Minimizando Distrações de Alunos com Bloqueio de Anúncios em Nível de Rede
Este guia de referência técnica e autoritário detalha a arquitetura, implantação e impacto nos negócios do bloqueio de anúncios em nível de rede em ambientes educacionais. Ele fornece a gerentes de TI e arquitetos de rede estratégias acionáveis para recuperar largura de banda, fortalecer a conformidade e eliminar riscos de malvertising.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada
- Arquitetura de Filtragem em Nível DNS
- Proxy e Inspeção SSL
- Integração com Controle de Acesso à Rede (NAC)
- Guia de Implementação
- Fase 1: Auditoria de Tráfego e Definição de Linha de Base
- Fase 2: Implantação Piloto
- Fase 3: Lançamento Completo e Ajuste de Políticas
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios
Resumo Executivo
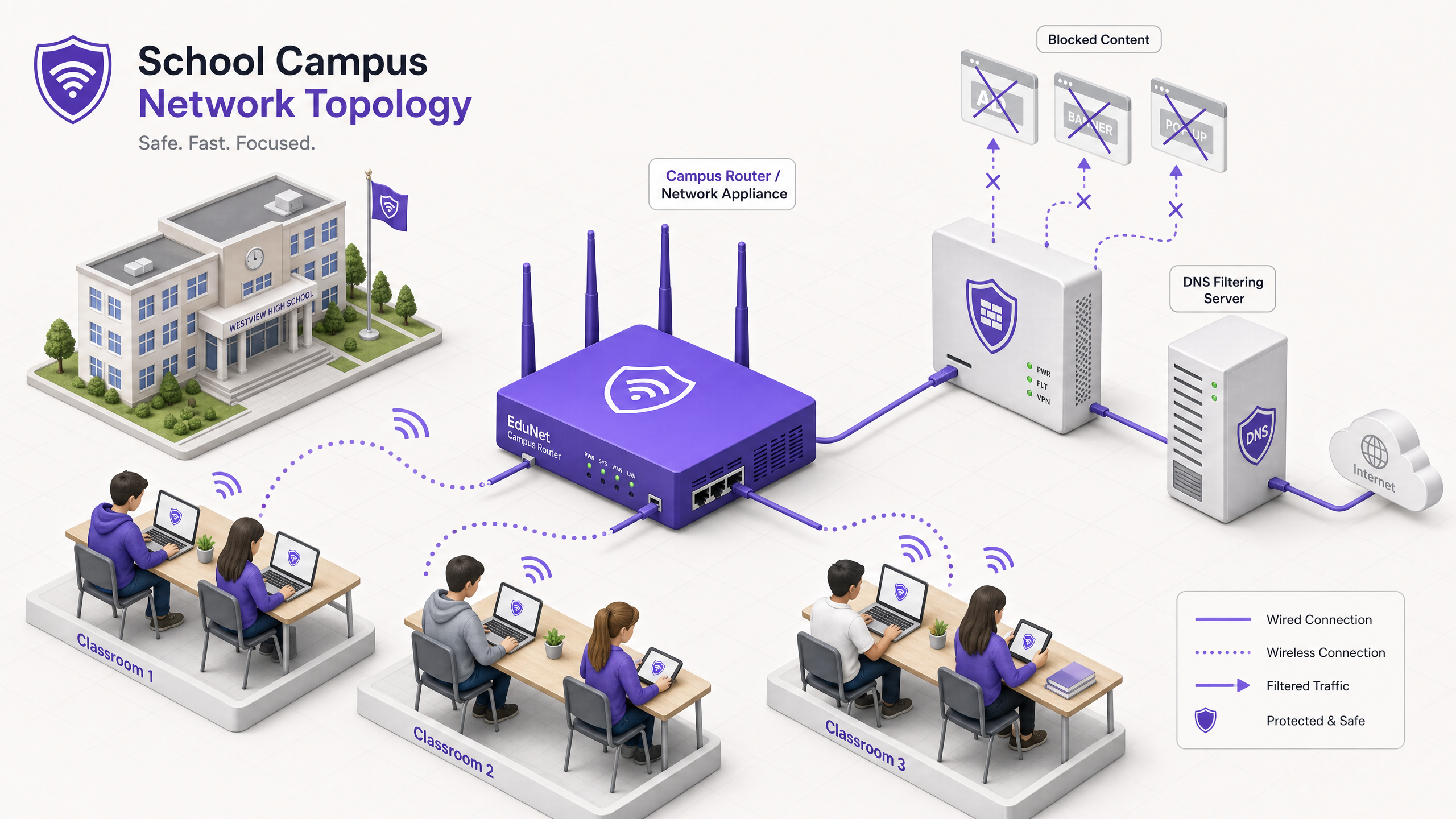
Para Diretores de TI e arquitetos de rede que gerenciam ambientes educacionais, a proliferação de dispositivos criou uma tempestade perfeita de consumo de largura de banda, riscos de segurança e lacunas de conformidade. Com os alunos trazendo uma média de 2,5 dispositivos para o campus, gerenciar a filtragem baseada em endpoint não é mais uma estratégia operacional viável.
