O Impacto dos Anúncios em Vídeo na Capacidade da Rede de Convidados
Este guia explora como os anúncios em vídeo de reprodução automática consomem silenciosamente a capacidade da rede de convidados em ambientes de alta densidade. Fornece estratégias acionáveis e neutras em relação ao fornecedor para gestores de TI e arquitetos de rede recuperarem largura de banda usando filtragem DNS na extremidade da rede.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada: A Física da Saturação da Rede Impulsionada por Anúncios
- A Anatomia de um Pedido Web
- A Penalidade de Largura de Banda dos Anúncios em Vídeo
- Consumo de Tempo de Antena e Ineficiência Espectral
- Cascatas de Latência na Resolução DNS
- Guia de Implementação: Arquitetura de Filtragem DNS na Extremidade da Rede
- Estratégia de Implementação Passo a Passo
- Melhores Práticas e Conformidade
- Privacidade por Design (Artigo 25 do GDPR)
- Segmentação de Rede (PCI DSS)
- Experiência de Utilizador Transparente
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio

Resumo Executivo
Para CTOs e arquitetos de rede que gerem locais de alta densidade — como estádios, centros de Retalho , ambientes de Hotelaria e centros de Transporte — o desempenho do WiFi de convidados é uma métrica operacional crítica. No entanto, o planeamento padrão da capacidade da rede muitas vezes ignora um consumo silencioso e estrutural da largura de banda: anúncios em vídeo de reprodução automática.
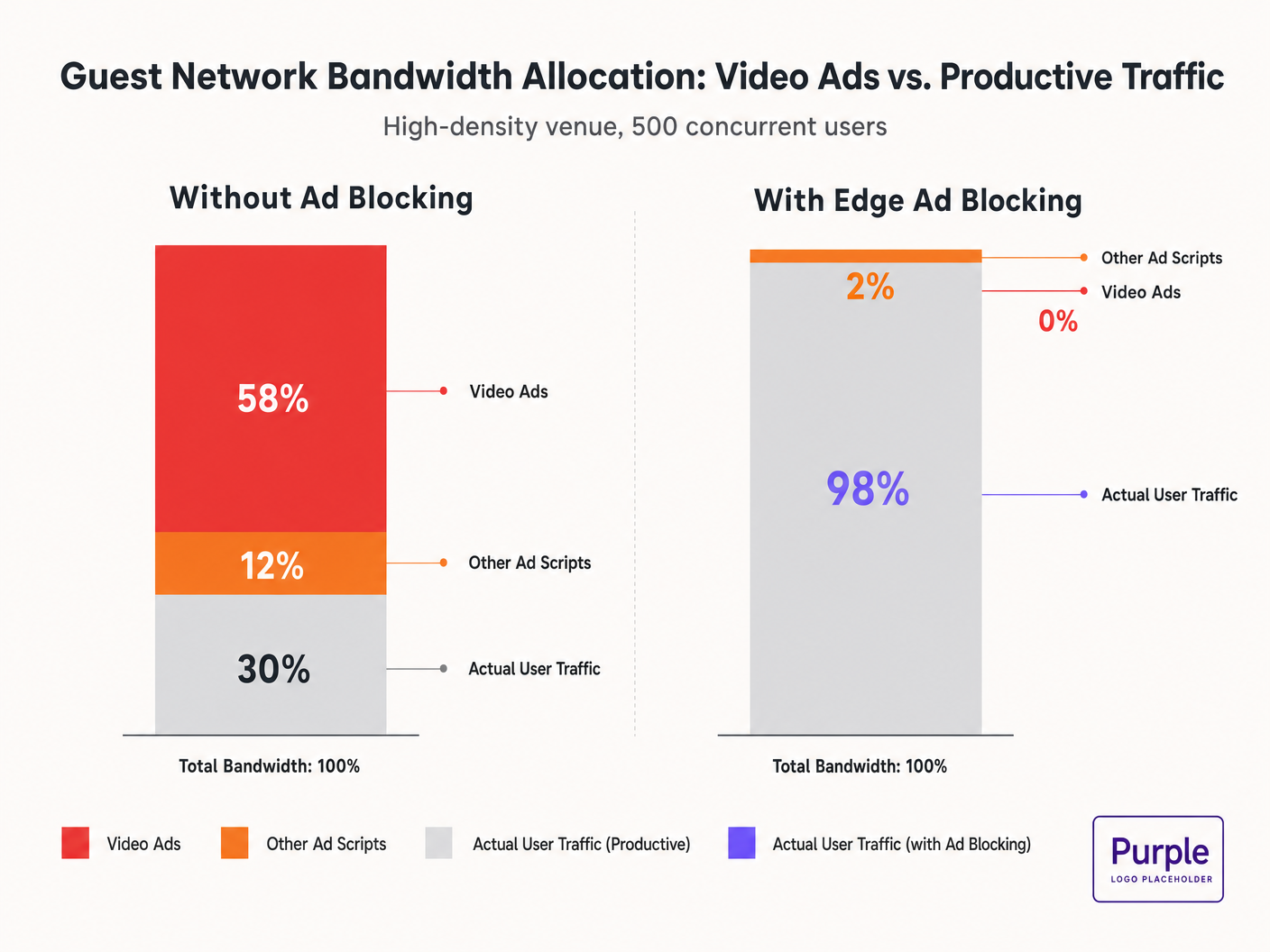
Quando os convidados se conectam à rede e navegam em propriedades web padrão, os seus dispositivos iniciam dezenas de conexões em segundo plano para redes de entrega de anúncios. Estes fluxos de vídeo de bitrate adaptativo podem consumir 50-70% da capacidade disponível, degradando a experiência para todos os utilizadores e saturando os links de backhaul. Este guia detalha a mecânica técnica deste consumo de largura de banda e fornece um plano neutro em relação ao fornecedor para mitigá-lo na extremidade da rede usando filtragem DNS. Ao implementar estas estratégias, os locais podem melhorar drasticamente o desempenho do Guest WiFi , reduzir os custos de infraestrutura e aumentar a conformidade sem esperar por um ciclo de atualização de hardware.
