , os locais podem gerenciar o acesso com segurança enquanto extraem insights operacionais valiosos dos dados de uso da rede — conectando a infraestrutura de autenticação a resultados de negócios mensuráveis, como análise de tempo de permanência, padrões de fluxo de pessoas e taxas de visitantes recorrentes.
Definições principais
EAP (Extensible Authentication Protocol)
An authentication framework defined in IEEE 802.1X that provides the transport mechanism for various authentication methods over network access infrastructure.
EAP is the umbrella framework; EAP-TLS and PEAP are specific methods that run within it. IT teams encounter EAP when configuring RADIUS policies and wireless supplicant profiles.
Supplicant
The client device — laptop, smartphone, scanner, or IoT device — that initiates the authentication request to join the network.
IT teams must ensure supplicants are correctly configured, particularly regarding certificate validation, to prevent Man-in-the-Middle attacks. Supplicant configuration is the most common source of PEAP vulnerabilities.
Authenticator
The network device — typically a wireless access point or managed switch — that blocks all traffic from the supplicant until the RADIUS server confirms successful authentication.
The authenticator acts as the gatekeeper, passing EAP messages between the supplicant and the RADIUS server without processing the authentication itself.
RADIUS Server
Remote Authentication Dial-In User Service. The centralised server that receives authentication requests from the authenticator, validates credentials against an identity store, and returns an Access-Accept or Access-Reject response.
The RADIUS server is the brain of the 802.1X architecture. High availability and low latency between the RADIUS server and the identity store (Active Directory, LDAP) are critical for reliable authentication.
PKI (Public Key Infrastructure)
The framework of roles, policies, hardware, and software needed to create, manage, distribute, and revoke digital certificates.
A robust PKI is an absolute prerequisite for deploying EAP-TLS successfully at scale. Without PKI, certificate lifecycle management becomes unmanageable and creates significant operational risk.
MDM (Mobile Device Management)
Software used by IT to monitor, manage, and secure corporate mobile devices, including the ability to push configuration profiles, certificates, and policies silently to enrolled devices.
MDM is critical for EAP-TLS deployments to automate the silent provisioning of client certificates to end-user devices. Microsoft Intune, Jamf, and VMware Workspace ONE are common MDM platforms.
Mutual Authentication
A security process where both parties in a communications link authenticate each other before data is exchanged — as opposed to one-way authentication where only one party is verified.
The defining feature of EAP-TLS. Mutual authentication ensures the client knows it is talking to the legitimate network server, and the server knows it is talking to an authorised client device.
MSCHAPv2 (Microsoft Challenge Handshake Authentication Protocol v2)
A password-based authentication protocol commonly used as the inner authentication method within PEAP tunnels. It uses a challenge-response mechanism to avoid transmitting passwords in plaintext.
MSCHAPv2 hashes can be captured and cracked offline if the PEAP tunnel is compromised by a rogue access point. This is why server certificate validation in PEAP is non-negotiable.
OpenRoaming
A WiFi federation standard that allows users to automatically and securely connect to participating networks across different venues and operators without re-authenticating, using certificate-based authentication.
Purple acts as a free identity provider for OpenRoaming under its Connect licence, enabling venues to offer seamless, secure connectivity that aligns with EAP-TLS certificate authentication principles.
Exemplos práticos
A national retail chain with 500 locations needs to secure corporate network access for store managers' tablets and handheld inventory scanners. They currently use a shared WPA2-PSK across all sites. They have Microsoft Intune deployed for device management.
Deploy EAP-TLS. Since the organisation already utilises Microsoft Intune, the heavy lifting of certificate deployment is already solved. Configure Intune to push unique client certificates to all corporate-owned tablets and scanners via a SCEP or PKCS certificate profile. The wireless infrastructure is reconfigured to use 802.1X pointing to a central or cloud-based RADIUS server (such as Microsoft NPS or a cloud RADIUS service). The RADIUS server is configured to accept authentication only from devices presenting certificates issued by the organisation's internal CA. Post-authentication, dynamic VLAN assignment places devices into the appropriate store operations segment.
A large conference centre needs to provide secure WiFi for 3,000 internal staff using their own personal devices (BYOD). They use Google Workspace for corporate identity but do not manage staff personal phones or laptops.
Deploy PEAP (specifically PEAP-MSCHAPv2 or EAP-TTLS/PAP against Google Secure LDAP). The IT team sets up a RADIUS server integrated with Google Workspace Secure LDAP. Staff members connect to the 'Staff_WiFi' SSID using their standard Google Workspace email and password. The IT team provides onboarding documentation — ideally via a captive portal or network onboarding tool — instructing staff to configure their devices to trust the specific RADIUS server certificate and to validate the server's domain name. A separate guest SSID is maintained for event attendees, managed through Purple's Guest WiFi platform for analytics and access control.