O bloqueio de anúncios em nível de rede representa uma mudança fundamental do gerenciamento de endpoints para o controle na camada de infraestrutura. Ao interceptar o tráfego no nível DNS ou proxy antes que ele chegue ao dispositivo cliente, as equipes de TI podem eliminar unilateralmente até 30% do consumo de largura de banda não educacional, mitigar riscos de malvertising e impor a conformidade com estruturas de proteção de dados como GDPR e COPPA.
Este guia de referência técnica descreve a arquitetura, a metodologia de implantação e a medição de ROI para a implementação de bloqueio de anúncios em nível de rede em campi K-12 e universitários, com base em implantações reais em ambientes de alta densidade.
Ouça nosso podcast complementar para uma visão estratégica:
Análise Técnica Detalhada
A implementação do bloqueio de anúncios na camada de rede requer uma abordagem arquitetônica em camadas para lidar com a diversidade do tráfego web moderno, particularmente a ubiquidade do HTTPS e os protocolos DNS criptografados emergentes.
Arquitetura de Filtragem em Nível DNS
A camada fundamental do bloqueio de anúncios de rede é a filtragem DNS. Quando um dispositivo cliente tenta resolver um domínio associado a redes de publicidade, telemetria ou rastreamento, o resolvedor DNS da rede intercepta a consulta e a verifica em uma lista de bloqueio dinâmica.
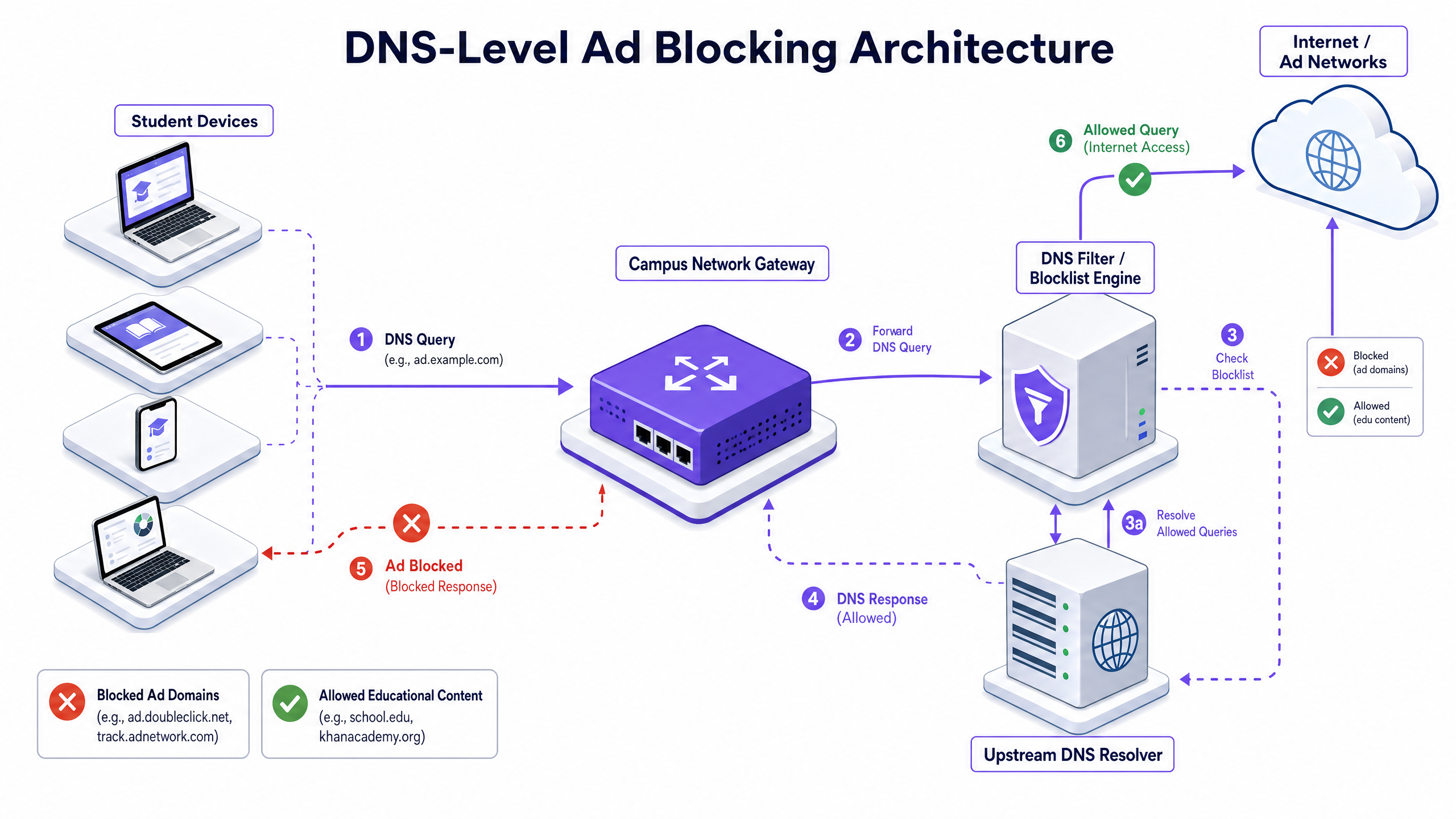
Esta abordagem é altamente eficiente porque impede que a conexão seja estabelecida. O payload do anúncio nunca é baixado, e o script de rastreamento nunca é executado. No entanto, as implantações modernas devem considerar DNS-over-HTTPS (DoH) e DNS-over-TLS (DoT). Se os dispositivos cliente ignorarem o resolvedor local usando DNS criptografado, a camada de filtragem é contornada. Os arquitetos de rede devem configurar firewalls de perímetro para bloquear endpoints DoH/DoT conhecidos (como 8.8.8.8 na porta 443) para forçar o fallback para DNS padrão (porta 53), ou implantar uma solução de gateway que inspecione nativamente o tráfego DoH.
