EAP-TLS vs. PEAP: Which Authentication Protocol Is Right for Your Network?
A comprehensive technical comparison of EAP-TLS and PEAP authentication protocols, covering security architecture, deployment complexity, and compliance implications. This guide provides actionable decision frameworks for IT leaders in hospitality, retail, events, and public-sector environments who need to select the right 802.1X authentication method for their enterprise WiFi infrastructure.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: Protocol Architecture
- EAP-TLS: Mutual Certificate Authentication
- PEAP: Tunnelled Password Authentication
- Implementation Guide: Deployment Strategies
- Deploying EAP-TLS
- Deploying PEAP
- Best Practices and Industry Standards
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
Selecting the right authentication protocol is a critical architectural decision that impacts both security posture and operational overhead. For IT managers, network architects, and CTOs operating in complex environments — such as Hospitality , Retail , stadiums, and public-sector organisations — the choice between EAP-TLS and PEAP often dictates the balance between ironclad security and deployment feasibility.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security) is widely regarded as the gold standard for enterprise WiFi security, relying on mutual certificate-based authentication. PEAP (Protected Extensible Authentication Protocol), conversely, encapsulates standard password-based authentication within an encrypted TLS tunnel, significantly reducing deployment complexity.
This technical reference guide provides a vendor-neutral, architectural deep-dive into both protocols. We explore their operational mechanics, evaluate deployment complexities, and provide actionable recommendations to ensure your network infrastructure meets modern security standards — including PCI DSS and GDPR compliance — while maintaining seamless connectivity for your users.
Technical Deep-Dive: Protocol Architecture
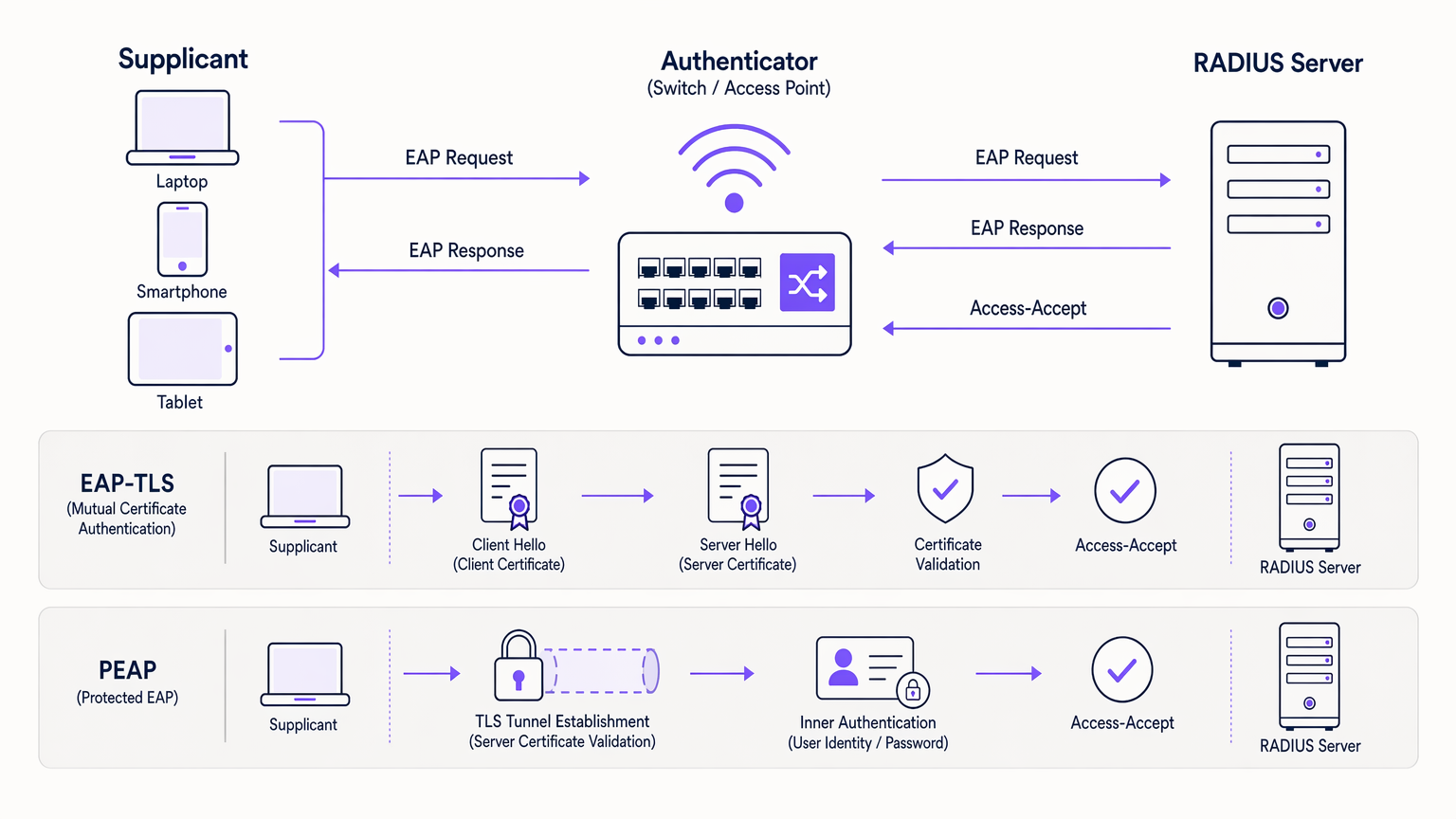
