L'impact des publicités vidéo sur le débit du réseau invité
Ce guide explore comment les publicités vidéo à lecture automatique consomment silencieusement le débit du réseau invité dans les environnements à haute densité. Il fournit des stratégies exploitables et neutres vis-à-vis des fournisseurs pour les responsables informatiques et les architectes réseau afin de récupérer de la bande passante à l'aide du filtrage DNS en périphérie.
Écouter ce guide
Voir la transcription du podcast
- Résumé Exécutif
- Plongée Technique : La Physique de la Saturation Réseau Causée par les Publicités
- L'Anatomie d'une Requête Web
- La Pénalité de Bande Passante des Publicités Vidéo
- Consommation du Temps d'Antenne et Inefficacité Spectrale
- Cascades de Latence de Résolution DNS
- Guide d'Implémentation : Architecture de Filtrage DNS en Périphérie
- Stratégie de Déploiement Étape par Étape
- Bonnes Pratiques et Conformité
- Confidentialité dès la Conception (GDPR Article 25)
- Segmentation Réseau (PCI DSS)
- Expérience utilisateur transparente
- Dépannage et atténuation des risques
- ROI et impact commercial

Résumé Exécutif
Pour les CTO et les architectes réseau gérant des sites à haute densité — tels que les stades, les centres Retail , les environnements Hospitality et les pôles de Transport — la performance du WiFi invité est une métrique opérationnelle critique. Cependant, la planification standard de la capacité réseau néglige souvent une consommation silencieuse et structurelle de la bande passante : les publicités vidéo à lecture automatique.
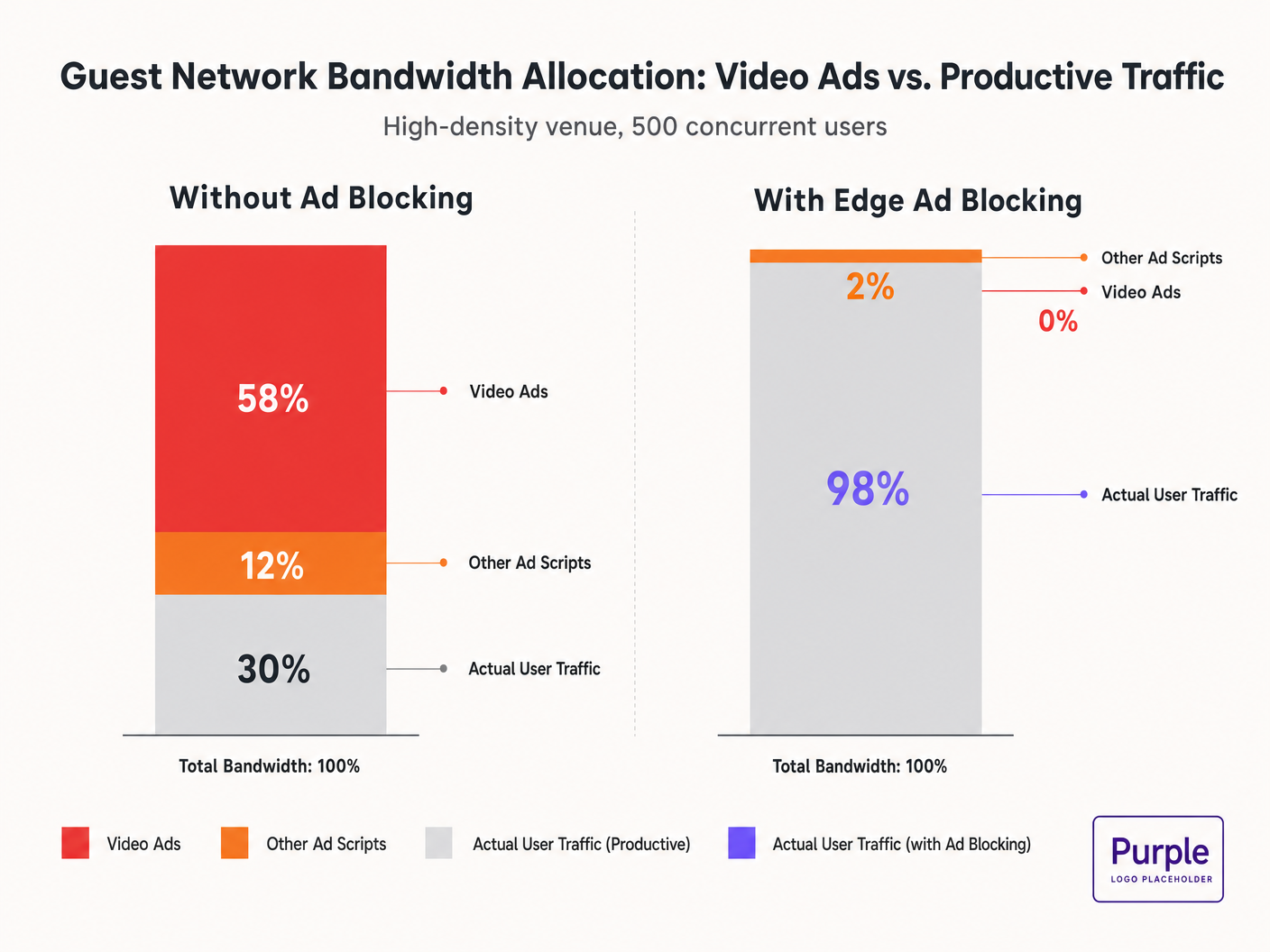
Lorsque les invités se connectent au réseau et naviguent sur des propriétés web standard, leurs appareils initient des dizaines de connexions en arrière-plan vers des réseaux de diffusion publicitaire. Ces flux vidéo à débit adaptatif peuvent consommer 50 à 70 % du débit disponible, dégradant l'expérience de tous les utilisateurs et saturant les liaisons de backhaul. Ce guide détaille les mécanismes techniques de cette consommation de bande passante et fournit un plan d'action neutre vis-à-vis des fournisseurs pour l'atténuer en périphérie à l'aide du filtrage DNS. En mettant en œuvre ces stratégies, les sites peuvent améliorer considérablement les performances du Guest WiFi , réduire les coûts d'infrastructure et renforcer la conformité sans attendre un cycle de renouvellement matériel.
