DNS Over HTTPS (DoH): Implicações para a Filtragem de WiFi Público
Este guia de referência técnica explica como o DNS over HTTPS (DoH) contorna a filtragem de conteúdo tradicional na porta 53 em redes WiFi públicas. Fornece estratégias de mitigação acionáveis e neutras em relação ao fornecedor para arquitetos de rede e gestores de TI recuperarem a visibilidade, imporem a conformidade e protegerem o acesso de convidados em ambientes empresariais.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada: O Mecanismo de Bypass DoH
- Padrões de Implementação: DoH ao Nível da Aplicação vs. DoH ao Nível do SO
- Guia de Implementação: Uma Arquitetura de Defesa em Profundidade
- Camada 1: Bloquear Endpoints de Resolvedores DoH Conhecidos
- Camada 2: Impor Interceção e Redirecionamento da Porta 53
- Camada 3: Bloquear a Porta 853 (DNS over TLS)
- Melhores Práticas e Considerações de Conformidade
- Resolução de Problemas e Mitigação de Riscos
- Regras de Interceção Incompletas
- Falhas de IPv6
- Quebra de Aplicações
- ROI e Impacto no Negócio
Resumo Executivo
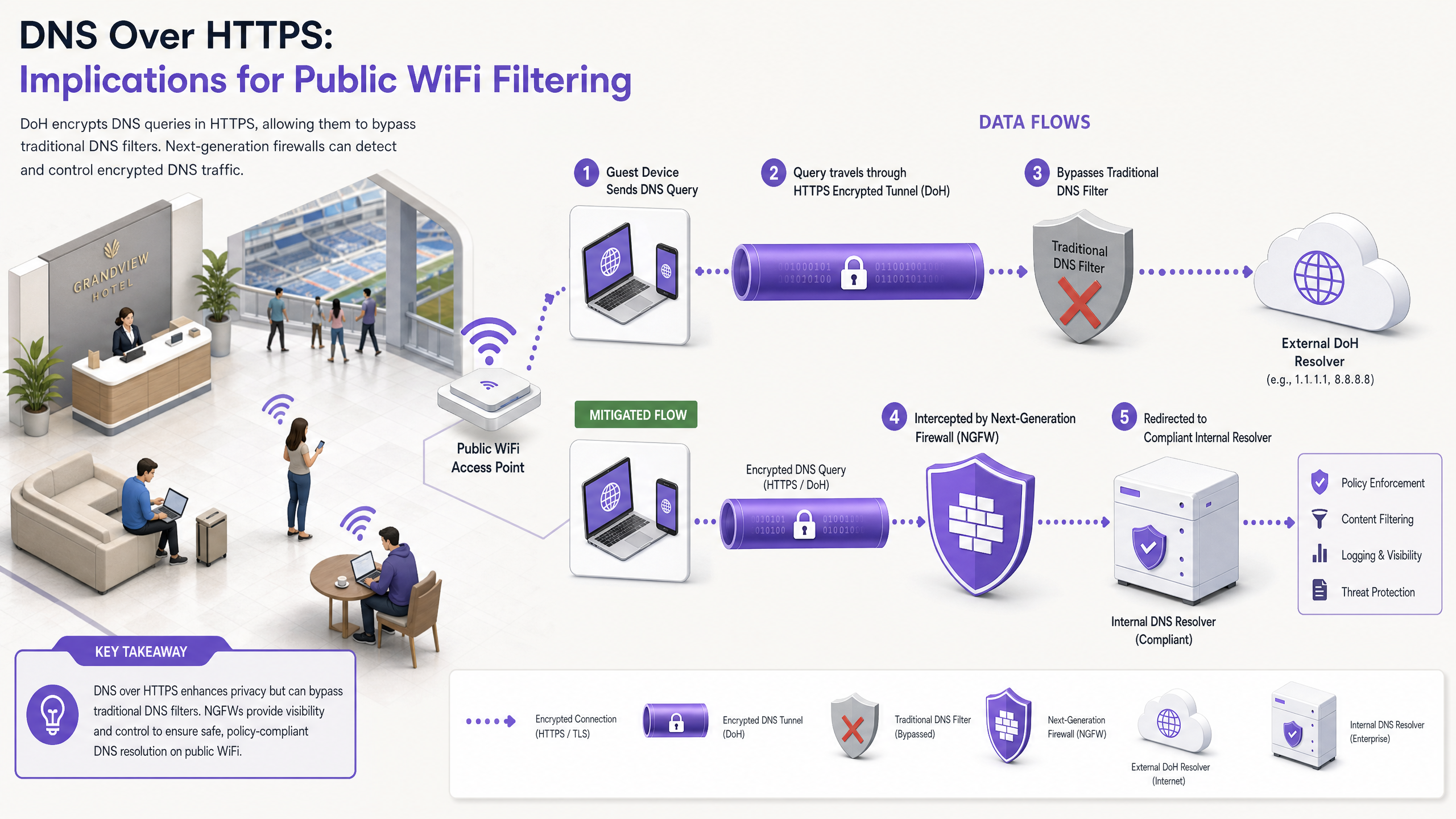
Durante quase uma década, a filtragem DNS tradicional na porta 53 serviu como o principal mecanismo para impor políticas de conteúdo e mitigar ameaças de malware em redes WiFi públicas. No entanto, a adoção generalizada de DNS over HTTPS (DoH) por navegadores e sistemas operativos convencionais perturba fundamentalmente este modelo. Ao encapsular consultas DNS dentro do tráfego HTTPS padrão na porta 443, o DoH torna estas consultas invisíveis às técnicas tradicionais de interceção de rede.
