Que Tipos de Dados de Clientes o WiFi Pode Capturar?
Este guia completo detalha as quatro categorias principais de dados de clientes capturados por plataformas empresariais de WiFi: identidade, comportamental, declarado e metadados de dispositivo. Ele oferece orientação acionável sobre arquitetura, conformidade e implantação para líderes de TI transformarem a infraestrutura de rede de convidados em um ativo de dados primários seguro.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: As Quatro Categorias de Dados WiFi
- 1. Dados de Identidade (Identificadores Declarados)
- 2. Dados Comportamentais (Análise de Rede)
- 3. Dados Declarados (Progressive Profiling)
- 4. Metadados de Dispositivo e Rede
- Guia de Implementação: Arquitetando para Captura de Dados
- Superando a Randomização de MAC
- Progressive Profiling vs. Atrito
- Melhores Práticas e Conformidade
- ROI e Impacto nos Negócios

Resumo Executivo
Para locais empresariais — desde propriedades de Varejo até grupos de Hotelaria — o WiFi para convidados evoluiu de uma comodidade básica para um canal crítico de aquisição de dados. No entanto, muitas organizações ainda implementam redes sem fio como pura infraestrutura de TI, perdendo a oportunidade de capturar inteligência de cliente primária e de alto sinal. Este guia detalha os tipos exatos de dados de clientes que uma plataforma empresarial de Guest WiFi pode capturar, a arquitetura técnica necessária para fazê-lo com segurança e as estruturas de conformidade necessárias para protegê-los. Exploramos as quatro categorias de dados primárias: identidade, comportamental, declarado e metadados de dispositivo. Para CTOs e arquitetos de rede, o objetivo é claro: implementar uma camada robusta de WiFi Analytics que ofereça ROI mensurável através do enriquecimento de CRM, enquanto adere estritamente aos princípios de minimização de dados e GDPR.
Análise Técnica Aprofundada: As Quatro Categorias de Dados WiFi
Quando um usuário se associa a uma rede sem fio empresarial, a plataforma pode capturar dados em quatro categorias distintas. Compreender os mecanismos técnicos e as limitações de cada uma é essencial para uma implantação eficaz.
1. Dados de Identidade (Identificadores Declarados)
Os dados de identidade são fornecidos explicitamente pelo usuário durante o processo de autenticação no Captive Portal (página de splash). Esta é a base da sua estratégia de dados primários.
- Endereço de E-mail e Número de Telefone: Capturados através de campos de formulário padrão. Estes servem como os principais identificadores persistentes para integração com CRM.
- Perfil de Login Social: Capturado via integração OAuth (por exemplo, Facebook, Google, Apple). Dependendo do consentimento do usuário, isso pode gerar dados de perfil ricos, incluindo nome, faixa etária e e-mail verificado.
Nota de Arquitetura Técnica: A captura de dados de identidade deve ser acoplada a um registro de consentimento auditável. A plataforma deve registrar o carimbo de data/hora, endereço IP, endereço MAC e os Termos e Condições específicos apresentados ao usuário. A arquitetura da Purple automatiza este registro para garantir a conformidade com o Artigo 7 do GDPR.
