GDPR and WiFi: Um Guia de Conformidade para Empresas
Um guia abrangente para líderes de TI e operadores de locais sobre como gerenciar a conformidade com a GDPR em redes WiFi corporativas. Ele aborda o mapeamento de dados, bases legais para processamento, design de consentimento de página inicial e políticas de retenção automatizadas.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: Quais Dados Você Está Realmente Coletando?
- Base Legal para Processamento
- Arquitetura da Página Inicial e Design de Consentimento
- Guia de Implementação: Uma Abordagem Passo a Passo
- Passo 1: Mapeamento de Dados e ROPA
- Passo 2: Configurar o Captive Portal
- Passo 3: Implementar Retenção Automatizada de Dados
- Passo 4: Executar Acordos de Processamento de Dados (DPAs)
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios

Resumo Executivo
Para CTOs, gerentes de TI e diretores de operações de locais, o WiFi para convidados é uma faca de dois gumes. Por um lado, é uma utilidade crítica para a experiência do convidado e um motor poderoso para WiFi Analytics . Por outro, representa uma área de superfície significativa para risco de proteção de dados. Se você opera Guest WiFi em Varejo , Hotelaria ou Transporte , você está processando dados pessoais sob o Regulamento Geral de Proteção de Dados (GDPR).
Este guia descomplica o jargão jurídico para fornecer uma estrutura prática e técnica para a conformidade. Abordamos os pontos de dados específicos capturados pela infraestrutura de rede, como projetar captive portals que atendam ao limite para consentimento explícito e como implementar políticas de retenção automatizadas que protejam sua organização da fiscalização regulatória, ao mesmo tempo em que permitem insights de negócios valiosos.
Ouça nosso briefing executivo de 10 minutos:
Análise Técnica Aprofundada: Quais Dados Você Está Realmente Coletando?
Um equívoco comum entre arquitetos de rede é que endereços MAC e endereços IP são identificadores puramente técnicos. Sob a GDPR, se um ponto de dados pode ser usado — direta ou indiretamente — para identificar uma pessoa natural, ele constitui dados pessoais.
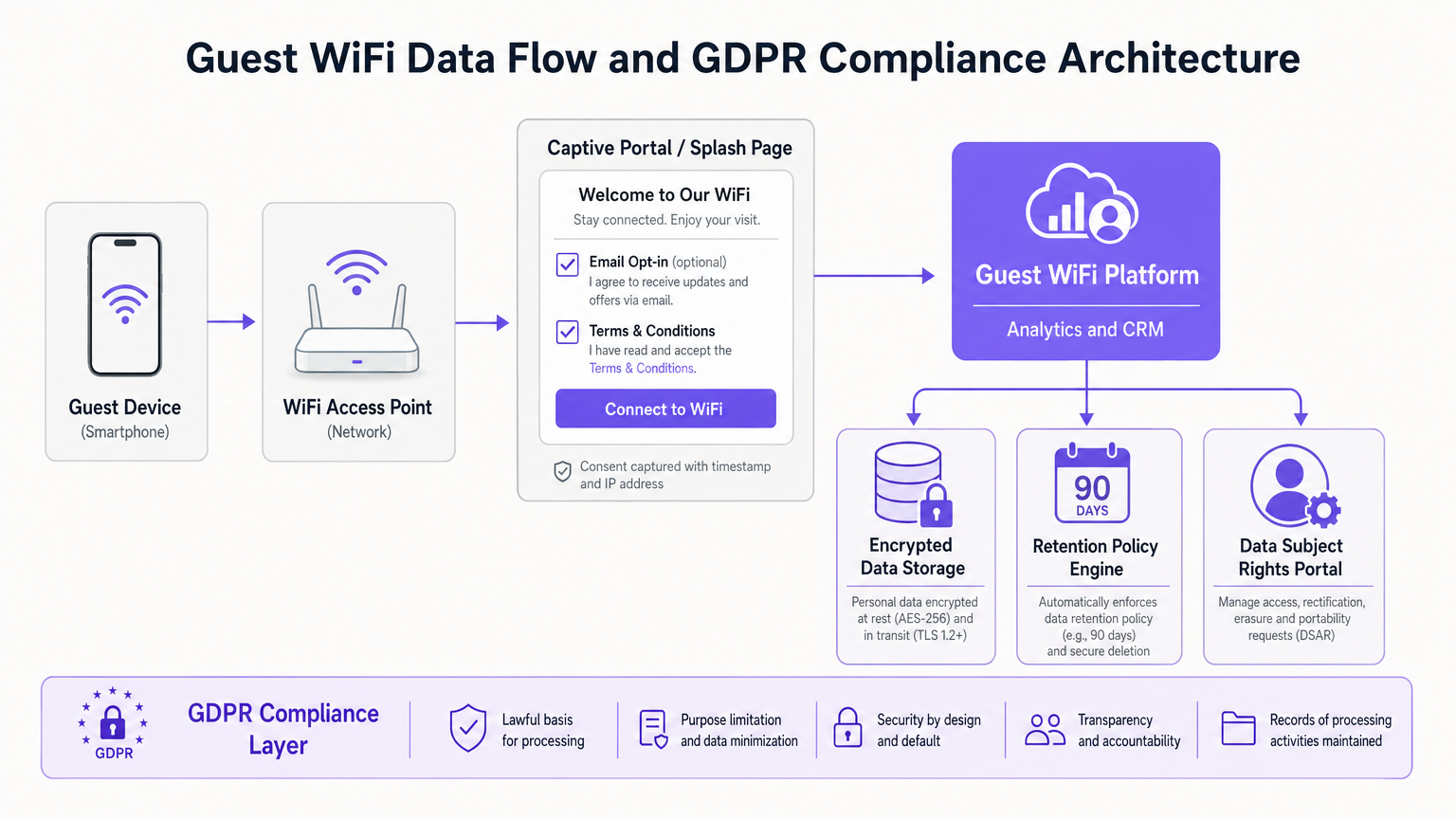
Quando um dispositivo se associa a um Ponto de Acesso WiFi, o controlador de rede registra o endereço MAC. Quando o usuário passa pelo captive portal, um endereço IP é atribuído a ele. Ambos são dados pessoais. Se sua página inicial inclui um formulário de registro, você também está capturando informações explicitamente identificáveis, como nomes, endereços de e-mail e, potencialmente, dados demográficos.
Base Legal para Processamento
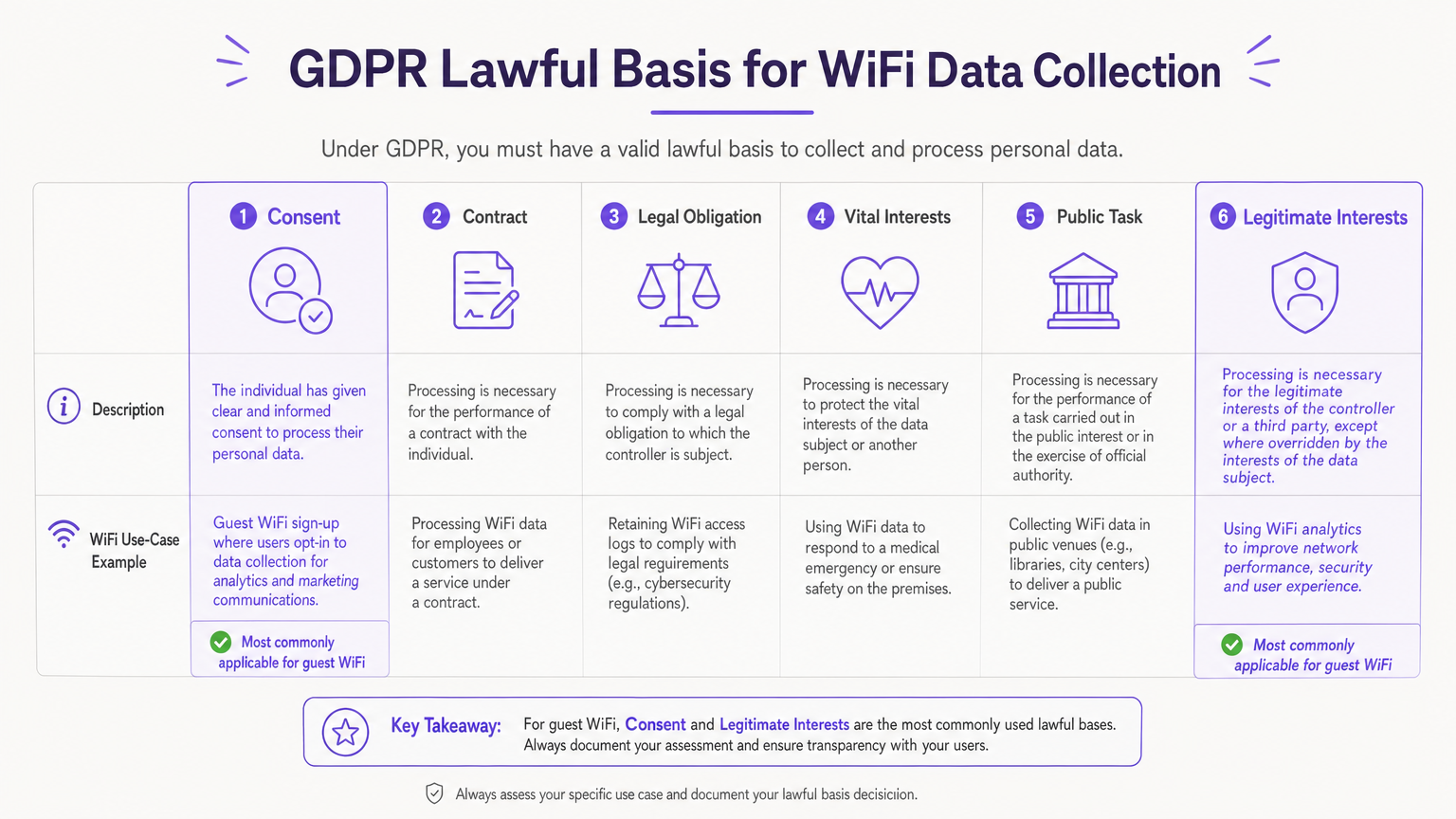