To make an informed decision, it is essential to understand the underlying mechanics of how these protocols secure the 802.1X authentication framework. Both protocols utilise a RADIUS server to handle authentication requests, but their methods of validating identity differ fundamentally. For a foundational understanding of RADIUS infrastructure, refer to our guide on What Is RADIUS? How RADIUS Servers Secure WiFi Networks .
EAP-TLS: Mutual Certificate Authentication
EAP-TLS operates on the principle of mutual authentication. Both the client device (supplicant) and the authentication server (RADIUS) must present valid digital certificates to establish a connection.
The Handshake: When a device attempts to connect, the RADIUS server presents its certificate to the client. The client validates this certificate against its trusted Root Certificate Authorities (CAs). Once the server is verified, the client presents its own unique certificate back to the server. If both certificates are valid and have not been revoked — checked via CRL or OCSP — a secure TLS session is established and network access is granted.
This mutual verification makes EAP-TLS highly resistant to credential theft, dictionary attacks, and Man-in-the-Middle (MitM) attacks. Because no passwords are transmitted, compromised user credentials cannot be used to breach the network.
PEAP: Tunnelled Password Authentication
PEAP was developed as a more deployable alternative to EAP-TLS, eliminating the need for client-side certificates while still providing robust security.
Tunnel Establishment: The RADIUS server presents its certificate to the client. The client validates the server, establishing an encrypted TLS tunnel. Within this secure tunnel, the client performs standard password-based authentication — typically MSCHAPv2 — against an identity provider such as Active Directory. The RADIUS server validates the credentials and grants access.
While PEAP is highly secure when configured correctly, it relies on users maintaining strong passwords. Critically, if a user's device is not configured to validate the server certificate, a rogue access point can intercept credentials. This is not a theoretical risk; it is a well-documented attack vector used in real-world penetration tests.