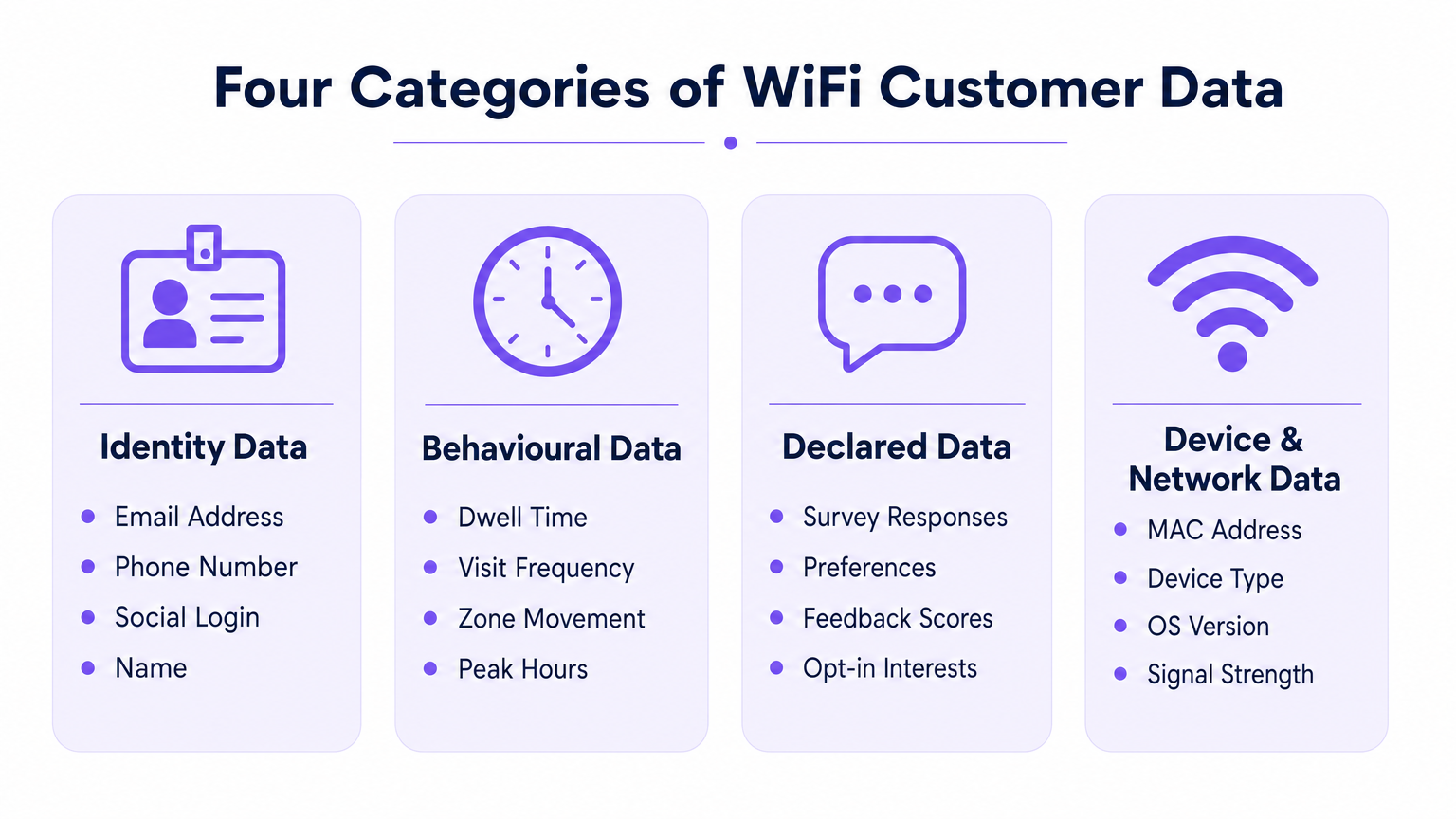
2. Dados Comportamentais (Análise de Rede)
Os dados comportamentais são derivados passivamente da interação do dispositivo com a infraestrutura de rede. Não requerem entrada ativa do usuário além de manter uma conexão.
- Presença e Tempo de Permanência: A duração em que um dispositivo permanece associado à rede. Tempos de permanência elevados em zonas específicas (por exemplo, um bar de hotel ou um expositor de varejo) correlacionam-se fortemente com a intenção de conversão.
- Frequência e Recência de Visitas: Rastreamento da diferença entre visitas para distinguir visitantes de primeira viagem de clientes fiéis que retornam.
- Movimento Nível de Zona: Ao triangular dados do Indicador de Força do Sinal Recebido (RSSI) através de múltiplos pontos de acesso, as plataformas podem mapear as jornadas dos usuários através de um espaço físico. Para uma análise mais aprofundada da tecnologia subjacente, consulte nosso guia sobre Sistema de Posicionamento Interno: Guia UWB, BLE e WiFi .
3. Dados Declarados (Progressive Profiling)
Os dados declarados vão além da identidade básica, capturando preferências explícitas diretamente do usuário. Esses dados possuem a mais alta qualidade de sinal porque dependem de entrada direta, e não de inferência.
