Reduzir a Latência em Redes WiFi de Alta Densidade
Este guia detalha como a eliminação de pesquisas DNS desnecessárias para domínios de rastreamento reduz drasticamente a latência em redes WiFi de alta densidade. Fornece orientações acionáveis sobre arquitetura, implementação e ROI para líderes de TI que gerem ambientes de espaços congestionados.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada
- A Anatomia de uma Tempestade de Consultas DNS
- Arquitetura para Resolução na Extremidade da Rede
- Guia de Implementação
- Passo 1: Auditoria da Linha de Base
- Passo 2: Implementação do Resolvedor Local
- Passo 3: Gerir DNS sobre HTTPS (DoH)
- Melhores Práticas
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio
- Podcast de Briefing de Especialistas
Resumo Executivo

Para CTOs e arquitetos de rede que gerem ambientes de alta densidade, como espaços de Hotelaria , estádios e propriedades de Retalho , a latência é frequentemente diagnosticada incorretamente como um problema puramente de RF ou de backhaul. No entanto, uma percentagem significativa da latência percebida em redes WiFi modernas provém da camada DNS. Quando um utilizador se conecta ao seu Guest WiFi , um único carregamento de página pode desencadear 20 a 70 consultas DNS, principalmente para pixels de rastreamento de terceiros, redes de anúncios e beacons de telemetria. Num espaço lotado, isto cria uma 'tempestade de consultas DNS' que sobrecarrega os resolvedores locais e ocupa tempo de antena valioso.