O Artigo 6 da GDPR exige uma base legal para o processamento de quaisquer dados pessoais. Para implantações de WiFi para convidados, duas bases são principalmente relevantes:
- Interesses Legítimos: Frequentemente usado para processar dados subjacentes de conexão de rede (endereços MAC, logs de sessão) necessários para fornecer um serviço seguro e funcional. Isso requer uma Avaliação de Interesses Legítimos (LIA) documentada.
- Consentimento: A base obrigatória para o processamento de dados para fins de marketing direto. O consentimento deve ser dado livremente, ser específico, informado e inequívoco.
Arquitetura da Página Inicial e Design de Consentimento
A página inicial é a interface crítica para a conformidade com a GDPR. Uma arquitetura em conformidade deve separar a aceitação dos termos e condições do consentimento de marketing.
- Sem Caixas Pré-marcadas: As opções de marketing devem exigir uma ação deliberada do usuário.
- Consentimento Desagregado: Você não pode condicionar o acesso à rede à concordância em receber comunicações de marketing.
- Granularidade: Se você está coletando dados para múltiplos propósitos (por exemplo, marketing por e-mail, marketing por SMS, compartilhamento com terceiros), cada um requer um mecanismo de consentimento separado.
- Transparência: Um link claro para a Política de Privacidade da sua organização deve estar presente antes que o usuário se conecte.
