EAP-TLS vs. PEAP: Quale protocollo di autenticazione è giusto per la tua rete?
Un confronto tecnico completo dei protocolli di autenticazione EAP-TLS e PEAP, che copre l'architettura di sicurezza, la complessità di implementazione e le implicazioni di conformità. Questa guida fornisce framework decisionali pratici per i leader IT in ambienti di ospitalità, vendita al dettaglio, eventi e settore pubblico che devono selezionare il metodo di autenticazione 802.1X corretto per la loro infrastruttura WiFi aziendale.
Ascolta questa guida
Visualizza trascrizione del podcast
- Riepilogo Esecutivo
- Analisi Tecnica Approfondita: Architettura del Protocollo
- EAP-TLS: Autenticazione Reciproca tramite Certificato
- PEAP: Autenticazione con Password Tunnelizzata
- Guida all'Implementazione: Strategie di Deployment
- Implementazione di EAP-TLS
- Implementazione di PEAP
- Migliori Pratiche e Standard di Settore
- Risoluzione dei Problemi e Mitigazione del Rischio
- ROI e Impatto sul Business

Riepilogo Esecutivo
La selezione del protocollo di autenticazione corretto è una decisione architetturale critica che influisce sia sulla postura di sicurezza che sul sovraccarico operativo. Per i manager IT, gli architetti di rete e i CTO che operano in ambienti complessi — come Ospitalità , Vendita al Dettaglio , stadi e organizzazioni del settore pubblico — la scelta tra EAP-TLS e PEAP spesso determina l'equilibrio tra una sicurezza inattaccabile e la fattibilità dell'implementazione.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security) è ampiamente considerato lo standard d'oro per la sicurezza WiFi aziendale, basandosi sull'autenticazione reciproca basata su certificati. PEAP (Protected Extensible Authentication Protocol), al contrario, incapsula l'autenticazione standard basata su password all'interno di un tunnel TLS crittografato, riducendo significativamente la complessità di implementazione.
Questa guida di riferimento tecnica fornisce un'analisi approfondita, neutrale rispetto al fornitore e architetturale di entrambi i protocolli. Esploriamo le loro meccaniche operative, valutiamo le complessità di implementazione e forniamo raccomandazioni pratiche per garantire che la tua infrastruttura di rete soddisfi i moderni standard di sicurezza — inclusa la conformità PCI DSS e GDPR — mantenendo al contempo una connettività senza interruzioni per i tuoi utenti.
