¿Es seguro el WiFi de los hoteles? Lo que todo viajero necesita saber
Esta guía técnica exhaustiva detalla los riesgos de seguridad específicos inherentes a las redes WiFi de hoteles, incluyendo APs no autorizados y ataques MITM. Proporciona pasos de implementación prácticos y neutrales para los gestores de TI y arquitectos de red para asegurar su infraestructura inalámbrica y aprovechar las plataformas de Guest WiFi gestionadas.
🎧 Escuchar esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado
- El Problema de la Autenticación: De Redes Abiertas a WPA3
- Segmentación de Red y Arquitectura VLAN
- El Panorama de Amenazas: Rogue APs y MITM
- Guía de Implementación
- Paso 1: Imponer la Aislación de Clientes
- Paso 2: Migrar a WPA3
- Paso 3: Implementar una Segmentación VLAN Estricta
- Paso 4: Desplegar un Captive Portal Gestionado
- Paso 5: Habilitar la Detección de Rogue APs
- Mejores Prácticas
- Resolución de Problemas y Mitigación de Riesgos
- Modo de Fallo: Errores de Certificado del Captive Portal
- Modo de Fallo: Roaming Deficiente y Conexiones Caídas
- Modo de Fallo: Congestión de la Red y Agotamiento del Ancho de Banda
- ROI e Impacto Empresarial
- Escuche el Informe

Resumen Ejecutivo
La pregunta "¿es seguro el WiFi de los hoteles?" domina con frecuencia las discusiones entre los gestores de TI empresariales y los equipos de viajes corporativos. Para los directores de operaciones de recintos y los arquitectos de red, proporcionar conectividad segura y fiable ya no es una comodidad para los huéspedes, sino un requisito de infraestructura crítico. Si bien la tecnología subyacente que impulsa las redes de hoteles ha avanzado, el panorama de amenazas ha evolucionado en paralelo. Los puntos de acceso no autorizados (rogue APs), los ataques de intermediario (MITM) y las arquitecturas mal segmentadas continúan exponiendo tanto a los huéspedes como a las operaciones del hotel a un riesgo significativo.
Esta guía de referencia técnica proporciona orientación práctica para los profesionales de TI que gestionan infraestructuras inalámbricas en Hostelería , Comercio minorista y otros grandes recintos públicos. Diseccionamos las vulnerabilidades específicas inherentes a las implementaciones heredadas, detallamos los estándares arquitectónicos necesarios para mitigarlas y describimos cómo la implementación de una solución de Guest WiFi gestionada puede transformar una posible responsabilidad en un activo seguro y generador de valor.
Análisis Técnico Detallado
Para comprender la postura de seguridad de una red WiFi de hotel, debemos examinar la arquitectura, los mecanismos de autenticación y el flujo de tráfico.
El Problema de la Autenticación: De Redes Abiertas a WPA3
Históricamente, las redes de hoteles dependían de SSIDs abiertos con captive portals para el registro de direcciones MAC, o WPA2-Personal con una clave precompartida (PSK) compartida. Ambos enfoques presentan fallos de seguridad fundamentales:
- Redes Abiertas: Transmiten datos en texto plano por el aire. Cualquiera con un sniffer de paquetes puede capturar el tráfico entre el cliente y el Access Point (AP).
- WPA2-PSK: Aunque el tráfico está cifrado, la naturaleza compartida de la clave significa que cualquier usuario autenticado puede descifrar el tráfico de otros usuarios en el mismo SSID.
El estándar de la industria está evolucionando hacia WPA3-SAE (Simultaneous Authentication of Equals). SAE reemplaza el handshake de PSK, asegurando que incluso si varios usuarios se conectan con la misma contraseña, cada sesión se asegura con una clave de cifrado única y con secreto hacia adelante. Además, las implementaciones empresariales deberían aprovechar Passpoint (Hotspot 2.0), permitiendo que los dispositivos se autentiquen de forma fluida y segura utilizando certificados o credenciales SIM, eliminando la necesidad de contraseñas compartidas vulnerables.
