O WiFi de Hotel é Seguro? O Que Todo Viajante Precisa Saber
Este guia técnico abrangente detalha os riscos de segurança específicos inerentes às redes WiFi de hotéis, incluindo APs maliciosos e ataques MITM. Ele fornece etapas de implementação acionáveis e neutras em relação ao fornecedor para gerentes de TI e arquitetos de rede protegerem sua infraestrutura sem fio e aproveitarem plataformas gerenciadas de Guest WiFi.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada
- O Problema da Autenticação: De Redes Abertas a WPA3
- Segmentação de Rede e Arquitetura VLAN
- O Cenário de Ameaças: APs Maliciosos e MITM
- Guia de Implementação
- Passo 1: Impor o Isolamento de Cliente
- Passo 2: Migrar para WPA3
- Passo 3: Implementar Segmentação VLAN Rigorosa
- Passo 4: Implementar um Captive Portal Gerenciado
- Passo 5: Habilitar Detecção de APs Maliciosos
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- Modo de Falha: Erros de Certificado do Captive Portal
- Modo de Falha: Roaming Ruim e Conexões Interrompidas
- Modo de Falha: Congestionamento da Rede e Esgotamento da Largura de Banda
- ROI e Impacto nos Negócios
- Ouça o Briefing

Resumo Executivo
A pergunta "o WiFi de hotel é seguro?" frequentemente domina as discussões entre gerentes de TI corporativos e equipes de viagens empresariais. Para diretores de operações de locais e arquitetos de rede, fornecer conectividade segura e confiável não é mais uma comodidade para o hóspede — é um requisito crítico de infraestrutura. Embora a tecnologia subjacente que alimenta as redes de hotéis tenha avançado, o cenário de ameaças evoluiu em paralelo. Pontos de acesso maliciosos, ataques man-in-the-middle (MITM) e arquiteturas mal segmentadas continuam a expor tanto hóspedes quanto operações hoteleiras a riscos significativos.
Este guia de referência técnica fornece orientação acionável para profissionais de TI que gerenciam infraestrutura sem fio em Hospitalidade , Varejo e outros locais públicos de grande escala. Dissecamos as vulnerabilidades específicas inerentes a implantações legadas, detalhamos os padrões arquitetônicos necessários para mitigá-las e descrevemos como a implementação de uma solução gerenciada de Guest WiFi pode transformar uma responsabilidade potencial em um ativo seguro e gerador de valor.
Análise Técnica Aprofundada
Para entender a postura de segurança de uma rede WiFi de hotel, devemos examinar a arquitetura, os mecanismos de autenticação e o fluxo de tráfego.
O Problema da Autenticação: De Redes Abertas a WPA3
Historicamente, as redes de hotéis dependiam de SSIDs abertos com captive portals para registro de endereço MAC, ou WPA2-Personal com uma Chave Pré-Compartilhada (PSK) compartilhada. Ambas as abordagens apresentam falhas de segurança fundamentais:
- Redes Abertas: Transmitem dados em texto simples pelo ar. Qualquer pessoa com um sniffer de pacotes pode capturar o tráfego entre o cliente e o Access Point (AP).
- WPA2-PSK: Embora o tráfego seja criptografado, a natureza compartilhada da chave significa que qualquer usuário autenticado pode descriptografar o tráfego de outros usuários no mesmo SSID.
O padrão da indústria está mudando para WPA3-SAE (Simultaneous Authentication of Equals). SAE substitui o handshake PSK, garantindo que, mesmo que vários usuários se conectem com a mesma senha, cada sessão seja protegida com uma chave de criptografia única e de segredo de encaminhamento. Além disso, as implantações corporativas devem aproveitar o Passpoint (Hotspot 2.0), permitindo que os dispositivos se autentiquem de forma contínua e segura usando certificados ou credenciais SIM, eliminando a necessidade de senhas compartilhadas vulneráveis.