Analisi Tecnica Approfondita: Architettura del Protocollo
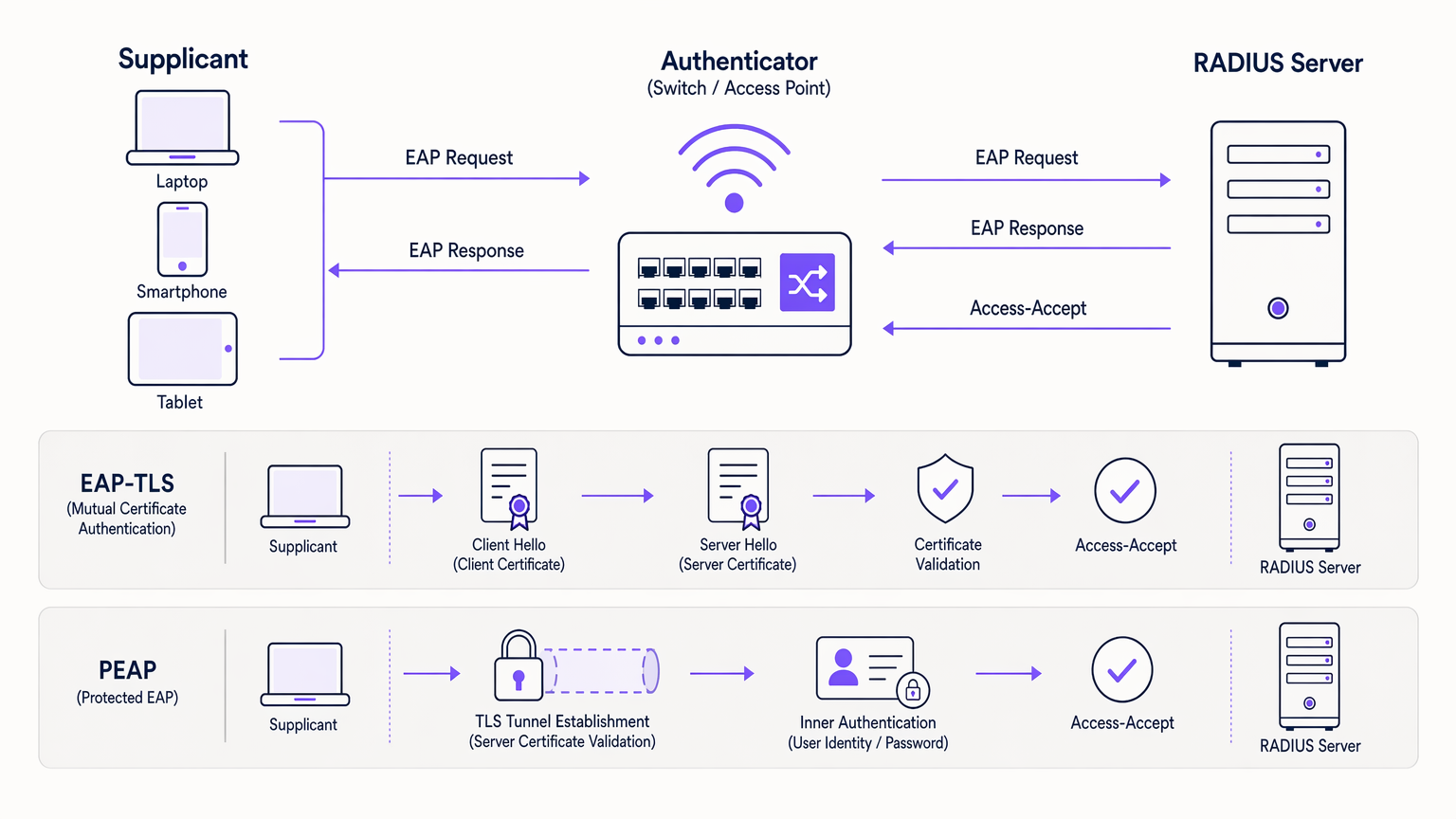
Per prendere una decisione informata, è essenziale comprendere le meccaniche sottostanti di come questi protocolli proteggono il framework di autenticazione 802.1X. Entrambi i protocolli utilizzano un server RADIUS per gestire le richieste di autenticazione, ma i loro metodi di convalida dell'identità differiscono fondamentalmente. Per una comprensione fondamentale dell'infrastruttura RADIUS, fare riferimento alla nostra guida su Cos'è RADIUS? Come i server RADIUS proteggono le reti WiFi .
EAP-TLS: Autenticazione Reciproca tramite Certificato
EAP-TLS opera sul principio dell'autenticazione reciproca. Sia il dispositivo client (supplicante) che il server di autenticazione (RADIUS) devono presentare certificati digitali validi per stabilire una connessione.
L'Handshake: Quando un dispositivo tenta di connettersi, il server RADIUS presenta il suo certificato al client. Il client convalida questo certificato rispetto alle sue Autorità di Certificazione (CA) radice fidate. Una volta verificato il server, il client presenta il proprio certificato unico al server. Se entrambi i certificati sono validi e non sono stati revocati — verificato tramite CRL o OCSP — viene stabilita una sessione TLS sicura e viene concesso l'accesso alla rete.
Questa verifica reciproca rende EAP-TLS altamente resistente al furto di credenziali, agli attacchi a dizionario e agli attacchi Man-in-the-Middle (MitM). Poiché non vengono trasmesse password, le credenziali utente compromesse non possono essere utilizzate per violare la rete.
PEAP: Autenticazione con Password Tunnelizzata
PEAP è stato sviluppato come alternativa più implementabile a EAP-TLS, eliminando la necessità di certificati lato client pur fornendo una sicurezza robusta.
Stabilimento del Tunnel: Il server RADIUS presenta il suo certificato al client. Il client convalida il server, stabilendo un tunnel TLS crittografato. All'interno di questo tunnel sicuro, il client esegue l'autenticazione standard basata su password — tipicamente MSCHAPv2 — contro un provider di identità come Active Directory. Il server RADIUS convalida le credenziali e concede l'accesso.
