EAP-TLS vs. PEAP: ¿Qué protocolo de autenticación es el adecuado para su red?
Una comparación técnica exhaustiva de los protocolos de autenticación EAP-TLS y PEAP, que abarca la arquitectura de seguridad, la complejidad de la implementación y las implicaciones de cumplimiento. Esta guía proporciona marcos de decisión prácticos para líderes de TI en entornos de hostelería, comercio minorista, eventos y sector público que necesitan seleccionar el método de autenticación 802.1X adecuado para su infraestructura WiFi empresarial.
Escuchar esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectura del Protocolo
- EAP-TLS: Autenticación Mutua por Certificado
- PEAP: Autenticación de Contraseña Tunelizada
- Guía de Implementación: Estrategias de Despliegue
- Despliegue de EAP-TLS
- Despliegue de PEAP
- Mejores Prácticas y Estándares de la Industria
- Resolución de Problemas y Mitigación de Riesgos
- ROI e Impacto Empresarial

Resumen Ejecutivo
La selección del protocolo de autenticación adecuado es una decisión arquitectónica crítica que afecta tanto a la postura de seguridad como a la sobrecarga operativa. Para los gerentes de TI, arquitectos de red y CTO que operan en entornos complejos —como Hostelería , Comercio Minorista , estadios y organizaciones del sector público— la elección entre EAP-TLS y PEAP a menudo dicta el equilibrio entre una seguridad férrea y la viabilidad de la implementación.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security) es ampliamente considerado como el estándar de oro para la seguridad WiFi empresarial, basándose en la autenticación mutua basada en certificados. PEAP (Protected Extensible Authentication Protocol), por el contrario, encapsula la autenticación estándar basada en contraseña dentro de un túnel TLS cifrado, reduciendo significativamente la complejidad de la implementación.
Esta guía de referencia técnica proporciona un análisis arquitectónico profundo y neutral de ambos protocolos. Exploramos su mecánica operativa, evaluamos las complejidades de la implementación y ofrecemos recomendaciones prácticas para garantizar que su infraestructura de red cumpla con los estándares de seguridad modernos —incluida la conformidad con PCI DSS y GDPR— mientras mantiene una conectividad fluida para sus usuarios.