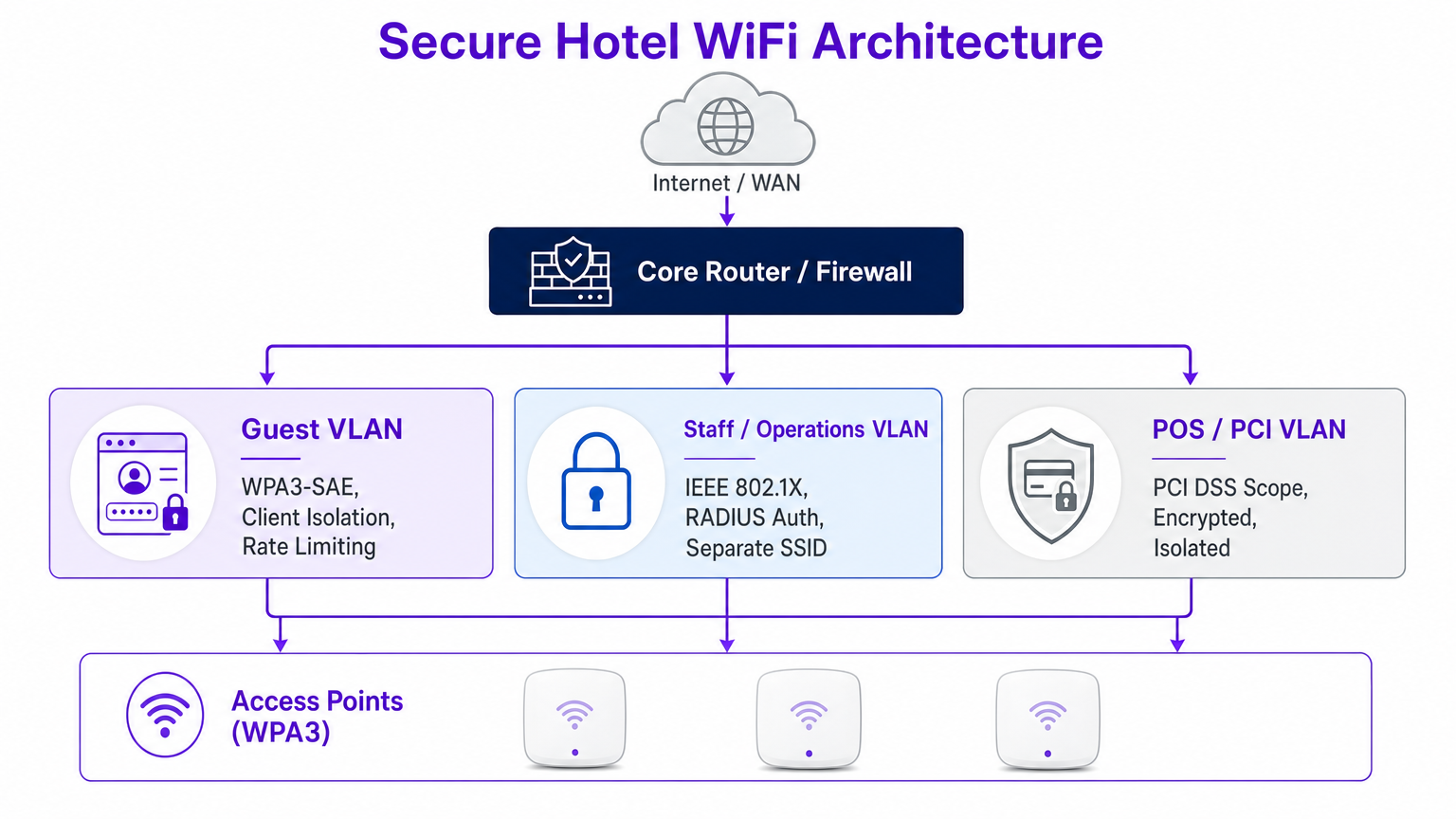
Segmentação de Rede e Arquitetura VLAN
Uma rede plana é uma rede comprometida. Quando os dispositivos dos hóspedes compartilham o mesmo domínio de broadcast que a tecnologia operacional (OT), sistemas de Ponto de Venda (POS) ou estações de trabalho administrativas, a superfície de ataque se expande exponencialmente.