Sebbene PEAP sia altamente sicuro se configurato correttamente, si basa sul mantenimento di password robuste da parte degli utenti. Fondamentalmente, se il dispositivo di un utente non è configurato per convalidare il certificato del server, un access point non autorizzato può intercettare le credenziali. Questo non è un rischio teorico; è un vettore di attacco ben documentato utilizzato in test di penetrazione reali.
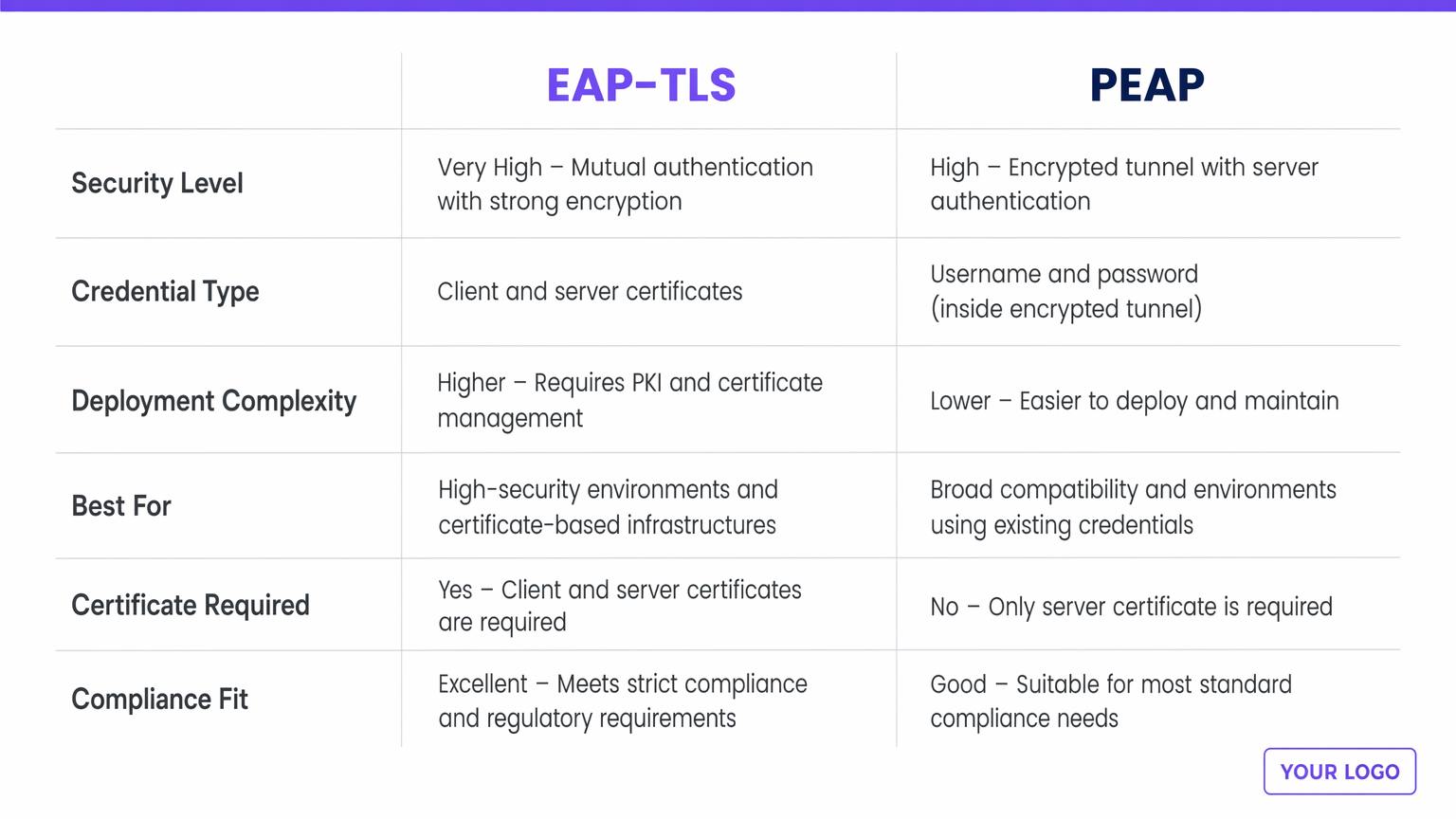
| Dimensione | EAP-TLS | PEAP |
|---|---|---|
| Livello di Sicurezza | Molto Alto — autenticazione reciproca tramite certificato | Alto — tunnel crittografato, solo certificato server |
| Tipo di Credenziale | Certificati digitali client e server | Nome utente e password (all'interno del tunnel TLS) |
| Complessità di Implementazione | Maggiore — richiede PKI e MDM | Minore — si integra con i servizi di directory esistenti |
| Ideale Per | Flotte di dispositivi aziendali, settori regolamentati | Ambienti BYOD, organizzazioni senza PKI |
| Certificato Client Richiesto | Sì | No |
| Idoneità PCI DSS / GDPR | Eccellente — preferito per ambienti ad alta conformità | Buono — conforme quando la convalida del server è applicata |
Guida all'Implementazione: Strategie di Deployment
La principale divergenza tra EAP-TLS e PEAP risiede nella loro complessità di implementazione e gestione del ciclo di vita.
Implementazione di EAP-TLS
L'implementazione di EAP-TLS richiede una robusta Infrastruttura a Chiave Pubblica (PKI) per emettere, gestire e revocare i certificati per ogni dispositivo sulla rete. Le soluzioni di Mobile Device Management (MDM) o Enterprise Mobility Management (EMM) sono praticamente obbligatorie per automatizzare il provisioning dei certificati agli endpoint su larga scala. I team IT devono gestire i cicli di vita dei certificati, gestendo i rinnovi prima della scadenza e garantendo una pronta revoca per i dispositivi smarriti o i dipendenti in uscita. EAP-TLS è più adatto per reti aziendali con dispositivi di proprietà aziendale, ambienti altamente regolamentati come Sanità o finanza, e architetture zero-trust.
Implementazione di PEAP