Análisis Técnico Detallado: Arquitectura del Protocolo
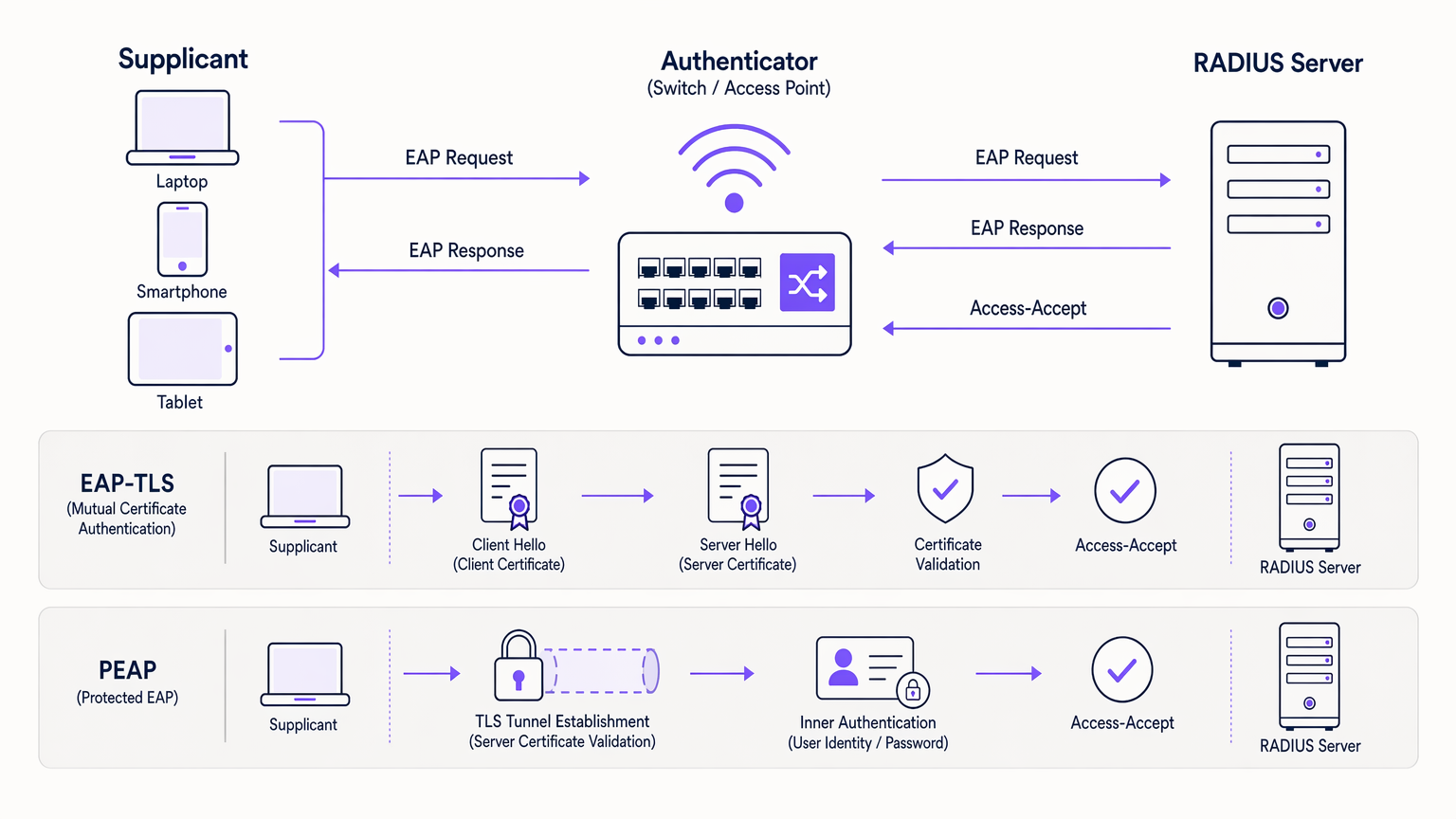
Para tomar una decisión informada, es esencial comprender la mecánica subyacente de cómo estos protocolos aseguran el marco de autenticación 802.1X. Ambos protocolos utilizan un servidor RADIUS para gestionar las solicitudes de autenticación, pero sus métodos de validación de identidad difieren fundamentalmente. Para una comprensión fundamental de la infraestructura RADIUS, consulte nuestra guía sobre ¿Qué es RADIUS? Cómo los servidores RADIUS aseguran las redes WiFi .
EAP-TLS: Autenticación Mutua por Certificado
EAP-TLS opera bajo el principio de autenticación mutua. Tanto el dispositivo cliente (solicitante) como el servidor de autenticación (RADIUS) deben presentar certificados digitales válidos para establecer una conexión.
El Handshake: Cuando un dispositivo intenta conectarse, el servidor RADIUS presenta su certificado al cliente. El cliente valida este certificado contra sus Autoridades de Certificación Raíz (CA) de confianza. Una vez verificado el servidor, el cliente presenta su propio certificado único al servidor. Si ambos certificados son válidos y no han sido revocados —verificado a través de CRL u OCSP— se establece una sesión TLS segura y se concede el acceso a la red.
Esta verificación mutua hace que EAP-TLS sea altamente resistente al robo de credenciales, ataques de diccionario y ataques Man-in-the-Middle (MitM). Dado que no se transmiten contraseñas, las credenciales de usuario comprometidas no pueden utilizarse para vulnerar la red.
PEAP: Autenticación de Contraseña Tunelizada
PEAP fue desarrollado como una alternativa más fácil de implementar a EAP-TLS, eliminando la necesidad de certificados del lado del cliente sin dejar de ofrecer una seguridad robusta.
Establecimiento del Túnel: El servidor RADIUS presenta su certificado al cliente. El cliente valida el servidor, estableciendo un túnel TLS cifrado. Dentro de este túnel seguro, el cliente realiza una autenticación estándar basada en contraseña —típicamente MSCHAPv2— contra un proveedor de identidad como Active Directory. El servidor RADIUS valida las credenciales y concede el acceso.