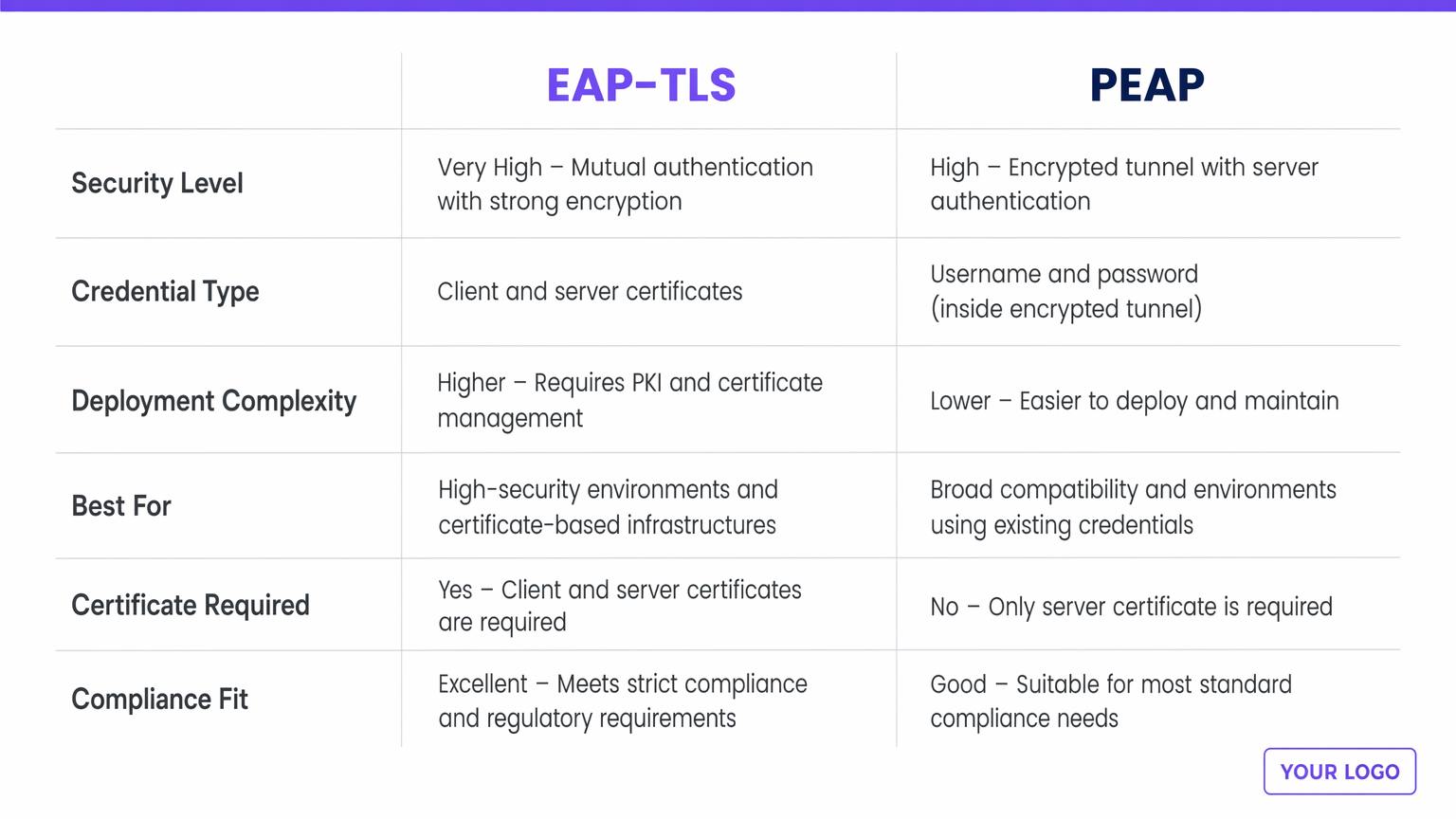
| Dimension | EAP-TLS | PEAP |
|---|---|---|
| Security Level | Very High — mutual certificate authentication | High — encrypted tunnel, server certificate only |
| Credential Type | Client and server digital certificates | Username and password (inside TLS tunnel) |
| Deployment Complexity | Higher — requires PKI and MDM | Lower — integrates with existing directory services |
| Best For | Corporate-owned device fleets, regulated industries | BYOD environments, organisations without PKI |
| Client Certificate Required | Yes | No |
| PCI DSS / GDPR Fit | Excellent — preferred for high-compliance environments | Good — compliant when server validation is enforced |
Implementation Guide: Deployment Strategies
The primary divergence between EAP-TLS and PEAP lies in their deployment complexity and lifecycle management.
Deploying EAP-TLS
Implementing EAP-TLS requires a robust Public Key Infrastructure (PKI) to issue, manage, and revoke certificates for every device on the network. Mobile Device Management (MDM) or Enterprise Mobility Management (EMM) solutions are practically mandatory to automate certificate provisioning to endpoints at scale. IT teams must manage certificate lifecycles, handling renewals before expiry and ensuring prompt revocation for lost devices or departing employees. EAP-TLS is best suited to corporate networks with corporate-owned devices, highly regulated environments such as Healthcare or finance, and zero-trust architectures.