Segmentación de Red y Arquitectura VLAN
Una red plana es una red comprometida. Cuando los dispositivos de los huéspedes comparten el mismo dominio de difusión que la tecnología operativa (OT), los sistemas de punto de venta (POS) o las estaciones de trabajo administrativas, la superficie de ataque se expande exponencialmente.
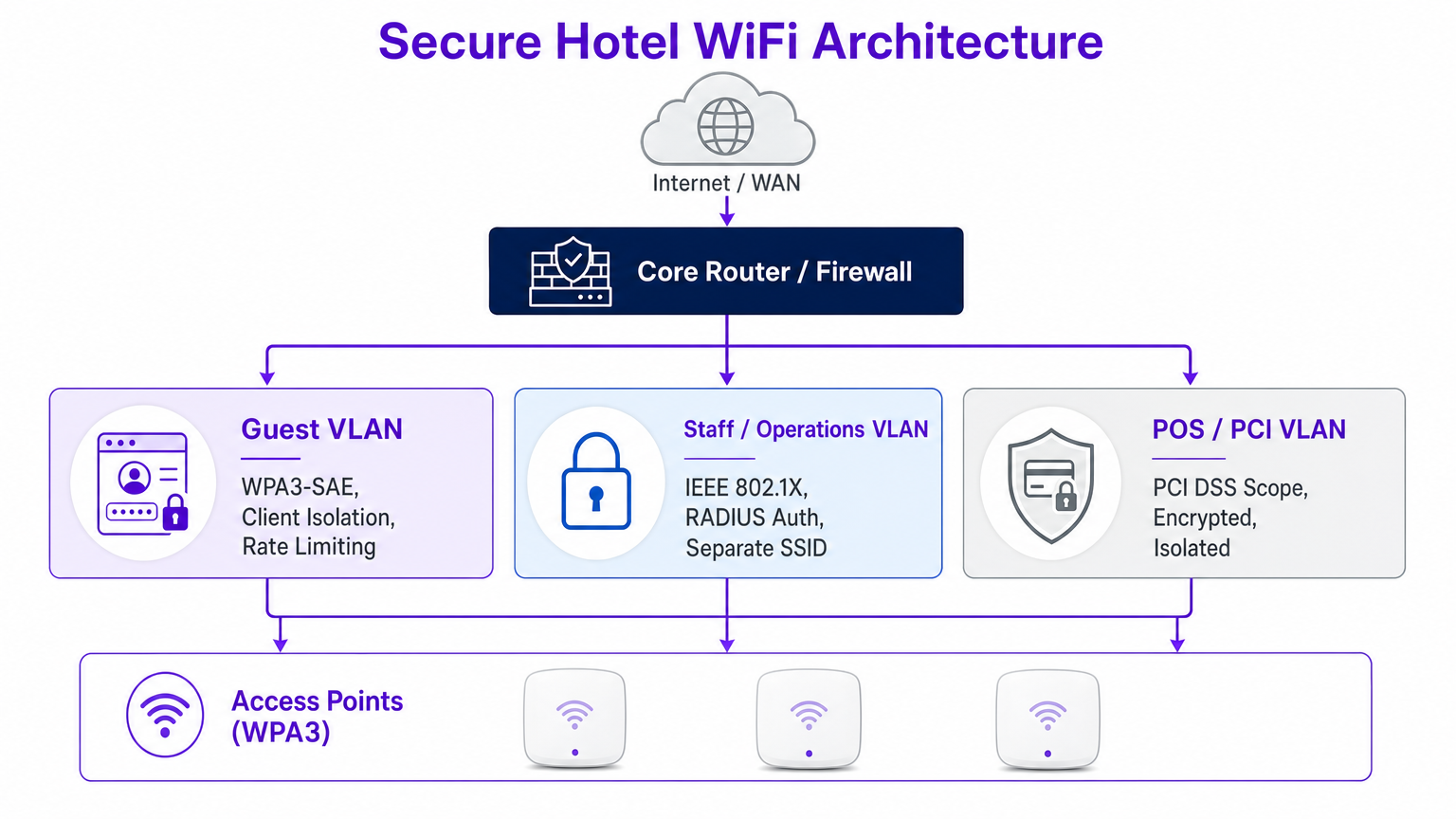
La mejor práctica dicta una estricta segmentación de VLAN a nivel de router central y firewall. La VLAN de invitados debe estar lógicamente aislada de la VLAN del personal (asegurada mediante autenticación IEEE 802.1X y RADIUS) y de la VLAN PCI (gobernada por estrictos requisitos de alcance PCI DSS).