Ouça o nosso briefing sobre este tópico:
Análise Técnica Detalhada: A Física da Saturação da Rede Impulsionada por Anúncios
A Anatomia de um Pedido Web
Quando um utilizador numa rede de convidados acede a um website com suporte de anúncios, o comportamento do navegador é altamente agressivo. Um único carregamento de página tipicamente desencadeia conexões para 8-40 domínios de terceiros separados, incluindo trocas de anúncios, Demand-Side Platforms (DSPs) e Content Delivery Networks (CDNs).
A Penalidade de Largura de Banda dos Anúncios em Vídeo
Os anúncios em vídeo, particularmente os formatos pre-roll e mid-roll servidos por grandes trocas, são entregues como fluxos de bitrate adaptativo. A CDN sonda a largura de banda disponível e serve o fluxo de maior qualidade possível. Num ambiente de alta densidade com 500 utilizadores concorrentes, se 20% dos utilizadores desencadearem um fluxo de anúncio 1080p a 4-8 Mbps, a procura agregada aumenta instantaneamente em 400-800 Mbps. Este tráfego não solicitado ignora a modelagem padrão de Qualidade de Serviço (QoS) porque se origina de conexões HTTPS legítimas.
Consumo de Tempo de Antena e Ineficiência Espectral
Além da saturação do backhaul, os anúncios em vídeo consomem valioso tempo de antena de rádio. Num meio sem fios partilhado, cada dispositivo que recebe ativamente um fluxo de alta bitrate reduz as oportunidades de transmissão para outros dispositivos. Embora o padrão IEEE 802.11ax (Wi-Fi 6) tenha introduzido OFDMA e BSS Colouring para melhorar a eficiência espectral, estes mecanismos não conseguem compensar o volume puro de dados exigido pelas redes de anúncios. A camada de rádio fica congestionada, levando a um aumento da latência e perda de pacotes para o tráfego produtivo.
Cascatas de Latência na Resolução DNS
A entrega de anúncios depende de cadeias de redirecionamento complexas. Uma única impressão de anúncio pode exigir 6-12 pesquisas DNS antes que o fluxo de vídeo seja iniciado. Numa implementação densa, isto aumenta exponencialmente a carga no resolvedor DNS local. Quando o resolvedor se torna um gargalo, a latência em cascata, causando degradação percetível do carregamento da página para cada utilizador na rede.