Écoutez notre exposé sur ce sujet :
Plongée Technique : La Physique de la Saturation Réseau Causée par les Publicités
L'Anatomie d'une Requête Web
Lorsqu'un utilisateur sur un réseau invité accède à un site web financé par la publicité, le comportement du navigateur est très agressif. Un seul chargement de page déclenche généralement des connexions à 8-40 domaines tiers distincts, y compris des régies publicitaires, des plateformes côté demande (DSPs) et des réseaux de diffusion de contenu (CDNs).
La Pénalité de Bande Passante des Publicités Vidéo
Les publicités vidéo, en particulier les formats pre-roll et mid-roll diffusés par les principales régies, sont livrées sous forme de flux à débit adaptatif. Le CDN sonde la bande passante disponible et diffuse le flux de la plus haute qualité possible. Dans un environnement à haute densité avec 500 utilisateurs simultanés, si 20 % des utilisateurs déclenchent un flux publicitaire 1080p à 4-8 Mbps, la demande agrégée augmente instantanément de 400-800 Mbps. Ce trafic non sollicité contourne la mise en forme standard de la Qualité de Service (QoS) car il provient de connexions HTTPS légitimes.
Consommation du Temps d'Antenne et Inefficacité Spectrale
Au-delà de la saturation du backhaul, les publicités vidéo consomment un temps d'antenne radio précieux. Dans un milieu sans fil partagé, chaque appareil recevant activement un flux à haut débit réduit les opportunités de transmission pour les autres appareils. Bien que la norme IEEE 802.11ax (Wi-Fi 6) ait introduit l'OFDMA et le BSS Colouring pour améliorer l'efficacité spectrale, ces mécanismes ne peuvent compenser le volume considérable de données exigé par les réseaux publicitaires. La couche radio devient congestionnée, entraînant une latence accrue et une perte de paquets pour le trafic productif.
Cascades de Latence de Résolution DNS
La diffusion publicitaire repose sur des chaînes de redirection complexes. Une seule impression publicitaire peut nécessiter 6 à 12 requêtes DNS avant l'initiation du flux vidéo. Dans un déploiement dense, cela augmente exponentiellement la charge sur le résolveur DNS local. Lorsque le résolveur devient un goulot d'étranglement, la latence se propage en cascade, provoquant une dégradation perceptible du chargement des pages pour chaque utilisateur sur le réseau.