El Panorama de Amenazas: Rogue APs y MITM
Las amenazas más prevalentes en entornos de hostelería no son exploits sofisticados de día cero, sino ataques oportunistas que aprovechan configuraciones erróneas.
- Ataques Evil Twin (Rogue APs): Los atacantes despliegan APs no autorizados que emiten el SSID del hotel. Los dispositivos se conectan automáticamente basándose en la intensidad de la señal, permitiendo al atacante interceptar todo el tráfico. Los controladores inalámbricos empresariales deben tener habilitada la detección y supresión continua de rogue APs.
- Man-in-the-Middle (MITM) mediante Envenenamiento ARP: Si la aislación de clientes está deshabilitada, un atacante en la red de invitados puede suplantar la dirección MAC de la puerta de enlace, enrutando todo el tráfico de la subred a través de su dispositivo.

Guía de Implementación
Desplegar una infraestructura WiFi segura en hoteles requiere un enfoque sistemático. Siga estos pasos neutrales al proveedor para fortalecer su infraestructura inalámbrica.
Paso 1: Imponer la Aislación de Clientes
La aislación de clientes (o aislación de AP) evita que los clientes inalámbricos en el mismo SSID se comuniquen directamente entre sí. Este único cambio de configuración neutraliza el envenenamiento ARP y la propagación de malware peer-to-peer.
- Acción: Habilite la aislación de clientes en todos los SSIDs orientados a huéspedes a través de su controlador de LAN inalámbrica (WLC) o panel de gestión en la nube.
Paso 2: Migrar a WPA3
La transición a WPA3-SAE es fundamental para proteger el tráfico inalámbrico.
- Acción: Audite su hardware de AP para verificar la compatibilidad con WPA3. Habilite el modo de transición WPA3 para admitir dispositivos heredados mientras impone WPA3 para clientes compatibles.
Paso 3: Implementar una Segmentación VLAN Estricta
Asegure la separación física y lógica del tráfico.
- Acción: Configure reglas de firewall para bloquear todo el tráfico originado en la VLAN de invitados y destinado a subredes internas (direcciones RFC 1918). Permita solo el tráfico HTTP/HTTPS y DNS saliente a la WAN.
Paso 4: Desplegar un Captive Portal Gestionado
Un captive portal robusto hace más que presentar términos y condiciones; gestiona la incorporación de dispositivos y se integra con análisis de backend.
- Acción: Implemente una plataforma centralizada de Guest WiFi . Asegúrese de que el portal se sirva a través de HTTPS para evitar la interceptación de credenciales durante la fase de inicio de sesión.
Paso 5: Habilitar la Detección de Rogue APs
El monitoreo proactivo es esencial.
- Acción: Configure su WLC para escanear BSSIDs no autorizados. Configure alertas automatizadas para el centro de operaciones de red (NOC) cuando se detecte un rogue AP operando en las instalaciones.
Mejores Prácticas
Al diseñar o auditar redes inalámbricas empresariales, siga estas mejores prácticas estándar de la industria:
- Adoptar Zero TrPrincipios para Huéspedes: Trate la red de invitados como hostil. Los recursos corporativos internos nunca deben ser accesibles desde la SSID de invitados sin una conexión VPN segura.
- Auditorías de Configuración Regulares: La deriva de la red ocurre. Realice revisiones trimestrales de las ACL de VLAN, las configuraciones de WLC y las versiones de firmware de AP. Para obtener más información sobre la selección de AP, revise Su Guía para un Punto de Acceso Inalámbrico Ruckus .