Para gestores de TI empresariais e arquitetos de rede que operam WiFi para convidados em Hotelaria , Retalho , estádios e locais do setor público, isto representa uma lacuna significativa de conformidade e segurança. Quando os dispositivos dos convidados contornam silenciosamente os resolvedores DNS designados do local, as políticas de utilização aceitável cuidadosamente construídas falham, expondo a rede ao tráfego de malware de comando e controlo (C2) e a conteúdo inadequado. Este guia detalha a mecânica do vetor de bypass DoH e fornece uma arquitetura de defesa em profundidade e em camadas para recuperar a visibilidade da rede, garantir a conformidade regulamentar e manter uma segurança robusta do WiFi para Convidados .
Análise Técnica Detalhada: O Mecanismo de Bypass DoH
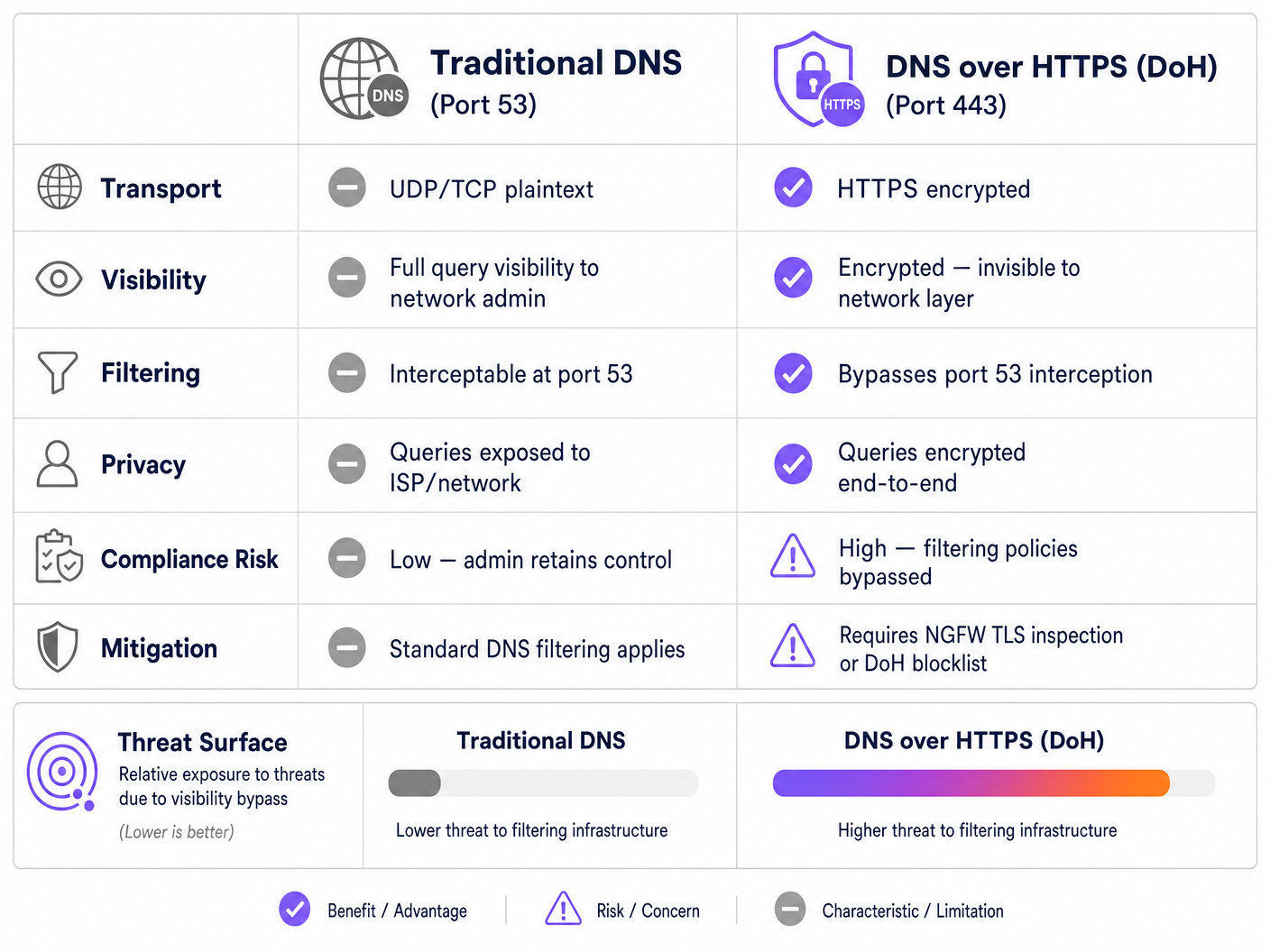
Para entender o vetor de ameaça DoH, é preciso primeiro examinar a arquitetura base da filtragem DNS tradicional. Historicamente, quando um dispositivo de convidado se conectava a uma rede pública e solicitava um domínio, a consulta era transmitida em texto simples através da porta UDP ou TCP 53. Os administradores de rede podiam facilmente intercetar este tráfego na firewall ou no controlador sem fios, redirecionando-o para um resolvedor DNS compatível que verificava o domínio solicitado em relação a feeds de inteligência de ameaças e políticas de categorização de conteúdo.
O DNS over HTTPS contorna todo este plano de controlo. Por design, o DoH encripta a consulta DNS e transmite-a para um resolvedor externo (como o 1.1.1.1 da Cloudflare ou o 8.8.8.8 da Google) usando encriptação TLS padrão sobre a porta 443. Da perspetiva da infraestrutura de rede do local, uma consulta DoH é indistinguível de um utilizador a navegar num site seguro ou a transmitir um vídeo.