PEAP è significativamente più facile da implementare perché sfrutta archivi di identità esistenti — Active Directory, LDAP o directory cloud — senza richiedere certificati client. Un server RADIUS con un certificato server valido (idealmente fda una CA pubblica) e l'integrazione con il servizio di directory esistente è sufficiente per iniziare. Il sovraccarico operativo è minimo: gli utenti si autenticano con le loro credenziali aziendali standard. Si applicano le politiche di rotazione delle password, che possono causare un lieve sovraccarico per l'helpdesk quando gli utenti dimenticano di aggiornare i loro profili WiFi dopo un cambio di password. PEAP è più adatto per ambienti BYOD, settori dell'istruzione e organizzazioni senza un'infrastruttura PKI o MDM consolidata.
Migliori Pratiche e Standard di Settore
Indipendentemente dal protocollo scelto, l'adesione agli standard di settore è non negoziabile per mitigare il rischio.
Imporre la Validazione del Certificato del Server: La vulnerabilità più comune nelle implementazioni PEAP è rappresentata da dispositivi client mal configurati che non convalidano il certificato del server RADIUS. Ciò consente agli aggressori di configurare punti di accesso non autorizzati e raccogliere credenziali. L'IT deve utilizzare politiche di gruppo o profili MDM per imporre una rigorosa validazione del server su ogni endpoint.
Implementare la Ridondanza RADIUS: L'autenticazione è un percorso critico. Assicurarsi che l'infrastruttura RADIUS sia altamente disponibile. Le soluzioni RADIUS basate su cloud possono alleviare i singoli punti di guasto on-premise. Le considerazioni architetturali per la resilienza della rete distribuita sono ulteriormente discusse in I Vantaggi Chiave della SD WAN per le Aziende Moderne .
Integrare con Moderni Provider di Identità: Per le sedi aperte al pubblico, sfruttare una robusta piattaforma Guest WiFi che agisce come provider di identità sicuro può semplificare l'accesso mantenendo la sicurezza. La licenza Connect di Purple, ad esempio, fornisce un provider di identità gratuito per servizi come OpenRoaming, colmando il divario tra la sicurezza di livello aziendale e l'onboarding senza interruzioni degli ospiti.