- Priorice la Privacidad y el Cumplimiento: Asegúrese de que sus prácticas de recopilación de datos se alineen con GDPR y las regulaciones de privacidad locales. Una plataforma de WiFi Analytics compatible proporciona información segura y anonimizada sin comprometer la privacidad del usuario.
- Eduque al Personal y a los Huéspedes: Proporcione directrices claras a los viajeros corporativos. Recomiende el uso de VPN corporativas y advierta contra la ignorancia de errores de certificado en los captive portals.
Resolución de Problemas y Mitigación de Riesgos
Incluso las redes bien diseñadas experimentan problemas. Aquí se presentan los modos de fallo comunes y las estrategias de mitigación.
Modo de Fallo: Errores de Certificado del Captive Portal
Síntoma: Los huéspedes reciben advertencias del navegador al intentar acceder a la página de inicio de sesión. Causa Raíz: El WLC o el servidor del portal está presentando un certificado SSL caducado, autofirmado o encadenado incorrectamente. Mitigación: Asegúrese de que el captive portal utilice un certificado válido de una Autoridad de Certificación (CA) pública de confianza. Implemente procesos automatizados de renovación de certificados.
Modo de Fallo: Roaming Deficiente y Conexiones Caídas
Síntoma: Los huéspedes experimentan desconexiones al moverse entre puntos de acceso. Causa Raíz: Planificación de RF inadecuada, canales superpuestos o falta de soporte para protocolos de roaming rápido (802.11r/k/v). Mitigación: Realice un estudio de sitio exhaustivo. Habilite 802.11r (Fast BSS Transition) para agilizar la autenticación durante el roaming, lo cual es particularmente crítico para aplicaciones de voz y vídeo.
Modo de Fallo: Congestión de la Red y Agotamiento del Ancho de Banda
Síntoma: Velocidades lentas y alta latencia durante las horas pico. Causa Raíz: Pocos usuarios intensivos que consumen el ancho de banda WAN disponible. Mitigación: Implemente la limitación de velocidad por cliente y la conformación del tráfico a nivel de aplicación en el firewall o el controlador para garantizar una distribución justa de los recursos.
ROI e Impacto Empresarial
Ver el WiFi del hotel únicamente como un centro de costes ignora su potencial como activo estratégico. Una red segura y bien gestionada ofrece un impacto empresarial medible.
- Reducción de Riesgos: Mitigar el riesgo de una violación de datos protege la reputación de la marca y evita costosas multas regulatorias (por ejemplo, sanciones por incumplimiento de PCI DSS).
- Eficiencia Operativa: La gestión centralizada y la incorporación automatizada reducen los tickets de soporte y liberan recursos de TI para proyectos estratégicos.
- Información Basada en Datos: Al aprovechar una plataforma segura de Guest WiFi , los establecimientos pueden capturar datos de primera parte, impulsando programas de fidelización y campañas de marketing personalizadas. Para una perspectiva más amplia sobre la selección de la plataforma adecuada, consulte nuestra Soluciones WiFi Empresariales: Guía del Comprador .
Cuando se integra eficazmente, la red se transforma de una utilidad en una base segura para la interacción con el cliente y la excelencia operativa.
Escuche el Informe
Para una inmersión más profunda en estos temas, escuche nuestro informe de audio:
Términos clave y definiciones
Evil Twin Access Point
A rogue wireless access point that masquerades as a legitimate network (often copying the SSID) to intercept user traffic and credentials.
IT teams must configure WLCs to detect and suppress these devices to protect guests from credential harvesting.
Client Isolation (AP Isolation)
A wireless network configuration that prevents devices connected to the same AP or SSID from communicating directly with one another.
Essential for public networks to prevent ARP poisoning, MITM attacks, and peer-to-peer malware spread.
WPA3-SAE
Simultaneous Authentication of Equals; the modern encryption standard that replaces the vulnerable Pre-Shared Key (PSK) exchange, ensuring forward secrecy.
Hotels must migrate to WPA3 to protect guest traffic from passive decryption by other users on the network.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic and limit the blast radius of a potential breach.
Critical for separating untrusted guest traffic from sensitive operational and PCI-scoped environments.