Aunque PEAP es altamente seguro cuando se configura correctamente, depende de que los usuarios mantengan contraseñas robustas. Críticamente, si el dispositivo de un usuario no está configurado para validar el certificado del servidor, un punto de acceso no autorizado puede interceptar las credenciales. Esto no es un riesgo teórico; es un vector de ataque bien documentado utilizado en pruebas de penetración en el mundo real.
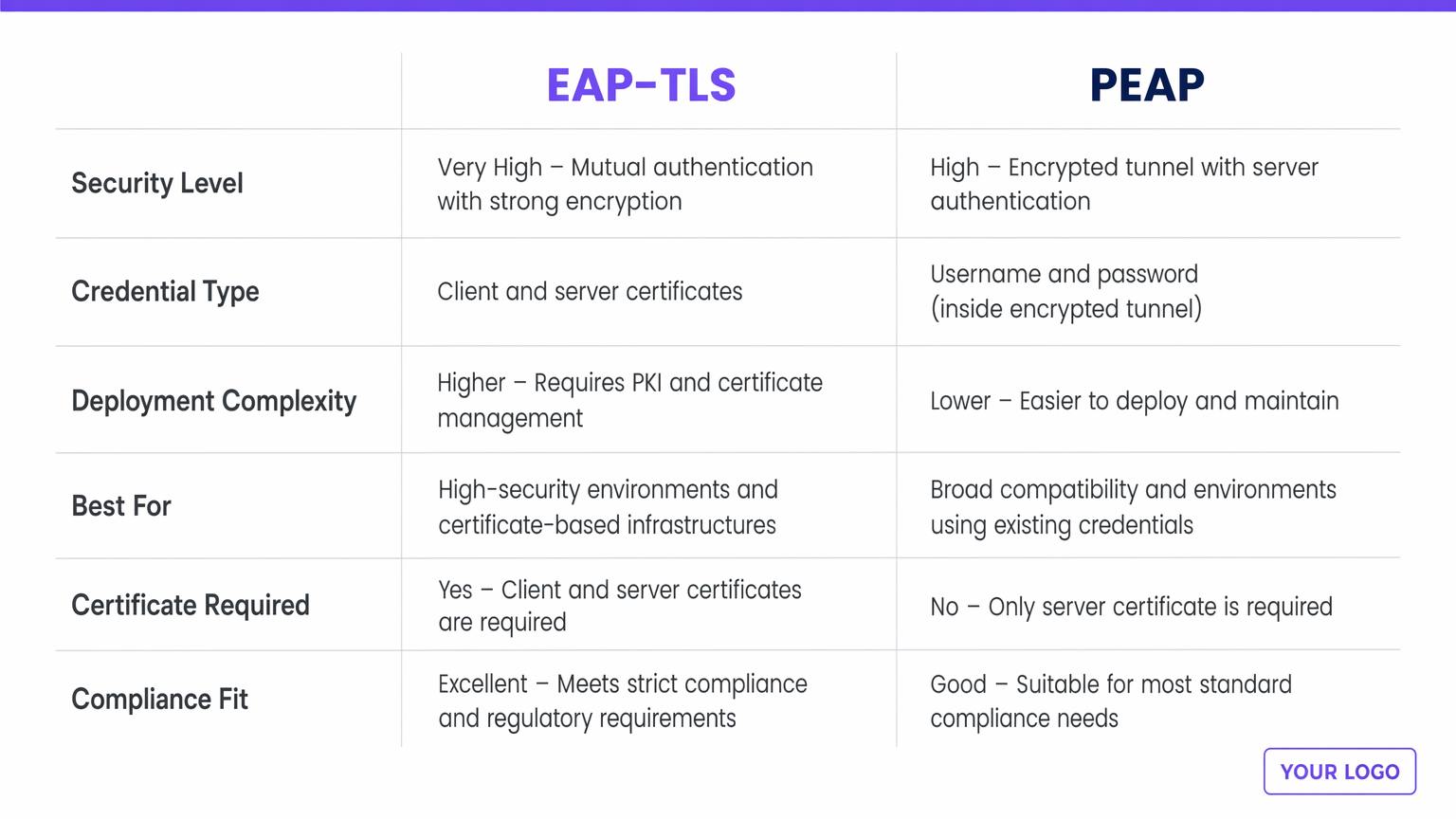
| Dimensión | EAP-TLS | PEAP |
|---|---|---|
| Nivel de Seguridad | Muy Alto — autenticación mutua por certificado | Alto — túnel cifrado, solo certificado de servidor |
| Tipo de Credencial | Certificados digitales de cliente y servidor | Nombre de usuario y contraseña (dentro del túnel TLS) |
| Complejidad de Implementación | Mayor — requiere PKI y MDM | Menor — se integra con servicios de directorio existentes |
| Ideal Para | Flotas de dispositivos corporativos, industrias reguladas | Entornos BYOD, organizaciones sin PKI |
| Certificado de Cliente Requerido | Sí | No |
| Adecuación PCI DSS / GDPR | Excelente — preferido para entornos de alta conformidad | Bueno — conforme cuando se aplica la validación del servidor |
Guía de Implementación: Estrategias de Despliegue
La divergencia principal entre EAP-TLS y PEAP reside en su complejidad de implementación y gestión del ciclo de vida.