Questões práticas
Q1. A university IT department is deploying secure WiFi across campus for 20,000 students. Students bring their own laptops and smartphones running a mix of Windows, macOS, iOS, and Android. The IT director insists on maximum security and proposes EAP-TLS. What is your architectural recommendation?
Dica: Consider the operational overhead of certificate management on unmanaged, personally-owned devices across a heterogeneous device estate.
Ver resposta modelo
Advise against EAP-TLS for this specific use case. While EAP-TLS offers the highest security, deploying and managing 20,000+ client certificates on unmanaged student devices without an MDM solution will create an insurmountable support burden. Students change devices frequently, and the onboarding process for certificate installation across iOS, Android, Windows, and macOS is complex without MDM automation. Recommend PEAP (or EAP-TTLS) integrated with the university's student directory service. Ensure robust onboarding tools are used to configure student devices to strictly validate the server certificate. Optionally, deploy EAP-TLS on a separate SSID for staff devices that are university-managed, creating a tiered security architecture.
Q2. During a security audit, a penetration tester successfully harvests user credentials from your PEAP-secured wireless network by setting up a rogue access point broadcasting the same SSID. What is the root cause of this vulnerability, and what is the remediation?
Dica: Think about what happens during the TLS tunnel establishment phase in PEAP, and what the client device is — or is not — checking.
Ver resposta modelo
The root cause is supplicant misconfiguration. The client devices are not configured to strictly validate the RADIUS server's digital certificate. When the rogue AP presented a fraudulent certificate, the client devices blindly trusted it, established the TLS tunnel with the attacker, and transmitted the MSCHAPv2 authentication exchange. The attacker can crack this offline. The remediation is threefold: (1) enforce strict server certificate validation via Group Policy or MDM profiles on all client devices; (2) specify the exact expected RADIUS server domain name in the supplicant configuration to prevent acceptance of certificates from other domains; (3) deploy a Wireless Intrusion Detection System (WIDS) to detect and alert on rogue access points.
Q3. A healthcare provider is upgrading its network to support mobile nursing workstations that access patient records. These workstations are corporate-owned, strictly managed by IT via Microsoft Intune, and the environment must comply with healthcare data protection regulations. Should they deploy PEAP or EAP-TLS?
Dica: Evaluate the regulatory environment, the level of device control, and the sensitivity of the data being accessed.
Ver resposta modelo
Deploy EAP-TLS without hesitation. The healthcare environment requires strict compliance and maximum security against credential theft — a compromised password in a healthcare network can expose patient records and trigger significant regulatory penalties under GDPR and sector-specific data protection requirements. Because the devices are corporate-owned and strictly managed via Microsoft Intune, deploying client certificates is operationally feasible and can be fully automated. EAP-TLS provides the necessary mutual authentication to ensure only authorised, corporate-managed devices can access the clinical network. Additionally, EAP-TLS simplifies compliance audits — auditors reviewing the network architecture will see a certificate-based, passwordless authentication system that is inherently more defensible than password-based alternatives.
Continue a ler esta série
PSK por Dispositivo por Fabricante: Comparativo entre iPSK, DPSK, MPSK e PPSK (e Suporte a WPA3)
Uma comparação abrangente das implementações de PSK por dispositivo no Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet e Ubiquiti UniFi. Saiba como o WPA3-SAE impacta as estratégias de chaves por dispositivo e quando implantar modos de transição em vez de migrar para o 802.1X.
O Que É Autenticação por Endereço MAC? Quando Usar e Quando Evitar
Este guia de referência técnica abrangente aborda a autenticação por endereço MAC em ambientes de WiFi corporativos — como a autenticação MAC baseada em RADIUS funciona na Camada 2, suas vulnerabilidades de segurança inerentes (incluindo spoofing de MAC e o impacto da randomização de MAC em nível de OS), e os contextos operacionais precisos onde ela permanece uma ferramenta válida para gerenciar dispositivos IoT e sem interface. Ele fornece orientação de implantação acionável para gerentes de TI e arquitetos de rede em locais de hotelaria, varejo, saúde e setor público, com exemplos práticos do mundo real, estruturas de decisão e contexto de integração para a plataforma de guest WiFi e análise da Purple.
Como Configurar WiFi Corporativo em iOS e macOS com 802.1X
Este guia autorizado fornece aos líderes de TI sêniores passos acionáveis para implantar WiFi corporativo 802.1X em dispositivos iOS e macOS. Ele aborda autenticação baseada em certificado (EAP-TLS), perfis de configuração MDM e integração de arquitetura para proteger redes corporativas, ao mesmo tempo que suporta iniciativas BYOD.