Guia de Implementação: Arquitetura de Filtragem DNS na Extremidade da Rede
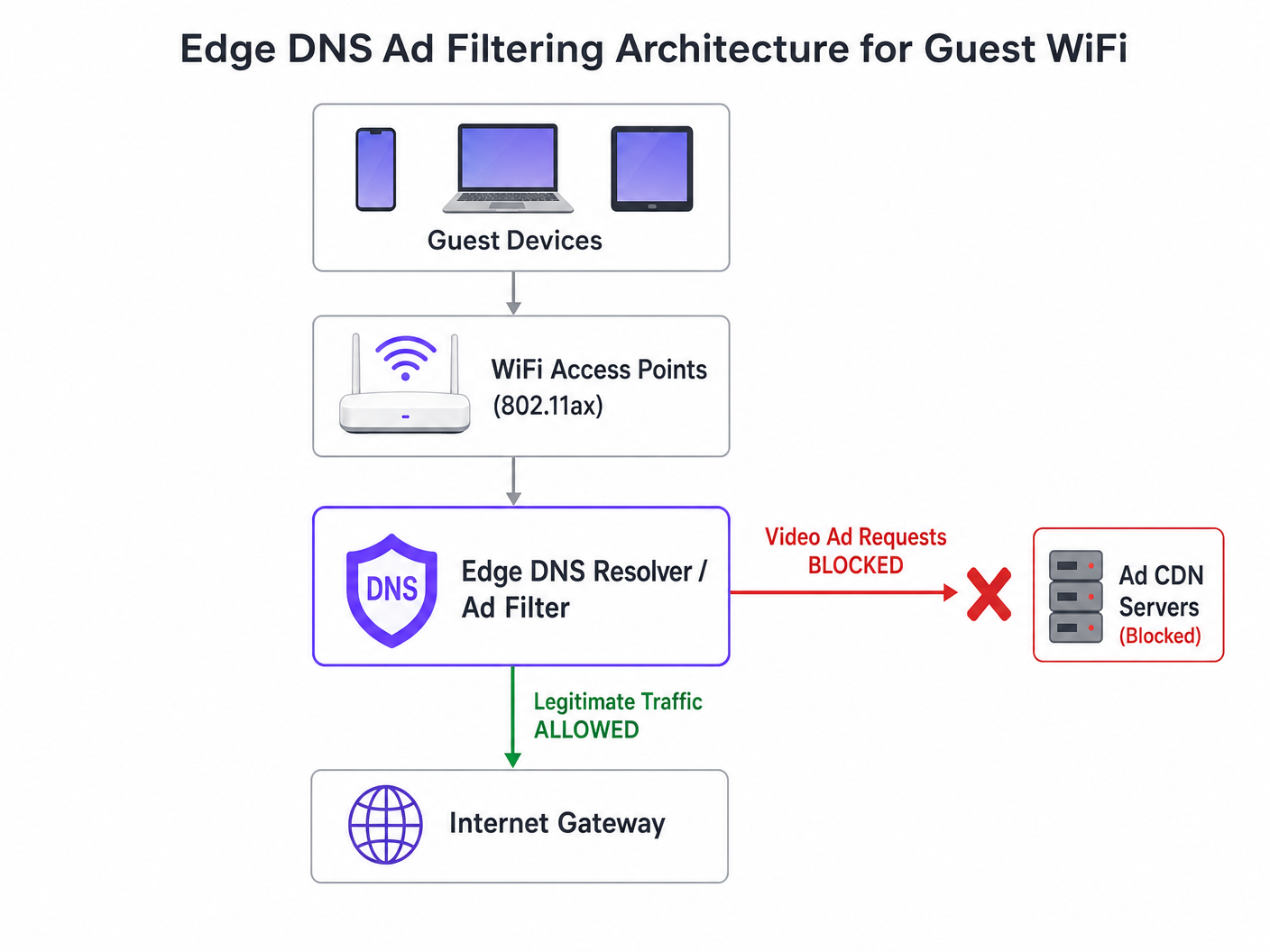
A intervenção arquitetónica mais eficaz é a filtragem DNS na extremidade da rede. Ao bloquear domínios de redes de anúncios ao nível do resolvedor, a rede impede que a conexão TCP seja estabelecida. Esta abordagem é sem estado, escala linearmente e adiciona latência insignificante.
Estratégia de Implementação Passo a Passo
- Instrumentação Passiva: Implemente o registo DNS passivo na rede de convidados durante 48-72 horas para estabelecer um perfil de tráfego de linha de base. Identifique os domínios mais consultados e o seu volume. Utilize plataformas como WiFi Analytics para visualizar estes dados.
- Aplicação Conservadora de Blocklist: Não implemente blocklists comunitárias massivas (por exemplo, a lista de Steven Black) no primeiro dia. Comece com os 500 principais domínios conhecidos de entrega de anúncios em vídeo. Valide que a entrega de conteúdo legítimo não é afetada.