Proxy e Inspeção SSL
Embora a filtragem DNS lide com a maioria do tráfego de anúncios, o proxy HTTP/HTTPS transparente oferece controle granular sobre URLs específicas, em vez de domínios inteiros. Como a vasta maioria do tráfego web é criptografada, a implantação de inspeção SSL (descriptografia Man-in-the-Middle) é necessária para a inspeção profunda de pacotes.
Isso requer a implantação de um certificado raiz confiável em todos os dispositivos gerenciados. Embora seja uma prática padrão em ambientes corporativos, a inspeção SSL em ambientes educacionais exige um escopo cuidadoso para evitar a descriptografia de tráfego sensível (por exemplo, portais bancários ou de saúde) e deve estar alinhada com a política de uso aceitável da organização.
Integração com Controle de Acesso à Rede (NAC)
A filtragem eficaz requer políticas sensíveis à identidade. A integração com IEEE 802.1X permite que a rede aplique políticas de filtragem diferenciadas com base no usuário autenticado ou perfil do dispositivo. Um aluno que faz login na rede via WPA3-Enterprise recebe uma política restritiva, enquanto um membro da equipe recebe uma política diferente, e um visitante na rede Guest WiFi recebe uma política de conformidade básica.
Guia de Implementação
A implantação do bloqueio de anúncios em nível de rede requer uma abordagem faseada para evitar a interrupção de atividades educacionais legítimas.
Fase 1: Auditoria de Tráfego e Definição de Linha de Base
Antes de implementar quaisquer regras de bloqueio, implante a solução de filtragem em modo de monitoramento passivo (somente registro) por 14-21 dias. Isso estabelece uma linha de base dos volumes e categorização atuais de consultas DNS. Use esses dados para identificar as principais redes de anúncios e domínios de rastreamento que atualmente consomem largura de banda. Esta linha de base é crítica para o cálculo posterior do ROI e relatórios de WiFi Analytics .