Despliegue de EAP-TLS
La implementación de EAP-TLS requiere una robusta Infraestructura de Clave Pública (PKI) para emitir, gestionar y revocar certificados para cada dispositivo en la red. Las soluciones de Mobile Device Management (MDM) o Enterprise Mobility Management (EMM) son prácticamente obligatorias para automatizar el aprovisionamiento de certificados a los puntos finales a escala. Los equipos de TI deben gestionar los ciclos de vida de los certificados, manejando las renovaciones antes de la expiración y asegurando una revocación rápida para dispositivos perdidos o empleados que se marchan. EAP-TLS es más adecuado para redes corporativas con dispositivos propiedad de la empresa, entornos altamente regulados como Sanidad o finanzas, y arquitecturas de confianza cero.
Despliegue de PEAP
PEAP es significativamente más fácil de implementar porque aprovecha los almacenes de identidad existentes —Active Directory, LDAP o directorios en la nube— sin requerir certificados de cliente. Un servidor RADIUS con un certificado de servidor válido (idealmente fde una CA pública) y la integración con su servicio de directorio existente son suficientes para empezar. La sobrecarga operativa es mínima: los usuarios se autentican con sus credenciales corporativas estándar. Se aplican políticas de rotación de contraseñas, lo que puede causar una pequeña sobrecarga en el servicio de asistencia cuando los usuarios olvidan actualizar sus perfiles de WiFi después de un cambio de contraseña. PEAP es el más adecuado para entornos BYOD, sectores educativos y organizaciones sin una infraestructura PKI o MDM establecida.
Mejores Prácticas y Estándares de la Industria
Independientemente del protocolo elegido, la adhesión a los estándares de la industria es innegociable para mitigar el riesgo.
Aplicar la Validación del Certificado del Servidor: La vulnerabilidad más común en las implementaciones de PEAP son los dispositivos cliente mal configurados que no validan el certificado del servidor RADIUS. Esto permite a los atacantes configurar puntos de acceso no autorizados y obtener credenciales. TI debe utilizar políticas de grupo o perfiles MDM para aplicar una validación estricta del servidor en cada punto final.
Implementar Redundancia RADIUS: La autenticación es una ruta crítica. Asegure que su infraestructura RADIUS sea altamente disponible. Las soluciones RADIUS basadas en la nube pueden aliviar los puntos únicos de fallo en las instalaciones. Las consideraciones arquitectónicas para la resiliencia de la red distribuida se discuten más a fondo en Los Beneficios Clave de SD WAN para Empresas Modernas .
Integrar con Proveedores de Identidad Modernos: Para lugares de cara al público, aprovechar una sólida plataforma de Guest WiFi que actúe como un proveedor de identidad seguro puede agilizar el acceso manteniendo la seguridad. La licencia Connect de Purple, por ejemplo, proporciona un proveedor de identidad gratuito para servicios como OpenRoaming, cerrando la brecha entre la seguridad de nivel empresarial y la incorporación fluida de invitados.