Ao implementar um cache DNS local agressivo e filtrar domínios de rastreamento na extremidade da rede, os espaços podem retornar um NXDOMAIN instantâneo para pedidos desnecessários. Esta abordagem elimina a viagem de ida e volta à internet pública, reduzindo a latência percebida em até 87%. Este guia fornece a arquitetura técnica e a estrutura de implementação para implantar WiFi otimizado para DNS, melhorando a experiência do utilizador, reduzindo os tickets de suporte e garantindo a captura de dados de WiFi Analytics sem interrupções.
Análise Técnica Detalhada
A Anatomia de uma Tempestade de Consultas DNS
Numa implementação de alta densidade a executar 802.11ax (WiFi 6/6E), mecanismos de eficiência como OFDMA e BSS Colouring são projetados para gerir a interferência de co-canal e otimizar o tempo de antena. No entanto, estes mecanismos assumem que o meio de rádio está a transmitir dados reais do utilizador. Quando 3.000 hóspedes num hotel ou 10.000 fãs num estádio tentam carregar páginas web simultaneamente, o volume puro de consultas DNS para domínios não essenciais (por exemplo, ad-tracker.com, analytics.thirdparty.net) introduz uma sobrecarga massiva.
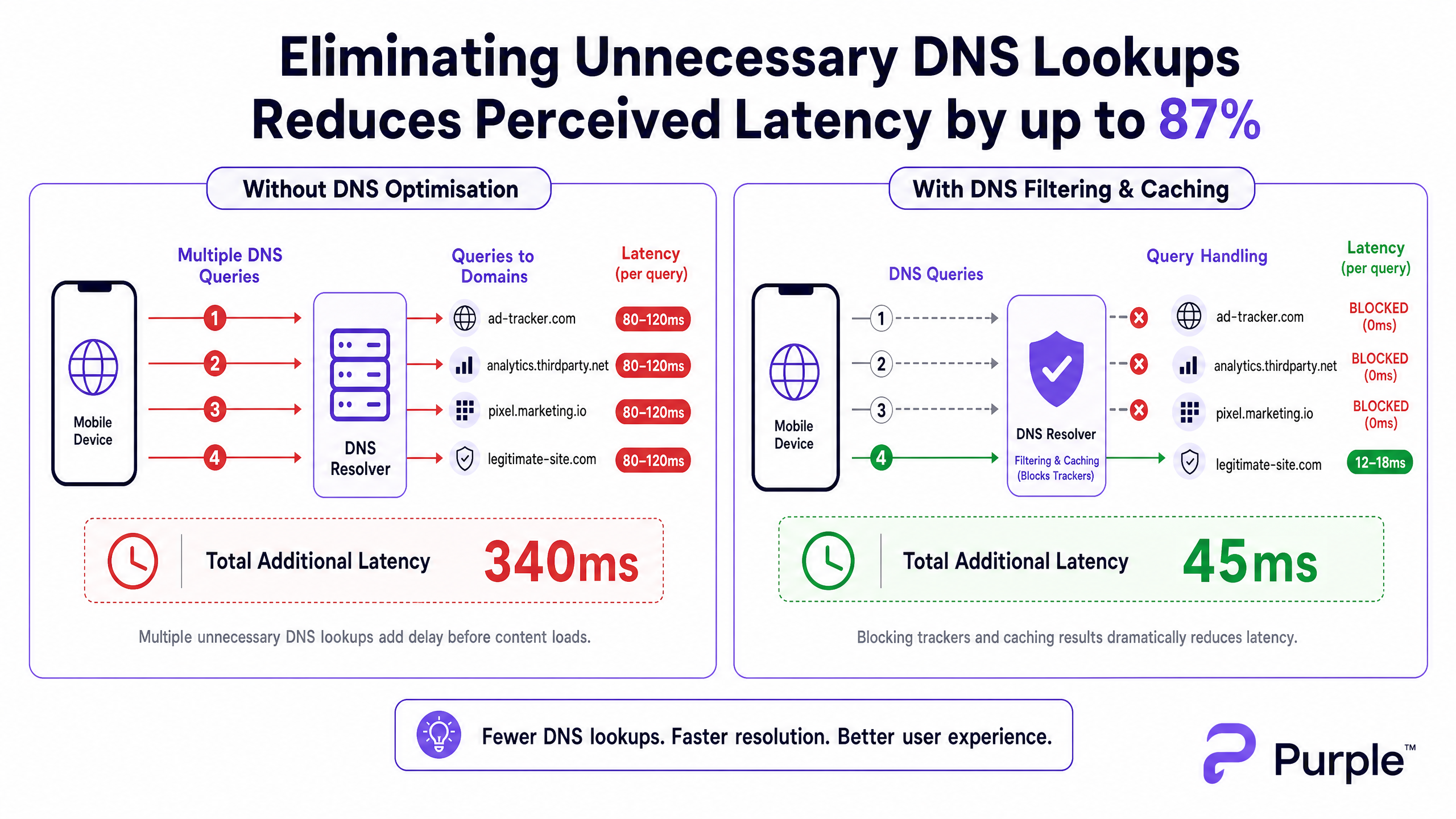
Cada consulta DNS enviada para um resolvedor externo (como o DNS padrão de um ISP ou o 8.8.8.8 da Google) incorre num tempo de ida e volta de 80-150ms numa rede congestionada. Se uma página requer 15 pesquisas de domínios de rastreamento antes de renderizar o conteúdo, o utilizador experimenta mais de um segundo de atraso 'invisível'. Isto não é um problema de débito; é um gargalo transacional.
Arquitetura para Resolução na Extremidade da Rede
Para mitigar isto, a arquitetura deve mover a resolução para a extremidade da rede. A implementação de um resolvedor DNS local com um cache TTL agressivo garante que domínios legítimos e frequentemente solicitados sejam resolvidos em menos de 5ms.