Fase 2: Implantação Piloto
Selecione um segmento de rede representativo — como uma única VLAN de estudante ou um edifício específico — para a fase piloto. Aplique as políticas iniciais da lista de bloqueio visando redes de anúncios e rastreadores conhecidos.
Passo Crucial: Estabeleça um processo de solicitação de lista de permissões de resposta rápida. Professores inevitavelmente encontrarão falsos positivos onde conteúdo educacional legítimo está hospedado em domínios categorizados como publicidade ou rastreamento. O suporte de TI deve estar preparado para avaliar e adicionar domínios à lista de permissões rapidamente para manter a confiança das partes interessadas.
Fase 3: Lançamento Completo e Ajuste de Políticas
Expanda a implantação para todos os segmentos de rede relevantes, aplicando políticas diferenciadas via integração 802.1X. Monitore os logs continuamente pelas primeiras 48 horas para identificar quaisquer problemas sistêmicos.
Garanta que a implantação esteja alinhada com políticas de segurança mais amplas, como a manutenção de um Explain what is audit trail for IT Security in 2026 para demonstrar conformidade com os requisitos de segurança.
Melhores Práticas
- Defesa em Camadas: Não dependa apenas da filtragem DNS. Combine-a com o gerenciamento de endpoints para dispositivos de propriedade da escola e regras de firewall robustas para bloquear tentativas de bypass (por exemplo, protocolos VPN, DoH).
- Segurança Padronizada: Garanta que todas as novas implantações sem fio utilizem WPA3 para proteger contra roubo de credenciais, que é um vetor para alunos que tentam acessar redes de funcionários para contornar a filtragem.
- Alinhamento de Conformidade: No Reino Unido, garanta que suas políticas de filtragem atendam aos requisitos básicos descritos no IWF Compliance for Public WiFi Networks in the UK (ou Cumplimiento IWF para redes WiFi públicas en el Reino Unido para operações em espanhol).
- Revisão Regular: As redes de anúncios mudam constantemente de domínios para evadir as listas de bloqueio. Garanta que sua solução de filtragem utilize feeds de inteligência de ameaças atualizados dinamicamente em vez de listas estáticas.
Solução de Problemas e Mitigação de Riscos
| Modo de Falha | Causa Raiz | Estratégia de Mitigação |
|---|---|---|
| Bypass via DNS Criptografado | Alunos configurando navegadores para usar DoH/DoT (por exemplo, Cloudflare, Google DNS). | Bloqueie endereços IP de provedores DoH conhecidos no firewall; force a resolução DNS local via DHCP. |
| Bypass via VPN | Uso de clientes VPN comerciais ou extensões de navegador. | Bloqueie protocolos VPN comuns (IPsec, OpenVPN, WireGuard) e domínios de provedores VPN conhecidos em VLANs de estudantes. |
| Bloqueio Excessivo (Falsos Positivos) | Filtragem heurística agressiva bloqueando conteúdo educacional. | Implemente um processo simplificado de solicitação de lista de permissões com suporte a SLA para a equipe de ensino; teste as políticas minuciosamente antes da implantação completa. |
| Vazamento de IPv6 | Filtragem aplicada apenas a IPv4, permitindo bypass via resolução DNS IPv6. | Garanta que a solução de filtragem e a infraestrutura de rede suportem e apliquem totalmente as políticas em toda a pilha IPv6. |
ROI e Impacto nos Negócios
O caso de negócios para o bloqueio de anúncios em nível de rede vai além da proteção; ele oferece eficiências operacionais mensuráveis.