Guide d'Implémentation : Architecture de Filtrage DNS en Périphérie
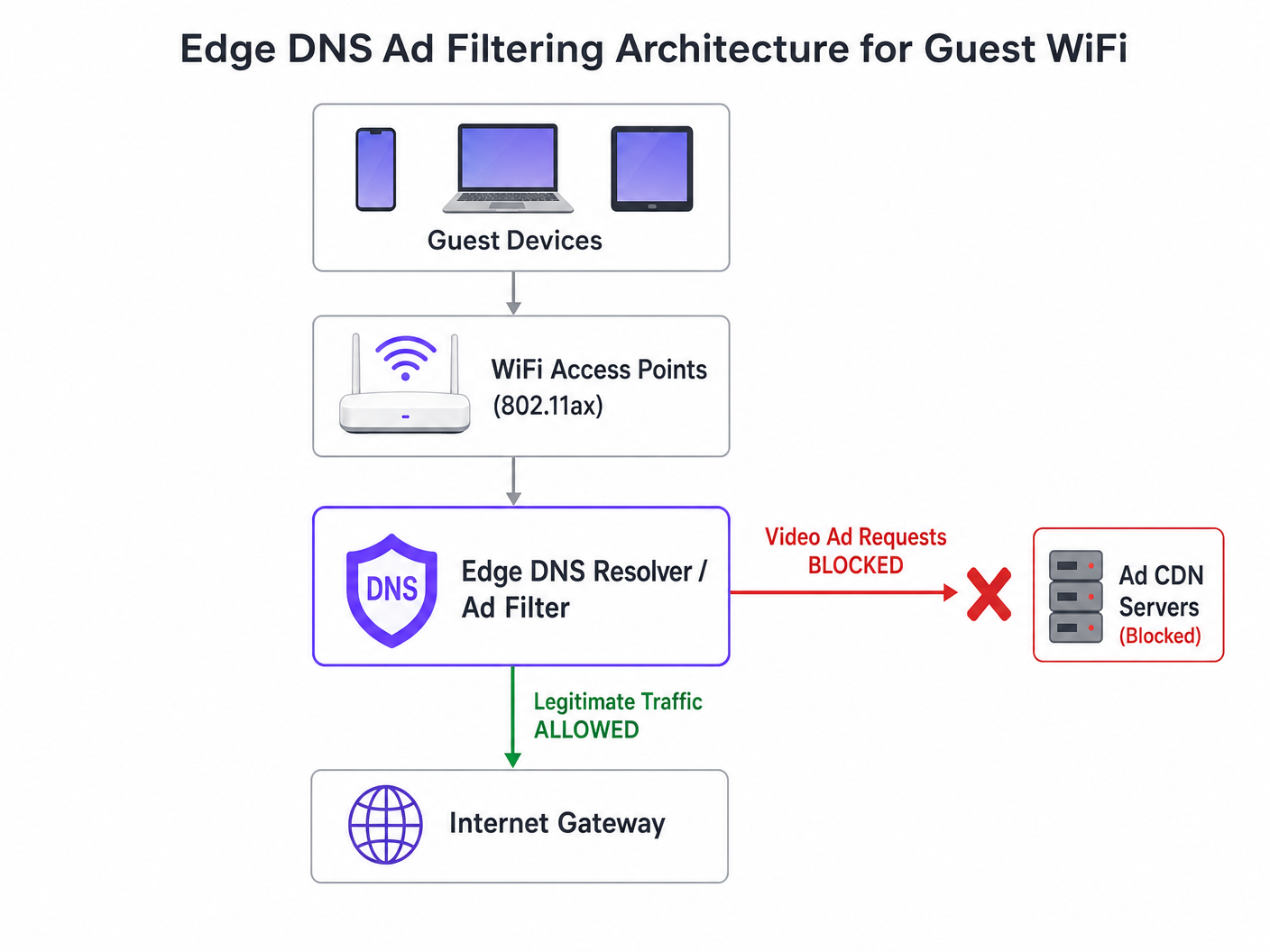
L'intervention architecturale la plus efficace est le filtrage DNS en périphérie. En bloquant les domaines des réseaux publicitaires au niveau du résolveur, le réseau empêche l'établissement de la connexion TCP. Cette approche est sans état, évolue linéairement et ajoute une latence négligeable.
Stratégie de Déploiement Étape par Étape
- Instrumentation Passive : Déployez la journalisation DNS passive sur le réseau invité pendant 48 à 72 heures pour établir un profil de trafic de référence. Identifiez les domaines les plus interrogés et leur volume. Utilisez des plateformes comme WiFi Analytics pour visualiser ces données.
- Application Conservatrice de la Liste de Blocage : Ne déployez pas de listes de blocage communautaires massives (par exemple, la liste de Steven Black) dès le premier jour. Commencez par les 500 principaux domaines de diffusion de publicités vidéo connus. Validez que la diffusion de contenu légitime n'est pas impactée.