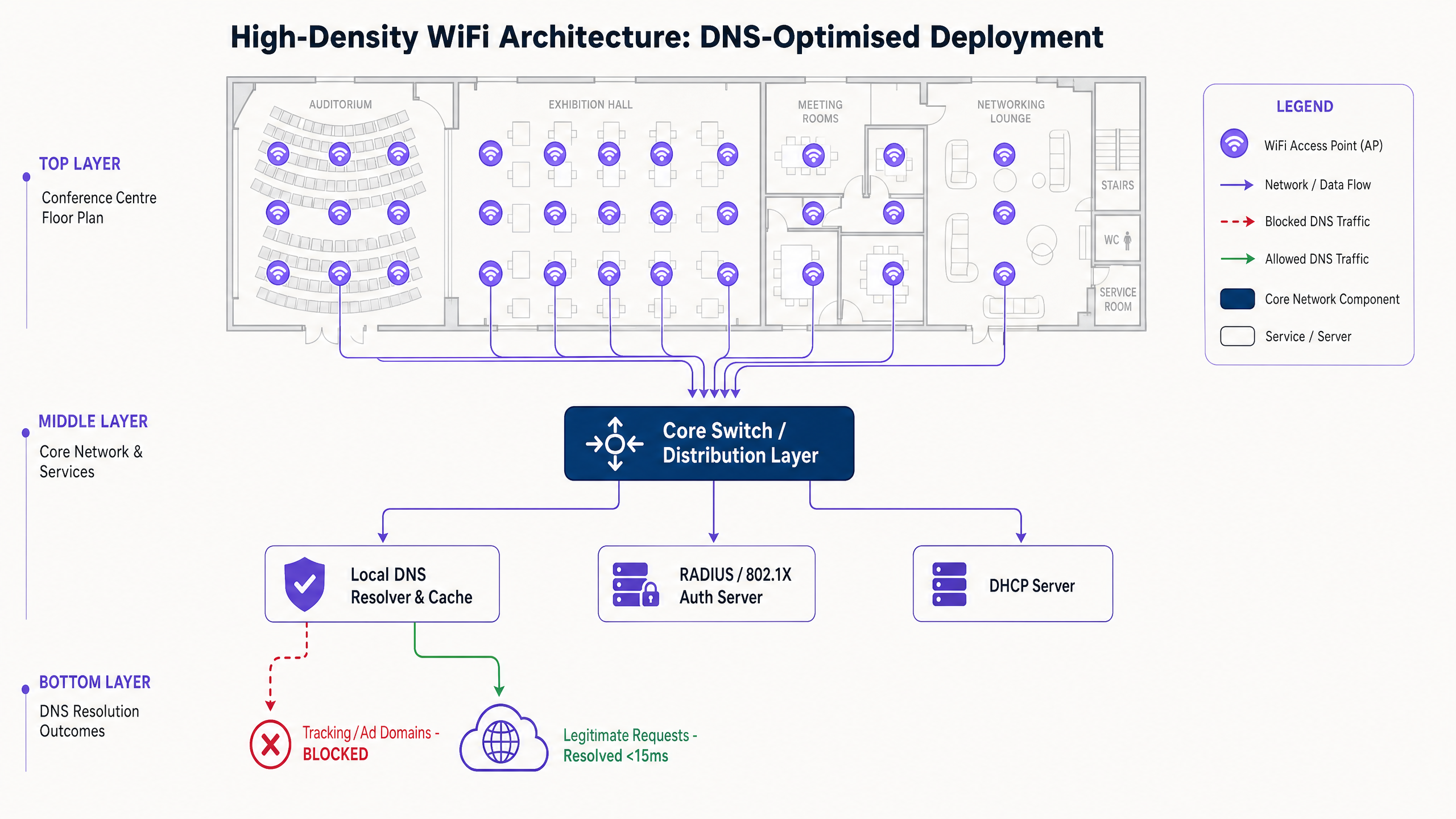
Crucialmente, este resolvedor deve integrar uma lista de bloqueio curada (por exemplo, modo empresarial Pi-hole, Cisco Umbrella) para descartar consultas para domínios de rastreamento conhecidos. Retornar um NXDOMAIN instantâneo liberta a oportunidade de transmissão (TXOP) no meio sem fios, permitindo que os dados de carga útil reais fluam mais rapidamente.