A melhor prática dita uma segmentação VLAN rigorosa no nível do roteador central e do firewall. A VLAN de hóspedes deve ser logicamente isolada da VLAN da equipe (protegida via IEEE 802.1X e autenticação RADIUS) e da VLAN PCI (governada por requisitos rigorosos de escopo PCI DSS).
O Cenário de Ameaças: APs Maliciosos e MITM
As ameaças mais prevalentes em ambientes de hospitalidade não são exploits sofisticados de dia zero, mas sim ataques oportunistas que exploram configurações incorretas.
- Ataques Evil Twin (APs Maliciosos): Atacantes implantam APs não autorizados transmitindo o SSID do hotel. Os dispositivos se conectam automaticamente com base na força do sinal, permitindo que o atacante intercepte todo o tráfego. Controladores sem fio corporativos devem ter detecção e supressão contínuas de APs maliciosos habilitadas.
- Man-in-the-Middle (MITM) via ARP Poisoning: Se o isolamento de cliente estiver desabilitado, um atacante na rede de hóspedes pode falsificar o endereço MAC do gateway, roteando todo o tráfego da sub-rede através de seu dispositivo.

Guia de Implementação
A implantação de uma infraestrutura WiFi de hotel segura requer uma abordagem sistemática. Siga estas etapas neutras em relação ao fornecedor para fortalecer sua infraestrutura sem fio.
Passo 1: Impor o Isolamento de Cliente
O isolamento de cliente (ou isolamento de AP) impede que clientes sem fio no mesmo SSID se comuniquem diretamente entre si. Essa única alteração de configuração neutraliza o ARP poisoning e a propagação de malware peer-to-peer.
- Ação: Habilite o isolamento de cliente em todos os SSIDs voltados para hóspedes através do seu controlador de LAN sem fio (WLC) ou painel de gerenciamento na nuvem.
Passo 2: Migrar para WPA3
A transição para WPA3-SAE é crítica para proteger o tráfego over-the-air.
- Ação: Audite seu hardware de AP para suporte a WPA3. Habilite o modo de Transição WPA3 para suportar dispositivos legados enquanto impõe o WPA3 para clientes capazes.
Passo 3: Implementar Segmentação VLAN Rigorosa
Garanta a separação física e lógica do tráfego.
- Ação: Configure regras de firewall para bloquear todo o tráfego originado da VLAN de hóspedes destinado a sub-redes internas (endereços RFC 1918). Permita apenas tráfego HTTP/HTTPS e DNS de saída para a WAN.
Passo 4: Implementar um Captive Portal Gerenciado
Um captive portal robusto faz mais do que apresentar termos e condições; ele gerencia o onboarding de dispositivos e se integra com análises de backend.
- Ação: Implemente uma plataforma centralizada de Guest WiFi . Garanta que o portal seja servido via HTTPS para evitar a interceptação de credenciais durante a fase de login.
Passo 5: Habilitar Detecção de APs Maliciosos
O monitoramento proativo é essencial.
- Ação: Configure seu WLC para escanear BSSIDs não autorizados. Configure alertas automatizados para o centro de operações de rede (NOC) quando um AP malicioso for detectado operando nas instalações.
Melhores Práticas
Ao arquitetar ou auditar redes sem fio corporativas, siga estas melhores práticas padrão da indústria:
- Adote Zero TrPrincípios para Hóspedes: Trate a rede de convidados como hostil. Recursos corporativos internos nunca devem ser acessíveis a partir do guest SSID sem uma conexão VPN segura.
- Auditorias de Configuração Regulares: A deriva da rede ocorre. Conduza revisões trimestrais de ACLs de VLAN, configurações de WLC e versões de firmware de AP. Para mais informações sobre seleção de AP, revise Seu Guia para um Ponto de Acesso Sem Fio Ruckus .
- Priorize a Privacidade e a Conformidade: Garanta que suas práticas de coleta de dados estejam alinhadas com o GDPR e as regulamentações locais de privacidade. Uma plataforma de WiFi Analytics compatível oferece insights seguros e anonimizados sem comprometer a privacidade do usuário.