Passpoint (Hotspot 2.0)
A standard that enables seamless and secure authentication to WiFi networks using certificates or SIM credentials, eliminating captive portals and shared passwords.
The future of secure guest onboarding, providing cellular-like roaming experiences for WiFi.
Rogue AP Detection
A feature of enterprise wireless controllers that scans the RF environment for unauthorized access points operating within the venue's airspace.
A necessary defensive measure to identify and mitigate Evil Twin attacks and unauthorized shadow IT.
ARP Poisoning
An attack where a malicious actor sends falsified Address Resolution Protocol (ARP) messages over a local area network to link their MAC address with the IP address of a legitimate gateway.
The primary mechanism for MITM attacks on poorly configured networks; mitigated by client isolation.
Captive Portal
A web page that users are forced to view and interact with before access is granted to the broader network.
Used for authentication, terms of service acceptance, and data capture via platforms like Purple's Guest WiFi.
Casos de éxito
A luxury 300-room hotel currently operates a flat network where guest devices, staff tablets, and POS terminals all connect to the same subnet. The IT Director needs to secure the environment ahead of a PCI DSS audit without disrupting the guest experience.
- Deploy three distinct VLANs: Guest (VLAN 10), Staff (VLAN 20), and POS/PCI (VLAN 30).
- Configure firewall ACLs: Block all inter-VLAN routing. Restrict Guest VLAN to outbound internet only. Restrict POS VLAN to specific payment gateway IPs.
- Enable AP Client Isolation on the Guest SSID.
- Implement WPA3-SAE on the Guest SSID, and 802.1X/RADIUS for the Staff SSID.
- Deploy a managed captive portal for guest onboarding.
A retail chain with 50 locations offers free public WiFi. The security team has detected multiple instances of attackers setting up 'Free_Store_WiFi' hotspots near the entrances to harvest credentials.
- Enable Rogue AP Detection on the enterprise wireless controllers across all locations.
- Configure the system to automatically classify APs broadcasting the corporate SSID on unauthorized MAC addresses as malicious.
- Implement wireless intrusion prevention system (WIPS) features to actively de-authenticate clients attempting to connect to the rogue APs.
- Transition the legitimate guest network to Passpoint (Hotspot 2.0) to rely on certificate-based authentication rather than open SSIDs.
Análisis de escenarios
Q1. You are auditing a newly acquired boutique hotel. The network uses WPA2-Personal with a password printed on a card in every room. The network is a single flat subnet. What is the immediate, most critical risk, and what is the first remediation step?
💡 Sugerencia:Consider what happens when every guest has the same encryption key on a flat network.
Mostrar enfoque recomendado
The most critical risk is that any guest can decrypt the traffic of any other guest, and because the network is flat, they can also attempt to access operational systems. The immediate first step is to enable AP Client Isolation to prevent peer-to-peer communication, followed closely by implementing VLAN segmentation to isolate guest traffic from hotel operations.
Q2. A corporate client requires assurance that their executives can safely work from your hotel. They demand that you implement WPA3. Your current APs only support WPA2. What is the best architectural response to secure their traffic without immediately replacing hardware?
💡 Sugerencia:Think about how the client can secure their own traffic end-to-end regardless of the local wireless encryption.
Mostrar enfoque recomendado
While WPA3 is ideal, the architectural response is to advise the client to mandate Corporate VPN usage for all executives. A VPN creates an encrypted tunnel at the network layer (IPsec/OpenVPN) or application layer (SSL/TLS), ensuring that even if the local WPA2 over-the-air encryption is compromised, the data payload remains secure.
Q3. Your WLC dashboard shows an alert for a 'Rogue AP' broadcasting your exact guest SSID. The signal is strongest near the lobby bar. What is the correct operational response?
💡 Sugerencia:Balancing automated technical responses with physical security investigation.
Mostrar enfoque recomendado
- Verify the alert in the WLC to confirm the BSSID does not belong to your infrastructure. 2. If supported and legal in your jurisdiction, initiate wireless containment (de-authentication frames) against the rogue AP to protect guests. 3. Dispatch onsite security or IT staff to the lobby bar to physically locate and remove the device.