Guia de Implementação
Passo 1: Auditoria da Linha de Base
Antes de alterar o caminho DNS, estabeleça uma linha de base. Instrumente o seu resolvedor existente ou implemente um tap passivo para capturar registos de consultas durante um período de pico de utilização. Identifique os 50 domínios mais consultados; tipicamente, 30-50% serão serviços de rastreamento ou telemetria.
Passo 2: Implementação do Resolvedor Local
Implemente um resolvedor no local ou alojado na extremidade da rede. Configure zonas autoritativas para recursos internos (split DNS) e aplique uma lista de bloqueio conservadora. Evite listas agressivas inicialmente para evitar quebrar aplicações legítimas.
Passo 3: Gerir DNS sobre HTTPS (DoH)
Os sistemas operativos modernos contornam cada vez mais os resolvedores locais usando DoH. Para manter o controlo, intercete o tráfego DoH na firewall bloqueando o TCP/UDP 443 de saída para provedores DoH conhecidos, redirecionando-os para o seu resolvedor DoH gerido. Para implicações mais profundas, reveja o nosso guia sobre DNS Over HTTPS (DoH): Implicações para a Filtragem de WiFi Público .
Melhores Práticas
- Listagem de Bloqueio Iterativa: Atualize as listas de bloqueio semanalmente através de feeds automatizados, mas mantenha um processo de lista de permissões de resposta rápida para falsos positivos.
- Alinhamento de Conformidade: Documente a filtragem DNS nos Termos de Serviço do seu Captive Portal. Isto alinha-se com o GDPR ao reduzir ativamente a recolha de dados de terceiros.
- Segmentação de VLAN: Teste novas listas de bloqueio numa VLAN de teste ou num subconjunto específico de APs antes da implementação em todo o espaço.
Resolução de Problemas e Mitigação de Riscos
- Quebra de Aplicação: O modo de falha mais comum é uma aplicação legítima falhar porque uma dependência foi bloqueada. Monitorize as taxas de pico de
NXDOMAIN; um aumento súbito geralmente indica um falso positivo. - Falhas de Bypass de DoH: Se a latência permanecer alta apesar da filtragem local, verifique os registos da firewall para DNS encriptado a contornar as suas regras de interceção.
- Envenenamento de Cache: Certifique-se de que o seu resolvedor local está protegido contra ataques de envenenamento de cache, particularmente em implementações públicas de Transporte ou Saúde .
ROI e Impacto no Negócio
Reduzir a latência através da otimização de DNS impacta diretamente o resultado final. Para um hotel, carregamentos mais rápidos do Captive Portal e navegação responsiva correlacionam-se diretamente com pontuações mais altas no TripAdvisor. Para um ambiente de retalho, garante uma integração perfeita com ferramentas como as iniciativas Purple Appoints Iain Fox as VP Growth – Public Sector to Drive Digital Inclusion and Smart City Innovation ou serviços baseados em localização como o Purple Launches Offline Maps Mode for Seamless, Secure Navigation to WiFi Hotspots .
Ao tratar o DNS como uma camada de infraestrutura crítica em vez de uma reflexão tardia, os espaços podem extrair o máximo desempenho do seu hardware RF existente investimentos.
Podcast de Briefing de Especialistas
Ouça o nosso consultor sénior a detalhar a mecânica e as estratégias de implementação para a otimização de DNS em locais de alta densidade.
Definições Principais
DNS Query Storm
A massive, simultaneous spike in domain name resolution requests, typically occurring when hundreds of devices connect and load tracking-heavy web pages simultaneously.
Common in stadiums and hotels during peak ingress times, causing perceived network failure even when bandwidth is available.
NXDOMAIN
A DNS response code indicating that the requested domain name does not exist.
Used strategically in DNS filtering to instantly terminate requests for known tracking domains, saving latency and airtime.
DNS over HTTPS (DoH)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
While good for consumer privacy, DoH can bypass corporate network controls and filtering, requiring specific firewall interception strategies.
TTL Cache (Time to Live)
A mechanism where a local DNS resolver stores the IP address of a recently resolved domain for a specified period, serving subsequent requests instantly without querying the authoritative server.