- Respostas a Pesquisas: Pesquisas pós-autenticação ou pós-visita (por exemplo, Net Promoter Score, feedback sobre instalações).
- Captura de Preferências: Solicitações durante a sessão que coletam interesses específicos (por exemplo, requisitos dietéticos em Saúde ou interesses de produtos no varejo).
4. Metadados de Dispositivo e Rede
Esses dados são gerados pelo hardware do dispositivo e pelo sistema operacional durante o processo de associação 802.11.
- Endereço MAC: O identificador de hardware. Restrição crucial: Desde o iOS 14 e Android 10, a randomização de MAC por rede é o padrão. Endereços MAC não podem mais ser usados de forma confiável como identificadores persistentes entre visitas sem um registro de usuário autenticado.
- Tipo de Dispositivo e Versão do SO: Extraídos da string HTTP User-Agent durante a renderização do portal ou via DHCP fingerprinting.
- Uso de Dados: Métricas de throughput (volume de upload/download), que auxiliam no planejamento de capacidade e na identificação de usuários com alto consumo de largura de banda.
Guia de Implementação: Arquitetando para Captura de Dados
A implantação de uma rede WiFi centrada em dados requer decisões arquitetônicas que equilibrem a experiência do usuário com o rendimento de dados.
Superando a Randomização de MAC
A mudança arquitetônica mais significativa nos últimos anos é a depreciação do endereço MAC como um identificador persistente. Para rastrear visitas repetidas com precisão, a arquitetura deve ancorar o perfil do usuário à credencial autenticada (e-mail/telefone) em vez do hardware do dispositivo.
- Início da Sessão: O dispositivo se conecta com um MAC randomizado.
- Autenticação: O usuário fornece e-mail via Captive Portal.
- Vinculação de Perfil: A plataforma vincula a sessão MAC randomizada atual ao perfil de e-mail persistente.
- Visitas Subsequentes: Se o dispositivo apresentar um novo MAC randomizado, o usuário deve se reautenticar (muitas vezes de forma transparente via um fluxo de usuário recorrente ou autenticação baseada em perfil como OpenRoaming) para revincular a sessão ao seu perfil.
Progressive Profiling vs. Atrito