Segmentación de Red Post-Autenticación: Una autenticación 802.1X exitosa no debe otorgar acceso irrestricto a toda la subred corporativa. Utilice políticas de asignación dinámica de VLAN para colocar a los usuarios en segmentos de red apropiados con ACLs restringidas.
Resolución de Problemas y Mitigación de Riesgos
Al gestionar redes 802.1X, los equipos de TI deben estar preparados para los modos de fallo comunes.
Caducidad del Certificado (EAP-TLS): Si el certificado de la CA o el certificado del servidor RADIUS caducan, todas las autenticaciones fallarán simultáneamente. Implemente una monitorización y alertas agresivas para los períodos de validez de los certificados — configure alertas a los 90, 30 y 7 días antes de la caducidad.
Configuración Errónea del Solicitante (PEAP): No validar el certificado del servidor es un riesgo crítico. Audite regularmente las configuraciones de los puntos finales para asegurar que "Validar certificado del servidor" se aplique estrictamente. Incluya esto como un elemento estándar en su lista de verificación de auditoría de seguridad.
Problemas de Tiempo de Espera de RADIUS: Una alta latencia entre el controlador inalámbrico y el servidor RADIUS, o entre el servidor RADIUS y Active Directory, puede causar tiempos de espera EAP y fallos de autenticación. Asegure una conectividad robusta y considere proxies RADIUS locales para sitios distribuidos. Esto es particularmente relevante para implementaciones multisitio de Transporte y minoristas.
Ataques de Puntos de Acceso Maliciosos: Realice evaluaciones periódicas de seguridad inalámbrica para detectar APs maliciosos. Los sistemas de detección de intrusiones inalámbricas (WIDS) integrados en su infraestructura de puntos de acceso pueden proporcionar una monitorización continua.
ROI e Impacto Empresarial
La decisión entre EAP-TLS y PEAP conlleva importantes implicaciones empresariales más allá de la arquitectura técnica.
EAP-TLS requiere un CapEx inicial más alto para soluciones PKI y MDM, junto con un OpEx continuo para la gestión de certificados. Sin embargo, proporciona el nivel más alto de mitigación de riesgos contra las brechas basadas en credenciales, que pueden resultar en daños financieros y reputacionales devastadores. Para los lugares que manejan datos sensibles u operan bajo un estricto cumplimiento normativo, el ROI de EAP-TLS se materializa a través de los costes de brecha evitados y las auditorías de cumplimiento optimizadas. Una sola brecha basada en credenciales en un entorno minorista u hotelero puede costar millones en remediación, multas regulatorias y daño a la marca.
PEAP ofrece un tiempo de valorización más rápido y menores costes de implementación. Es altamente efectivo para entornos donde el objetivo principal es un acceso seguro y cifrado sin la sobrecarga de la gestión de dispositivos. Al integrar PEAP con una solución integral de WiFi Analytics , los lugares pueden gestionar el acceso de forma segura mientras extraen valiosos conocimientos operativos de los datos de uso de la red, conectando la infraestructura de autenticación con resultados empresariales medibles como el análisis del tiempo de permanencia, los patrones de afluencia y las tasas de visitantes recurrentes.
Definiciones clave
EAP (Extensible Authentication Protocol)
An authentication framework defined in IEEE 802.1X that provides the transport mechanism for various authentication methods over network access infrastructure.
EAP is the umbrella framework; EAP-TLS and PEAP are specific methods that run within it. IT teams encounter EAP when configuring RADIUS policies and wireless supplicant profiles.
Supplicant
The client device — laptop, smartphone, scanner, or IoT device — that initiates the authentication request to join the network.
IT teams must ensure supplicants are correctly configured, particularly regarding certificate validation, to prevent Man-in-the-Middle attacks. Supplicant configuration is the most common source of PEAP vulnerabilities.
Authenticator
The network device — typically a wireless access point or managed switch — that blocks all traffic from the supplicant until the RADIUS server confirms successful authentication.
The authenticator acts as the gatekeeper, passing EAP messages between the supplicant and the RADIUS server without processing the authentication itself.