Segmentazione della Rete Post-Autenticazione: Un'autenticazione 802.1X riuscita non dovrebbe concedere accesso illimitato all'intera sottorete aziendale. Utilizzare politiche di assegnazione VLAN dinamiche per posizionare gli utenti in segmenti di rete appropriati con ACL ristrette.
Risoluzione dei Problemi e Mitigazione del Rischio
Quando si gestiscono reti 802.1X, i team IT devono essere preparati per le modalità di guasto comuni.
Scadenza del Certificato (EAP-TLS): Se il certificato della CA o il certificato del server RADIUS scade, tutte le autenticazioni falliranno simultaneamente. Implementare un monitoraggio e un sistema di allerta aggressivi per i periodi di validità dei certificati — impostare avvisi a 90, 30 e 7 giorni prima della scadenza.
Errata Configurazione del Supplicante (PEAP): La mancata validazione del certificato del server è un rischio critico. Verificare regolarmente le configurazioni degli endpoint per assicurarsi che la "Validazione del certificato del server" sia rigorosamente applicata. Includere questo come elemento standard nella checklist di audit di sicurezza.
Problemi di Timeout RADIUS: Un'elevata latenza tra il controller wireless e il server RADIUS, o tra il server RADIUS e Active Directory, può causare timeout EAP e fallimenti di autenticazione. Garantire una connettività robusta e considerare proxy RADIUS locali per siti distribuiti. Questo è particolarmente rilevante per le implementazioni multi-sito Transport e retail.
Attacchi di Punti di Accesso Rogue: Condurre valutazioni periodiche della sicurezza wireless per rilevare AP rogue. I sistemi di rilevamento delle intrusioni wireless (WIDS) integrati nell'infrastruttura dei punti di accesso possono fornire un monitoraggio continuo.
ROI e Impatto sul Business
La decisione tra EAP-TLS e PEAP comporta significative implicazioni aziendali al di là dell'architettura tecnica.
EAP-TLS richiede un CapEx iniziale più elevato per le soluzioni PKI e MDM, insieme a un OpEx continuo per la gestione dei certificati. Tuttavia, offre il più alto livello di mitigazione del rischio contro le violazioni basate su credenziali, che possono causare danni finanziari e reputazionali devastanti. Per le sedi che gestiscono dati sensibili o operano sotto stretta conformità normativa, il ROI di EAP-TLS si realizza attraverso i costi di violazione evitati e audit di conformità semplificati. Una singola violazione basata su credenziali in un ambiente retail o hospitality può costare milioni in risanamento, multe normative e danni al marchio.
PEAP offre un time-to-value più rapido e costi di implementazione inferiori. È altamente efficace per ambienti in cui l'obiettivo primario è un accesso sicuro e crittografato senza il sovraccarico della gestione dei dispositivi. Integrando PEAP con una soluzione completa di WiFi Analytics , le sedi possono gestire in modo sicuro l'accesso estraendo al contempo preziose informazioni operative dai dati di utilizzo della rete — collegando l'infrastruttura di autenticazione a risultati aziendali misurabili come l'analisi del tempo di permanenza, i modelli di affluenza e i tassi di visitatori di ritorno.
Definizioni chiave
EAP (Extensible Authentication Protocol)
An authentication framework defined in IEEE 802.1X that provides the transport mechanism for various authentication methods over network access infrastructure.
EAP is the umbrella framework; EAP-TLS and PEAP are specific methods that run within it. IT teams encounter EAP when configuring RADIUS policies and wireless supplicant profiles.
Supplicant
The client device — laptop, smartphone, scanner, or IoT device — that initiates the authentication request to join the network.
IT teams must ensure supplicants are correctly configured, particularly regarding certificate validation, to prevent Man-in-the-Middle attacks. Supplicant configuration is the most common source of PEAP vulnerabilities.
Authenticator
The network device — typically a wireless access point or managed switch — that blocks all traffic from the supplicant until the RADIUS server confirms successful authentication.
The authenticator acts as the gatekeeper, passing EAP messages between the supplicant and the RADIUS server without processing the authentication itself.