- Eduque a Equipe e os Hóspedes: Forneça diretrizes claras aos viajantes corporativos. Recomende o uso de VPNs corporativas e alerte contra a ignorância de erros de certificado em captive portals.
Solução de Problemas e Mitigação de Riscos
Mesmo redes bem projetadas apresentam problemas. Aqui estão os modos de falha comuns e as estratégias de mitigação.
Modo de Falha: Erros de Certificado do Captive Portal
Sintoma: Hóspedes recebem avisos do navegador ao tentar acessar a página de login. Causa Raiz: O WLC ou servidor de portal está apresentando um certificado SSL expirado, autoassinado ou com cadeia de confiança inadequada. Mitigação: Garanta que o captive portal utilize um certificado válido de uma Autoridade Certificadora (CA) pública confiável. Implemente processos automatizados de renovação de certificados.
Modo de Falha: Roaming Ruim e Conexões Interrompidas
Sintoma: Hóspedes experimentam desconexões ao se moverem entre pontos de acesso. Causa Raiz: Planejamento de RF inadequado, canais sobrepostos ou falta de suporte para protocolos de roaming rápido (802.11r/k/v). Mitigação: Conduza uma pesquisa de site abrangente. Habilite 802.11r (Fast BSS Transition) para otimizar a autenticação durante o roaming, o que é particularmente crítico para aplicações de voz e vídeo.
Modo de Falha: Congestionamento da Rede e Esgotamento da Largura de Banda
Sintoma: Velocidades lentas e alta latência durante os horários de pico. Causa Raiz: Alguns usuários pesados consumindo a largura de banda WAN disponível. Mitigação: Implemente limitação de taxa por cliente e modelagem de tráfego em nível de aplicação no firewall ou controlador para garantir uma distribuição justa de recursos.
ROI e Impacto nos Negócios
Ver o WiFi de hotel apenas como um centro de custo ignora seu potencial como um ativo estratégico. Uma rede segura e bem gerenciada oferece um impacto mensurável nos negócios.
- Redução de Riscos: Mitigar o risco de uma violação de dados protege a reputação da marca e evita multas regulatórias caras (por exemplo, penalidades por não conformidade com PCI DSS).
- Eficiência Operacional: Gerenciamento centralizado e onboarding automatizado reduzem os tickets de helpdesk e liberam recursos de TI para projetos estratégicos.
- Insights Orientados por Dados: Ao aproveitar uma plataforma segura de Guest WiFi , os locais podem capturar dados primários, impulsionando programas de fidelidade e campanhas de marketing personalizadas. Para uma perspectiva mais ampla sobre a seleção da plataforma certa, consulte nosso Soluções WiFi Empresariais: Um Guia do Comprador .
Quando integrada de forma eficaz, a rede se transforma de uma utilidade em uma base segura para o engajamento do cliente e a excelência operacional.
Ouça o Briefing
Para um aprofundamento nesses tópicos, ouça nosso briefing em áudio:
Termos-Chave e Definições
Evil Twin Access Point
A rogue wireless access point that masquerades as a legitimate network (often copying the SSID) to intercept user traffic and credentials.
IT teams must configure WLCs to detect and suppress these devices to protect guests from credential harvesting.
Client Isolation (AP Isolation)
A wireless network configuration that prevents devices connected to the same AP or SSID from communicating directly with one another.
Essential for public networks to prevent ARP poisoning, MITM attacks, and peer-to-peer malware spread.
WPA3-SAE
Simultaneous Authentication of Equals; the modern encryption standard that replaces the vulnerable Pre-Shared Key (PSK) exchange, ensuring forward secrecy.
Hotels must migrate to WPA3 to protect guest traffic from passive decryption by other users on the network.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic and limit the blast radius of a potential breach.
Critical for separating untrusted guest traffic from sensitive operational and PCI-scoped environments.
Passpoint (Hotspot 2.0)
A standard that enables seamless and secure authentication to WiFi networks using certificates or SIM credentials, eliminating captive portals and shared passwords.