- Configuration DNS Split-Horizon : Assurez une séparation stricte entre l'infrastructure DNS d'entreprise et celle des invités. La politique de filtrage doit être limitée exclusivement au VLAN invité pour éviter les perturbations opérationnelles.
- Maintenance Automatisée de la Liste de Blocage : Les réseaux publicitaires font pivoter dynamiquement les domaines et utilisent des algorithmes de génération de domaines (DGAs). Configurez le résolveur pour qu'il récupère les informations de veille sur les menaces et les flux de listes de blocage mis à jour au moins toutes les 4 heures.
- Gestion du DNS over HTTPS (DoH) : Les navigateurs modernes peuvent tenter de contourner les résolveurs locaux en utilisant le DoH. Atténuez cela en bloquant le port TCP/UDP 443 sortant vers les plages d'adresses IP des fournisseurs DoH connus, forçant ainsi le retour au résolveur fourni par le réseau.
Pour une plongée plus approfondie dans les spécificités de configuration, consultez notre guide sur Improving WiFi Speeds by Blocking Ad Networks at the Edge .
Bonnes Pratiques et Conformité
Confidentialité dès la Conception (GDPR Article 25)
L'implémentation du filtrage DNS en périphérie s'aligne sur les principes de confidentialité dès la conception du GDPR. En empêchant les connexions aux domaines de suivi tiers, le réseau protège intrinsèquement les données des invités contre la collecte non autorisée. Cette approche proactive réduit la charge de conformité du site.
Segmentation Réseau (PCI DSS)
Pour le commerce de détail et l'hospitalles sites traitant des paiements, PCI DSS exige une segmentation stricte du réseau. Le filtrage DNS renforce cette limite en garantissant que les appareils des invités ne peuvent pas agir par inadvertance comme des conduits pour des charges utiles malveillantes livrées via des réseaux publicitaires compromis (malvertising).
Expérience utilisateur transparente
Contrairement aux interstitiels de captive portal ou à l'inspection approfondie des paquets, le filtrage DNS est transparent. L'utilisateur bénéficie de chargements de page plus rapides et d'une consommation de batterie réduite. Si un emplacement publicitaire ne se charge pas, il se réduit généralement ou affiche un espace vide, ce qui est rarement perçu comme une défaillance du réseau par l'utilisateur.
Dépannage et atténuation des risques
| Mode de défaillance | Cause première | Stratégie d'atténuation |
|---|---|---|
| Blocage excessif de contenu légitime | Blocage au niveau racine des CDN partagés (par exemple, Akamai, Fastly). | Mettre en œuvre le filtrage au niveau du sous-domaine. Maintenir une liste blanche robuste pour les services essentiels du site. |
| Filtrage contourné par DoH | Navigateurs utilisant des résolveurs DoH codés en dur. | Acheminer vers null les IP des fournisseurs DoH connus. Mettre en œuvre des politiques de split-tunneling si vous utilisez la gestion des appareils mobiles (MDM). |
| Épuisement du CPU du résolveur | Infrastructure DNS sous-dimensionnée gérant des réponses NXDOMAIN excessives. | Provisionner les résolveurs avec un CPU/RAM adéquat. Utiliser le cache de manière agressive. Envisager des résolveurs récursifs hébergés dans le cloud pour l'élasticité. |
ROI et impact commercial
L'impact commercial du filtrage DNS en périphérie est immédiat et mesurable :
- Récupération de la bande passante : Les sites récupèrent généralement 30 à 50 % de la bande passante de leur réseau invité, ce qui retarde les coûteuses mises à niveau du backhaul.
- Amélioration de la satisfaction des invités : Des chargements de page plus rapides et une connectivité fiable sont directement corrélés à des scores de promoteur net (NPS) plus élevés et à des avis positifs sur le site.
- Efficacité opérationnelle : La réduction des tickets d'assistance liés au "WiFi lent" permet aux équipes informatiques de se concentrer sur des initiatives stratégiques, telles que le déploiement du Mode Cartes hors ligne ou l'expansion des intégrations de villes intelligentes, comme le préconise notre direction (voir Purple nomme Iain Fox VP Croissance ).
- Posture de sécurité renforcée : Le blocage proactif des malvertising et des domaines de suivi simplifie les audits de sécurité et les rapports de conformité. Apprenez-en davantage sur le maintien d'une posture sécurisée dans notre article : Expliquer ce qu'est une piste d'audit pour la sécurité informatique en 2026 .