RADIUS Server
Remote Authentication Dial-In User Service. The centralised server that receives authentication requests from the authenticator, validates credentials against an identity store, and returns an Access-Accept or Access-Reject response.
The RADIUS server is the brain of the 802.1X architecture. High availability and low latency between the RADIUS server and the identity store (Active Directory, LDAP) are critical for reliable authentication.
PKI (Public Key Infrastructure)
The framework of roles, policies, hardware, and software needed to create, manage, distribute, and revoke digital certificates.
A robust PKI is an absolute prerequisite for deploying EAP-TLS successfully at scale. Without PKI, certificate lifecycle management becomes unmanageable and creates significant operational risk.
MDM (Mobile Device Management)
Software used by IT to monitor, manage, and secure corporate mobile devices, including the ability to push configuration profiles, certificates, and policies silently to enrolled devices.
MDM is critical for EAP-TLS deployments to automate the silent provisioning of client certificates to end-user devices. Microsoft Intune, Jamf, and VMware Workspace ONE are common MDM platforms.
Mutual Authentication
A security process where both parties in a communications link authenticate each other before data is exchanged — as opposed to one-way authentication where only one party is verified.
The defining feature of EAP-TLS. Mutual authentication ensures the client knows it is talking to the legitimate network server, and the server knows it is talking to an authorised client device.
MSCHAPv2 (Microsoft Challenge Handshake Authentication Protocol v2)
A password-based authentication protocol commonly used as the inner authentication method within PEAP tunnels. It uses a challenge-response mechanism to avoid transmitting passwords in plaintext.
MSCHAPv2 hashes can be captured and cracked offline if the PEAP tunnel is compromised by a rogue access point. This is why server certificate validation in PEAP is non-negotiable.
OpenRoaming
A WiFi federation standard that allows users to automatically and securely connect to participating networks across different venues and operators without re-authenticating, using certificate-based authentication.
Purple acts as a free identity provider for OpenRoaming under its Connect licence, enabling venues to offer seamless, secure connectivity that aligns with EAP-TLS certificate authentication principles.
Esempi pratici
A national retail chain with 500 locations needs to secure corporate network access for store managers' tablets and handheld inventory scanners. They currently use a shared WPA2-PSK across all sites. They have Microsoft Intune deployed for device management.
Deploy EAP-TLS. Since the organisation already utilises Microsoft Intune, the heavy lifting of certificate deployment is already solved. Configure Intune to push unique client certificates to all corporate-owned tablets and scanners via a SCEP or PKCS certificate profile. The wireless infrastructure is reconfigured to use 802.1X pointing to a central or cloud-based RADIUS server (such as Microsoft NPS or a cloud RADIUS service). The RADIUS server is configured to accept authentication only from devices presenting certificates issued by the organisation's internal CA. Post-authentication, dynamic VLAN assignment places devices into the appropriate store operations segment.
A large conference centre needs to provide secure WiFi for 3,000 internal staff using their own personal devices (BYOD). They use Google Workspace for corporate identity but do not manage staff personal phones or laptops.
Deploy PEAP (specifically PEAP-MSCHAPv2 or EAP-TTLS/PAP against Google Secure LDAP). The IT team sets up a RADIUS server integrated with Google Workspace Secure LDAP. Staff members connect to the 'Staff_WiFi' SSID using their standard Google Workspace email and password. The IT team provides onboarding documentation — ideally via a captive portal or network onboarding tool — instructing staff to configure their devices to trust the specific RADIUS server certificate and to validate the server's domain name. A separate guest SSID is maintained for event attendees, managed through Purple's Guest WiFi platform for analytics and access control.
Domande di esercitazione
Q1. A university IT department is deploying secure WiFi across campus for 20,000 students. Students bring their own laptops and smartphones running a mix of Windows, macOS, iOS, and Android. The IT director insists on maximum security and proposes EAP-TLS. What is your architectural recommendation?
Suggerimento: Consider the operational overhead of certificate management on unmanaged, personally-owned devices across a heterogeneous device estate.