Guia de Implementação: Uma Abordagem Passo a Passo
A implantação de uma solução de WiFi para convidados em conformidade exige ir além das políticas estáticas para a aplicação técnica.
Passo 1: Mapeamento de Dados e ROPA
Antes de configurar qualquer sistema, mapeie o fluxo de dados. Documente exatamente quais dados seus pontos de acesso, controladores e plataformas de análise coletam. Isso forma seu Registro de Atividades de Processamento (ROPA) sob o Artigo 30.
Passo 2: Configurar o Captive Portal
Implemente uma página inicial que adere estritamente aos princípios de design de consentimento descritos acima. Garanta que a plataforma capture um carimbo de data/hora verificável e endereço IP junto com qualquer consentimento dado, criando um rastro de auditoria imutável.
Passo 3: Implementar Retenção Automatizada de Dados
O Artigo 5(1)(e) dita que os dados não devem ser mantidos por mais tempo do que o necessário. Processos de exclusão manual são propensos a falhas. Configure sua plataforma Guest WiFi para purgar automaticamente logs de rede (por exemplo, após 90 dias para fins de segurança) e contatos de marketing não engajados de acordo com seu cronograma de retenção definido.
Passo 4: Executar Acordos de Processamento de Dados (DPAs)
Se você utiliza um fornecedor terceirizado para análise de WiFi ou gerenciamento de captive portal, ele atua como um Processador de Dados. O Artigo 28 exige um DPA assinado detalhando o escopo, a natureza e a finalidade do processamento, bem como as medidas de segurança que o processador deve implementar.
Melhores Práticas
- Anonimização e Agregação: Ao utilizar WiFi Analytics para análise de fluxo de pessoas ou tempo de permanência, garanta que os dados sejam anonimizados ou agregados para mitigar riscos de privacidade.
- Auditorias Regulares: Trate a conformidade com a GDPR como um programa contínuo. Realize auditorias anuais da configuração da sua página inicial, configurações de retenção e DPAs de fornecedores.
- Direitos do Titular dos Dados: Garanta que você tenha um processo claro para lidar com Solicitações de Acesso do Titular dos Dados (DSARs) e solicitações de exclusão (o direito de ser esquecido) dentro do prazo legal de um mês.
Solução de Problemas e Mitigação de Riscos
Modo de Falha Comum: "Muros de Consentimento" Muitos locais tentam forçar o consentimento de marketing escondendo o botão "Conectar" até que a caixa de marketing seja marcada. Isso invalida o consimento sob o GDPR, pois não é "livremente concedido". Correção: Ofereça opções claras e separadas. Forneça um incentivo para o opt-in de marketing (por exemplo, um código de desconto), mas garanta um caminho para se conectar sem optar por isso.
Modo de Falha Comum: Dados Obsoletos Acumular anos de dados de hóspedes sem um mecanismo de purga aumenta seu perfil de risco em caso de violação. Correção: Utilize plataformas como a Purple que oferecem motores de política de retenção automatizados para aplicar suas regras de ciclo de vida de dados programaticamente.
ROI e Impacto nos Negócios
A conformidade é frequentemente vista como um centro de custo, mas uma implantação de WiFi bem arquitetada e compatível com o GDPR realmente gera valor de negócio. Ao construir confiança através de práticas de dados transparentes, os estabelecimentos observam uma captura de dados de maior qualidade. Quando os hóspedes optam explicitamente, o banco de dados de marketing resultante é altamente engajado, impulsionando melhores taxas de conversão para promoções de varejo ou programas de fidelidade de hospitalidade. Para saber mais sobre como maximizar esse valor, consulte nosso guia sobre Como Coletar Dados Primários Através do WiFi .
Termos-Chave e Definições
Captive Portal
The web page that users are directed to before gaining access to a public WiFi network, used for authentication and consent capture.
This is the primary interface where IT teams must implement GDPR-compliant consent mechanisms.