Padrões de Implementação: DoH ao Nível da Aplicação vs. DoH ao Nível do SO
O desafio para os administradores de rede é agravado pela forma como o DoH é implementado em diferentes plataformas. Existem dois padrões de implementação principais:
- DoH ao Nível da Aplicação: Neste modelo, a aplicação mantém a sua própria configuração DoH independentemente do sistema operativo anfitrião. O Mozilla Firefox é o exemplo canónico; quando o DoH está ativado, o Firefox ignora os servidores DNS atribuídos por DHCP e encaminha todas as consultas para o seu fornecedor DoH preferido. As regras de interceção da porta 53 do local são totalmente contornadas.
- DoH ao Nível do SO (Oportunista): Sistemas operativos modernos, incluindo Windows 11 e Android, empregam DoH oportunista. O SO verifica se o resolvedor DNS atribuído por DHCP tem um endpoint DoH conhecido. Se for encontrada uma correspondência, o SO atualiza automaticamente a ligação para DoH. Embora isto preserve a escolha do resolvedor pelo administrador, ainda desvia o tráfego para a porta 443, o que pode contornar ferramentas de monitorização legadas que esperam tráfego na porta 53.
Além disso, os administradores devem ter em conta o DNS over TLS (DoT), que opera na porta 853. Embora o DoT seja mais fácil de bloquear devido à sua porta dedicada, é o padrão predefinido para a funcionalidade "Private DNS" do Android e representa um risco de bypass idêntico se a porta 853 for deixada aberta na VLAN de convidados.