Visualizza risposta modello
Advise against EAP-TLS for this specific use case. While EAP-TLS offers the highest security, deploying and managing 20,000+ client certificates on unmanaged student devices without an MDM solution will create an insurmountable support burden. Students change devices frequently, and the onboarding process for certificate installation across iOS, Android, Windows, and macOS is complex without MDM automation. Recommend PEAP (or EAP-TTLS) integrated with the university's student directory service. Ensure robust onboarding tools are used to configure student devices to strictly validate the server certificate. Optionally, deploy EAP-TLS on a separate SSID for staff devices that are university-managed, creating a tiered security architecture.
Q2. During a security audit, a penetration tester successfully harvests user credentials from your PEAP-secured wireless network by setting up a rogue access point broadcasting the same SSID. What is the root cause of this vulnerability, and what is the remediation?
Suggerimento: Think about what happens during the TLS tunnel establishment phase in PEAP, and what the client device is — or is not — checking.
Visualizza risposta modello
The root cause is supplicant misconfiguration. The client devices are not configured to strictly validate the RADIUS server's digital certificate. When the rogue AP presented a fraudulent certificate, the client devices blindly trusted it, established the TLS tunnel with the attacker, and transmitted the MSCHAPv2 authentication exchange. The attacker can crack this offline. The remediation is threefold: (1) enforce strict server certificate validation via Group Policy or MDM profiles on all client devices; (2) specify the exact expected RADIUS server domain name in the supplicant configuration to prevent acceptance of certificates from other domains; (3) deploy a Wireless Intrusion Detection System (WIDS) to detect and alert on rogue access points.
Q3. A healthcare provider is upgrading its network to support mobile nursing workstations that access patient records. These workstations are corporate-owned, strictly managed by IT via Microsoft Intune, and the environment must comply with healthcare data protection regulations. Should they deploy PEAP or EAP-TLS?
Suggerimento: Evaluate the regulatory environment, the level of device control, and the sensitivity of the data being accessed.
Visualizza risposta modello
Deploy EAP-TLS without hesitation. The healthcare environment requires strict compliance and maximum security against credential theft — a compromised password in a healthcare network can expose patient records and trigger significant regulatory penalties under GDPR and sector-specific data protection requirements. Because the devices are corporate-owned and strictly managed via Microsoft Intune, deploying client certificates is operationally feasible and can be fully automated. EAP-TLS provides the necessary mutual authentication to ensure only authorised, corporate-managed devices can access the clinical network. Additionally, EAP-TLS simplifies compliance audits — auditors reviewing the network architecture will see a certificate-based, passwordless authentication system that is inherently more defensible than password-based alternatives.
Continua a leggere questa serie
Cos'è l'autenticazione tramite indirizzo MAC? Quando usarla e quando evitarla
Questa guida tecnica di riferimento autorevole copre l'autenticazione tramite indirizzo MAC negli ambienti WiFi aziendali — come funziona l'autenticazione MAC basata su RADIUS al Livello 2, le sue vulnerabilità di sicurezza intrinseche (inclusi lo spoofing MAC e l'impatto della randomizzazione MAC a livello di OS), e i precisi contesti operativi in cui rimane uno strumento valido per la gestione di dispositivi IoT e headless. Fornisce indicazioni pratiche per l'implementazione a responsabili IT e architetti di rete in strutture ricettive, retail, sanitarie e del settore pubblico, con esempi pratici, framework decisionali e contesto di integrazione per la piattaforma di guest WiFi e analisi di Purple.
Come configurare il WiFi aziendale su iOS e macOS con 802.1X
Questa guida autorevole fornisce ai leader IT senior passaggi pratici per l'implementazione del WiFi aziendale 802.1X su dispositivi iOS e macOS. Copre l'autenticazione basata su certificati (EAP-TLS), i profili di configurazione MDM e l'integrazione dell'architettura per proteggere le reti aziendali supportando al contempo le iniziative BYOD.
Come configurare il WiFi aziendale sui dispositivi Android con EAP-TLS
Questa guida di riferimento tecnico fornisce ai leader IT senior un progetto completo per la distribuzione dell'autenticazione 802.1X EAP-TLS sui dispositivi Android. Copre i meccanismi architetturali, le strategie di implementazione manuale e basate su MDM e le metodologie di risoluzione dei problemi necessarie per proteggere le reti wireless aziendali.