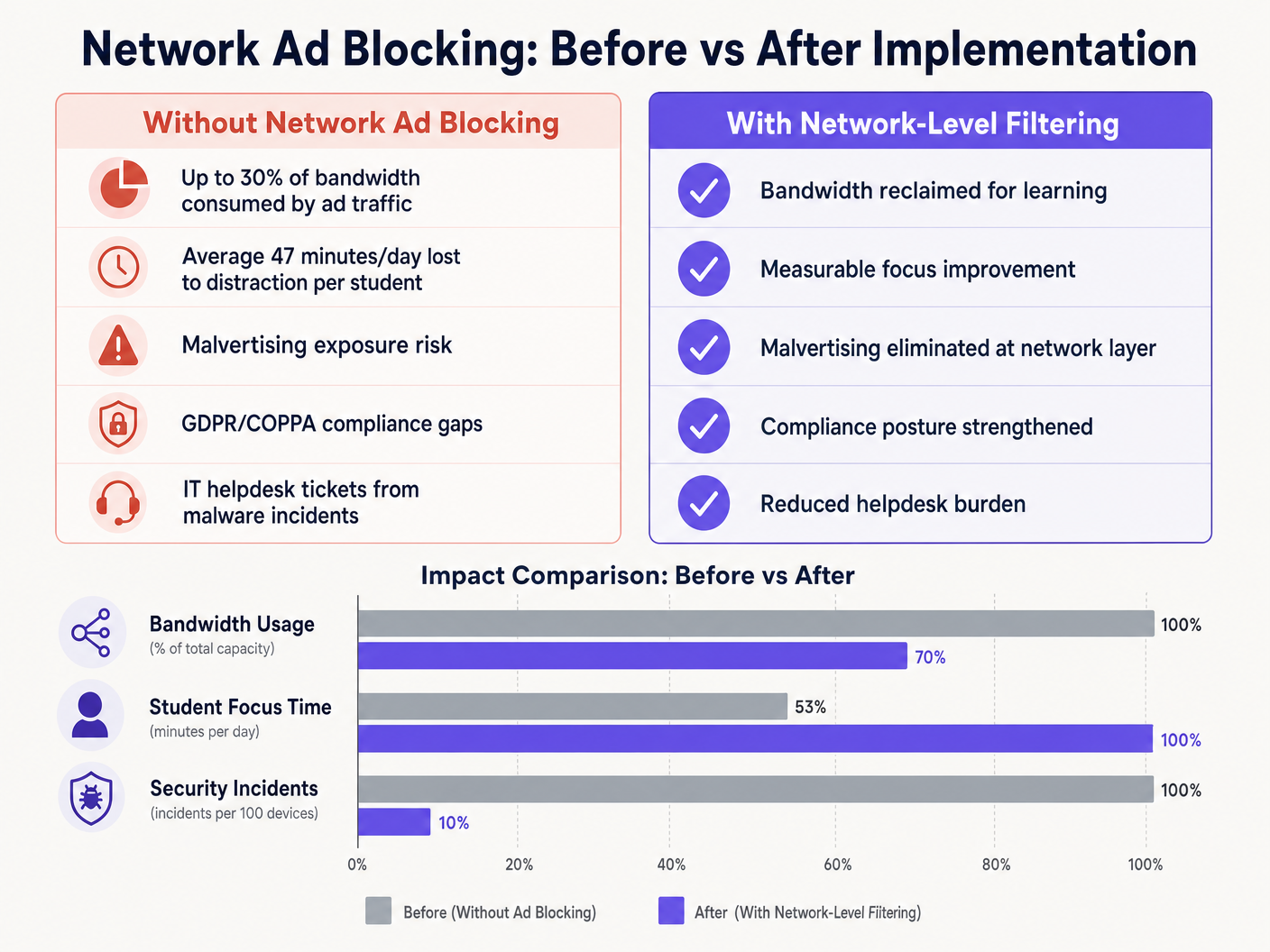
Ao eliminar cargas de anúncios e scripts de rastreamento na borda da rede, os locais geralmente recuperam de 15% a 30% de sua largura de banda total. Essa capacidade recuperada adia a necessidade de atualizações caras de circuitos e melhora o desempenho de aplicativos críticos na nuvem. Além disso, o bloqueio de domínios de malvertising na camada DNS reduz significativamente o volume de incidentes de malware, diminuindo diretamente o volume de tickets do helpdesk de TI e os custos de remediação.
Seja implantando em uma escola, otimizando Office Wi Fi: Optimize Your Modern Office Wi-Fi Network , ou gerenciando ambientes de alta densidade em Varejo , Saúde , Hotelaria , ou Transporte , compreender a camada física, como Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 , e proteger a camada lógica através da filtragem DNS são componentes essenciais da arquitetura de rede moderna.
Definições principais
DNS Filtering
The process of using the Domain Name System to block malicious websites and filter out harmful or unwanted content by returning a null IP address for blocked domains.