Não solicite todos os pontos de dados na primeira conexão. Captive Portals de alta fricção sofrem com altas taxas de abandono. Implemente o progressive profiling: à medida quek para um endereço de e-mail na primeira visita, um número de telefone na terceira visita e uma pesquisa de preferência na quinta visita.
Para orientações específicas sobre como proteger esses dados após a captura, consulte Como Proteger Dados de Clientes Coletados via WiFi .
Melhores Práticas e Conformidade
Trate o WiFi para convidados como um projeto de estratégia de dados, não apenas uma implantação de TI. A conformidade deve ser incorporada à arquitetura desde o primeiro dia.
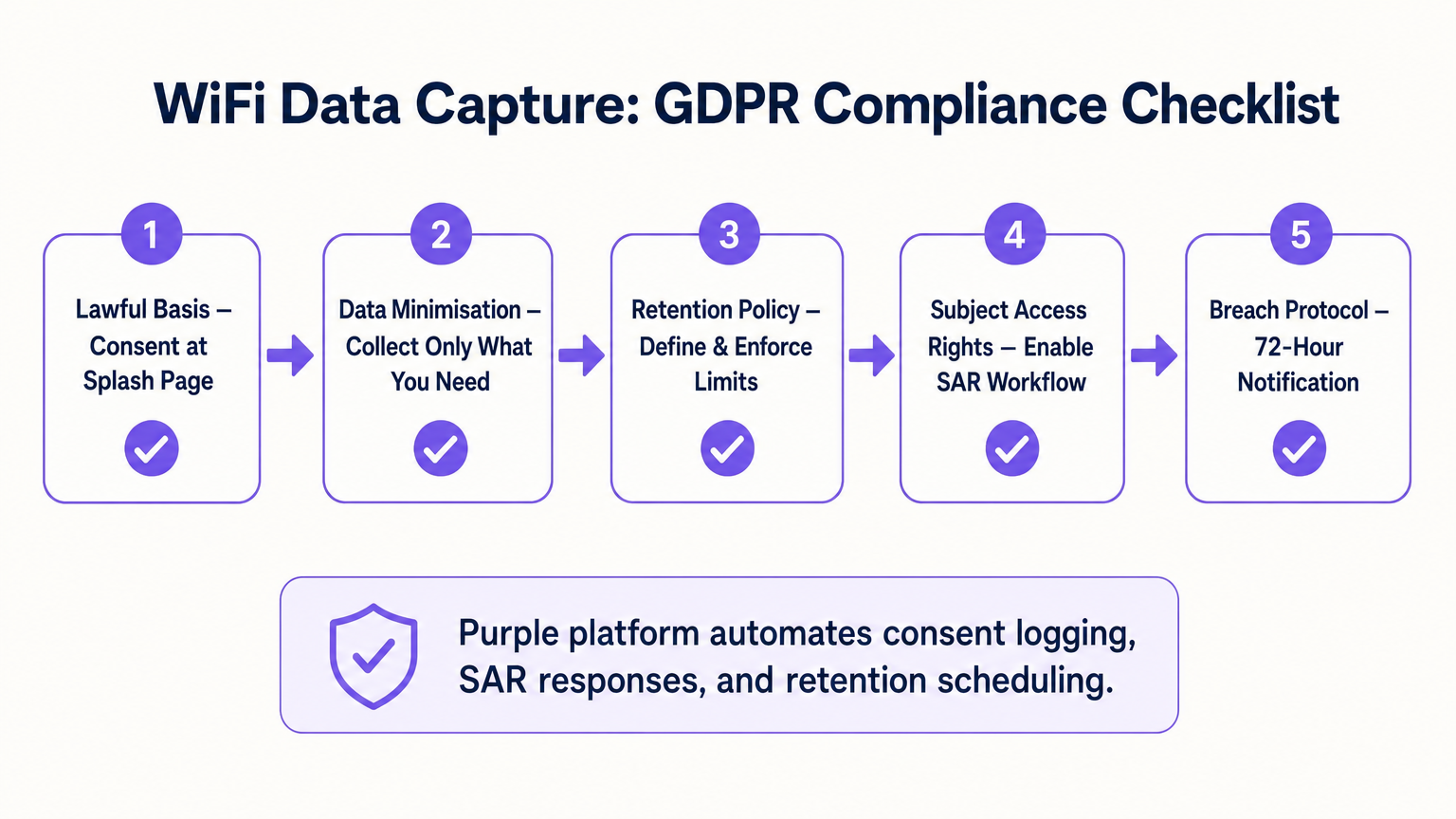
- Base Legal e Consentimento: Garanta que o captive portal separe explicitamente a aceitação dos Termos de Serviço do Consentimento de Marketing. Caixas pré-selecionadas não estão em conformidade com a GDPR.
- Minimização de Dados: Colete apenas os dados para os quais você tem um caso de uso comercial. Se você não tem uma estratégia de marketing por SMS, não exija a coleta de número de telefone.
- Retenção Automatizada: Configure a plataforma para limpar automaticamente perfis inativos após um período definido (por exemplo, 24 meses) para cumprir os princípios de limitação de armazenamento.
- Solicitações de Acesso do Titular (SAR): Garanta que sua plataforma tenha um fluxo de trabalho automatizado para exportar ou excluir os dados de um usuário dentro do prazo legal de 30 dias após a solicitação.
ROI e Impacto nos Negócios
O ROI de uma plataforma de análise de WiFi é medido por sua integração com o stack de martech mais amplo. Ao enviar dados de identidade, comportamentais e declarados via API para plataformas como Salesforce ou HubSpot, os locais podem acionar fluxos de trabalho automatizados. Por exemplo, um hub de Transporte pode enviar automaticamente um e-mail com um desconto para o lounge a um passageiro cujo tempo de permanência exceda 45 minutos. O impacto final nos negócios é a conversão de tráfego anônimo em um banco de dados segmentado e comercializável.
Termos-Chave e Definições
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted. It is the primary mechanism for capturing identity data and consent.
IT teams configure this to balance security, branding, and data capture requirements.