RADIUS Server
Remote Authentication Dial-In User Service. The centralised server that receives authentication requests from the authenticator, validates credentials against an identity store, and returns an Access-Accept or Access-Reject response.
The RADIUS server is the brain of the 802.1X architecture. High availability and low latency between the RADIUS server and the identity store (Active Directory, LDAP) are critical for reliable authentication.
PKI (Public Key Infrastructure)
The framework of roles, policies, hardware, and software needed to create, manage, distribute, and revoke digital certificates.
A robust PKI is an absolute prerequisite for deploying EAP-TLS successfully at scale. Without PKI, certificate lifecycle management becomes unmanageable and creates significant operational risk.
MDM (Mobile Device Management)
Software used by IT to monitor, manage, and secure corporate mobile devices, including the ability to push configuration profiles, certificates, and policies silently to enrolled devices.
MDM is critical for EAP-TLS deployments to automate the silent provisioning of client certificates to end-user devices. Microsoft Intune, Jamf, and VMware Workspace ONE are common MDM platforms.
Mutual Authentication
A security process where both parties in a communications link authenticate each other before data is exchanged — as opposed to one-way authentication where only one party is verified.
The defining feature of EAP-TLS. Mutual authentication ensures the client knows it is talking to the legitimate network server, and the server knows it is talking to an authorised client device.
MSCHAPv2 (Microsoft Challenge Handshake Authentication Protocol v2)
A password-based authentication protocol commonly used as the inner authentication method within PEAP tunnels. It uses a challenge-response mechanism to avoid transmitting passwords in plaintext.
MSCHAPv2 hashes can be captured and cracked offline if the PEAP tunnel is compromised by a rogue access point. This is why server certificate validation in PEAP is non-negotiable.
OpenRoaming
A WiFi federation standard that allows users to automatically and securely connect to participating networks across different venues and operators without re-authenticating, using certificate-based authentication.
Purple acts as a free identity provider for OpenRoaming under its Connect licence, enabling venues to offer seamless, secure connectivity that aligns with EAP-TLS certificate authentication principles.
Ejemplos prácticos
A national retail chain with 500 locations needs to secure corporate network access for store managers' tablets and handheld inventory scanners. They currently use a shared WPA2-PSK across all sites. They have Microsoft Intune deployed for device management.
Deploy EAP-TLS. Since the organisation already utilises Microsoft Intune, the heavy lifting of certificate deployment is already solved. Configure Intune to push unique client certificates to all corporate-owned tablets and scanners via a SCEP or PKCS certificate profile. The wireless infrastructure is reconfigured to use 802.1X pointing to a central or cloud-based RADIUS server (such as Microsoft NPS or a cloud RADIUS service). The RADIUS server is configured to accept authentication only from devices presenting certificates issued by the organisation's internal CA. Post-authentication, dynamic VLAN assignment places devices into the appropriate store operations segment.
A large conference centre needs to provide secure WiFi for 3,000 internal staff using their own personal devices (BYOD). They use Google Workspace for corporate identity but do not manage staff personal phones or laptops.
Deploy PEAP (specifically PEAP-MSCHAPv2 or EAP-TTLS/PAP against Google Secure LDAP). The IT team sets up a RADIUS server integrated with Google Workspace Secure LDAP. Staff members connect to the 'Staff_WiFi' SSID using their standard Google Workspace email and password. The IT team provides onboarding documentation — ideally via a captive portal or network onboarding tool — instructing staff to configure their devices to trust the specific RADIUS server certificate and to validate the server's domain name. A separate guest SSID is maintained for event attendees, managed through Purple's Guest WiFi platform for analytics and access control.
Preguntas de práctica
Q1. A university IT department is deploying secure WiFi across campus for 20,000 students. Students bring their own laptops and smartphones running a mix of Windows, macOS, iOS, and Android. The IT director insists on maximum security and proposes EAP-TLS. What is your architectural recommendation?
Sugerencia: Consider the operational overhead of certificate management on unmanaged, personally-owned devices across a heterogeneous device estate.