Deploying PEAP
PEAP is significantly easier to deploy because it leverages existing identity stores — Active Directory, LDAP, or cloud directories — without requiring client certificates. A RADIUS server with a valid server certificate (ideally from a public CA) and integration with your existing directory service is sufficient to get started. Operational overhead is minimal: users authenticate with their standard corporate credentials. Password rotation policies apply, which can cause minor helpdesk overhead when users forget to update their WiFi profiles after a password change. PEAP is best suited to BYOD environments, education sectors, and organisations without an established PKI or MDM infrastructure.
Best Practices and Industry Standards
Regardless of the protocol chosen, adherence to industry standards is non-negotiable for mitigating risk.
Enforce Server Certificate Validation: The most common vulnerability in PEAP deployments is misconfigured client devices that do not validate the RADIUS server's certificate. This allows attackers to set up rogue access points and harvest credentials. IT must use group policies or MDM profiles to enforce strict server validation on every endpoint.
Implement RADIUS Redundancy: Authentication is a critical path. Ensure your RADIUS infrastructure is highly available. Cloud-based RADIUS solutions can alleviate on-premises single points of failure. The architectural considerations for distributed network resilience are discussed further in The Core SD WAN Benefits for Modern Businesses .
Integrate with Modern Identity Providers: For public-facing venues, leveraging a robust Guest WiFi platform that acts as a secure identity provider can streamline access while maintaining security. Purple's Connect licence, for example, provides a free identity provider for services like OpenRoaming, bridging the gap between enterprise-grade security and seamless guest onboarding.
Network Segmentation Post-Authentication: A successful 802.1X authentication should not grant unrestricted access to the entire corporate subnet. Use dynamic VLAN assignment policies to place users in appropriate network segments with restricted ACLs.
Troubleshooting & Risk Mitigation
When managing 802.1X networks, IT teams must be prepared for common failure modes.
Certificate Expiry (EAP-TLS): If the CA certificate or the RADIUS server certificate expires, all authentication will fail simultaneously. Implement aggressive monitoring and alerting for certificate validity periods — set alerts at 90, 30, and 7 days before expiry.
Supplicant Misconfiguration (PEAP): Failing to validate the server certificate is a critical risk. Regularly audit endpoint configurations to ensure "Validate server certificate" is strictly enforced. Include this as a standard item in your security audit checklist.
RADIUS Timeout Issues: High latency between the wireless controller and the RADIUS server, or between the RADIUS server and Active Directory, can cause EAP timeouts and authentication failures. Ensure robust connectivity and consider local RADIUS proxies for distributed sites. This is particularly relevant for multi-site Transport and retail deployments.
Rogue Access Point Attacks: Conduct periodic wireless security assessments to detect rogue APs. Wireless intrusion detection systems (WIDS) integrated into your access point infrastructure can provide continuous monitoring.
ROI & Business Impact
The decision between EAP-TLS and PEAP carries significant business implications beyond the technical architecture.
EAP-TLS requires a higher initial CapEx for PKI and MDM solutions, alongside ongoing OpEx for certificate management. However, it provides the highest level of risk mitigation against credential-based breaches, which can result in devastating financial and reputational damage. For venues handling sensitive data or operating under strict regulatory compliance, the ROI of EAP-TLS is realised through avoided breach costs and streamlined compliance audits. A single credential-based breach in a retail or hospitality environment can cost millions in remediation, regulatory fines, and brand damage.
PEAP offers faster time-to-value and lower implementation costs. It is highly effective for environments where the primary goal is secure, encrypted access without the overhead of device management. By integrating PEAP with a comprehensive WiFi Analytics solution, venues can securely manage access while extracting valuable operational insights from network usage data — connecting authentication infrastructure to measurable business outcomes such as dwell time analysis, footfall patterns, and return visitor rates.
Key Definitions
EAP (Extensible Authentication Protocol)
An authentication framework defined in IEEE 802.1X that provides the transport mechanism for various authentication methods over network access infrastructure.