Guia de Implementação: Uma Arquitetura de Defesa em Profundidade
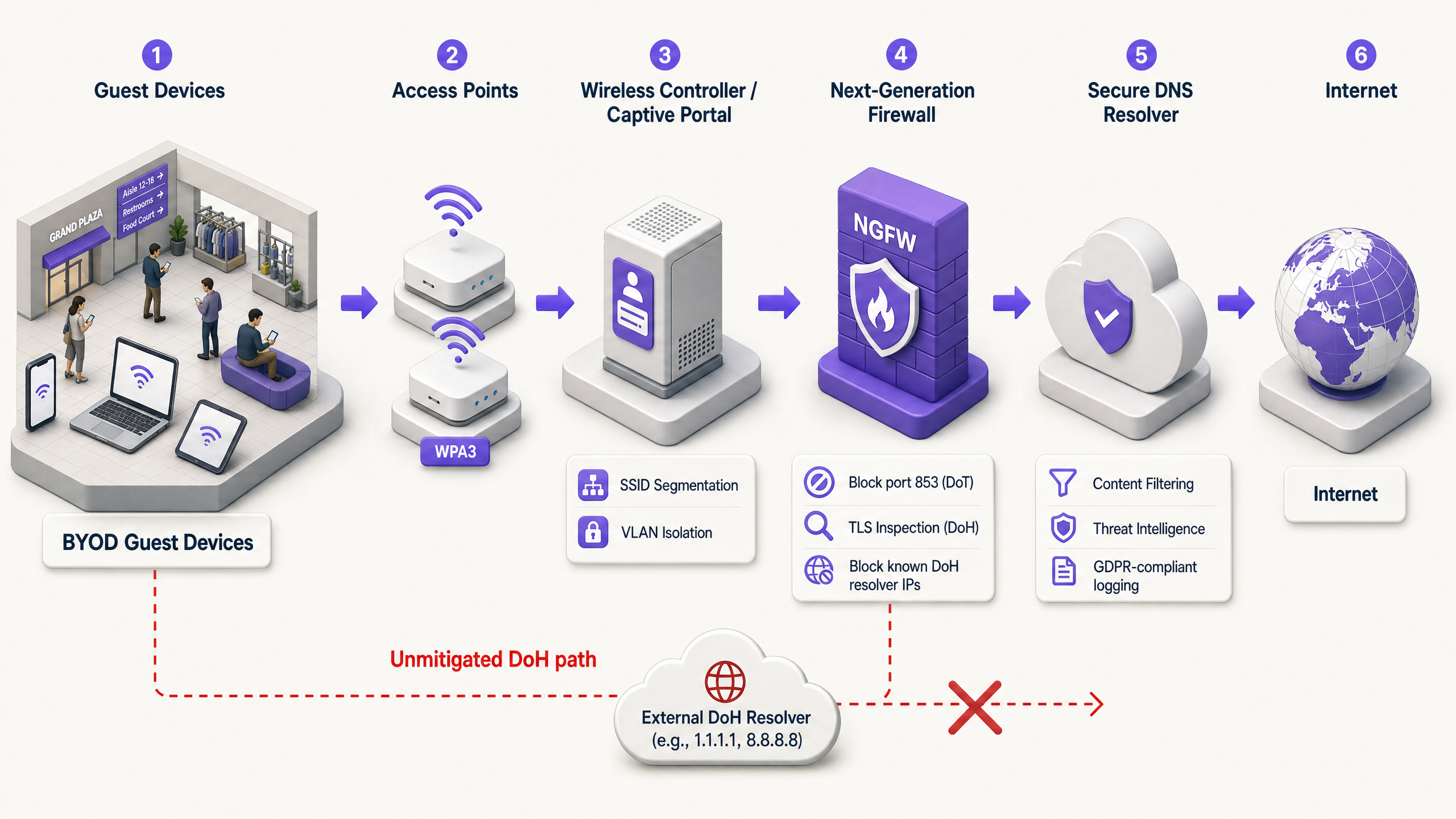
Recuperar o controlo sobre a resolução DNS requer uma estratégia de mitigação em várias camadas. Confiar num único ponto de controlo é insuficiente contra protocolos modernos e encriptados. Os arquitetos de rede devem implementar a seguinte arquitetura para proteger o acesso de convidados e garantir a conformidade com frameworks como PCI DSS e GDPR.