Ver respuesta modelo
Advise against EAP-TLS for this specific use case. While EAP-TLS offers the highest security, deploying and managing 20,000+ client certificates on unmanaged student devices without an MDM solution will create an insurmountable support burden. Students change devices frequently, and the onboarding process for certificate installation across iOS, Android, Windows, and macOS is complex without MDM automation. Recommend PEAP (or EAP-TTLS) integrated with the university's student directory service. Ensure robust onboarding tools are used to configure student devices to strictly validate the server certificate. Optionally, deploy EAP-TLS on a separate SSID for staff devices that are university-managed, creating a tiered security architecture.
Q2. During a security audit, a penetration tester successfully harvests user credentials from your PEAP-secured wireless network by setting up a rogue access point broadcasting the same SSID. What is the root cause of this vulnerability, and what is the remediation?
Sugerencia: Think about what happens during the TLS tunnel establishment phase in PEAP, and what the client device is — or is not — checking.
Ver respuesta modelo
The root cause is supplicant misconfiguration. The client devices are not configured to strictly validate the RADIUS server's digital certificate. When the rogue AP presented a fraudulent certificate, the client devices blindly trusted it, established the TLS tunnel with the attacker, and transmitted the MSCHAPv2 authentication exchange. The attacker can crack this offline. The remediation is threefold: (1) enforce strict server certificate validation via Group Policy or MDM profiles on all client devices; (2) specify the exact expected RADIUS server domain name in the supplicant configuration to prevent acceptance of certificates from other domains; (3) deploy a Wireless Intrusion Detection System (WIDS) to detect and alert on rogue access points.
Q3. A healthcare provider is upgrading its network to support mobile nursing workstations that access patient records. These workstations are corporate-owned, strictly managed by IT via Microsoft Intune, and the environment must comply with healthcare data protection regulations. Should they deploy PEAP or EAP-TLS?
Sugerencia: Evaluate the regulatory environment, the level of device control, and the sensitivity of the data being accessed.
Ver respuesta modelo
Deploy EAP-TLS without hesitation. The healthcare environment requires strict compliance and maximum security against credential theft — a compromised password in a healthcare network can expose patient records and trigger significant regulatory penalties under GDPR and sector-specific data protection requirements. Because the devices are corporate-owned and strictly managed via Microsoft Intune, deploying client certificates is operationally feasible and can be fully automated. EAP-TLS provides the necessary mutual authentication to ensure only authorised, corporate-managed devices can access the clinical network. Additionally, EAP-TLS simplifies compliance audits — auditors reviewing the network architecture will see a certificate-based, passwordless authentication system that is inherently more defensible than password-based alternatives.
Continúe leyendo esta serie
PSK por dispositivo por fabricante: comparación de iPSK, DPSK, MPSK y PPSK (y compatibilidad con WPA3)
Una comparación exhaustiva de las implementaciones de PSK por dispositivo en Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet y Ubiquiti UniFi. Descubra cómo afecta WPA3-SAE a las estrategias de claves por dispositivo y cuándo implementar modos de transición en lugar de migrar a 802.1X.
¿Qué es la autenticación de dirección MAC? Cuándo usarla y cuándo evitarla
Esta guía de referencia técnica autorizada cubre la autenticación de dirección MAC en entornos empresariales de WiFi: cómo funciona la autenticación MAC basada en RADIUS en la Capa 2, sus vulnerabilidades de seguridad inherentes (incluyendo la suplantación de MAC y el impacto de la aleatorización de MAC a nivel de SO), y los contextos operativos precisos donde sigue siendo una herramienta válida para gestionar dispositivos IoT y sin interfaz. Proporciona una guía de implementación práctica para gerentes de TI y arquitectos de red en hostelería, comercio minorista, atención médica y recintos del sector público, con ejemplos prácticos del mundo real, marcos de decisión y contexto de integración para la plataforma de WiFi para invitados y análisis de Purple.
Cómo configurar WiFi empresarial en iOS y macOS con 802.1X
Esta guía autorizada proporciona a los líderes de TI sénior pasos prácticos para implementar WiFi empresarial 802.1X en dispositivos iOS y macOS. Cubre la autenticación basada en certificados (EAP-TLS), los perfiles de configuración de MDM y la integración de la arquitectura para proteger las redes corporativas al tiempo que apoya las iniciativas BYOD.