EAP is the umbrella framework; EAP-TLS and PEAP are specific methods that run within it. IT teams encounter EAP when configuring RADIUS policies and wireless supplicant profiles.
Supplicant
The client device — laptop, smartphone, scanner, or IoT device — that initiates the authentication request to join the network.
IT teams must ensure supplicants are correctly configured, particularly regarding certificate validation, to prevent Man-in-the-Middle attacks. Supplicant configuration is the most common source of PEAP vulnerabilities.
Authenticator
The network device — typically a wireless access point or managed switch — that blocks all traffic from the supplicant until the RADIUS server confirms successful authentication.
The authenticator acts as the gatekeeper, passing EAP messages between the supplicant and the RADIUS server without processing the authentication itself.
RADIUS Server
Remote Authentication Dial-In User Service. The centralised server that receives authentication requests from the authenticator, validates credentials against an identity store, and returns an Access-Accept or Access-Reject response.
The RADIUS server is the brain of the 802.1X architecture. High availability and low latency between the RADIUS server and the identity store (Active Directory, LDAP) are critical for reliable authentication.
PKI (Public Key Infrastructure)
The framework of roles, policies, hardware, and software needed to create, manage, distribute, and revoke digital certificates.
A robust PKI is an absolute prerequisite for deploying EAP-TLS successfully at scale. Without PKI, certificate lifecycle management becomes unmanageable and creates significant operational risk.
MDM (Mobile Device Management)
Software used by IT to monitor, manage, and secure corporate mobile devices, including the ability to push configuration profiles, certificates, and policies silently to enrolled devices.
MDM is critical for EAP-TLS deployments to automate the silent provisioning of client certificates to end-user devices. Microsoft Intune, Jamf, and VMware Workspace ONE are common MDM platforms.
Mutual Authentication
A security process where both parties in a communications link authenticate each other before data is exchanged — as opposed to one-way authentication where only one party is verified.
The defining feature of EAP-TLS. Mutual authentication ensures the client knows it is talking to the legitimate network server, and the server knows it is talking to an authorised client device.
MSCHAPv2 (Microsoft Challenge Handshake Authentication Protocol v2)
A password-based authentication protocol commonly used as the inner authentication method within PEAP tunnels. It uses a challenge-response mechanism to avoid transmitting passwords in plaintext.
MSCHAPv2 hashes can be captured and cracked offline if the PEAP tunnel is compromised by a rogue access point. This is why server certificate validation in PEAP is non-negotiable.
OpenRoaming
A WiFi federation standard that allows users to automatically and securely connect to participating networks across different venues and operators without re-authenticating, using certificate-based authentication.
Purple acts as a free identity provider for OpenRoaming under its Connect licence, enabling venues to offer seamless, secure connectivity that aligns with EAP-TLS certificate authentication principles.
Worked Examples
A national retail chain with 500 locations needs to secure corporate network access for store managers' tablets and handheld inventory scanners. They currently use a shared WPA2-PSK across all sites. They have Microsoft Intune deployed for device management.
Deploy EAP-TLS. Since the organisation already utilises Microsoft Intune, the heavy lifting of certificate deployment is already solved. Configure Intune to push unique client certificates to all corporate-owned tablets and scanners via a SCEP or PKCS certificate profile. The wireless infrastructure is reconfigured to use 802.1X pointing to a central or cloud-based RADIUS server (such as Microsoft NPS or a cloud RADIUS service). The RADIUS server is configured to accept authentication only from devices presenting certificates issued by the organisation's internal CA. Post-authentication, dynamic VLAN assignment places devices into the appropriate store operations segment.
A large conference centre needs to provide secure WiFi for 3,000 internal staff using their own personal devices (BYOD). They use Google Workspace for corporate identity but do not manage staff personal phones or laptops.
Deploy PEAP (specifically PEAP-MSCHAPv2 or EAP-TTLS/PAP against Google Secure LDAP). The IT team sets up a RADIUS server integrated with Google Workspace Secure LDAP. Staff members connect to the 'Staff_WiFi' SSID using their standard Google Workspace email and password. The IT team provides onboarding documentation — ideally via a captive portal or network onboarding tool — instructing staff to configure their devices to trust the specific RADIUS server certificate and to validate the server's domain name. A separate guest SSID is maintained for event attendees, managed through Purple's Guest WiFi platform for analytics and access control.