MAC Randomisation
A privacy feature in modern OSs (iOS, Android) where the device generates a temporary, random MAC address for each specific WiFi network it joins, preventing cross-network tracking.
This forces network architects to rely on authenticated user profiles rather than hardware identifiers for repeat visit tracking.
Dwell Time
The total duration a device remains continuously associated with the WiFi network or a specific zone within the network.
Used by operations and marketing to gauge engagement, queue lengths, or intent to purchase.
Progressive Profiling
The practice of collecting user data incrementally over multiple sessions rather than demanding all information during the initial interaction.
Crucial for maintaining high WiFi connection rates while still building rich customer profiles over time.
First-Party Data
Information a company collects directly from its customers and owns entirely, typically gathered via direct interactions like WiFi authentication.
Highly valuable as third-party cookies deprecate; it provides the most accurate and compliant foundation for marketing.
Received Signal Strength Indicator (RSSI)
A measurement of the power present in a received radio signal. Used in WiFi analytics to estimate the distance between a device and an access point.
The technical metric underlying zone-level movement tracking and indoor positioning.
Subject Access Request (SAR)
A mechanism under GDPR allowing individuals to request a copy of their personal data, or request its deletion.
IT must ensure the WiFi platform can easily query and export or purge specific user records to meet the 30-day compliance window.
Data Minimisation
The principle that a data controller should limit the collection of personal information to what is directly relevant and necessary to accomplish a specified purpose.
A core compliance requirement; prevents venues from hoarding unnecessary data that increases breach liability.
Estudos de Caso
A 200-room hotel needs to increase direct bookings and reduce OTA (Online Travel Agency) commissions. They currently offer open, unauthenticated WiFi.
The hotel deploys a captive portal requiring email or social authentication. They implement progressive profiling: on the first connection, they capture email and marketing consent. On the third connection during the stay, a micro-survey captures the reason for travel (Business/Leisure). Post-checkout, the CRM uses the WiFi identity data to send a targeted 'Book Direct' offer for their next stay, bypassing the OTA.
A large retail chain wants to measure the impact of a new store layout on customer engagement, but their current WiFi only tracks total daily connections.
The IT team upgrades the network to support zone-level analytics by calibrating multiple access points. They define virtual zones within the analytics platform corresponding to key departments. They can now measure not just presence, but 'Zone Dwell Time'. By comparing dwell times in the newly laid-out zones against historical benchmarks, they quantify the layout's impact on engagement.
Análise de Cenário
Q1. Your marketing team wants to track how often specific customers return to your stadium over a season. The current network uses open access (no portal) and tracks MAC addresses. Why will this fail, and what must you change?
💡 Dica:Consider recent changes in mobile operating system privacy features.
Mostrar Abordagem Recomendada
It will fail due to MAC randomisation; modern devices present a different MAC address on subsequent visits, breaking the tracking. You must implement a captive portal to force authentication (e.g., via email or ticketing integration) and anchor the repeat visit tracking to that persistent user credential rather than the hardware MAC.
Q2. A venue director requests that the new WiFi splash page collects Name, Email, Phone, Date of Birth, Postcode, and Dietary Preferences to build a comprehensive CRM database immediately. How should the IT architect respond?
💡 Dica:Balance data yield against the user experience and connection drop-off rates.
Mostrar Abordagem Recomendada
The architect should advise against this due to the Friction vs. Yield trade-off. A 6-field form will cause massive connection abandonment. Instead, recommend progressive profiling: capture Name and Email on the first visit, and use subsequent visits to prompt for Phone or Dietary Preferences. Furthermore, under data minimisation principles, Date of Birth should not be collected unless there is a strict legal requirement (e.g., age-gated venues).
Q3. During a security audit, the compliance team asks how the WiFi platform proves that a user opted into marketing communications. What specific data points must the system be able to produce?
💡 Dica:Think about the requirements of GDPR Article 7 regarding the demonstration of consent.
Mostrar Abordagem Recomendada
The system must produce a definitive audit trail for that specific user. This includes the timestamp of the consent action, the IP address and MAC address used during the session, the exact version of the Terms & Conditions/Privacy Policy presented at that time, and the specific checkbox (which must have been actively opted-in, not pre-ticked) that the user interacted with.