Camada 1: Bloquear Endpoints de Resolvedores DoH Conhecidos
A mitigação mais imediata e eficaz é bloquear o tráfego HTTPS de saída para resolvedores DoH públicos conhecidos na extremidade da rede. Embora o tráfego DoH se misture com o HTTPS padrão, os endereços IP de destino e os domínios dos principais fornecedores de DoH estão bem documentados.
Ao configurar a Firewall de Próxima Geração (NGFW) para descartar ligações a estes endpoints específicos (por exemplo, dns.google, cloudflare-dns.com), os administradores forçam a resolução DoH do dispositivo cliente a falhar. Na maioria das implementações, quando o DoH falha, o cliente voltará graciosamente ao DNS tradicional e não encriptado na porta 53, que pode então ser intercetado e filtrado.
Nota de Implementação: Esta abordagem requer a manutenção de uma lista de bloqueio atualizada. Os fornecedores de firewalls empresariais geralmente fornecem feeds de ameaças dinâmicos que atualizam automaticamente os endpoints DoH conhecidos, reduzindo significativamente a sobrecarga operacional.
Camada 2: Impor Interceção e Redirecionamento da Porta 53
Bloquear o DoH só é eficaz se o tráfego de fallback for gerido corretamente. A rede deve ser configurada para intercetar todo o tráfego UDP e TCP de saída na porta 53 originário da VLAN de convidados. Este tráfego deve ser redirecionado forçosamente (através de regras NAT/encaminhamento de portas) para o resolvedor DNS aprovado e compatível do local.
Este passo é crítico porque muitos dispositivos ou aplicações maliciosas codificam servidores DNS públicos (por exemplo, 8.8.8.8) na sua pilha de rede, ignorando as configurações fornecidas por DHCP. Sem interceção forçada, estes dispositivos contornarão com sucesso as políticas de filtragem do local, mesmo que o DoH seja bloqueado.
Camada 3: Bloquear a Porta 853 (DNS over TLS)
Para abordar o vetor de bypass DoT, os administradores devem bloquear explicitamente o tráfego de saída na porta TCP 853 da rede de convidados. Semelhante à mitigação DoH, blocking DoT força os dispositivos Android e outros clientes compatíveis com DoT a recorrer ao DNS padrão da porta 53.
Melhores Práticas e Considerações de Conformidade
A implementação da mitigação de DoH não é meramente um exercício técnico; é um requisito fundamental para manter a conformidade regulamentar e aplicar políticas de utilização aceitável.
- Documentação da Política: Garanta que os termos e condições do Captive Portal do local declarem explicitamente que a filtragem de DNS está em vigor para fins de segurança e conformidade. Isso proporciona defesa legal sob o GDPR e a Lei de Segurança Online do Reino Unido ao bloquear protocolos DNS encriptados.
- Segmentação de Rede: O Guest WiFi deve ser estritamente isolado das redes corporativas e de pagamento usando VLANs e regras de firewall. Este é um requisito central do PCI DSS v4.0, que também exige monitorização robusta do tráfego de rede — monitorização que é impossível se o DoH for permitido para contornar os controlos de segurança.
- Monitorização Contínua: Aproveite as capacidades de relatório do seu serviço de filtragem de DNS empresarial para monitorizar volumes de consultas e identificar padrões anómalos. Uma queda súbita no tráfego da porta 53 de uma sub-rede específica frequentemente indica que um novo resolvedor DoH, não bloqueado, está a ser utilizado pelos dispositivos cliente.
- Integração com Análise: Ao implementar acesso seguro para convidados, considere como o fluxo de autenticação se integra com objetivos de negócio mais amplos. A utilização de um wi fi assistant para autenticação segura baseada em perfil garante que os utilizadores se conectam em segurança, permitindo que o local aproveite o WiFi Analytics para entender o fluxo de visitantes e os tempos de permanência, de forma semelhante a como o Offline Maps Mode melhora a experiência do visitante.
Resolução de Problemas e Mitigação de Riscos
Ao implementar a mitigação de DoH, as equipas de rede frequentemente encontram modos de falha específicos. Antecipar estes problemas reduz o tempo de inatividade e o atrito com os convidados.