- Configuração DNS Split-Horizon: Garanta uma separação rigorosa entre a infraestrutura DNS corporativa e de convidados. A política de filtragem deve ser aplicada exclusivamente à VLAN de convidados para evitar interrupções operacionais.
- Manutenção Automatizada de Blocklist: As redes de anúncios rodam dinamicamente domínios e usam Algoritmos de Geração de Domínios (DGAs). Configure o resolvedor para obter informações de ameaças atualizadas e feeds de blocklist pelo menos a cada 4 horas.
- Gestão de DNS over HTTPS (DoH): Navegadores modernos podem tentar contornar os resolvedores locais usando DoH. Mitigue isto bloqueando a porta TCP/UDP 443 de saída para intervalos de IP de provedores DoH conhecidos, forçando o fallback para o resolvedor fornecido pela rede.
Para uma análise mais aprofundada das especificidades da configuração, consulte o nosso guia sobre Melhorar as Velocidades WiFi Bloqueando Redes de Anúncios na Extremidade da Rede .
Melhores Práticas e Conformidade
Privacidade por Design (Artigo 25 do GDPR)
A implementação da filtragem DNS na extremidade da rede alinha-se com os princípios de privacidade por design do GDPR. Ao impedir conexões a domínios de rastreamento de terceiros, a rede protege inerentemente os dados dos convidados contra a recolha não autorizada. Esta postura proativa reduz o encargo de conformidade do local.
Segmentação de Rede (PCI DSS)
Para retalho e hospitallocais que processam pagamentos, o PCI DSS exige uma segmentação de rede rigorosa. A filtragem de DNS reforça este limite, garantindo que os dispositivos dos convidados não possam, inadvertidamente, atuar como condutas para cargas maliciosas entregues através de redes de anúncios comprometidas (malvertising).
Experiência de Utilizador Transparente
Ao contrário dos intersticiais de Captive Portal ou da inspeção profunda de pacotes, a filtragem de DNS é transparente. O utilizador experiencia carregamentos de página mais rápidos e menor consumo de bateria. Se um espaço de anúncio não carregar, geralmente colapsa ou exibe um espaço em branco, o que raramente é percebido como uma falha de rede pelo utilizador.
Resolução de Problemas e Mitigação de Riscos
| Modo de Falha | Causa Raiz | Estratégia de Mitigação |
|---|---|---|
| Bloqueio excessivo de conteúdo legítimo | Bloqueio ao nível da raiz de CDNs partilhadas (p. ex., Akamai, Fastly). | Implementar filtragem ao nível do subdomínio. Manter uma lista de permissões robusta para serviços críticos do local. |
| Filtragem contornada por DoH | Navegadores a usar resolvedores DoH codificados. | Encaminhar para nulo IPs de provedores DoH conhecidos. Implementar políticas de split-tunneling se usar gestão de dispositivos móveis (MDM). |
| Esgotamento da CPU do Resolvedor | Infraestrutura DNS subdimensionada a lidar com respostas NXDOMAIN excessivas. | Provisionar resolvedores com CPU/RAM adequados. Usar caching agressivamente. Considerar resolvedores recursivos alojados na cloud para elasticidade. |
ROI e Impacto no Negócio
O impacto no negócio da filtragem de DNS na edge é imediato e mensurável:
- Recuperação de Largura de Banda: Os locais normalmente recuperam 30-50% da largura de banda da sua rede de convidados, atrasando atualizações de backhaul dispendiosas.
- Satisfação Melhorada dos Convidados: Carregamentos de página mais rápidos e conectividade fiável correlacionam-se diretamente com pontuações mais altas de Net Promoter Score (NPS) e avaliações positivas do local.
- Eficiência Operacional: A redução de tickets de helpdesk relacionados com "WiFi lento" permite que as equipas de TI se concentrem em iniciativas estratégicas, como a implementação do Modo de Mapas Offline ou a expansão de integrações de cidades inteligentes, conforme defendido pela nossa liderança (ver Purple Appoints Iain Fox as VP Growth ).
- Postura de Segurança Reforçada: O bloqueio proativo de malvertising e domínios de rastreamento simplifica as auditorias de segurança e os relatórios de conformidade. Saiba mais sobre como manter uma postura de segurança no nosso artigo: Explain what is audit trail for IT Security in 2026 .
Definições Principais
Edge DNS Filtering
The practice of blocking access to specific domains at the local DNS resolver level, preventing devices from resolving the IP addresses of known ad networks.