Data Controller
The entity that determines the purposes and means of the processing of personal data.
The venue operator (e.g., the hotel or retailer) is typically the Data Controller and holds primary legal responsibility.
Data Processor
An entity that processes personal data on behalf of the controller.
Third-party vendors, such as cloud WiFi analytics platforms (like Purple), act as Data Processors and require a DPA.
Data Processing Agreement (DPA)
A legally binding contract between a Data Controller and a Data Processor regulating how personal data is handled.
IT managers must ensure a signed DPA is in place with every vendor in the WiFi technology stack.
Lawful Basis
The legal justification under Article 6 of the GDPR required to process personal data.
IT teams must document whether they are relying on Consent, Legitimate Interests, or another basis for each data type collected.
Legitimate Interests Assessment (LIA)
A documented risk assessment demonstrating that the processing of personal data is necessary and balanced against the individual's rights.
Required when retaining network logs for security purposes without explicit user consent.
Record of Processing Activities (ROPA)
A formal document detailing all personal data processing activities within an organisation.
The output of the initial data mapping exercise, required by Article 30 for most enterprise deployments.
Data Subject Access Request (DSAR)
A request from an individual to access the personal data an organisation holds about them.
IT teams must have technical mechanisms in place to extract and provide a user's WiFi session and registration data within one month.
Estudos de Caso
A 200-room hotel needs to implement guest WiFi. The marketing director wants to capture email addresses to promote the hotel restaurant, but the IT director is concerned about GDPR compliance regarding network logs.
- The IT team configures the network controllers to retain MAC addresses and session data for 90 days under the lawful basis of 'Legitimate Interests' (for network security and troubleshooting), documenting this in an LIA.
- The captive portal is designed with two distinct sections: a mandatory checkbox for accepting the Terms of Service, and an optional, unticked checkbox for restaurant marketing emails.
- The hotel updates its Privacy Notice to clearly state these two distinct processing activities and links to it from the splash page.
A large retail chain uses WiFi analytics to track customer footfall and dwell time across 50 stores. They want to ensure this tracking doesn't violate GDPR.
The retail chain configures their WiFi analytics platform to immediately hash or pseudonymise MAC addresses upon collection. They use this aggregated data to generate heatmaps and footfall trends without identifying individual shoppers. They also place clear signage at store entrances informing customers that anonymised WiFi analytics are in use.
Análise de Cenário
Q1. Your marketing team wants to increase the size of their email database. They propose changing the guest WiFi splash page so that the 'Connect to Internet' button only becomes active after the user ticks a box agreeing to receive promotional offers. Is this compliant?
💡 Dica:Consider the GDPR definition of 'freely given' consent.
Mostrar Abordagem Recomendada
No, this is not compliant. This creates a 'consent wall' or bundled consent. Under GDPR, consent must be freely given. If access to the service (the WiFi) is made conditional on consenting to marketing, the consent is invalid. The marketing opt-in must be separate and optional.
Q2. A guest requests a copy of all data your venue holds on them (a DSAR). Your IT team exports their CRM profile showing their name and email, but ignores the WiFi controller logs containing their MAC address and connection times. Have you fulfilled the DSAR?
💡 Dica:Think about what constitutes 'personal data' under GDPR.
Mostrar Abordagem Recomendada
No. Because MAC addresses and connection logs can be linked to the identified individual (especially since they registered via the captive portal), those logs constitute personal data. A complete DSAR response must include the network-level data associated with their device.
Q3. You are migrating to a new cloud-based WiFi analytics provider. The vendor provides a standard Terms of Service document online. Is this sufficient for GDPR compliance?
💡 Dica:Review the requirements for engaging third-party data processors.
Mostrar Abordagem Recomendada
No. Under Article 28, you must have a formal, written Data Processing Agreement (DPA) in place with the vendor. The DPA must specifically detail the nature, purpose, and duration of the processing, the types of personal data involved, and the security obligations of the processor.