Regras de Interceção Incompletas
A falha de implementação mais comum é a interceção incompleta da porta 53. Os administradores podem configurar o servidor DHCP para distribuir os IPs de DNS corretos, mas falham em implementar as regras NAT do firewall necessárias para capturar pedidos de DNS codificados. Mitigação: Teste sempre a implementação configurando um dispositivo cliente com um servidor DNS estático e externo (por exemplo, 9.9.9.9) e verificando se os pedidos ainda são encaminhados com sucesso para o serviço de filtragem do local.
Falhas de IPv6
À medida que as redes transitam para configurações dual-stack, as regras de firewall são frequentemente escritas exclusivamente para IPv4. Se as listas de bloqueio de DoH e as regras de interceção da porta 53 não cobrirem o IPv6, os dispositivos modernos contornarão sem problemas os controlos de IPv4 usando a sua pilha IPv6. Mitigação: Garanta que todas as listas de bloqueio de DoH, regras de redirecionamento da porta 53 e regras de descarte da porta 853 sejam aplicadas simetricamente em ambas as tabelas de encaminhamento IPv4 e IPv6.
Quebra de Aplicações
O bloqueio agressivo de DoH pode ocasionalmente quebrar aplicações móveis específicas que dependem exclusivamente da sua própria implementação de DoH e recusam-se a recorrer ao DNS padrão. Mitigação: Mantenha um processo de exceção documentado. Se uma aplicação crítica para o negócio falhar, utilize a inspeção TLS (se disponível no NGFW) para permitir seletivamente o tráfego DoH para o resolvedor dessa aplicação específica, em vez de abrir o DoH globalmente.
ROI e Impacto no Negócio
O caso de negócio para uma mitigação robusta de DoH está enraizado na prevenção de riscos e na garantia de conformidade. Um único incidente — como um convidado a aceder a conteúdo ilegal resultando numa investigação regulamentar, ou um dispositivo IoT comprometido a estabelecer uma conexão C2 via DoH — pode incorrer em custos que excedem em muito o tempo de engenharia necessário para implementar os controlos adequados.
Para uma empresa que opera em vários locais, a padronização da arquitetura de mitigação de DoH garante uma aplicação consistente da política. Esta padronização reduz a carga operacional sobre o serviço de apoio de TI, uma vez que as notificações de abuso dos ISPs caem para zero e o desempenho da rede é preservado ao bloquear conteúdo inadequado de alta largura de banda. Em última análise, proteger a camada DNS garante que o investimento do local em Guest WiFi permaneça um ativo seguro e em conformidade, em vez de um passivo.
Definições Principais
DNS over HTTPS (DoH)
A protocol for performing remote Domain Name System (DNS) resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
When IT teams deploy content filtering, DoH acts as a bypass mechanism, hiding DNS queries within standard encrypted web traffic.
DNS over TLS (DoT)
A security protocol for encrypting and wrapping DNS queries and answers via the Transport Layer Security (TLS) protocol, operating on a dedicated port (853).
Often enabled by default on modern Android devices (Private DNS), DoT must be blocked at the firewall to ensure queries fall back to the venue's filtered DNS.
Opportunistic DoH
A behavior where an operating system or browser automatically upgrades standard DNS queries to DoH if it detects that the configured DNS resolver supports the encrypted protocol.
This feature, common in Windows 11 and Chrome, means that even if a venue assigns a standard DNS IP, the traffic may still shift to encrypted port 443, bypassing legacy monitoring.
Port 53 Interception
A network firewall configuration that captures all outbound traffic on UDP/TCP port 53 and forcibly redirects it to a designated DNS resolver, regardless of the destination IP requested by the client.
Essential for capturing DNS queries from devices with hardcoded DNS settings or those that have fallen back from a failed DoH connection.
Next-Generation Firewall (NGFW)
A network security device that provides capabilities beyond a traditional, stateful firewall, including deep packet inspection, application awareness, and TLS/SSL decryption.
NGFWs are critical for DoH mitigation as they can identify and block DoH traffic based on application signatures rather than just IP addresses.
Fallback Behavior
The programmed response of a client device when its preferred encrypted DNS protocol (DoH or DoT) fails to connect, typically resulting in the device reverting to standard, unencrypted DNS.