Practice Questions
Q1. A university IT department is deploying secure WiFi across campus for 20,000 students. Students bring their own laptops and smartphones running a mix of Windows, macOS, iOS, and Android. The IT director insists on maximum security and proposes EAP-TLS. What is your architectural recommendation?
Hint: Consider the operational overhead of certificate management on unmanaged, personally-owned devices across a heterogeneous device estate.
View model answer
Advise against EAP-TLS for this specific use case. While EAP-TLS offers the highest security, deploying and managing 20,000+ client certificates on unmanaged student devices without an MDM solution will create an insurmountable support burden. Students change devices frequently, and the onboarding process for certificate installation across iOS, Android, Windows, and macOS is complex without MDM automation. Recommend PEAP (or EAP-TTLS) integrated with the university's student directory service. Ensure robust onboarding tools are used to configure student devices to strictly validate the server certificate. Optionally, deploy EAP-TLS on a separate SSID for staff devices that are university-managed, creating a tiered security architecture.
Q2. During a security audit, a penetration tester successfully harvests user credentials from your PEAP-secured wireless network by setting up a rogue access point broadcasting the same SSID. What is the root cause of this vulnerability, and what is the remediation?
Hint: Think about what happens during the TLS tunnel establishment phase in PEAP, and what the client device is — or is not — checking.
View model answer
The root cause is supplicant misconfiguration. The client devices are not configured to strictly validate the RADIUS server's digital certificate. When the rogue AP presented a fraudulent certificate, the client devices blindly trusted it, established the TLS tunnel with the attacker, and transmitted the MSCHAPv2 authentication exchange. The attacker can crack this offline. The remediation is threefold: (1) enforce strict server certificate validation via Group Policy or MDM profiles on all client devices; (2) specify the exact expected RADIUS server domain name in the supplicant configuration to prevent acceptance of certificates from other domains; (3) deploy a Wireless Intrusion Detection System (WIDS) to detect and alert on rogue access points.
Q3. A healthcare provider is upgrading its network to support mobile nursing workstations that access patient records. These workstations are corporate-owned, strictly managed by IT via Microsoft Intune, and the environment must comply with healthcare data protection regulations. Should they deploy PEAP or EAP-TLS?
Hint: Evaluate the regulatory environment, the level of device control, and the sensitivity of the data being accessed.
View model answer
Deploy EAP-TLS without hesitation. The healthcare environment requires strict compliance and maximum security against credential theft — a compromised password in a healthcare network can expose patient records and trigger significant regulatory penalties under GDPR and sector-specific data protection requirements. Because the devices are corporate-owned and strictly managed via Microsoft Intune, deploying client certificates is operationally feasible and can be fully automated. EAP-TLS provides the necessary mutual authentication to ensure only authorised, corporate-managed devices can access the clinical network. Additionally, EAP-TLS simplifies compliance audits — auditors reviewing the network architecture will see a certificate-based, passwordless authentication system that is inherently more defensible than password-based alternatives.
Continue reading in this series
Per-Device PSK by Vendor: iPSK, DPSK, MPSK and PPSK Compared (and WPA3 Support)
A comprehensive comparison of per-device PSK implementations across Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet, and Ubiquiti UniFi. Learn how WPA3-SAE impacts per-device key strategies and when to deploy transition modes versus moving to 802.1X.
Per-Device PSK by Vendor: iPSK, DPSK, MPSK and PPSK Compared (and WPA3 Support)
A comprehensive comparison of per-device PSK implementations across Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet, and Ubiquiti UniFi. Learn how WPA3-SAE impacts per-device key strategies and when to deploy transition modes versus moving to 802.1X.
Captive Portal Authentication Methods Compared
This authoritative technical reference guide evaluates the architectural, operational, and compliance trade-offs of five core captive portal authentication methods. It provides network architects, IT directors, and marketing managers with the quantitative data and decision frameworks required to balance guest onboarding friction with data-collection requirements across enterprise venues.