Used by IT teams to silently drop unwanted traffic before a TCP connection is even attempted, saving bandwidth and improving performance.
Adaptive Bitrate Streaming (ABR)
A technology that dynamically adjusts the quality of a video stream based on the user's available bandwidth.
Ad networks use ABR to serve the highest possible quality video, which aggressively consumes available guest WiFi throughput.
Split-Horizon DNS
A configuration where different DNS responses are provided depending on the source IP address of the query (e.g., guest vs. corporate).
Essential for applying restrictive filtering policies to guest networks without impacting back-office operations.
DNS over HTTPS (DoH)
A protocol for performing remote DNS resolution via the HTTPS protocol, encrypting the queries.
DoH can bypass local edge filtering; network architects must actively block known DoH providers to enforce local DNS policies.
BSS Colouring
A Wi-Fi 6 (802.11ax) feature that adds a 'colour' identifier to transmissions, allowing access points to ignore traffic from overlapping networks.
Improves radio efficiency in dense venues, but does not solve the backhaul saturation caused by video ads.
NXDOMAIN
A DNS response code indicating that the requested domain name does not exist.
The standard response returned by a filtering resolver when a device attempts to query a blocked ad network domain.
Domain Generation Algorithm (DGA)
Techniques used by malware and some aggressive ad networks to periodically generate new domain names to evade static blocklists.
Requires IT teams to use dynamic, frequently updated threat intelligence feeds rather than static hosts files.
Malvertising
The use of online advertising to distribute malware or redirect users to malicious websites.
Blocking ad networks at the edge inherently protects guest devices from these threats, improving the venue's security posture.
Exemplos Práticos
A 400-room hotel is experiencing severe guest WiFi degradation every evening between 19:00 and 22:00. The 1 Gbps backhaul is saturated, but the property management system (PMS) shows only 600 connected devices. How should the network architect address this without upgrading the circuit?
- Implement passive DNS logging on the guest VLAN to analyze the traffic profile during the peak window. 2. Identify the top bandwidth-consuming domains, which are likely video ad CDNs. 3. Deploy a recursive DNS resolver with a curated blocklist targeting these specific ad networks. 4. Configure the guest DHCP scope to assign the new resolver. 5. Monitor bandwidth utilization; expect a 30-40% reduction in peak load.
A stadium IT director wants to implement DNS ad blocking but is concerned about breaking the venue's own mobile app, which uses a third-party analytics SDK.
- Audit the mobile app's network dependencies using a proxy tool. 2. Identify the specific API endpoints required for the app's functionality. 3. Add these specific FQDNs (Fully Qualified Domain Names) to the DNS resolver's allowlist, superseding any blocklist policies. 4. Roll out the filtering policy to a subset of access points (e.g., one concourse) for beta testing before a venue-wide deployment.
Perguntas de Prática
Q1. A retail chain wants to deploy DNS filtering across 500 stores. They currently use a cloud-managed firewall solution. Should they deploy local DNS resolvers at each store or route all DNS queries to a centralized cloud resolver?
Dica: Consider the latency impact of DNS queries on page load times.
Ver resposta modelo
They should route queries to a centralized cloud resolver with geographically distributed points of presence (PoPs), provided the latency to the nearest PoP is under 20ms. Deploying and maintaining 500 local resolvers introduces significant operational overhead. Cloud resolvers offer centralized policy management and automated blocklist updates, which is ideal for a distributed retail environment.
Q2. After implementing a DNS blocklist, the marketing team reports that the venue's captive portal splash page is failing to load for some users. What is the most likely cause?
Dica: Captive portals often rely on external resources for tracking or authentication.
Ver resposta modelo
The blocklist has likely inadvertently blocked a CDN or tracking pixel domain (e.g., Google Analytics or a social login API) that the captive portal depends on. The architect must review the DNS logs for the captive portal's walled garden IP range, identify the blocked dependency, and add it to the allowlist.
Q3. A conference centre is hosting a digital marketing summit. The IT director is concerned that blocking ad networks will disrupt the attendees' ability to work and demonstrate their products. How should this be handled?
Dica: Network policies can be segmented by SSID or VLAN.
Ver resposta modelo
The IT director should provision a dedicated SSID/VLAN for the summit attendees with a bypass policy that uses unfiltered DNS resolvers (e.g., 8.8.8.8). The standard guest WiFi network can remain filtered. This provides the necessary access for the specific event without compromising the performance of the general public network.