Network architects rely on this behavior; by intentionally breaking DoH/DoT connections, they force the device to use the interceptable port 53.
Command-and-Control (C2)
The infrastructure used by attackers to communicate with compromised devices (malware/botnets) within a target network.
Modern malware increasingly uses DoH to hide C2 communications from enterprise network monitors, making DoH mitigation a critical security requirement.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The captive portal is the legally appropriate location to inform users that their DNS traffic is being filtered and that encrypted DNS protocols are blocked.
Exemplos Práticos
A 400-room hotel recently deployed a cloud-based DNS filtering service to comply with brand standards regarding family-friendly content. However, the IT manager notices that a significant portion of guest traffic is still reaching adult content sites, and the DNS filtering dashboard shows lower-than-expected query volumes. How should the network architect remediate this bypass?
- Audit Firewall Rules: The architect must first verify that outbound TCP/UDP port 53 is being intercepted and NAT-redirected to the cloud DNS service.
- Block DoH Resolvers: Implement an NGFW blocklist to drop outbound HTTPS (port 443) traffic destined for known DoH providers (e.g., Cloudflare, Google, Quad9).
- Block DoT: Add a firewall rule to drop all outbound TCP port 853 traffic to prevent Android Private DNS bypass.
- Verify IPv6: Ensure all the above rules are applied to both IPv4 and IPv6 traffic.
A retail chain with 150 locations needs to implement DNS filtering to block malware and phishing on their guest WiFi. They use basic branch firewalls without advanced TLS inspection capabilities. How can they effectively mitigate DoH without upgrading their hardware?
Without TLS inspection, the chain must rely on robust routing and blocklists.
- Deploy a dynamic DoH IP/Domain blocklist on the branch firewalls, configured to update automatically via an external threat feed.
- Implement strict port 53 NAT redirection to the enterprise DNS filter.
- Block port 853 entirely.
- Update the captive portal Terms of Service to explicitly state that encrypted DNS protocols are blocked to enforce network security policies.
Perguntas de Prática
Q1. A stadium network engineer configures the DHCP server to provide the IP address of their secure, filtered DNS service to all guest devices. However, testing reveals that devices with manually configured DNS settings (e.g., 8.8.8.8) are successfully bypassing the filter. What is the most appropriate architectural fix?
Dica: Consider the difference between suggesting a route and enforcing a route at the network edge.
Ver resposta modelo
The engineer must implement a NAT port forwarding rule on the stadium's firewall. This rule should intercept all outbound UDP and TCP traffic on port 53 originating from the guest VLAN and forcibly translate the destination IP to the secure DNS service's IP address. This ensures that regardless of the client's local configuration, the traffic is routed through the filtering policy.
Q2. Following the implementation of a strict DoH blocklist, the IT helpdesk at a conference centre receives reports that a specific, bespoke event management app is failing to load for attendees. Packet capture shows the app is attempting to use its own hardcoded DoH resolver, which is being blocked, and the app refuses to fall back to standard DNS. How should this be resolved?
Dica: Balance security policy with business continuity. Can the firewall distinguish between general DoH traffic and traffic to a specific, approved endpoint?
Ver resposta modelo
The administrator should create an exception in the NGFW policy. Rather than disabling the DoH blocklist globally, they should identify the specific IP address or domain of the DoH resolver used by the event management app and whitelist it. If the firewall supports application-layer (Layer 7) inspection, a more robust solution is to create a policy that permits DoH traffic only if the destination matches the approved application's infrastructure, ensuring general DoH bypass attempts remain blocked.
Q3. A public sector organisation is auditing its guest WiFi compliance. They have successfully blocked port 853 (DoT) and implemented port 53 interception. However, they lack the budget for an NGFW with advanced TLS inspection or dynamic DoH blocklists. What is the most effective remaining strategy to mitigate DoH?
Dica: If dynamic lists aren't available, how can you address the vast majority of opportunistic DoH traffic?
Ver resposta modelo
The organisation should implement a static blocklist on their existing firewall, targeting the IP addresses and domains of the most common public DoH providers (e.g., Cloudflare, Google, Quad9). While this requires manual maintenance and won't catch obscure DoH resolvers, research shows that the vast majority of DoH traffic defaults to a handful of major providers. This provides a highly effective '80/20' solution within their budget constraints.