Définitions clés
Edge DNS Filtering
The practice of blocking access to specific domains at the local DNS resolver level, preventing devices from resolving the IP addresses of known ad networks.
Used by IT teams to silently drop unwanted traffic before a TCP connection is even attempted, saving bandwidth and improving performance.
Adaptive Bitrate Streaming (ABR)
A technology that dynamically adjusts the quality of a video stream based on the user's available bandwidth.
Ad networks use ABR to serve the highest possible quality video, which aggressively consumes available guest WiFi throughput.
Split-Horizon DNS
A configuration where different DNS responses are provided depending on the source IP address of the query (e.g., guest vs. corporate).
Essential for applying restrictive filtering policies to guest networks without impacting back-office operations.
DNS over HTTPS (DoH)
A protocol for performing remote DNS resolution via the HTTPS protocol, encrypting the queries.
DoH can bypass local edge filtering; network architects must actively block known DoH providers to enforce local DNS policies.
BSS Colouring
A Wi-Fi 6 (802.11ax) feature that adds a 'colour' identifier to transmissions, allowing access points to ignore traffic from overlapping networks.
Improves radio efficiency in dense venues, but does not solve the backhaul saturation caused by video ads.
NXDOMAIN
A DNS response code indicating that the requested domain name does not exist.
The standard response returned by a filtering resolver when a device attempts to query a blocked ad network domain.
Domain Generation Algorithm (DGA)
Techniques used by malware and some aggressive ad networks to periodically generate new domain names to evade static blocklists.
Requires IT teams to use dynamic, frequently updated threat intelligence feeds rather than static hosts files.
Malvertising
The use of online advertising to distribute malware or redirect users to malicious websites.
Blocking ad networks at the edge inherently protects guest devices from these threats, improving the venue's security posture.
Exemples concrets
A 400-room hotel is experiencing severe guest WiFi degradation every evening between 19:00 and 22:00. The 1 Gbps backhaul is saturated, but the property management system (PMS) shows only 600 connected devices. How should the network architect address this without upgrading the circuit?
- Implement passive DNS logging on the guest VLAN to analyze the traffic profile during the peak window. 2. Identify the top bandwidth-consuming domains, which are likely video ad CDNs. 3. Deploy a recursive DNS resolver with a curated blocklist targeting these specific ad networks. 4. Configure the guest DHCP scope to assign the new resolver. 5. Monitor bandwidth utilization; expect a 30-40% reduction in peak load.
A stadium IT director wants to implement DNS ad blocking but is concerned about breaking the venue's own mobile app, which uses a third-party analytics SDK.
- Audit the mobile app's network dependencies using a proxy tool. 2. Identify the specific API endpoints required for the app's functionality. 3. Add these specific FQDNs (Fully Qualified Domain Names) to the DNS resolver's allowlist, superseding any blocklist policies. 4. Roll out the filtering policy to a subset of access points (e.g., one concourse) for beta testing before a venue-wide deployment.
Questions d'entraînement
Q1. A retail chain wants to deploy DNS filtering across 500 stores. They currently use a cloud-managed firewall solution. Should they deploy local DNS resolvers at each store or route all DNS queries to a centralized cloud resolver?
Conseil : Consider the latency impact of DNS queries on page load times.
Voir la réponse type
They should route queries to a centralized cloud resolver with geographically distributed points of presence (PoPs), provided the latency to the nearest PoP is under 20ms. Deploying and maintaining 500 local resolvers introduces significant operational overhead. Cloud resolvers offer centralized policy management and automated blocklist updates, which is ideal for a distributed retail environment.
Q2. After implementing a DNS blocklist, the marketing team reports that the venue's captive portal splash page is failing to load for some users. What is the most likely cause?
Conseil : Captive portals often rely on external resources for tracking or authentication.
Voir la réponse type
The blocklist has likely inadvertently blocked a CDN or tracking pixel domain (e.g., Google Analytics or a social login API) that the captive portal depends on. The architect must review the DNS logs for the captive portal's walled garden IP range, identify the blocked dependency, and add it to the allowlist.
Q3. A conference centre is hosting a digital marketing summit. The IT director is concerned that blocking ad networks will disrupt the attendees' ability to work and demonstrate their products. How should this be handled?
Conseil : Network policies can be segmented by SSID or VLAN.
Voir la réponse type
The IT director should provision a dedicated SSID/VLAN for the summit attendees with a bypass policy that uses unfiltered DNS resolvers (e.g., 8.8.8.8). The standard guest WiFi network can remain filtered. This provides the necessary access for the specific event without compromising the performance of the general public network.