The primary mechanism for network-level ad blocking, operating upstream of client devices.
DNS-over-HTTPS (DoH)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
A common method used to bypass local network DNS filtering policies.
Malvertising
The use of online advertising to spread malware, often through legitimate advertising networks without the publisher's knowledge.
A key security risk mitigated by network-level ad blocking.
SSL Inspection
The process of intercepting, decrypting, and inspecting HTTPS traffic for malicious content or policy violations before re-encrypting and forwarding it.
Required for deep packet inspection of encrypted web traffic, though complex to deploy in BYOD environments.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Used to identify users and devices to apply differentiated filtering policies.
WPA3-Enterprise
The latest generation of Wi-Fi security, providing enhanced cryptographic strength and protecting against dictionary attacks.
Essential for securing campus networks and ensuring users cannot easily spoof identities to bypass filtering.
VLAN (Virtual Local Area Network)
A logical subnetwork that groups a collection of devices from different physical LANs.
Used to segment student, staff, and guest traffic to apply different security and filtering policies.
Transparent Proxy
An intermediary system that sits between a user and a content provider, intercepting requests without requiring client-side configuration.
Used to enforce URL-level filtering policies without deploying endpoint agents.
Exemplos práticos
A large multi-academy trust with 15,000 students across 12 campuses needs to implement ad blocking. They currently use a mix of school-issued Chromebooks and a BYOD policy for sixth-form students. The network is struggling with bandwidth congestion during peak hours.
- Deploy a cloud-managed DNS filtering solution across all 12 campuses, pointing all DHCP-assigned DNS settings to the cloud resolvers.
- Configure the firewall to block outbound port 53 traffic to any external IP other than the approved cloud resolvers to prevent manual DNS overrides.
- Block known DoH provider IPs at the firewall.
- Integrate the DNS filtering solution with the trust's Active Directory via 802.1X to apply different filtering policies: a strict policy for the Chromebook VLAN and a slightly more permissive policy for the BYOD VLAN, while maintaining core ad and malvertising blocking across both.
A university campus IT team receives complaints from the Computer Science faculty that the new network ad blocking solution is preventing access to legitimate development tools and APIs used in coursework.
- Review the DNS query logs for the Computer Science VLAN to identify the specific domains being blocked.
- Create a dedicated policy group for the Computer Science faculty and student VLANs.
- Implement a scoped whitelist for the required development domains, applying it only to the Computer Science policy group to maintain security across the rest of the campus.
- Establish a fast-track IT ticketing category specifically for 'Educational Content Blocking' to handle future requests with a 2-hour SLA.
Questões práticas
Q1. You have deployed DNS filtering across the campus network, but monitoring shows that a significant number of student BYOD devices are still loading ads and accessing restricted content. What is the most likely cause, and how should you address it?
Dica: Consider how modern browsers handle DNS queries independently of the operating system's network settings.
Ver resposta modelo
The most likely cause is that modern browsers on the BYOD devices are using DNS-over-HTTPS (DoH) to bypass the local network's DNS resolver. To address this, configure the perimeter firewall to block known DoH provider IP addresses and drop outbound traffic on port 53 that does not originate from the approved campus DNS resolvers. This forces the devices to fall back to the local, filtered DNS infrastructure.
Q2. The school's leadership team wants to block all social media and advertising networks globally across the entire campus to ensure maximum compliance. As the IT Director, why might you advise against a single global policy, and what architecture would you propose instead?
Dica: Consider the different user groups on campus and their specific needs.
Ver resposta modelo
A single global policy will inevitably cause operational friction. Staff may need access to social media for communications or marketing, and certain ad networks may be required for legitimate educational tools. Instead, propose a segmented architecture using 802.1X integration to apply identity-aware policies. Create distinct VLANs and policy groups for Students, Staff, and Guests, applying strict blocking to students while allowing necessary access for staff.
Q3. Before switching the new DNS filtering solution into active enforcement mode, what critical operational process must be established with the IT helpdesk?
Dica: Think about the impact of false positives on teaching staff.
Ver resposta modelo
A rapid-response whitelist request process must be established. Heuristic filtering will inevitably block some legitimate educational resources (false positives). Without a fast, SLA-backed process for teachers to request domains be unblocked, the deployment will disrupt learning and cause stakeholder resistance.