The future of secure guest onboarding, providing cellular-like roaming experiences for WiFi.
Rogue AP Detection
A feature of enterprise wireless controllers that scans the RF environment for unauthorized access points operating within the venue's airspace.
A necessary defensive measure to identify and mitigate Evil Twin attacks and unauthorized shadow IT.
ARP Poisoning
An attack where a malicious actor sends falsified Address Resolution Protocol (ARP) messages over a local area network to link their MAC address with the IP address of a legitimate gateway.
The primary mechanism for MITM attacks on poorly configured networks; mitigated by client isolation.
Captive Portal
A web page that users are forced to view and interact with before access is granted to the broader network.
Used for authentication, terms of service acceptance, and data capture via platforms like Purple's Guest WiFi.
Estudos de Caso
A luxury 300-room hotel currently operates a flat network where guest devices, staff tablets, and POS terminals all connect to the same subnet. The IT Director needs to secure the environment ahead of a PCI DSS audit without disrupting the guest experience.
- Deploy three distinct VLANs: Guest (VLAN 10), Staff (VLAN 20), and POS/PCI (VLAN 30).
- Configure firewall ACLs: Block all inter-VLAN routing. Restrict Guest VLAN to outbound internet only. Restrict POS VLAN to specific payment gateway IPs.
- Enable AP Client Isolation on the Guest SSID.
- Implement WPA3-SAE on the Guest SSID, and 802.1X/RADIUS for the Staff SSID.
- Deploy a managed captive portal for guest onboarding.
A retail chain with 50 locations offers free public WiFi. The security team has detected multiple instances of attackers setting up 'Free_Store_WiFi' hotspots near the entrances to harvest credentials.
- Enable Rogue AP Detection on the enterprise wireless controllers across all locations.
- Configure the system to automatically classify APs broadcasting the corporate SSID on unauthorized MAC addresses as malicious.
- Implement wireless intrusion prevention system (WIPS) features to actively de-authenticate clients attempting to connect to the rogue APs.
- Transition the legitimate guest network to Passpoint (Hotspot 2.0) to rely on certificate-based authentication rather than open SSIDs.
Análise de Cenário
Q1. You are auditing a newly acquired boutique hotel. The network uses WPA2-Personal with a password printed on a card in every room. The network is a single flat subnet. What is the immediate, most critical risk, and what is the first remediation step?
💡 Dica:Consider what happens when every guest has the same encryption key on a flat network.
Mostrar Abordagem Recomendada
The most critical risk is that any guest can decrypt the traffic of any other guest, and because the network is flat, they can also attempt to access operational systems. The immediate first step is to enable AP Client Isolation to prevent peer-to-peer communication, followed closely by implementing VLAN segmentation to isolate guest traffic from hotel operations.
Q2. A corporate client requires assurance that their executives can safely work from your hotel. They demand that you implement WPA3. Your current APs only support WPA2. What is the best architectural response to secure their traffic without immediately replacing hardware?
💡 Dica:Think about how the client can secure their own traffic end-to-end regardless of the local wireless encryption.
Mostrar Abordagem Recomendada
While WPA3 is ideal, the architectural response is to advise the client to mandate Corporate VPN usage for all executives. A VPN creates an encrypted tunnel at the network layer (IPsec/OpenVPN) or application layer (SSL/TLS), ensuring that even if the local WPA2 over-the-air encryption is compromised, the data payload remains secure.
Q3. Your WLC dashboard shows an alert for a 'Rogue AP' broadcasting your exact guest SSID. The signal is strongest near the lobby bar. What is the correct operational response?
💡 Dica:Balancing automated technical responses with physical security investigation.
Mostrar Abordagem Recomendada
- Verify the alert in the WLC to confirm the BSSID does not belong to your infrastructure. 2. If supported and legal in your jurisdiction, initiate wireless containment (de-authentication frames) against the rogue AP to protect guests. 3. Dispatch onsite security or IT staff to the lobby bar to physically locate and remove the device.