Crucial for reducing latency for legitimate, highly trafficked domains (e.g., google.com, netflix.com) in a venue.
Airtime Overhead
The proportion of wireless transmission capacity consumed by management frames, control frames, and transactional protocols (like DNS) rather than actual user payload data.
Reducing unnecessary DNS queries directly reduces airtime overhead, improving the efficiency of the entire AP cluster.
Split DNS
An implementation where different DNS responses are provided depending on the source IP address of the request, often used to resolve internal hostnames differently from external ones.
Necessary when a venue hosts local services (like a captive portal or local media server) that should not be resolved via the public internet.
BSS Colouring
A spatial reuse technique in 802.11ax (WiFi 6) that assigns a 'colour' (a number) to each Basic Service Set, allowing APs on the same channel to differentiate between their own traffic and overlapping network traffic.
A key RF optimisation feature that works best when the network isn't bogged down by unnecessary transactional overhead like excessive DNS lookups.
Passive DNS Tap
A method of monitoring DNS traffic by copying packets from a switch port (SPAN port) without interfering with the actual flow of traffic.
Used during the initial audit phase to understand query volume and identify the top tracking domains before implementing filtering.
Exemplos Práticos
A 500-room resort hotel experiences severe 'slow WiFi' complaints during the 4:00 PM to 6:00 PM check-in window, despite having upgraded to WiFi 6 access points last year. Backhaul utilisation is only at 40%.
- Deploy a local caching DNS resolver (e.g., Unbound) on the guest VLAN. 2. Implement a conservative tracking domain blocklist. 3. Configure the DHCP server to assign the local resolver's IP to all guest clients. 4. Implement firewall rules blocking outbound port 53 to force all DNS traffic through the local resolver.
A large conference centre needs to implement DNS filtering to improve latency but is concerned about modern smartphones bypassing the local resolver using DNS over HTTPS (DoH).
- Identify the IP ranges of major public DoH providers (Cloudflare, Google, Quad9). 2. Create firewall rules blocking outbound TCP port 443 to these specific IP ranges. 3. Deploy a local DoH-capable resolver. 4. Use network policy (e.g., DHCP Option 6) to direct clients to the managed DoH resolver.
Perguntas de Prática
Q1. You are managing a stadium WiFi network. During halftime, users report slow loading times. Dashboard metrics show AP CPU utilisation is low, and backhaul bandwidth is at 30% capacity. What is the most likely cause, and what is the immediate mitigation?
Dica: Consider the transactional volume that occurs when 15,000 people open their phones simultaneously.
Ver resposta modelo
The most likely cause is a DNS query storm overwhelming the local resolver or upstream ISP resolver. The immediate mitigation is to verify the local resolver's cache hit rate and ensure that a blocklist for high-volume tracking domains is active, instantly returning NXDOMAIN to reduce the query load.
Q2. A retail chain implements local DNS filtering to block tracking domains. A week later, the marketing team complains that their new in-store analytics app is failing to load on the guest WiFi. How do you resolve this while maintaining latency benefits?
Dica: Filtering is not a set-and-forget configuration.
Ver resposta modelo
Review the DNS query logs for the specific devices or timeframes when the app failed. Identify the blocked domain that the app depends on (a false positive). Add this specific domain to the resolver's whitelist, ensuring the app functions while the rest of the tracking domains remain blocked.
Q3. You deploy a local DNS resolver with aggressive caching and filtering in a public sector building. However, packet captures show a significant volume of DNS traffic still leaving the network on port 443. What is happening, and how do you enforce local policy?
Dica: Modern browsers use encrypted protocols to bypass standard port 53 DNS.
Ver resposta modelo
Devices are using DNS over HTTPS (DoH) to bypass the local resolver. To enforce policy, you must configure the firewall to block outbound TCP/UDP port 443 traffic destined for known public DoH provider IP ranges (e.g., Cloudflare, Google), forcing devices to fall back to the DHCP-provided local resolver.